TL;DR:
- Government agencies face increasingly targeted and severe cyber threats from nation-states and criminal groups that exploit outdated defenses. Implementing proactive cybersecurity frameworks and rigorous leadership oversight is essential to mitigate risks, ensure compliance, and foster organizational resilience. Acting now to assess and elevate security maturity helps agencies protect sensitive data, maintain public trust, and avoid costly breaches.
Government agencies now face a threat environment that is more aggressive, more targeted, and more consequential than at any prior point. Adversaries ranging from nation-state actors to financially motivated criminal groups actively probe agency networks for sensitive citizen data, classified records, and operational infrastructure. The assumption that existing perimeter defenses are sufficient is not just outdated; it actively invites risk. Phishing alone remains the dominant attack vector across organizations worldwide, and government entities are far from immune. This guide walks C-level leaders through the regulatory, operational, and strategic dimensions of cybersecurity, providing frameworks and actions that translate awareness into resilience.
Table of Contents
- The evolving cyber threat landscape for government agencies
- Regulatory requirements: Why compliance starts with cybersecurity
- From controls to outcomes: Strategic frameworks that work
- Building resilience: Steps for C-level leaders
- Perspective: The hidden cost of overlooking cybersecurity maturity
- Next steps: Strengthen your agency's cybersecurity posture
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Threats are constant | Government agencies remain primary targets for diverse cyberattacks affecting public trust and service continuity. |
| Compliance is foundational | Legal requirements mandate modern cybersecurity controls such as encryption and multi-factor authentication. |
| Frameworks drive results | Implementing strategic frameworks like NIST CSF turns compliance efforts into measurable security improvements. |
| Leadership matters | C-level executives must prioritize accountability, clear milestones, and resource allocation for resilience. |
| Partner for progress | Engaging external experts accelerates maturity and helps agencies stay ahead of evolving threats. |
The evolving cyber threat landscape for government agencies
The threat landscape facing government agencies today bears little resemblance to what it was even five years ago. Attack types have grown both more diverse and more sophisticated, with adversaries combining technical exploits, social engineering, and insider manipulation to overcome traditional defenses. Understanding this environment is the essential starting point for any serious cybersecurity investment decision.
Phishing remains the most disruptive and prevalent threat vector across sectors, and government agencies are prime targets due to the sensitivity of the data they hold. The Cyber Security Breaches Survey 2025/2026 documents the continued dominance of phishing as the attack type most likely to result in a material breach. The reality is that a single convincing email sent to the right employee can provide an adversary with the access needed to compromise an entire system.
The top threats currently targeting government agencies include:
- Phishing and spear phishing: Highly targeted email attacks designed to harvest credentials or deploy malware
- Ransomware: Attacks that encrypt critical systems and demand payment, often disabling citizen-facing services for days or weeks
- Insider threats: Malicious or negligent employees with privileged access who expose sensitive data intentionally or accidentally
- Supply chain compromises: Attacks that exploit third-party vendors or software to gain access to agency networks
These threats do not operate in isolation. A phishing campaign may be the entry point, while ransomware is the final payload. Understanding the cybersecurity best practices for CISOs means recognizing how attacks chain together and designing defenses that interrupt multiple stages of an attack lifecycle.
"When a government agency suffers a successful breach, the consequences extend far beyond operational disruption. Public trust erodes, citizen data is exposed, and the credibility of the institution itself comes under scrutiny. Recovery is measured not just in dollars but in years of rebuilding confidence."
Threat actors targeting agencies are often well-resourced. Nation-state groups invest heavily in reconnaissance, zero-day exploits, and persistent access techniques. Criminal organizations targeting government entities for financial gain have grown equally sophisticated. This is not an environment where minimal controls provide adequate protection, and agencies that are cybersecurity for government contractors must apply this same level of scrutiny across their extended contractor networks.
Regulatory requirements: Why compliance starts with cybersecurity
Compliance with federal cybersecurity mandates is not optional, but meeting minimum requirements should never be mistaken for actually being secure. Understanding what the law requires, and why those requirements exist, helps C-level leaders treat compliance as a baseline rather than a ceiling.
6 USC 1523) establishes clear obligations for agency heads: identify sensitive data, assess current security controls, encrypt sensitive data at rest and in transit, and enforce multi-factor authentication (MFA) for both privileged users and remote access. These are not abstract guidelines; they are statutory requirements with direct accountability for agency leadership.
The table below maps key compliance requirements to the security outcomes they are designed to achieve:
| Compliance requirement | Underlying security outcome |
|---|---|
| Multi-factor authentication (MFA) | Prevents credential theft from enabling unauthorized access |
| Data encryption at rest and in transit | Protects sensitive data even if storage or transmission is compromised |
| Role-based access controls | Limits damage from insider threats and credential compromise |
| Sensitive data inventory | Enables prioritized protection of highest-risk assets |
| Regular control assessments | Ensures defenses remain effective as threats evolve |
| Incident response planning | Reduces dwell time and limits breach impact |
Pro Tip: Treat each compliance control as a risk-reduction decision, not a paperwork exercise. When your team can articulate why a control exists and what risk it mitigates, audits become straightforward and the control actually gets implemented correctly rather than nominally.
The consequences of non-compliance extend well beyond a failed audit. Agencies risk legal liability, loss of federal funding, mandatory remediation timelines, and, critically, the kind of reputational damage that takes years to repair. Understanding compliance frameworks more broadly illustrates how organizations across sectors treat regulatory requirements as the foundation rather than the final word on security.

Building a cybersecurity strategy for compliance means designing controls that satisfy regulators today while also scaling to meet emerging requirements tomorrow. Frameworks that are bolted on reactively tend to create gaps precisely where auditors will look. A proactive approach, grounded in continuous risk assessment and documented control ownership, makes compliance sustainable rather than cyclical. Leaders who invest in building resilient cybersecurity frameworks position their agencies to absorb regulatory evolution without scrambling every time new guidance is issued.
From controls to outcomes: Strategic frameworks that work
Having clear legal requirements is one thing. Translating those requirements into day-to-day operational strength is another challenge entirely. Cybersecurity frameworks provide the structure that bridges the gap between policy and practice, turning abstract mandates into measurable, auditable outcomes.
The GSA Cybersecurity Framework aligns federal agency security programs with the NIST Cybersecurity Framework (CSF), providing a lifecycle approach to managing cyber risk. The five core functions of the NIST CSF are:
- Identify: Develop an understanding of systems, assets, data, and capabilities that require protection. This includes asset inventory, risk assessments, and governance structures.
- Protect: Implement safeguards to limit or contain the impact of potential cybersecurity events, covering access control, data security, and security awareness training.
- Detect: Develop and implement the capabilities necessary to identify cybersecurity events in a timely manner, including continuous monitoring and anomaly detection.
- Respond: Take action regarding a detected cybersecurity event. This function covers response planning, communications, analysis, mitigation, and improvement.
- Recover: Maintain plans for resilience and restore any capabilities or services that were impaired due to a cybersecurity event, including recovery planning and improvements.
The contrast between reactive and proactive approaches to these functions is significant and measurable:
| Dimension | Reactive approach | Proactive framework approach |
|---|---|---|
| Asset management | Ad hoc, incomplete inventory | Continuous, documented asset lifecycle |
| Threat detection | Alert-driven, post-breach discovery | Continuous monitoring, behavioral analytics |
| Incident response | Improvised, undocumented | Rehearsed, role-assigned, documented |
| Compliance readiness | Periodic scramble before audits | Continuous evidence collection |
| Recovery capability | Undefined, often lengthy | Tested, time-bound recovery objectives |
Using established frameworks makes executive-level reporting straightforward, investment prioritization defensible, and continuous improvement systematic. Leaders who reference top cybersecurity framework tips when planning adoption consistently achieve faster maturity gains than those who attempt to build custom approaches from scratch.
Pro Tip: Assign a named owner and a documented milestone to every framework function during adoption. Vague aspirations like "improve detection capability" produce vague results. A specific commitment such as "deploy SIEM coverage across all production systems by Q3 with the security operations lead accountable" produces measurable outcomes.
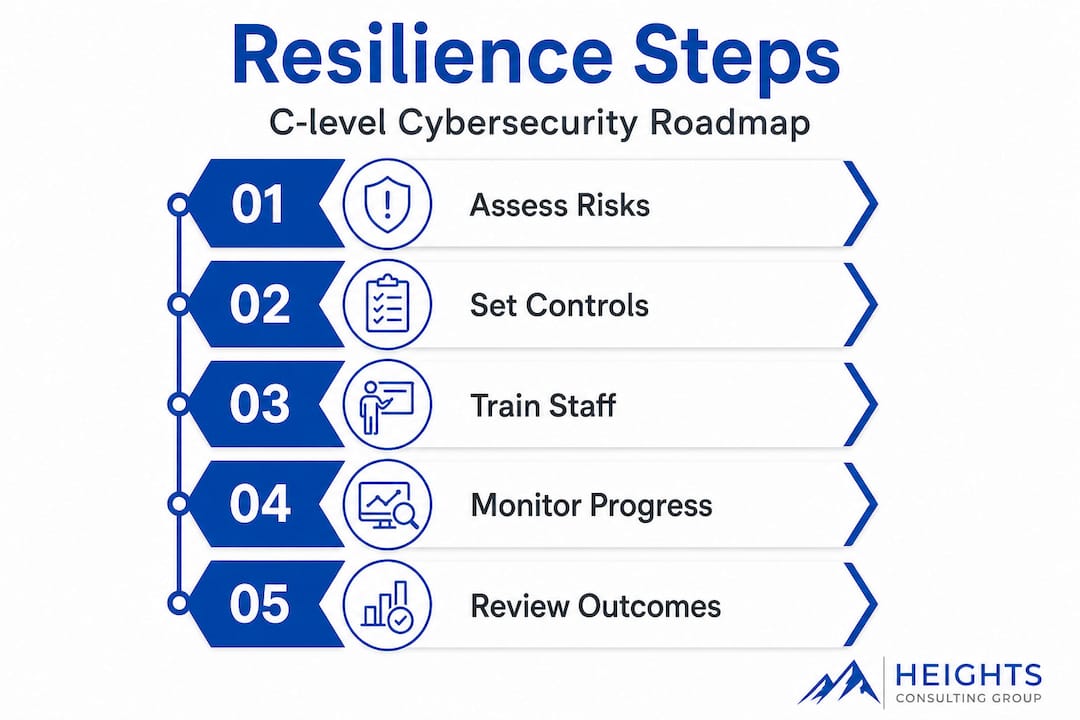
Building resilience: Steps for C-level leaders
Frameworks and controls create the architecture for security, but executive leadership drives the culture and accountability that make them work in practice. Moving from basic compliance toward genuine cyber resilience requires deliberate action from the top of the organization.
The following steps are the foundation of executive-led cyber resilience:
- Set explicit expectations: Define measurable security outcomes, not just activities. Establish what "good" looks like for detection time, response time, and recovery capability.
- Clarify and protect funding: Cybersecurity budgets that are routinely raided for other priorities signal that security is negotiable. Leadership must treat security investment as mission-critical infrastructure.
- Drive cross-agency ownership: Security is not solely the CISO's responsibility. Every agency head, program director, and system owner shares accountability for their piece of the security posture.
- Review progress with rigor: Quarterly reviews of key security metrics, not just compliance status, keep leadership informed and teams accountable. Use dashboards that show threat exposure, not just checkbox completion.
- Test assumptions through exercises: Tabletop exercises and red team assessments reveal gaps that documentation never will. Build these into the annual operating calendar.
Common pitfalls that undermine even well-intentioned security programs include:
- Lack of specificity: Plans that describe aspirations without milestones or assigned owners produce inconsistent results
- Diffuse responsibility: When everyone is accountable, no one is accountable; clear role assignments are essential
- Underestimating resource needs: Security programs routinely fail because they are scoped without realistic staffing and technology budgets
- Treating security as an IT issue only: Operational, legal, and communications functions all have roles in resilience
- Neglecting the basics: MFA, patch management, and asset inventory remain common gaps behind major breaches
"Cyber strategy effectiveness depends on execution detail, not just intent. Agencies should evaluate whether their plans specify milestones, responsibilities, and funding commitments, rather than aspirations alone." This perspective, consistent with assessments of national cyber strategy plans, applies directly to agency-level planning.
The cybersecurity checklist for executives provides a practical starting point for leaders who want to assess their current posture before committing to a roadmap. For those ready to elevate the governance dimension, boardroom cybersecurity governance offers frameworks that integrate security decision-making into agency leadership structures.
Perspective: The hidden cost of overlooking cybersecurity maturity
There is a pattern that surfaces repeatedly in agencies that suffer significant breaches: leadership treated cybersecurity as a compliance obligation to be discharged at minimum cost rather than a capability to be developed with intention. The consequences are predictable and expensive.
The conventional wisdom of "meet the minimum and move on" creates a dangerous illusion of protection. Each year that an agency defers investment in detection capabilities, staff training, or incident response readiness is a year that adversaries are gaining ground. The compounding effect is real: deferred security investment does not simply pause risk; it amplifies it, because threats continue to evolve while defenses stagnate.
In our experience working with regulated agencies, the weak link behind the majority of significant incidents is almost never a sophisticated zero-day exploit. It is a missed MFA deployment, an incomplete asset inventory, or a response plan that has never been tested. These are not exotic failures; they are organizational failures rooted in the assumption that basic measures are sufficient. They are not.
Investing beyond the basics produces measurable improvements that extend well past technical metrics. Agencies with mature security programs detect threats faster, contain incidents with less operational disruption, and recover with fewer resources expended. Critically, they also maintain public trust more effectively because their communications during and after an incident are credible, informed, and transparent.
The call to action for every C-level leader reading this is specific: initiate a security maturity audit now. Not after a budget cycle. Not after the next compliance review. A structured maturity assessment using your cybersecurity resilience strategy as a baseline will tell you exactly where your gaps are, what they cost you in risk exposure, and what investments will generate the highest return in terms of reduced likelihood and impact of a significant incident. The agencies that act before a security event are the ones that avoid making headlines for the wrong reasons.
Next steps: Strengthen your agency's cybersecurity posture
The path from reading this guide to building a genuinely resilient cybersecurity program requires more than awareness. It requires partners who understand both the technical requirements and the operational realities of government environments.

Heights Consulting Group works directly with C-level leaders and agency security teams to move from compliance checklists to strategic cyber resilience. Whether your agency needs help standing up a managed cybersecurity services program that provides continuous protection without requiring a fully built-in-house SOC, or support developing a cybersecurity strategy for compliance that satisfies regulators while actually reducing risk, our team brings the framework expertise and implementation depth to deliver results. Contact us today to schedule a strategic consultation and start turning executive intent into demonstrable security outcomes.
Frequently asked questions
Are there specific laws that mandate cybersecurity for U.S. government agencies?
Yes, federal regulations such as 6 USC 1523) require agencies to adopt controls like MFA, encryption, and role-based access to protect sensitive data. These are statutory obligations, not advisory guidelines, carrying direct accountability for agency leadership.
What's the difference between compliance and true cybersecurity?
Compliance meets the minimum legal standards, while true cybersecurity protects operations by addressing evolving threats and building resilience. The GSA Cybersecurity Framework helps agencies translate compliance requirements into measurable security outcomes that go beyond checkbox satisfaction.
Which attacks are most common against government agencies?
Phishing, ransomware, and insider threats are among the most frequent and disruptive attacks encountered. The Cyber Security Breaches Survey 2025/2026 confirms phishing as the dominant attack type most likely to result in a material breach across all sectors including government.
How do cybersecurity frameworks help agencies?
Frameworks like the NIST CSF provide a structured lifecycle covering Identify, Protect, Detect, Respond, and Recover, enabling agencies to manage cyber risk systematically rather than reactively. They also make audits, investment decisions, and performance reporting significantly more straightforward for leadership teams.
Recommended
- 7 Government Cybersecurity Best Practices for CISOs
- A Guide to Cybersecurity for Government Contractors - Heights Consulting Group
- Cybersecurity Strategy: Heights Consulting's Executive Guide
- Aligning Cybersecurity with Business Objectives for Growth - Heights Consulting Group
- Security in High-Risk Banking – Ensuring Compliance and Protection
