TL;DR:
- Cybersecurity is a critical business risk impacting costs, reputation, and regulatory compliance.
- Executives must integrate cyber risk management into overall business strategy and risk tolerance.
- Supply chain security and human factors are key areas for board-level oversight and proactive mitigation.
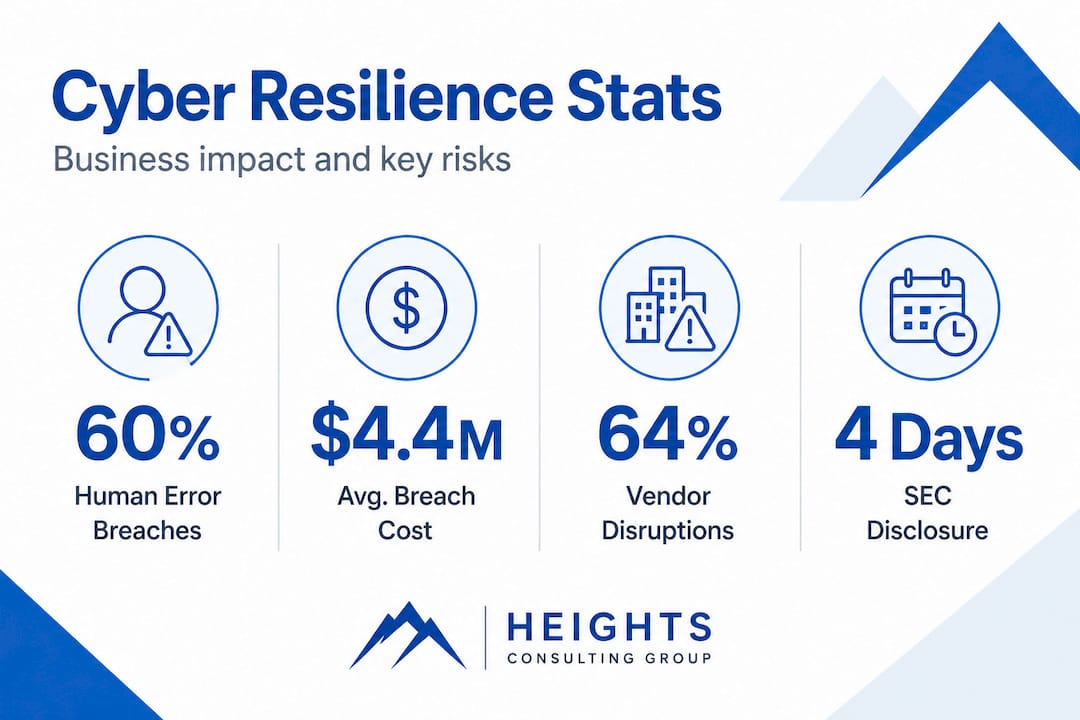
Cybersecurity is no longer a back-office concern managed quietly by IT teams. Breaches cost organizations an average of $4.4 million globally, factoring in regulatory fines, legal fees, operational downtime, and lasting reputational damage. That figure alone reframes cybersecurity as a material business risk, one that sits squarely on the agenda of every CEO, CFO, and board member. This article connects the dots between financial exposure, regulatory accountability, strategic risk integration, and supply chain governance to give C-level executives a clear roadmap for leading with security.
Table of Contents
- Security as a material business risk for executives
- Regulatory accountability: SEC rules, NIST CSF, and C-level exposure
- Integration: Embedding cyber risk management into business strategy
- Supply chain and third-party risks: The weakest link
- Beyond compliance: What most executives miss about cyber resilience
- Take the next step: Elevate your cybersecurity leadership
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cyber risk is a board issue | Security incidents are now material business risks that require direct oversight from C-levels and boards. |
| Regulatory demands require speed | SEC rules mandate rapid breach disclosure and rigorous annual reporting, driving executive accountability. |
| Integrated strategy drives resilience | Aligning cyber risk quantification with business goals empowers informed executive decision-making and enterprise-wide protection. |
| Supply chain is a major vulnerability | Third-party risks often lead to recurring breaches and require diligent governance from senior leadership. |
| Leadership goes beyond compliance | True cyber resilience comes from explicit risk tolerance and cross-functional ownership, not just regulatory checklists. |
Security as a material business risk for executives
The days of treating cybersecurity as a purely technical discipline are over. When a breach occurs, the consequences ripple far beyond the IT department, touching investor relations, customer trust, regulatory standing, and long-term strategic positioning. C-levels who still delegate cyber risk entirely to their security teams are accepting exposure they may not fully understand.
The numbers make the case plainly. Cybersecurity budgets average $24 million in regulated industries, and 66% of organizations in those sectors report increased cybersecurity incidents year over year. High-performing organizations distinguish themselves by briefing C-levels and boards monthly or quarterly, treating security posture as an ongoing business metric rather than an annual audit exercise.
| Risk category | Typical financial impact | Executive exposure |
|---|---|---|
| Regulatory fines | $500K to $10M+ | Direct CEO/board liability |
| Legal and litigation costs | $1M to $5M | General counsel involvement |
| Operational downtime | $100K to $1M per day | COO and CFO accountability |
| Reputational damage | Long-term revenue loss | Brand and investor relations |
| Breach notification costs | $250K to $1M | Compliance and legal teams |
"Cybersecurity is no longer a technology problem. It is a business problem with technology dimensions, and the board is now the last line of accountability." This shift in perspective is what separates organizations that recover quickly from those that spend years rebuilding trust.
The most consequential change in recent years is not the sophistication of attacks. It is the speed at which AI-driven security updates are forcing organizations to adapt, compressing response timelines and raising the bar for what qualifies as reasonable executive oversight. C-levels who understand this dynamic can make faster, better-informed decisions when incidents occur.
Key material risks that every executive should track include:
- Regulatory penalties tied to data protection laws such as HIPAA, GDPR, and state-level privacy statutes
- Contractual liability when third-party agreements require specific security standards
- Market capitalization loss following public breach disclosures
- Talent and operational disruption caused by ransomware or system outages
- Supply chain cascades that amplify a single vendor compromise across the enterprise
Developing boardroom-ready cybersecurity capabilities means translating these risks into language that resonates with board directors and investors, not just security analysts. The role of security advisory in cybersecurity strategy has expanded precisely because executives need trusted advisors who can bridge the gap between technical realities and business decisions.
Pro Tip: Treat cybersecurity risk the same way you treat financial or legal risk. Assign ownership, set thresholds, require regular reporting, and escalate material issues to the board. If your security team cannot produce a risk summary in business terms, that is a governance gap worth closing immediately.
Regulatory accountability: SEC rules, NIST CSF, and C-level exposure
Having established why cybersecurity is more than an IT concern, the regulatory context that holds C-levels accountable deserves direct attention. Two frameworks now define the minimum standard for executive governance: the SEC's cybersecurity disclosure rules and NIST Cybersecurity Framework 2.0.
The SEC requires public companies to disclose material cybersecurity incidents within 4 business days and to detail risk management strategy and governance in annual 10-K filings. CEOs and boards face direct accountability for the accuracy and timeliness of those disclosures.
NIST CSF 2.0 introduced a Govern function that explicitly requires C-levels to establish cybersecurity risk strategies, define roles and responsibilities, and integrate security into enterprise-wide risk management. This is not optional guidance. For organizations subject to federal contracting, CMMC, or FedRAMP requirements, it carries real compliance weight.
| Requirement | SEC cybersecurity rules | NIST CSF 2.0 |
|---|---|---|
| Incident disclosure | 4 business days for material incidents | Respond and recover functions |
| Annual reporting | 10-K risk management and governance | Govern function documentation |
| Board oversight | Explicit board accountability | Organizational roles and policies |
| Risk strategy | Disclose strategy to investors | Integrate into enterprise risk |
| Applicability | Public companies | All organizations, federal contractors |
Here are the core governance steps every C-level should implement to satisfy both frameworks:
- Establish a cybersecurity risk committee that includes the CEO, CFO, General Counsel, and CISO, meeting at least quarterly.
- Define materiality thresholds for cybersecurity incidents in writing, so disclosure decisions are made on clear criteria rather than judgment calls under pressure.
- Document the risk management strategy in a format suitable for 10-K inclusion and board review.
- Map NIST CSF 2.0 Govern requirements to existing enterprise risk management policies and identify gaps.
- Conduct annual tabletop exercises that simulate a material breach and walk through the disclosure process with legal counsel present.
- Assign board-level oversight to a specific director or audit committee with defined cybersecurity competency requirements.
A well-structured regulatory compliance guide gives executives the scaffolding to meet these requirements without building every process from scratch. Organizations that treat compliance as a cybersecurity compliance advantage rather than a burden consistently outperform peers in both security posture and investor confidence. Establishing information security policies that align with these regulatory demands is a foundational step that many organizations overlook until an incident forces the issue.
Integration: Embedding cyber risk management into business strategy
Understanding regulatory requirements sets the stage for the more ambitious goal: integrating cyber risk into business strategy as a genuine competitive advantage. This requires moving beyond compliance checkboxes and into the discipline of risk quantification.

The FAIR model (Factor Analysis of Information Risk) offers a structured approach to expressing cyber risk in financial terms. Unlike traditional qualitative assessments that produce red, yellow, and green heat maps, FAIR produces dollar-denominated outputs that align directly with how boards and CFOs evaluate business risk. CISOs must evolve from technical roles into business risk strategists, quantifying cyber risks using models like FAIR to meet board expectations and align with enterprise risk management frameworks.
| Dimension | Traditional risk assessment | FAIR model |
|---|---|---|
| Output format | Red/yellow/green heat map | Dollar-denominated loss estimates |
| Board alignment | Limited, requires translation | Direct, speaks financial language |
| Decision support | Prioritization by severity | Cost-benefit analysis of controls |
| Scenario modeling | Qualitative descriptions | Probabilistic financial scenarios |
| Audit defensibility | Moderate | High, structured methodology |
The FAIR model in finance has gained significant traction in financial services, where regulators and boards already expect quantified risk reporting. The same discipline applies across healthcare, defense contracting, and critical infrastructure sectors.
Here is a practical sequence for embedding cyber risk into business strategy:
- Inventory your critical assets by business value, not just technical classification. Ask which systems, if compromised, would cause the most material harm.
- Apply FAIR analysis to your top five threat scenarios, producing a range of probable annual loss exposure for each.
- Present findings in financial terms during board reporting, alongside existing financial and operational risk metrics.
- Align security investment decisions to the risk reduction value they deliver, measured in reduced expected loss.
- Integrate cyber risk into M&A due diligence, capital allocation decisions, and strategic planning cycles.
Aligning cybersecurity with business goals is not a one-time exercise. It requires ongoing calibration as the threat landscape, regulatory environment, and business strategy evolve. Building a cybersecurity culture in the C-suite ensures that risk awareness permeates strategic decisions at every level, not just in the security team.
Pro Tip: When preparing board-level cybersecurity reporting, lead with business impact, not technical metrics. Replace "we blocked 2 million threats last month" with "our controls reduced expected annual loss exposure by $3.2 million this quarter." That framing drives better resource allocation decisions.
Supply chain and third-party risks: The weakest link
Strategic integration leads directly into one of the most underestimated risk domains for C-levels: supply chain and third-party security. Even organizations with mature internal controls can be severely compromised through a vendor, contractor, or software provider.
The scale of the problem is significant. Third-party risks cause an average of 12 breaches per year per organization, with operational disruptions affecting 64% of impacted companies and financial loss reported by 52%. These are not edge cases. They are recurring, predictable events that demand board-level governance.
Key third-party risk sources and mitigation actions:
- Software and SaaS vendors: Require SOC 2 Type II reports and conduct annual security reviews for all critical vendors.
- Managed service providers (MSPs): Verify that MSPs maintain their own security certifications and conduct penetration testing.
- Cloud infrastructure providers: Understand the shared responsibility model and confirm your organization fulfills its side of the security equation.
- Contractors and temporary staff: Enforce least-privilege access and revoke credentials immediately upon contract termination.
- Subcontractors in the supply chain: Extend your vendor risk assessment program to tier-2 and tier-3 suppliers for high-value contracts.
- Open-source software components: Maintain a software bill of materials (SBOM) to track vulnerabilities in third-party code embedded in your products.
Operational disruptions from third-party breaches can cascade quickly. A compromised payroll vendor can expose employee data. A breached logistics partner can halt operations. A vulnerable software library can open your entire product suite to exploitation. The 2020 SolarWinds incident remains the defining case study, demonstrating how a single vendor compromise can affect thousands of downstream organizations simultaneously.
Enhancing governance with virtual CISO services is one practical way organizations address the oversight gap in third-party risk management, particularly when internal security leadership lacks the bandwidth to manage a growing vendor ecosystem.
Pro Tip: Build supply chain risk reviews into your board-level governance calendar. Require quarterly reporting on the top 10 critical vendors, including any changes in their security posture, audit status, or incident history. This single practice can prevent the kind of surprise that turns a vendor's problem into your organization's crisis.
Beyond compliance: What most executives miss about cyber resilience
Here is the perspective that most cybersecurity articles avoid stating plainly: compliance is a floor, not a ceiling, and organizations that confuse the two are building a false sense of security.
Human error causes 60% of breaches, and no compliance framework eliminates that risk. CISOs do not have the authority or the organizational reach to stop every attack alone. The decisions that matter most, such as how much risk to accept, which business processes to protect above all others, and how to respond when controls fail, belong to the C-suite.
True resilience requires proactive risk-taking and cross-functional alignment that goes well beyond siloed security teams. That means the CFO owns the financial risk tolerance conversation. The COO owns operational recovery planning. The General Counsel owns disclosure readiness. The CEO owns the culture that determines whether employees report suspicious activity or hide it out of fear.
What we consistently observe is that organizations with the strongest cyber resilience share one trait: explicit, documented risk tolerance set by the executive team, not inherited from a compliance framework. They know what they are willing to lose, what they are not willing to lose, and they have made deliberate investments based on that clarity. The alignment of cybersecurity with business objectives is not a security team initiative. It is an executive leadership responsibility.
The uncomfortable truth is that many C-levels are still waiting for their CISO to tell them when they are secure. That question has no satisfying answer. The better question is: "Given our risk tolerance, are we making the right investments and decisions?" That reframe is where genuine resilience begins.
Take the next step: Elevate your cybersecurity leadership
The strategic insights in this article reflect the real challenges we help C-level executives and security leaders navigate every day. Translating cyber risk into business terms, meeting SEC and NIST requirements, and building supply chain governance are not abstract goals. They are achievable with the right advisory partner.

Heights Consulting Group specializes in helping executives move from reactive compliance to proactive resilience. Whether you need technical cybersecurity consulting to assess your current posture, a strategic framework to align security with business objectives, or guidance on strategic cybersecurity solutions that turn risk into competitive advantage, our team brings the executive-level perspective your organization needs. Contact Heights CG today to schedule a strategic consultation tailored to your industry and risk profile.
Frequently asked questions
What is the average financial impact of a security breach for C-levels?
The average global cost per breach is $4.4 million, covering regulatory fines, legal fees, operational downtime, and reputational damage that can persist for years.
What are the SEC's requirements for cybersecurity incident disclosure?
Public companies must disclose material incidents within 4 business days and include risk management strategy and governance details in their annual 10-K filings, with direct accountability assigned to CEOs and boards.
How can C-levels quantify cyber risk for board reporting?
Executives can apply the FAIR model to express cyber risks in dollar-denominated terms, integrating those outputs directly into enterprise risk management dashboards and board reporting cycles.
Why is supply chain security critical for C-levels?
Third-party risks produce an average of 12 breaches per year per organization, with 64% causing operational disruptions and 52% resulting in direct financial loss, making vendor governance a board-level priority.
What is the top reason for cybersecurity breaches?
Human error accounts for 60% of breaches, which is why C-levels must define explicit risk tolerance and foster cross-functional accountability rather than relying solely on the CISO to prevent every incident.
