Security leaders in American healthcare organizations face relentless, evolving cyber threats that demand vigilance beyond basic controls. The challenge is clear: adversaries increasingly exploit gaps that traditional tools overlook, raising urgent concerns about patient data and regulatory compliance. By embracing strategic threat hunting objectives, CISOs and IT security managers gain the tools to proactively uncover hidden risks, enhance detection capabilities, and build stronger defenses tailored to the unique needs of the healthcare sector.
Table of Contents
- Step 1: Establish Threat Hunting Objectives
- Step 2: Implement Foundational Threat Intelligence
- Step 3: Deploy Advanced Threat Detection Tools
- Step 4: Analyze and Investigate Threat Indicators
- Step 5: Validate Threat Containment and Remediation
Quick Summary
| Key Insight | Explanation |
|---|---|
| 1. Define Threat Hunting Objectives | Establish clear goals aligned with your organization's unique risks to proactively identify hidden security threats. |
| 2. Implement Threat Intelligence | Develop comprehensive data collection and analysis practices to convert threat information into actionable strategic insights. |
| 3. Deploy Advanced Detection Tools | Utilize integrated security platforms that enable real-time monitoring and automated responses to mitigate threats effectively. |
| 4. Analyze Threat Indicators Systematically | Validate and prioritize threat data through a structured approach to transform raw indicators into strategic responses. |
| 5. Validate Containment and Remediation | Conduct thorough analyses post-incident to ensure all threats are neutralized and relevant vulnerabilities are addressed effectively. |
Step 1: Establish threat hunting objectives
Threat hunting requires strategic planning to proactively identify potential security compromises within your organization's digital ecosystem. By defining precise hunting objectives, security teams can systematically explore potential vulnerabilities and uncover hidden threats that traditional detection methods might miss.
Effective threat hunting objectives should focus on several critical dimensions. Consider establishing goals that align with your organization's specific risk landscape:
- Identify unknown threats targeting your unique technology infrastructure
- Detect potential lateral movement within internal network segments
- Investigate suspicious user behavior that could indicate compromise
- Analyze advanced persistent threats evading standard security controls
To develop robust objectives, CISOs must collaborate closely with their security operations center (SOC) and threat intelligence teams. This cross-functional approach ensures that hunting efforts are data-driven, targeted, and capable of uncovering complex attack patterns that automated systems might overlook.
Here's how threat hunting objectives differ from traditional detection methods:
| Approach | Focus Area | Proactivity Level | Typical Outcome |
|---|---|---|---|
| Threat Hunting | Identifying unknown threats | Highly proactive | Early risk mitigation |
| Traditional Detection | Responding to known threats | Reactive | Post-compromise response |
| Automated Monitoring | Predefined alert triggers | Semi-proactive | Quick but limited detection |
| Manual Review | Case-by-case analysis | Low proactivity | Often delayed response |
Strategic threat hunting transforms reactive security postures into proactive defense mechanisms that anticipate and neutralize potential risks before they escalate.
Pro tip: Document your threat hunting objectives with measurable key performance indicators to track the effectiveness and continuous improvement of your hunting program.
Step 2: Implement foundational threat intelligence
Building a robust threat intelligence capability requires strategic planning and systematic execution. By developing threat-informed defense principles, security teams can transform their approach from reactive monitoring to proactive risk management.
Key components of foundational threat intelligence implementation include:
- Collect comprehensive data from multiple internal and external sources
- Analyze threat landscape specific to your industry and technology environment
- Contextualize intelligence with organizational risk profiles
- Establish clear communication channels between threat intelligence and security teams
- Develop actionable threat indicators that drive strategic decision-making
Successful threat intelligence integration demands cross-functional collaboration. CISOs must work closely with threat analysts, security operations, and IT infrastructure teams to create a unified approach that translates raw threat data into meaningful defensive strategies.
Effective threat intelligence is not about collecting information, but transforming data into strategic insights that enable proactive cybersecurity measures.
Pro tip: Regularly validate and update your threat intelligence sources to ensure ongoing relevance and accuracy of your defensive strategies.
Step 3: Deploy advanced threat detection tools
Deploying advanced threat detection tools transforms your cybersecurity infrastructure from passive defense to proactive threat neutralization. By implementing comprehensive event logging practices, security teams can create a robust, multi-layered defense mechanism against sophisticated cyber threats.
Key components of an effective threat detection tool deployment strategy include:
- Select integrated security platforms that offer comprehensive visibility
- Configure multi-layered detection techniques combining signature and behavior-based analysis
- Implement real-time monitoring across network and endpoint environments
- Establish automated threat response capabilities
- Integrate AI-powered anomaly detection mechanisms
Successful deployment requires careful planning and systematic implementation. CISOs must prioritize tools that provide comprehensive visibility, including intrusion detection systems (IDS), security information and event management (SIEM) platforms, and endpoint detection and response (EDR) solutions. These tools should work synergistically to create a holistic security ecosystem that can detect, analyze, and respond to potential threats in real time.
Below is a summary of critical business impacts for advanced threat detection tool implementation:
| Impact Area | Business Benefit | Example Scenario |
|---|---|---|
| Operational Continuity | Minimizes downtime | Rapid response stops ransomware |
| Regulatory Compliance | Strengthens audit results | Detects data access violations |
| Financial Protection | Reduces incident costs | Prevents fraud-related losses |
| Reputational Security | Maintains customer trust | Blocks large-scale data breach |
Advanced threat detection is not about acquiring the most expensive tools, but implementing a strategic, integrated approach that adapts to your unique organizational risk profile.
Pro tip: Conduct thorough compatibility testing and phased rollout to minimize operational disruptions during advanced threat detection tool implementation.
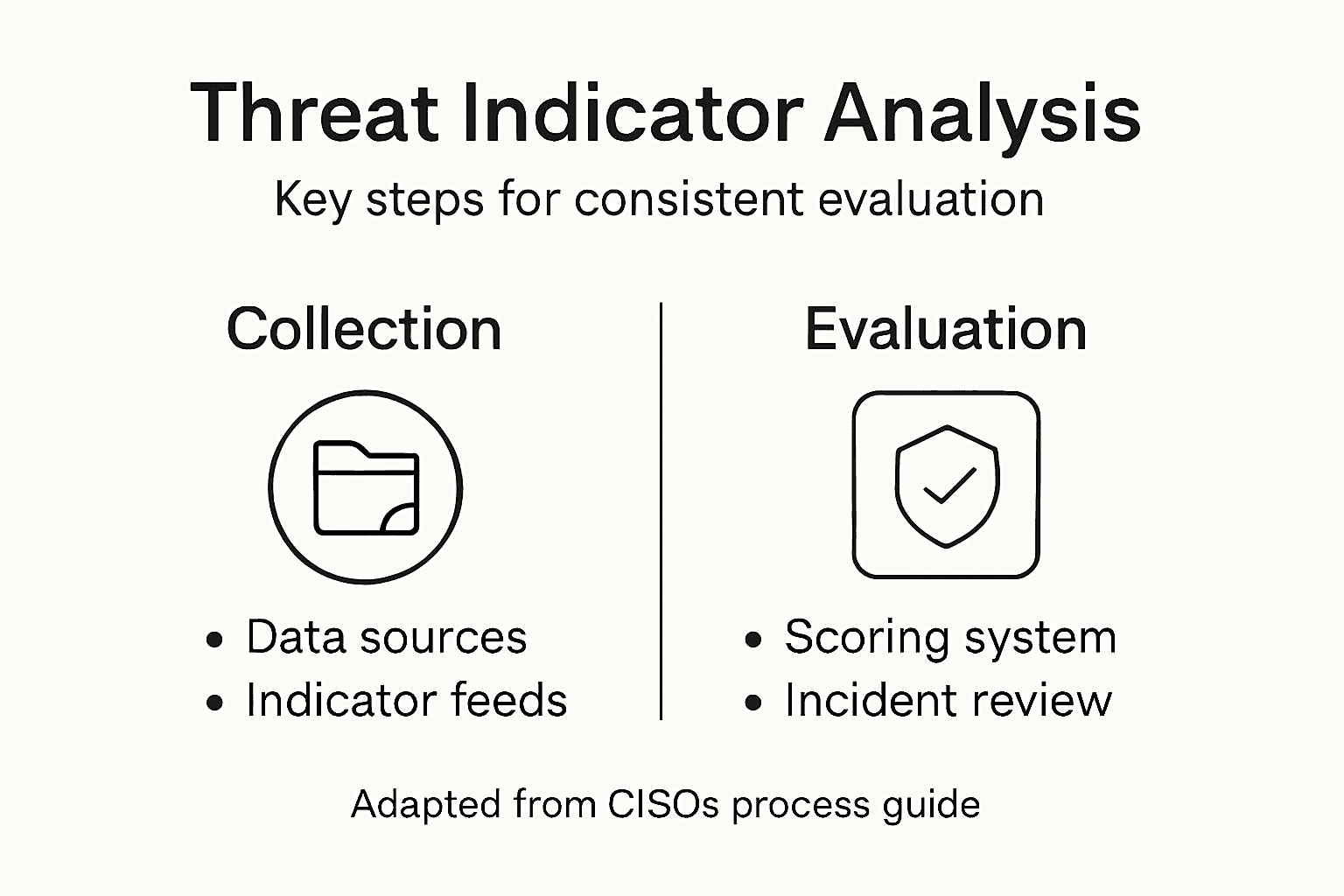
Step 4: Analyze and investigate threat indicators
Effective threat indicator analysis demands a systematic and strategic approach to transforming raw data into actionable intelligence. By creating integrated threat intelligence workflows, security teams can uncover hidden threats and rapidly respond to potential security incidents.
Key strategies for comprehensive threat indicator investigation include:
- Correlate multiple threat data sources to validate potential indicators
- Assess threat indicator context and potential organizational impact
- Prioritize indicators based on risk severity and relevance
- Validate threat intelligence through manual and automated techniques
- Document detailed investigation findings for future reference
Successful threat indicator analysis requires a meticulous approach that combines technical expertise with strategic thinking. CISOs should establish a structured methodology that enables security analysts to systematically evaluate indicators, assess their credibility, and determine appropriate response mechanisms. This process involves cross-referencing threat data, understanding attack patterns, and developing a nuanced understanding of potential security risks.
Threat indicator analysis is not about collecting information, but transforming raw data into strategic insights that drive proactive defense strategies.
Pro tip: Develop a standardized scoring system for threat indicators to ensure consistent and objective evaluation across your security team.
Step 5: Validate threat containment and remediation
Threat containment and remediation validation is a critical phase in cybersecurity defense that ensures threats are completely neutralized and systemic vulnerabilities are addressed. By implementing comprehensive vulnerability management workflows, security teams can meticulously track and confirm the effectiveness of their incident response strategies.
Key validation strategies for effective threat containment include:
- Conduct thorough post-incident forensic analysis
- Verify complete threat actor removal from network environments
- Document all remediation steps with precise technical details
- Test system integrity after containment procedures
- Monitor potential reinfection vectors continuously
Successful validation requires a methodical approach that bridges security and IT teams. CISOs must establish rigorous protocols that not only address immediate threats but also prevent potential future compromises. This involves creating detailed artifacts, analyzing attack patterns, and developing adaptive mitigation strategies that evolve with emerging cybersecurity challenges.
Effective threat containment is not a single action, but a continuous process of monitoring, analyzing, and adapting to protect organizational resilience.
Pro tip: Develop a standardized incident response checklist that includes specific validation criteria to ensure consistent and comprehensive threat remediation.
Elevate Your Threat Hunting Strategy with Expert Cybersecurity Guidance
The Advanced Threat Hunting Process Guide for CISOs highlights the crucial need for strategic planning, actionable intelligence, and advanced detection tools to stay ahead of evolving cyber threats. If your organization struggles with defining precise hunting objectives or validating threat containment, you are not alone. Many security leaders face challenges turning raw data into proactive defense and ensuring continuous risk mitigation with limited resources.
Unlock lasting security benefits with Heights Consulting Group's expertise. Our tailored cybersecurity consulting services align threat hunting initiatives with your business goals and compliance demands. We specialize in enabling CISOs to implement integrated threat intelligence, deploy cutting-edge detection technology, and validate containment effectively across complex IT environments. Benefit from our experience in regulatory frameworks such as NIST and SOC 2 while transforming cybersecurity into a competitive advantage.

Ready to transform your proactive defense approach? Discover how our managed cybersecurity and threat hunting solutions can empower your organization to detect and remediate sophisticated threats before they impact your business. Visit Heights Consulting Group today to start your journey toward resilient cybersecurity. Learn more about our strategic consulting services and how we help security leaders achieve measurable outcomes.
Frequently Asked Questions
What are the key objectives to establish in an advanced threat hunting program?
To establish effective objectives for your advanced threat hunting program, focus on areas like identifying unknown threats, detecting lateral movement, investigating suspicious user behavior, and analyzing advanced persistent threats. Collaborate with your security operations center and threat intelligence teams to align these goals with your organization's risk landscape.
How can I implement foundational threat intelligence in my organization?
To implement foundational threat intelligence, start by collecting comprehensive data from both internal and external sources. Regularly analyze your industry's threat landscape and establish communication channels between relevant teams to transform raw data into actionable insights.
What features should I look for in advanced threat detection tools?
When selecting advanced threat detection tools, prioritize platforms that offer integrated visibility, multi-layered detection techniques, real-time monitoring, and automated threat response capabilities. Aim to implement tools that work together to enhance your overall security posture within a streamlined framework.
How should I analyze and investigate threat indicators?
To analyze and investigate threat indicators effectively, correlate multiple data sources to validate potential threats and assess their context within your organization. Prioritize indicators based on their risk severity and document your findings systematically for future reference.
What steps should I take to validate threat containment and remediation?
To validate threat containment and remediation, conduct a thorough post-incident forensic analysis and ensure complete removal of threat actors from your network. Document all remediation steps and monitor for potential reinfection vectors to adapt your defenses moving forward.
How can I ensure continuous improvement in my threat hunting efforts?
To ensure continuous improvement in your threat hunting efforts, document your objectives with measurable key performance indicators and regularly assess their effectiveness. This approach helps refine your hunting strategies and adapt to new threats within a rapidly changing cybersecurity landscape.
