TL;DR:
- Sophisticated adversaries target endpoints due to their critical role and vulnerabilities in modern architectures.
- EDR solutions provide behavioral monitoring, threat hunting, automated response, and forensic logging.
- Effective deployment requires organizational commitment, strategic planning, and continuous tuning for maximum protection.
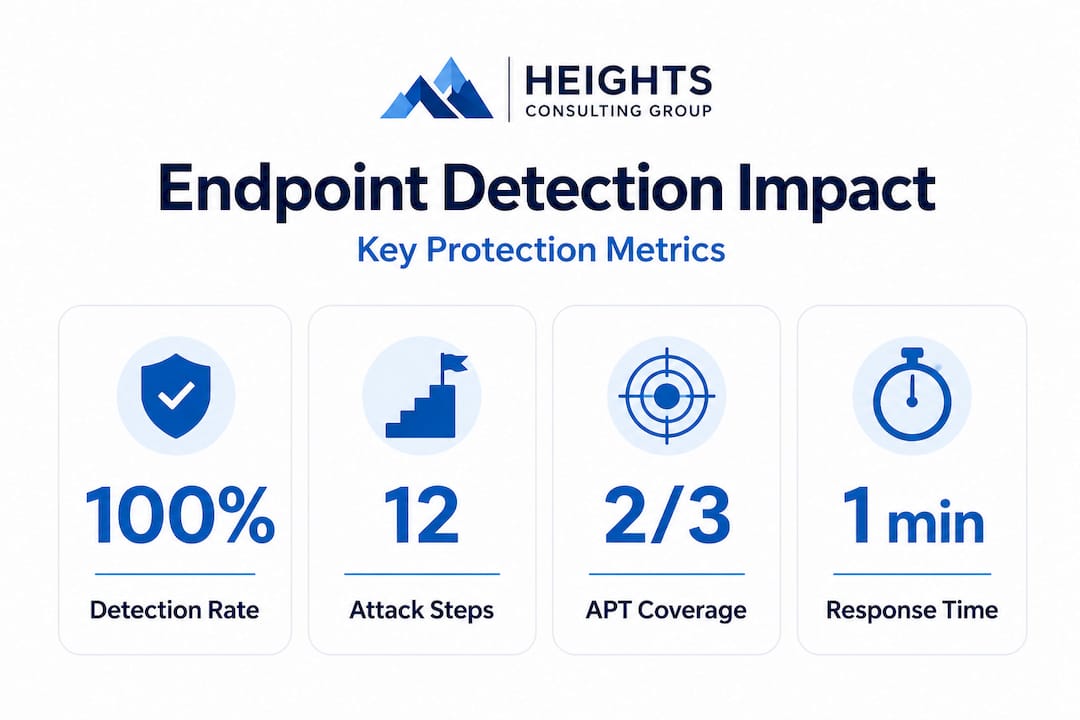
Sophisticated threat actors no longer batter the front gate. They slip in through laptops, mobile devices, and remote workstations, bypassing perimeter defenses that most regulated organizations still rely on as their primary shield. Certified EDR solutions now detect at least two-thirds of advanced persistent threat attack steps in rigorous independent testing, yet many enterprises continue to operate with legacy antivirus as their endpoint strategy. For C-level executives and security leaders in healthcare, finance, defense contracting, and other regulated sectors, that gap is not a technical footnote. It is an operational and compliance liability that demands immediate strategic attention.
Table of Contents
- The cybersecurity landscape in regulated industries
- What makes endpoint detection so critical?
- How EDR stops advanced threats: A closer look
- Best practices for deploying endpoint detection in your organization
- What most executives miss about endpoint detection
- Drive strategic security outcomes with expert guidance
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Regulated industries face new threats | Sophisticated attacks bypass legacy tools, demanding modern endpoint strategies. |
| EDR bridges major security gaps | Endpoint detection provides real-time visibility and rapid threat response standard AV cannot. |
| Compliance demands detection capability | Effective endpoint detection is now a must for regulatory frameworks and risk management. |
| Deployment must be strategic | Successful endpoint programs require board-level support, integration, and ongoing optimization. |
| Expert guidance accelerates results | Leaders can drive better security and compliance through managed services and consultancy. |
The cybersecurity landscape in regulated industries
Regulated industries operate under a fundamentally different threat calculus than the general enterprise market. A data breach in a hospital system does not just trigger remediation costs. It triggers HIPAA investigations, potential civil penalties, patient notification requirements, and reputational damage that can erode years of trust. A defense contractor that experiences an undetected endpoint compromise may face CMMC decertification, contract loss, and national security implications. The stakes are categorically higher, and the adversaries know it.
Threat actors specifically target endpoints because those devices sit at the intersection of user behavior, sensitive data, and network access. Perimeter defenses such as firewalls and intrusion detection systems were designed for a network architecture that no longer exists at scale. Remote work, cloud adoption, and third-party integrations have dissolved the traditional boundary. Attackers exploit this reality by targeting endpoints to move laterally, escalate privileges, and exfiltrate data before any alert fires.
"The endpoint is where the human meets the network, and it remains the most exploited attack surface in regulated industries. Protecting it requires more than signature-based detection. It requires behavioral intelligence."
Compliance frameworks have responded to this reality. NIST SP 800-171, CMMC Level 2 and above, HIPAA Security Rule technical safeguards, and SOC 2 Type II all include explicit or implied requirements for continuous monitoring, anomaly detection, and incident response capabilities at the endpoint level. Traditional antivirus, which relies on known malware signatures, cannot satisfy these requirements against modern adversaries using fileless malware, living-off-the-land techniques, and zero-day exploits. Following endpoint security best practices is no longer optional for organizations subject to these frameworks.
Key risks that regulated organizations face without effective endpoint detection include:
- Undetected lateral movement that allows attackers to access sensitive systems for weeks or months before discovery
- Compliance audit failures resulting from inability to demonstrate continuous monitoring and evidence of threat response
- Regulatory fines and sanctions tied directly to insufficient technical safeguards at the endpoint level
- Operational disruption from ransomware or destructive attacks that could have been contained at the initial compromise point
- Reputational damage that compounds financial losses and undermines client and partner confidence
Independent testing confirms that EPR tests show 100% protection and detection rates across multiple phases for leading products, a standard that legacy antivirus simply cannot meet. Organizations that align cybersecurity with enterprise strategy recognize that endpoint protection is not a cost center. It is a risk management investment with measurable returns. Reviewing cybersecurity best practices for modern businesses reinforces that endpoint security is foundational, not supplemental.
With the stakes established, it is vital to understand exactly what endpoint detection offers beyond traditional defenses.
What makes endpoint detection so critical?
Endpoint Detection and Response, commonly referred to as EDR, represents a fundamental shift in how organizations monitor and protect their devices. Rather than relying on a database of known malicious signatures, EDR platforms continuously collect and analyze behavioral telemetry from every endpoint. This means the system can identify suspicious patterns, such as a process attempting to access credential stores or an application spawning unexpected child processes, even when no known malware signature is present.
The criticality of EDR stems from five core capabilities that legacy tools simply do not provide:
- Real-time behavioral monitoring. EDR agents observe process execution, file system changes, network connections, and registry modifications continuously. This visibility enables detection of threats that operate entirely in memory or use legitimate system tools to carry out malicious activity.
- Threat hunting support. Security teams can proactively query endpoint telemetry to search for indicators of compromise that automated alerts may have missed. This is particularly valuable for identifying advanced persistent threats that operate slowly and deliberately to avoid triggering thresholds.
- Automated response and containment. When a threat is confirmed, EDR platforms can isolate the affected endpoint from the network, terminate malicious processes, and roll back unauthorized changes, all without waiting for human intervention.
- Forensic evidence collection. Every action taken by a threat actor is logged with timestamps, process chains, and network connections. This forensic trail is essential for compliance reporting, regulatory investigations, and post-incident analysis.
- Integration with compliance frameworks. EDR telemetry maps directly to control requirements in NIST, CMMC, HIPAA, and SOC 2, providing the continuous monitoring evidence that auditors require.
Certified EDR solutions detect at least two-thirds of APT attack steps across 12-step MITRE ATT&CK scenarios with low false positives, a performance level that directly addresses the alert fatigue problem that plagues security operations teams. Fewer false positives mean analysts focus on real threats rather than chasing noise. Understanding the difference between EDR versus antivirus is essential for executives making investment decisions, because the capability gap is substantial. Organizations exploring AI-powered protection will find that modern EDR platforms increasingly incorporate machine learning to improve detection accuracy over time.
Pro Tip: When evaluating EDR vendors, request independent test results from organizations like AV-Comparatives or MITRE ATT&CK Evaluations. Vendor-provided benchmarks rarely reflect real-world performance against sophisticated adversaries. Use the endpoint detection strategy guide to structure your evaluation criteria before engaging vendors.
Knowing its criticality, executives need to see how endpoint detection functions in real-world complex scenarios.
How EDR stops advanced threats: A closer look
Advanced persistent threats do not announce themselves. They move methodically through the MITRE ATT&CK framework, from initial access through execution, persistence, privilege escalation, lateral movement, and ultimately data exfiltration. Each stage presents a detection opportunity that EDR platforms are specifically designed to exploit.

Consider a realistic attack scenario in a financial services firm. An attacker sends a spear-phishing email that delivers a malicious macro. The user opens the document, and the macro executes PowerShell commands in memory, never touching the disk in a way that signature-based tools would flag. The attacker then uses legitimate Windows administrative tools to move laterally toward a database server containing customer financial records. At every stage, the EDR platform is collecting behavioral telemetry, correlating events across endpoints, and building a threat timeline that security analysts can act on.
| Capability | Traditional antivirus | EDR platform |
|---|---|---|
| Signature-based detection | Yes | Yes |
| Behavioral analysis | No | Yes |
| Fileless malware detection | No | Yes |
| Real-time threat hunting | No | Yes |
| Automated containment | No | Yes |
| Forensic evidence logging | Limited | Comprehensive |
| MITRE ATT&CK mapping | No | Yes |
| Compliance reporting support | Minimal | Extensive |
The performance data from independent testing makes the case clearly. EPR tests show 100% protection and detection rates across multiple attack phases for leading EDR products, while traditional antivirus solutions consistently fail to detect fileless and living-off-the-land attacks that now represent the majority of enterprise breaches.
Pro Tip: Deployment without tuning is one of the most common and costly mistakes organizations make with EDR. Out-of-the-box configurations generate excessive alerts and miss context-specific threats. Work with your security team or a managed security partner to calibrate detection rules against your specific environment, user behavior baselines, and regulatory context. This tuning process, combined with advanced threat detection capabilities, is what separates effective EDR deployments from expensive shelfware.
The speed of containment matters enormously. Organizations that prevent costly breaches through proactive monitoring demonstrate that early detection and automated response can reduce breach containment time from weeks to hours. In regulated industries, that difference translates directly to reduced regulatory exposure and lower incident response costs. Understanding the full capability comparison between EDR versus antivirus helps security leaders build a compelling business case for the board.
This effectiveness leads organizations to wonder how they can integrate and operationalize endpoint detection effectively.
Best practices for deploying endpoint detection in your organization
Effective EDR deployment is not a technology project. It is an organizational initiative that requires executive sponsorship, cross-functional coordination, and ongoing operational commitment. The following steps provide a structured path for C-level leaders and IT security teams.
- Conduct a baseline endpoint security assessment. Before selecting or deploying an EDR solution, organizations must understand their current coverage gaps, device inventory, and existing detection capabilities. Use a structured process to assess endpoint security across all device types, including managed, unmanaged, and third-party endpoints.
- Map EDR capabilities to your compliance framework. Identify which specific controls in NIST, CMMC, HIPAA, or SOC 2 your EDR deployment will satisfy. Document this mapping before deployment so that compliance evidence collection is built into the process from the start.
- Define detection and response playbooks. EDR platforms generate alerts, but human decisions determine outcomes. Develop documented playbooks for the most likely threat scenarios in your industry, including ransomware, credential theft, and insider threats.
- Integrate EDR with your broader security architecture. Effective endpoint detection does not operate in isolation. Connect EDR telemetry to your SIEM (Security Information and Event Management) platform, identity management systems, and network monitoring tools to achieve correlated visibility across the attack surface.
- Establish continuous monitoring and tuning cadences. Threat actors evolve their tactics continuously. Proactive cybersecurity monitoring requires scheduled reviews of detection rules, false positive rates, and emerging threat intelligence to keep EDR configurations effective.
Common pitfalls that undermine EDR deployments include:
- Coverage gaps from unmanaged or shadow IT devices that fall outside the EDR agent deployment
- Alert fatigue caused by poorly tuned detection rules that generate hundreds of low-fidelity alerts per day
- Insufficient staff training that leaves analysts unable to interpret EDR telemetry or execute response playbooks effectively
- Lack of executive visibility into endpoint security metrics, which prevents informed resource allocation decisions
- Failure to align with cloud environments, where cloud security best practices must extend endpoint detection to cloud workloads and virtual machines
Certified EDR solutions detect at least two-thirds of advanced attack steps in independent testing, but that detection capability only translates into organizational protection when the deployment is complete, the team is trained, and the response process is operational. Following endpoint security best practices throughout the deployment lifecycle ensures that the investment delivers its full protective value.
By understanding these concrete steps, leaders can confidently drive risk reduction and measurable return on investment from endpoint detection.
What most executives miss about endpoint detection
The most common executive misconception about endpoint detection is that it is a compliance checkbox. Purchase the tool, deploy the agent, check the box, pass the audit. This framing fundamentally misunderstands both the threat environment and the opportunity that EDR represents.
Endpoint detection, when properly deployed and operationalized, is one of the most powerful sources of organizational intelligence that a security program can generate. The behavioral telemetry collected by EDR platforms reveals not just active threats but also the patterns of user behavior, application usage, and network communication that define your organization's normal operating baseline. That baseline is the foundation of every meaningful security decision, from access control policy to incident response prioritization.
The organizations that treat EDR as a strategic capability rather than a compliance tool gain a measurable competitive advantage. They detect breaches faster, contain them more effectively, and produce the forensic evidence that regulators and cyber insurers increasingly require. They also build the institutional knowledge to improve their security posture continuously, rather than reacting to incidents after the fact.
There is also an uncomfortable truth about the "good enough" mentality that persists in many regulated organizations. Passing a compliance audit with a legacy antivirus deployment does not mean the organization is protected. It means the auditor accepted the documentation. Sophisticated adversaries do not read audit reports. They probe for behavioral gaps that signature-based tools cannot detect, and they exploit those gaps methodically. Transforming cybersecurity from a reactive posture to a proactive one requires treating endpoint maturity as a board-level metric, not a technical detail delegated entirely to the IT team.
Measuring endpoint maturity means tracking detection coverage across the MITRE ATT&CK framework, monitoring mean time to detect and respond, and reviewing false positive rates as indicators of operational efficiency. These metrics tell the board a story about organizational resilience that compliance audit results alone cannot convey.
Drive strategic security outcomes with expert guidance
Endpoint detection is a strategic priority, and translating that priority into operational reality requires more than technology. It requires expertise, process design, and continuous management that most internal teams are not resourced to provide alone.

Heights Consulting Group works with C-level executives and security leaders in regulated industries to design, implement, and manage endpoint detection programs that satisfy both security and compliance requirements. Our cybersecurity consulting services include endpoint security assessments, EDR vendor selection, deployment planning, and compliance mapping across NIST, CMMC, HIPAA, and SOC 2 frameworks. For organizations that need continuous operational coverage, our managed cybersecurity services provide 24/7 monitoring, threat hunting, and incident response built around your specific regulatory environment. Contact Heights CG to start the conversation about strengthening your endpoint security posture.
Frequently asked questions
How does endpoint detection improve compliance in regulated industries?
Endpoint detection provides the continuous monitoring and forensic evidence most compliance frameworks require, with certified EDR solutions detecting at least two-thirds of advanced attack steps, ensuring early threat detection and the audit-ready reporting that regulators expect.
Are all endpoint detection solutions equally effective against APTs?
Not all solutions are equal. Leading EDR platforms demonstrated detection of at least two-thirds of advanced attacks in independent AV-Comparatives testing, but effectiveness, false positive rates, and response capabilities vary significantly across vendors.
What's the main difference between EDR and traditional antivirus?
EDR offers real-time behavioral monitoring, threat hunting, and automated response capabilities, while traditional antivirus relies on known malware signatures and cannot detect unknown, fileless, or advanced threats with comparable effectiveness.
What are the signs our organization needs better endpoint detection?
High alert volume with unclear action steps, unresolved incidents that linger without containment, and gaps in compliance reporting around continuous monitoring are clear signals that your current endpoint detection and response capabilities need improvement.
Can endpoint detection reduce overall cyber risk for enterprise organizations?
Yes. EPR tests show 100% protection and detection rates across multiple attack phases for leading EDR products, translating directly into faster breach containment, reduced regulatory exposure, and lower overall cyber risk for enterprise organizations.
Recommended
- Endpoint detection strategy guide for executives 2026
- Endpoint Security Best Practices for Risk Reduction
- Endpoint Detection and Response vs Antivirus in the AI Era - Heights Consulting Group
- What is Endpoint Security? Protect Data & Meet Compliance | Symmetry Network Management
- Cybersecurity Tools Every Business Needs
