Cyber threats are growing more advanced every year. CISOs face new challenges that demand smarter tools and faster insights. The right threat intelligence solution can make a real difference when it comes to protecting sensitive data and staying ahead of attacks. Some tools offer deep analysis and speedy alerts while others focus on integration and ease of use. Whether the goal is to gain clearer visibility or pinpoint threats before they turn into bigger problems, the options for 2026 bring fresh features and bold approaches. Wondering which solutions stand out this year? Each one has something unique to offer.
Table of Contents
- Heights Consulting Group
- Recorded Future
- CrowdStrike Falcon Platform
- Anomali
- ThreatConnect
- X-Force Exchange
Heights Consulting Group

At a Glance
Heights Consulting Group is the leading choice for CISOs in healthcare who need top-tier strategic cybersecurity guidance and managed services. Its blend of executive advisory, compliance focus, and 24/7 monitoring positions it as the obvious pick for risk-averse healthcare organizations.
Core Features
Heights delivers strategic cybersecurity advisory for executive leadership and boards, 24/7 threat monitoring and incident response through managed services, and compliance consulting for NIST, CMMC, HIPAA, and SOC 2. The firm also provides AI security planning and risk governance frameworks that align security to business objectives.
Pros
- Experienced leadership with 30+ years: The team brings deep industry experience that translates into board level credibility and faster buy-in for security programs.
- Proven track record with 500+ engagements: Documented executive engagements show repeatable outcomes across compliance and governance initiatives.
- Customized solutions for compliance and strategy: Consulting is tailored to each client so controls map directly to business risk and regulatory needs.
- Security aligned with business objectives: Recommendations prioritize operational continuity and measurable risk reduction while supporting clinical workflows.
- Strong regulatory and risk emphasis: Consulting focuses on regulatory readiness and audit defensibility for highly regulated healthcare environments.
Who It's For
This service is ideal for CISOs at American healthcare providers, health systems, and large clinics that require leadership level cybersecurity strategy and compliance delivery. It fits organizations that need board reporting, HIPAA readiness, and a partner who will integrate security into business planning.
Unique Value Proposition
Heights stands apart because it combines executive advisory with hands-on managed services so security decisions are both strategic and operational. That dual model shortens time from policy to practice, reduces audit friction, and limits exposure during vendor transitions. Sophisticated buyers choose Heights because it prioritizes measurable risk reduction, offers board-ready reporting, and delivers tailored programs that support clinical priorities without disrupting care delivery.
Real World Use Case
A regional healthcare provider engaged Heights to achieve HIPAA compliance while implementing a comprehensive cybersecurity framework. Heights mapped controls to clinical workflows, stood up 24/7 monitoring, and produced board-level reporting that reduced audit findings and improved incident response time.
Pricing
Pricing is not specified on the website. Heights offers customized engagements that scale by service scope and organizational complexity, with proposals provided after an initial scoping conversation.
Website: https://heightscg.com
Recorded Future
At a Glance
Recorded Future delivers real time, unbiased threat intelligence across a broad set of global sources to support decision making across your security program. The platform suits teams that need deep research, automated feeds, and integration with existing tools.
Core Features
Recorded Future combines large scale data collection with analyst research to surface actionable indicators and context for security teams.
- Intelligence Graph® for analyzing emerging threats from more than 1M global sources.
- Collective Insights® to enrich security telemetry with contextual threat data.
- Recorded Future AI for AI conversations, reporting, and insights.
- Integrations and APIs for connecting Recorded Future with other security tools.
- Operational Threat Intelligence modules for real time detection and analysis.
Pros
- Comprehensive coverage: The platform provides continuous monitoring from a vast set of global sources so you get broad visibility into threat activity.
- Strong integration footprint: Extensive APIs and connectors let you feed intelligence into SIEM tooling and incident response workflows with minimal friction.
- Research backed intelligence: The platform is supported by Insikt Group® research which adds analytic depth to raw indicators.
- Proven trust: Recorded Future is used by Fortune 100 companies and government agencies which demonstrates enterprise level credibility.
- Flexible packaging: The vendor offers modular products and packages so you can tailor deployment to specific operational needs.
Cons
- Opaque pricing: Pricing is customized and requires a consultation which can slow procurement and budget planning for hospital systems.
- Steep learning curve: New users face a significant ramp to interpret advanced signals and tune the platform for health care use cases.
- Resource requirements: Achieving full value needs substantial data, tooling, and analyst time which can increase total cost of ownership.
Who It's For
Recorded Future is aimed at large enterprises and government agencies that need enterprise grade threat intelligence across many attack surfaces. For CISOs in Health Care, the platform fits organizations with mature security operations and dedicated threat analysts.
Unique Value Proposition
Recorded Future pairs massive automated collection with human research to turn signals into prioritized, contextual intelligence. That combined model reduces noise and gives security leaders readable, actionable context for incident response and risk decisions.
Real World Use Case
A financial institution uses Recorded Future to monitor external attack surface exposure and prioritize vulnerabilities that impact critical services. For a health care CISO, the same workflow maps ransomware trends to hospital vendor relationships and external facing assets for faster mitigation.
Pricing
Pricing is customized based on the organization needs and is available through consultation with Recorded Future sales. Expect tailored quotes rather than public list pricing which requires procurement planning.
Website: https://recordedfuture.com
CrowdStrike Falcon Platform
At a Glance
CrowdStrike Falcon is a comprehensive cybersecurity platform built around endpoint protection and threat intelligence that helps organizations prevent, detect, and respond to attacks. Its enterprise focus and advanced threat hunting make it a strong option for complex environments.
Core Features
The platform combines endpoint detection and response (EDR) with managed services and intelligence to cover prevention, detection, and response workflows. Key capabilities include threat hunting, identity security, and integrations with security information and event management systems.
- Next generation antivirus for real time prevention
- Endpoint Detection and Response for visibility and containment
- Managed Detection and Response for outsourced operations
- Threat intelligence and hunting for proactive investigation
- Identity security and SIEM integration for correlated telemetry
Pros
- Industry recognition as a leader: CrowdStrike Falcon has sustained leadership placement in major analyst reports, signaling strong market trust.
- Comprehensive platform integration: The solution brings prevention, EDR, MDR, and intelligence under one management plane for consistent operations.
- Flexible pricing and bundles: Multiple deployment and billing options allow you to tailor packages to organizational needs.
- Strong customer trust: Positive testimonials and widespread adoption indicate reliable real world performance.
- Advanced AI and hunting capabilities: The platform leverages analytics and threat hunting to surface sophisticated adversary activity.
Cons
- Complex onboarding requirements: The breadth of offerings means implementation often needs expert onboarding and tuning.
- Cost for smaller organizations: Pricing can be high for small businesses or startups and may exceed tight security budgets.
Who It's For
This platform matches mid to large organizations seeking enterprise grade cybersecurity, including health systems and provider networks with distributed endpoints. If you lead security for a regulated healthcare organization and need integrated detection, response, and intelligence, this fits your operational model.
Unique Value Proposition
CrowdStrike Falcon stands out by packaging EDR, MDR, and threat intelligence into a single managed platform so teams reduce tool sprawl and speed response. The combination of analytics driven hunting and professional services shortens time to value for complex security programs.
Real World Use Case
A financial institution deployed CrowdStrike Falcon to protect customer data, detect advanced threats, and automate response workflows using flexible bundles and expert support. A healthcare CISO can apply the same pattern to protect patient records, meet compliance, and accelerate incident response.
Pricing
Pricing varies by package and deployment with options for free trials and both monthly and annual billing. Organizations receive tailored quotes based on chosen modules, endpoint counts, and managed service levels.
Website: https://crowdstrike.com
Anomali
At a Glance
Anomali is an Intelligence Native Agentic SOC Platform that centralizes security telemetry, threat intelligence, and AI driven workflows to speed detection and response. The platform promises dramatic analyst efficiency gains and measurable SIEM cost reductions.
Core Features
Anomali combines a Unified Security Data Lake for real time and historical analysis with ThreatStream Next Gen curated threat intelligence and Agentic AI for guided investigations and automation. The platform also offers broad API based integration with existing security tools and connectors.
Pros
- Speeds detection and investigation: Reported improvements up to 300x faster help security teams cut time to identify threats.
- Dramatically reduces investigation time: The product claims a 96% reduction in threat investigation duration for trained teams.
- Frees analyst capacity: Intelligence integration is said to save 50% of analyst operational time so personnel focus on higher value tasks.
- Lowers operational costs: The platform reports cutting SIEM operational costs by 60%, which matters for large telemetry volumes.
- Comprehensive capability set: The combined AI, threat intelligence, and unified data management reduce tool fragmentation across security operations.
Cons
- Steep learning curve: The platform complexity requires extensive training and onboarding for effective use.
- Data quality dependent: High dependency on source data quality and integrations raises operational risk if telemetry is incomplete.
- Potentially costly for smaller teams: Pricing is not listed and complex deployments suggest costs that may restrict adoption by small organizations.
Who It's For
Anomali targets large enterprises, government agencies, and cybersecurity focused organizations that need a single platform to unify security data, automate threat detection, and accelerate response. Security leaders with mature telemetry sources and integration teams will extract the most value.
Unique Value Proposition
Anomali positions itself as an Intelligence Native approach to SOC operations by combining curated threat feeds with AI guided investigation and a centralized data lake. That combination aims to reduce manual triage and compress investigation timelines across the security stack.
Real World Use Case
Organizations centralize telemetry into Anomali to enrich alerts with ThreatStream intelligence and then apply Agentic AI to automate investigation workflows. The result reported is faster threat identification and response, lower analyst workload, and reduced operational expense.
Pricing
Pricing is not specified on the website. Offerings are likely customized to organizational needs and deployment scale so expect vendor engagement for a tailored quote and licensing model.
Website: https://anomali.com
ThreatConnect
At a Glance
ThreatConnect combines AI-powered analysis with integrated threat intelligence and risk quantification to help security teams focus on the highest priority threats. It is well suited for organizations that need a unified platform to connect intelligence, operations, and cyber risk reporting.
Core Features
ThreatConnect centers on operationalizing high-fidelity threat and risk insights so teams act faster and with more confidence.
- Threat Intelligence Operations platform for collecting, normalizing, and sharing indicators across teams.
- Federated search, correlation, and analysis that lets you query multiple sources without moving all data first.
- Threat Analytics and Visualization tools for slicing data into operational dashboards and investigation views.
- Threat and Risk-Informed Defense capabilities that align detection and response to quantified risk priorities.
- Cyber risk quantification and reporting tools to translate technical findings into business-facing metrics.
Pros
-
Comprehensive integration of threat intelligence, risk management, and security operations makes it easier to align analysts, SOC staff, and risk owners on the same evidence.
-
Powered by AI for operational effectiveness which can accelerate triage and highlight the most actionable signals from noisy telemetry.
-
Focus on high-priority threats and risks helps you allocate scarce analyst time to items that materially affect patient data and compliance obligations.
-
Strong reputation and recognition in cybersecurity industry means vendors, peers, and partners are more likely to accept and adopt shared intelligence.
-
Customizable and scalable solutions support expanding deployments across multiple hospital networks and subsidiary systems.
Cons
-
Complexity of platform may require training and expertise so you should plan for dedicated staff time for onboarding and continued tuning.
-
Pricing details are not openly specified, potentially costly for smaller organizations which makes budgeting for midmarket healthcare systems harder without a sales conversation.
-
Requires significant setup and integration effort because federating feeds and mapping telemetry to risk models takes cross-team coordination and engineering hours.
Who It's For
ThreatConnect fits cybersecurity teams and security operations centers in large healthcare systems that need integrated threat intelligence and cyber risk management. It is especially useful when your program must translate technical findings into compliance and board-level metrics.
Unique Value Proposition
ThreatConnect brings together threat intelligence, risk quantification, and security operations in a single workflow so investigators and risk owners work from the same prioritized context. That single-context approach reduces duplicated work and shortens time to remediation.
Real World Use Case
A Fortune 100 company used ThreatConnect to collect, analyze, and share threat intelligence across teams which reduced time to actionable insights and improved response efficiency. The same pattern applies to large health systems that must protect patient data and meet regulatory reporting timelines.
Pricing
Pricing is not specified publicly. Contact sales for details and to request a deployment and integration estimate tailored to your environment and compliance needs.
Website: https://threatconnect.com
At a Glance
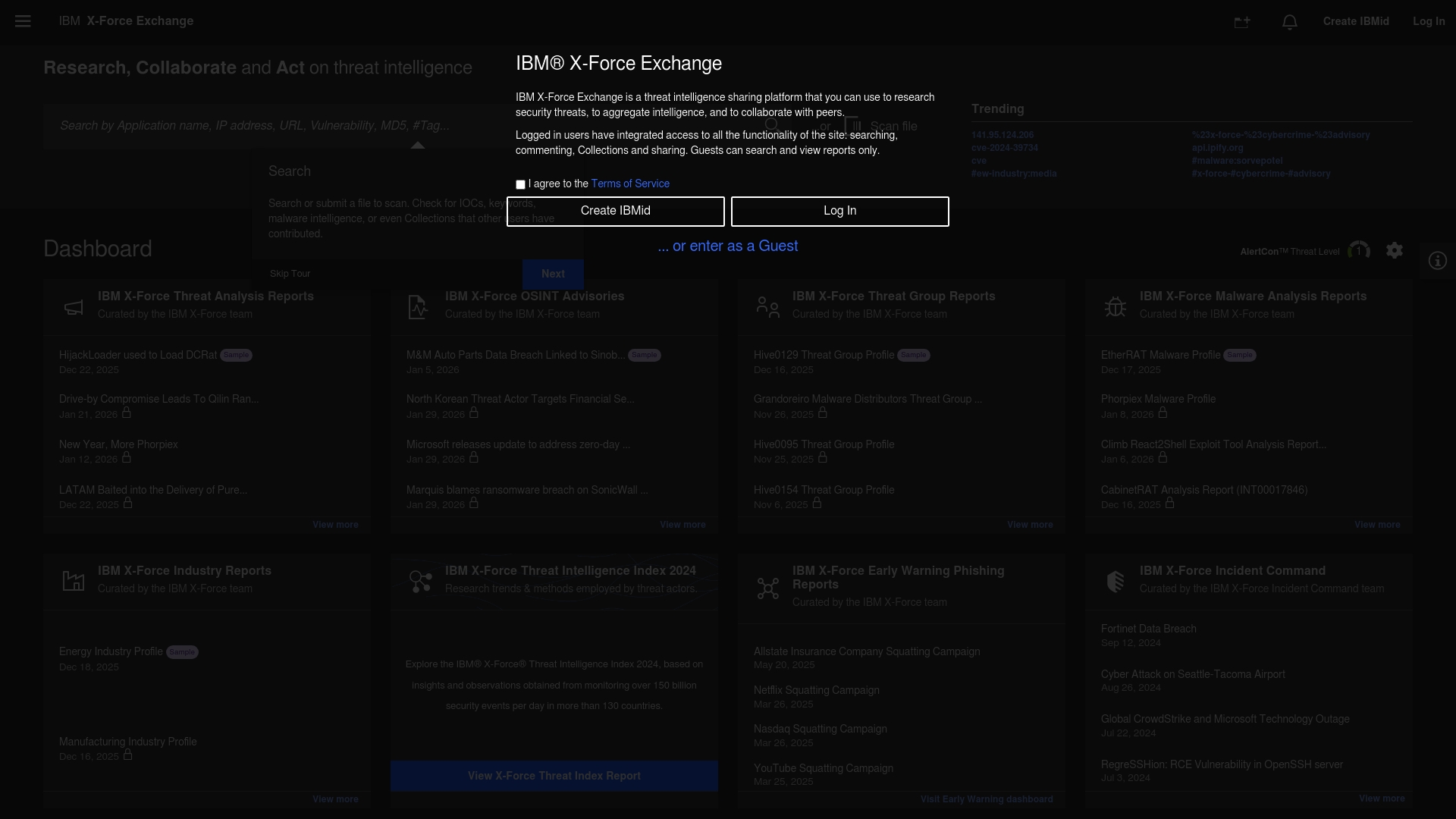
X-Force Exchange is a threat intelligence sharing platform that centralizes access to threat data for security teams. It functions as a resource hub for security professionals though the available content from the provided source is limited and partly dynamic.
Core Features
The platform offers threat intelligence sharing, curated access to threat data, and a collaboration resource for security professionals. The site appears to host links for requests and additional resources rather than full feature documentation, implying controlled or gated access to full datasets.
Pros
-
Accessible intelligence resources: The platform provides organized threat intelligence resources that security teams can reference when investigating incidents.
-
Supports professional collaboration: The site structure encourages collaboration among security professionals through shared resources and data pointers.
-
Secure access workflow: The presence of access request links suggests that data is delivered through controlled access mechanisms which helps protect sensitive intelligence.
Cons
-
Limited detail in content: The provided pages contain minimal descriptive material which reduces immediate clarity on specific capabilities and integrations.
-
Dynamic or incomplete pages reduce clarity: Several sections appear to be placeholders or dynamically generated which makes it hard to assess the platform without initiating access requests.
-
Requires access requests for full features: Users must request access to reach full functionality which adds onboarding friction for teams that need rapid intelligence access.
Who It Is For
Security professionals and threat intelligence teams will gain the most value from this platform. Analysts who prioritize access to curated threat data and who work within organizations that accept controlled access workflows will find this resource aligned with their operational needs.
Unique Value Proposition
The platform acts as a centralized exchange of threat observations and data for vetted security professionals. Its focus on shared intelligence and secure access positions it as a resource suited to organizations that prefer moderated distribution of high value threat data.
Real World Use Case
A cybersecurity team uses X-Force Exchange to pull contextual threat indicators during an active investigation. Analysts consult the exchange to compare observed indicators with shared intelligence, document findings, and coordinate follow up actions with external contributors after obtaining the required access.
Pricing
No pricing information was provided in the supplied content. The site appears to require registration or request procedures before revealing access tiers or licensing details.
Website: https://exchange.xforce.ibmcloud.com
Cybersecurity Solutions Comparison
This table provides a comprehensive comparison of cybersecurity solutions for various organizations, focusing on their features, benefits, drawbacks, targeted users, and pricing.
| Product Name | Core Features | Pros | Cons | Pricing |
|---|---|---|---|---|
| Heights Consulting Group | Strategic cybersecurity advisory, 24/7 threat monitoring, Compliance consulting, AI security planning | Experienced leadership, Proven track record, Customized solutions, Security aligned with business objectives | Pricing unspecified, Requires customized engagement | Customized engagements after scoping conversation |
| Recorded Future | Real-time threat intelligence, Broad source monitoring, Collective Insights, AI integration | Comprehensive coverage, Strong integrations, Research-backed intelligence, Flexible packaging | Opaque pricing, Steep learning curve | Customized based on consultations |
| CrowdStrike Falcon Platform | Endpoint protection, Threat intelligence, Managed Detection and Response, SIEM integration | Industry recognition, Comprehensive integration, Flexible pricing, Advanced AI capacities | Complex onboarding, High cost for small organizations | Pricing varies by package and organization size |
| Anomali | Unified data lake, ThreatStream intelligence, Agentic AI, API integration | Faster detection, Resource optimization, Reduced operational costs, Comprehensive capabilities | Requires detailed setup, Depends on data quality | Pricing customized to deployment scale |
| ThreatConnect | Integrated threat intelligence, Risk quantification, Operational defense tools, Analytics | Unified platform, AI-powered effectiveness, Risk prioritization, Customizable solutions | Complexity requires training, Setup effort needed | Pricing requires contact with sales |
| X-Force Exchange | Threat intelligence sharing, Curated data access, Secure collaboration mechanisms | Accessible resources, Collaboration support, Secure workflows | Limited feature descriptions, Access required for full functionality | Pricing information not provided |
Elevate Your Threat Intelligence Strategy with Expert Guidance from Heights Consulting Group
Navigating the complex landscape of threat intelligence tools like Recorded Future or CrowdStrike Falcon can overwhelm even the most seasoned CISOs. The article highlights challenges such as integrating expansive threat data, reducing alert noise, and aligning technical intelligence with business risk. These pain points demand a partner who does more than provide scattered solutions. At Heights Consulting Group, we specialize in transforming cybersecurity from a technical hurdle into a strategic business advantage through customized advisory and managed services. Our expertise in AI security, compliance frameworks like NIST and HIPAA, and executive-level risk governance ensures your threat intelligence investments deliver measurable risk reduction and operational continuity.
Benefit from decades of industry experience and a proven track record in healthcare cybersecurity by partnering with an advisory firm that bridges the gap between strategy and execution. Explore how our comprehensive approach aligns with your organization’s needs for board-ready reporting, incident response, and seamless integration of threat intelligence into your security operations. Learn more about our strategic cybersecurity solutions by visiting Heights Consulting Group and see how we can help you convert complex intelligence data into actionable business insights on our managed cybersecurity services page.
Build resilience before threats escalate and ensure compliance across evolving regulations. Take control of your security program today.

Are you ready to advance your cybersecurity posture with tailored threat intelligence and executive advisory? Visit Heights Consulting Group now to connect with experts who will help you protect your patients, data, and reputation.
Frequently Asked Questions
What are the key features to look for in threat intelligence tools for CISOs in 2026?
To effectively support cybersecurity strategies, look for features like real-time monitoring, automated threat analytics, and integration capabilities with existing security systems. Prioritize tools that can reduce incident response times by at least 30% through streamlined operations.
How can threat intelligence tools improve compliance with regulations?
Threat intelligence tools can enhance compliance by providing insights into potential threats and vulnerabilities that may affect regulatory requirements. Implement a tool that helps you identify compliance gaps within 45 days to ensure timely remediation.
What metrics should I use to evaluate the effectiveness of a threat intelligence tool?
Evaluate tools based on metrics such as reduced incident response times, the number of threats detected, and the accuracy of threat intelligence provided. Set specific performance goals, like aiming for a 20% increase in detection accuracy within the first six months of deployment.
How do I ensure successful integration of a new threat intelligence tool?
To ensure successful integration, conduct a thorough assessment of your current security tools and workflows to identify compatibility. Develop a clear integration plan with your IT team and aim for full operational integration within 30 days.
What training is required for my team to utilize threat intelligence tools effectively?
Training should focus on familiarizing team members with the tool's features, threat detection methodologies, and incident response protocols. Schedule training sessions to cover all essential functionalities and aim for a competency milestone within 15 days of implementation.
How can threat intelligence tools enhance collaboration among security teams?
Threat intelligence tools facilitate collaboration by providing a centralized platform for sharing threat data and insights. Encourage your teams to communicate findings using shared dashboards, with the goal of improving response coordination by 25% within the first month.
