Every American healthcare organization faces a daily challenge as digital threats grow more sophisticated and persistent. Protecting sensitive patient data and maintaining operational continuity call for more than simple security tools. Vulnerability assessments offer a systematic way to uncover technical and operational weaknesses before they become a crisis. This approach empowers CISOs and cybersecurity managers to drive risk management, regulatory compliance, and informed readiness, laying the groundwork for robust cyber resilience.
Table of Contents
- Understanding Vulnerability Assessments In Healthcare
- Types Of Vulnerability Assessments Explained
- How Assessments Enhance Cyber Resilience
- Compliance Requirements And Regulatory Impact
- Risks Of Neglecting Vulnerability Assessments
- Comparing Assessments To Other Security Solutions
Key Takeaways
| Point | Details |
|---|---|
| Importance of Vulnerability Assessments | Regular vulnerability assessments are crucial for identifying and mitigating cybersecurity risks in healthcare organizations. |
| Types of Assessments Matter | Employ a variety of assessment types to comprehensively evaluate security across interconnected medical technologies. |
| Proactive Cyber Resilience | Implement proactive strategies that prioritize risk identification and create robust defense plans to enhance cyber resilience. |
| Regulatory Compliance | Adhere to regulatory requirements by integrating vulnerability management into your ongoing security processes for continuous improvement. |
Understanding Vulnerability Assessments in Healthcare
Healthcare organizations face complex and evolving cybersecurity challenges that demand systematic, proactive risk management strategies. Vulnerability assessments represent a critical component of comprehensive healthcare security frameworks, enabling institutions to identify, evaluate, and mitigate potential digital risks before they escalate into serious security incidents.
A vulnerability assessment is a structured technical evaluation designed to systematically scan, identify, and classify potential security weaknesses within an organization's digital infrastructure. For healthcare environments, these assessments go beyond generic IT security approaches and incorporate specialized considerations unique to medical technology ecosystems. Systematic hazard vulnerability analysis involves multiple critical components:
- Comprehensive infrastructure scanning
- Identifying potential security gaps
- Ranking risks by probability and potential impact
- Developing targeted mitigation strategies
- Ensuring compliance with healthcare regulatory standards
Healthcare vulnerability assessments are particularly crucial because medical systems handle extremely sensitive information and operate mission-critical technologies that directly impact patient safety. Unlike typical corporate IT environments, healthcare networks include complex interconnected systems like electronic health records, medical imaging equipment, patient monitoring devices, and administrative platforms.
Vulnerability assessments provide a structured approach to understanding an organization's security posture, transforming potential risks into manageable, strategic improvements.
The assessment process typically involves advanced technical scanning tools, expert analysis, and comprehensive reporting that helps healthcare leadership make informed cybersecurity decisions. By systematically examining network configurations, software vulnerabilities, access controls, and potential threat vectors, organizations can develop robust defensive strategies.
Pro tip: Conduct vulnerability assessments quarterly and immediately after significant infrastructure changes to maintain continuous security readiness.
Types of Vulnerability Assessments Explained
Healthcare organizations rely on multiple specialized vulnerability assessment types to comprehensively evaluate and mitigate potential security risks across their complex technological ecosystems. Vulnerability assessment methodologies have evolved to address the unique challenges presented by medical technology infrastructures.
The primary types of vulnerability assessments in healthcare include:
- Network Infrastructure Assessment
- Scanning network configurations
- Identifying potential entry points
- Evaluating firewall and security protocols
- Medical Device Security Assessment
- Testing interconnected medical equipment
- Analyzing potential communication vulnerabilities
- Ensuring device firmware security
- Application Security Assessment
- Evaluating electronic health record systems
- Testing software integration points
- Identifying potential data exposure risks
Each assessment type serves a distinct purpose in healthcare cybersecurity. Network infrastructure assessments focus on the broader technological ecosystem, examining how different systems communicate and potential weak points that malicious actors could exploit. Medical device security assessments are particularly critical, given the sensitive nature of healthcare technology and the potential patient safety implications of a security breach.

Here's a summary of how different vulnerability assessment types support healthcare cybersecurity:
| Assessment Type | Unique Focus in Healthcare | Example Impact on Patient Care |
|---|---|---|
| Network Infrastructure | System communication & access routes | Prevents data breaches via open ports |
| Medical Device Security | Device connectivity & firmware | Ensures safe operation of monitors |
| Application Security | Health app & EHR integrations | Protects confidential patient data |
Healthcare vulnerability assessments are not just technical exercises but essential strategies for protecting patient data and ensuring continuous medical service delivery.
The Administration for Strategic Preparedness and Response (ASPR) recommends a comprehensive approach that goes beyond traditional IT security models. These assessments must consider not just technological vulnerabilities, but also organizational processes, human factors, and potential disruption scenarios that could impact patient care.
Pro tip: Integrate multiple assessment types to create a holistic view of your healthcare organization's cybersecurity landscape and prioritize remediation efforts strategically.
How Assessments Enhance Cyber Resilience
Cyber resilience in healthcare represents a comprehensive approach to protecting digital infrastructure beyond traditional security measures. Strategic cyber preparedness involves developing robust mechanisms that enable organizations to anticipate, withstand, and rapidly recover from potential cybersecurity incidents.
Healthcare organizations enhance cyber resilience through several critical strategies:
- Proactive Risk Identification
- Continuously mapping potential vulnerabilities
- Understanding systemic technological weaknesses
- Developing predictive threat models
- Comprehensive Defense Planning
- Creating multilayered security frameworks
- Implementing adaptive response protocols
- Establishing rapid incident recovery procedures
- Organizational Capability Building
- Training workforce in cybersecurity awareness
- Developing cross-functional incident response teams
- Integrating cybersecurity into organizational culture
The systematic identification of vulnerabilities allows healthcare leaders to transform potential risks into strategic advantages. By understanding technological and human factors that contribute to cybersecurity challenges, organizations can develop nuanced, comprehensive defense strategies that protect patient data and maintain critical medical services.
Cyber resilience is not about preventing every possible attack, but about building adaptive systems that can effectively detect, respond, and recover from potential security incidents.
Healthcare technology ecosystems require sophisticated, multidimensional approaches to cyber resilience. This means moving beyond traditional perimeter defenses and developing dynamic, intelligent systems that can anticipate and mitigate emerging threats across complex technological landscapes.
Pro tip: Conduct regular tabletop exercises simulating cyber incidents to test and refine your organization's resilience strategies and response capabilities.
Compliance Requirements and Regulatory Impact
Healthcare organizations must navigate complex regulatory landscapes that demand rigorous cybersecurity standards and comprehensive vulnerability management. HIPAA Security Risk Assessment requirements establish critical frameworks for protecting electronic protected health information (ePHI) across healthcare technology ecosystems.
Key compliance requirements encompass multiple critical domains:
- Administrative Safeguards
- Developing comprehensive security policies
- Implementing formal risk management processes
- Creating workforce security training programs
- Physical Safeguards
- Controlling physical access to sensitive systems
- Implementing workstation and device security protocols
- Managing inventory and device tracking mechanisms
- Technical Safeguards
- Establishing access control systems
- Implementing encryption technologies
- Creating audit logging and monitoring mechanisms
The regulatory landscape requires healthcare organizations to demonstrate not just technical compliance, but a proactive approach to risk management. These mandates are designed to be flexible, allowing organizations to develop security strategies that align with their unique technological infrastructures and operational requirements.
Compliance is not a destination, but a continuous journey of risk management and strategic security enhancement.
Healthcare leaders must recognize that regulatory requirements represent minimum standards, not comprehensive security strategies. Effective compliance demands going beyond checkbox approaches and developing holistic, adaptive cybersecurity frameworks that anticipate emerging technological risks.
Pro tip: Document every vulnerability assessment comprehensively, creating an audit trail that demonstrates your organization's systematic approach to regulatory compliance.
Risks of Neglecting Vulnerability Assessments
Neglecting vulnerability assessments in healthcare creates a catastrophic cascade of potential risks that extend far beyond simple technological vulnerabilities. Hazard vulnerability analysis reveals the profound consequences of overlooking systematic risk identification and mitigation strategies.
The most critical risks of failing to conduct comprehensive vulnerability assessments include:
- Patient Safety Risks
- Potential exposure of sensitive medical data
- Compromised medical device security
- Interruption of critical patient care systems
- Operational Disruption Risks
- Extended system downtime
- Reduced medical service capabilities
- Compromised emergency response mechanisms
- Financial and Reputational Risks
- Potential regulatory fines
- Increased cybersecurity insurance costs
- Loss of patient and stakeholder trust
Healthcare organizations that ignore vulnerability assessments essentially create invisible vulnerabilities that can rapidly transform into catastrophic security incidents. These gaps can provide malicious actors with multiple entry points into critical healthcare infrastructure, potentially compromising entire technological ecosystems.
Unaddressed vulnerabilities are not mere technical challenges, but potential threats to patient safety, organizational integrity, and medical service continuity.
The comprehensive impact of neglecting vulnerability assessments extends beyond immediate technological risks. Organizations face potential legal liabilities, regulatory penalties, and long-term reputational damage that can fundamentally undermine their operational capabilities and patient trust.
Pro tip: Treat vulnerability assessments as ongoing, dynamic processes rather than one-time compliance checkboxes, ensuring continuous adaptation to emerging technological risks.
Comparing Assessments to Other Security Solutions
Healthcare cybersecurity requires a nuanced approach that distinguishes vulnerability assessments from other security interventions. Vulnerability assessment frameworks provide a comprehensive, proactive strategy that fundamentally differs from reactive security solutions.
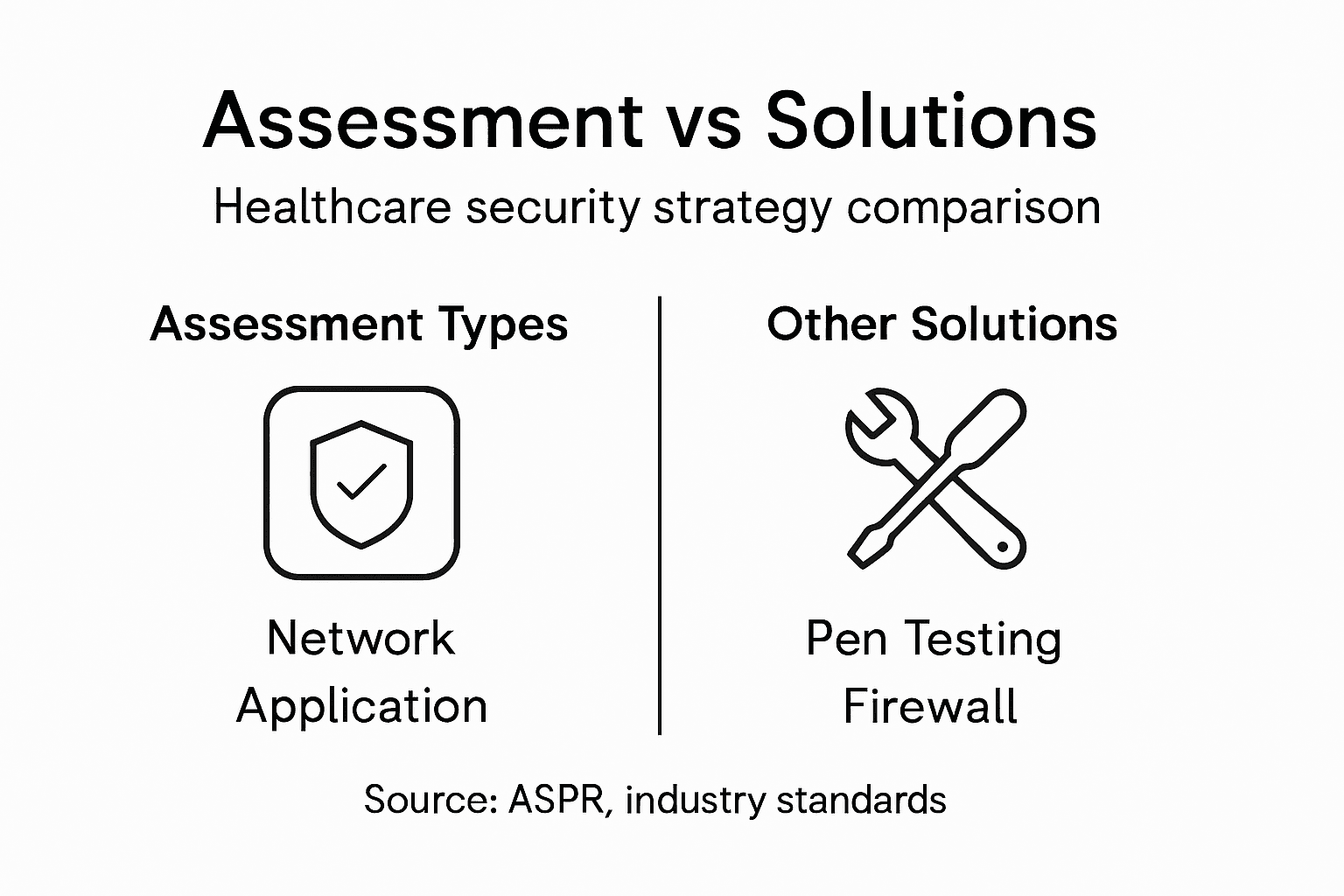
Key distinctions between vulnerability assessments and other security approaches include:
Compare these core healthcare cybersecurity approaches to understand their roles:
| Approach | Primary Role | When to Use |
|---|---|---|
| Vulnerability Assessment | Ongoing risk discovery | Routine or after changes |
| Incident Response | Post-breach mitigation | After a detected incident |
| Penetration Testing | Attack simulation & proof | Periodic security validation |
- Vulnerability Assessments
- Proactive risk identification
- Systematic weakness mapping
- Prioritized remediation strategies
- Incident Response
- Reactive problem resolution
- Post-breach mitigation
- Emergency management
- Penetration Testing
- Simulated attack scenarios
- Point-in-time security evaluation
- Specific vulnerability validation
Unlike isolated security tools that provide snapshot evaluations, vulnerability assessments offer a dynamic, continuous approach to understanding and managing technological risks. These assessments go beyond identifying immediate weaknesses, creating a strategic framework for ongoing security enhancement and organizational resilience.
Vulnerability assessments transform cybersecurity from a reactive checkpoint into a strategic, adaptive risk management process.
Healthcare organizations need comprehensive security strategies that integrate multiple approaches. While penetration testing and incident response have critical roles, vulnerability assessments provide the foundational intelligence that enables more targeted, effective security interventions.
Pro tip: Integrate multiple security approaches, using vulnerability assessments as the cornerstone of a comprehensive, adaptive cybersecurity strategy.
Strengthen Healthcare Cybersecurity with Strategic Vulnerability Assessments
Healthcare organizations face critical challenges in identifying and managing complex vulnerabilities that threaten patient safety, data privacy, and operational continuity. The article highlights the need for continuous, proactive vulnerability assessments that transform hidden risks into actionable insights. Key pain points include safeguarding interconnected medical devices, protecting electronic health records, and meeting rigorous regulatory compliance demands while maintaining resilient healthcare delivery.
At Heights Consulting Group, we understand these urgent challenges and offer tailored cybersecurity solutions designed to integrate vulnerability assessments within your broader risk management and compliance frameworks. Our expert advisory and technical implementation services ensure your organization can identify risks early, prioritize remediation effectively, and build adaptive cyber resilience across your healthcare technology ecosystems. By partnering with us, healthcare leaders gain the strategic advantage of turning cybersecurity requirements into sustainable business strengths.
Explore how our managed cybersecurity, incident response, and compliance services can help you stay ahead in an evolving threat landscape. Secure your critical healthcare assets today with Heights Consulting Group.

Protect your patients and organization by embedding strategic vulnerability assessments into your cybersecurity program now. Visit Heights Consulting Group to learn more and take the first step toward resilient healthcare security. Also discover our full range of cybersecurity consulting services tailored for complex and regulated environments.
Frequently Asked Questions
What is a vulnerability assessment in healthcare?
A vulnerability assessment in healthcare is a structured evaluation that identifies, evaluates, and classifies potential security weaknesses within an organization’s digital infrastructure, focusing on protecting sensitive medical information and ensuring patient safety.
Why are vulnerability assessments critical for healthcare organizations?
Vulnerability assessments are essential for healthcare organizations to proactively identify security risks that can compromise patient data, disrupt operations, and impact patient care, allowing for the development of robust defensive strategies.
How often should vulnerability assessments be conducted in healthcare?
Healthcare organizations should conduct vulnerability assessments quarterly and immediately after significant infrastructure changes to ensure continuous security readiness and to address emerging threats effectively.
What types of vulnerabilities do healthcare assessments typically focus on?
Healthcare vulnerability assessments typically focus on three primary types: network infrastructure, medical device security, and application security, each addressing specific risks within the healthcare technology ecosystem.