Traditional security tools alone are no match for determined cyber adversaries in regulated industries. American CISOs and IT security managers must move from reactive defense to proactive threat hunting to uncover advanced attacks before they escalate. As evolving compliance requirements raise the stakes, this approach offers a path to greater resilience by combining skilled analysts, advanced detection techniques, and adaptive strategies for meeting modern regulatory demands.
Table of Contents
- Threat Hunting Fundamentals And Misconceptions
- Types And Models Of Threat Hunting Methodologies
- How Threat Hunting Works In Enterprise Environments
- Essential Tools And Skills For Effective Threat Hunts
- Compliance Requirements And Regulatory Impacts
- Risks, Investments, And Common Pitfalls
Key Takeaways
| Point | Details |
|---|---|
| Proactive Approach | Threat hunting is essential for identifying hidden threats before they escalate, moving beyond traditional reactive security methods. |
| Advanced Methodologies | Employ diverse hunting models such as attack-centric and defense-centric approaches to strengthen security posture. |
| Continuous Learning | Cultivating a skilled team focused on ongoing education and adaptability is crucial for effective threat detection. |
| Compliance Integration | Align threat hunting efforts with regulatory requirements to not only enhance security but also gain a strategic advantage. |
Threat hunting fundamentals and misconceptions
Threat hunting represents a proactive cybersecurity approach where security professionals actively search for hidden threats and vulnerabilities within an organization's network infrastructure. Unlike traditional reactive security methods that respond after an incident occurs, threat hunting involves systematically investigating potential security risks before they escalate into full-scale breaches.
At its core, threat hunting requires a deep understanding of adversarial tactics and advanced investigative techniques. Cybersecurity threat hunting involves analyzing network traffic patterns, system logs, and endpoint data to identify anomalies that might indicate malicious activity. Security teams leverage several key strategies:
- Hypothesis-driven investigations targeting specific threat scenarios
- Advanced data correlation across multiple security telemetry sources
- Behavioral analysis of user and system interactions
- Continuous monitoring of network and endpoint environments
- Utilizing threat intelligence feeds to understand emerging attack patterns
Common misconceptions about threat hunting often undermine its effectiveness. Many organizations mistakenly believe that traditional security tools like antivirus software and firewalls are sufficient for comprehensive protection. However, modern threat actors continuously evolve their techniques, rendering static defense mechanisms inadequate. Threat hunting requires human expertise, advanced analytics, and a proactive mindset to detect sophisticated threats that automated systems might miss.
Pro tip: Develop a threat hunting program that combines technological tools, skilled analysts, and continuous learning to stay ahead of emerging cyber risks.
Types and models of threat hunting methodologies
Threat hunting methodologies represent sophisticated frameworks designed to systematically identify, analyze, and mitigate potential cybersecurity risks across organizational networks. These structured approaches enable security professionals to move beyond reactive defense and proactively uncover hidden vulnerabilities and potential threat vectors.
Threat modeling approaches can be categorized into several distinct methodological frameworks that provide unique perspectives on cybersecurity risk assessment:
- Attack-centric model: Focuses on potential attacker strategies and techniques
- Defense-centric model: Emphasizes defensive capabilities and infrastructure resilience
- Asset-centric model: Prioritizes identifying and protecting critical organizational assets
- Hybrid model: Combines multiple perspectives for comprehensive threat analysis
Each methodology offers distinct advantages in understanding potential security risks. The attack-centric model, for instance, requires deep knowledge of adversarial tactics and current threat landscapes. Security teams simulate potential attack scenarios, mapping out possible intrusion paths and understanding how threat actors might exploit system vulnerabilities. By comprehensively modeling potential threats, organizations can develop more robust and proactive defense strategies.
Moreover, modern threat hunting methodologies increasingly integrate advanced technologies like machine learning and behavioral analytics to enhance threat detection capabilities. These sophisticated approaches enable security teams to move beyond traditional signature-based detection methods and identify subtle, complex threat patterns that might otherwise remain undetected.
Here's a summary comparing common threat hunting models and their unique focal points:
| Model Type | Primary Focus | Typical Use Case | Key Strength |
|---|---|---|---|
| Attack-centric | Attacker methods and tactics | Simulating real-world attacks | Anticipates attacker moves |
| Defense-centric | Protecting infrastructure | Strengthening security controls | Improves resilience |
| Asset-centric | Securing critical assets | Prioritizing crown jewel assets | Focuses on business impact |
| Hybrid | Combining various perspectives | Enterprise-wide risk assessments | Offers balanced protection |
Pro tip: Implement a multi-model threat hunting approach that combines different methodological perspectives to create a comprehensive and adaptive security strategy.
How threat hunting works in enterprise environments
Threat hunting in enterprise environments represents a sophisticated, proactive cybersecurity strategy that goes far beyond traditional defensive mechanisms. Unlike reactive security approaches that wait for alerts, threat hunting actively seeks out potential security breaches and hidden vulnerabilities across complex organizational networks.
Cyber threat hunting services typically involve a comprehensive, multilayered approach that integrates several critical components:
- Advanced data collection from multiple network sources
- Continuous monitoring of system and user behavior
- Sophisticated threat intelligence analysis
- Predictive risk assessment techniques
- Comprehensive network and endpoint telemetry examination
The process begins with establishing a baseline of normal network behavior, enabling security teams to identify anomalies that might indicate potential intrusions. Threat hunters leverage sophisticated tools like Security Information and Event Management (SIEM) systems, Extended Detection and Response (XDR) platforms, and machine learning algorithms to conduct deep, nuanced investigations that traditional security tools might miss.
Enterprise threat hunting requires a combination of human expertise and advanced technological capabilities. Security professionals must develop intricate understanding of potential attacker methodologies, continuously updating their knowledge about emerging threat landscapes. This approach transforms cybersecurity from a reactive defense mechanism to a proactive, intelligence-driven discipline that anticipates and neutralizes potential security risks before they can cause significant damage.

Pro tip: Develop a threat hunting team with diverse skill sets, combining technical expertise, analytical thinking, and continuous learning to create a robust, adaptive cybersecurity strategy.
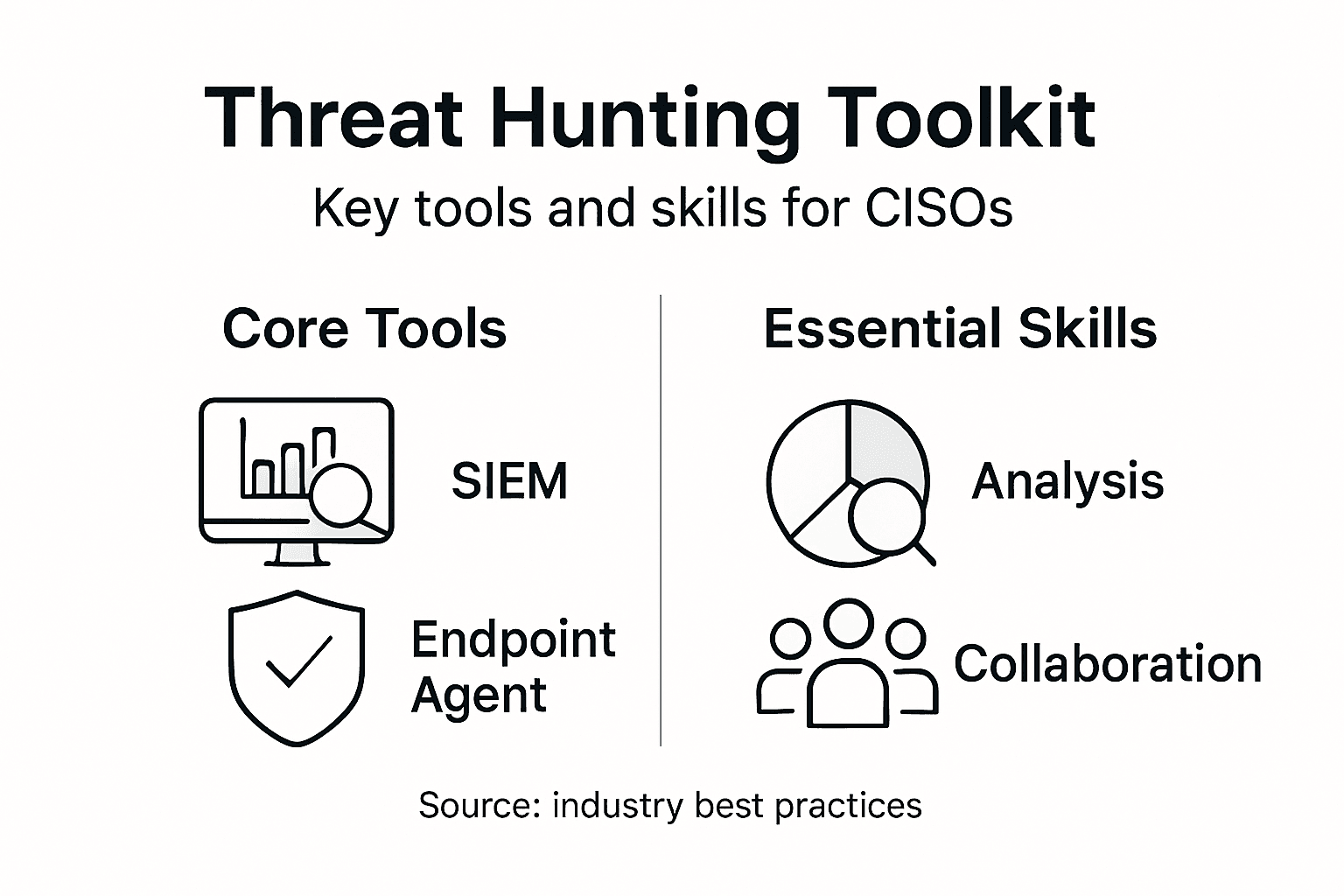
Essential tools and skills for effective threat hunts
Threat hunting demands a sophisticated blend of technological expertise, analytical skills, and deep understanding of cybersecurity dynamics. Security professionals must develop a comprehensive toolkit that combines advanced technologies with nuanced human intelligence to effectively identify and neutralize potential security threats.
Cybersecurity threat hunting skills encompass a diverse range of technical and cognitive capabilities:
- Advanced network and endpoint forensics
- Proficiency in scripting languages like PowerShell
- Deep understanding of system and network architectures
- Machine learning and data analysis techniques
- Critical thinking and hypothesis development skills
- Comprehensive knowledge of attacker methodologies
The technological arsenal for effective threat hunting includes sophisticated tools that enable deep system investigation. Security professionals leverage platforms like Security Information and Event Management (SIEM) systems, Extended Detection and Response (XDR) platforms, and advanced forensic tools such as Volatility and Dumplt to conduct comprehensive network investigations. These tools allow threat hunters to perform memory forensics, analyze system behaviors, and uncover subtle indicators of potential security breaches.
Successful threat hunting requires more than technical proficiency. It demands a proactive, investigative mindset that combines technical skills with strategic thinking. Professionals must continuously adapt to evolving threat landscapes, develop sophisticated hypotheses about potential security risks, and maintain an ongoing learning approach that anticipates emerging cyber threats.
Pro tip: Develop a continuous learning program that combines hands-on technical training, threat intelligence updates, and collaborative skill development to stay ahead of sophisticated cyber adversaries.
Compliance requirements and regulatory impacts
Navigating the complex landscape of cybersecurity compliance requires a strategic approach that aligns threat hunting activities with stringent regulatory frameworks. Organizations must develop comprehensive strategies that not only protect against cyber threats but also satisfy increasingly rigorous industry-specific security standards and legal requirements.
Cyber threat hunting services play a critical role in maintaining regulatory compliance by providing detailed documentation and systematic threat investigation processes. Key compliance considerations include:
- Adherence to industry-specific security regulations
- Comprehensive documentation of threat hunting activities
- Alignment with data protection and privacy standards
- Robust risk management and reporting mechanisms
- Continuous monitoring and audit trail maintenance
Different sectors face unique regulatory landscapes that demand specialized compliance approaches. Financial institutions must comply with frameworks like GLBA and PCI DSS, healthcare organizations navigate HIPAA requirements, while government agencies follow stringent NIST and FedRAMP guidelines. Each regulatory environment requires tailored threat hunting strategies that demonstrate proactive security measures and comprehensive risk management.
Successful compliance integration demands more than mere checkbox exercise. Security leaders must develop threat hunting programs that inherently support regulatory requirements, transforming compliance from a burdensome obligation into a strategic advantage. This approach involves creating robust documentation, implementing continuous improvement processes, and demonstrating measurable security outcomes that satisfy regulatory scrutiny.
Below is a comparison of regulatory frameworks and their main cybersecurity compliance focus:
| Regulation | Industry Focus | Core Security Requirement |
|---|---|---|
| GLBA | Financial services | Safeguarding customer data |
| PCI DSS | Payment processing | Protecting cardholder information |
| HIPAA | Healthcare | Securing patient health records |
| NIST/FedRAMP | Government | Ensuring controlled data access |
Pro tip: Develop a compliance-integrated threat hunting framework that simultaneously addresses security risks and regulatory requirements, turning regulatory compliance into a competitive organizational strength.
Risks, investments, and common pitfalls
Threat hunting represents a significant strategic investment for organizations, requiring careful consideration of potential risks, resource allocation, and potential return on cybersecurity initiatives. Unlike traditional security approaches, threat hunting demands a nuanced understanding of potential vulnerabilities and the sophisticated tactics employed by modern cyber adversaries.
Cybersecurity threat hunting risks encompass several critical dimensions:
- Misalignment of organizational resources and hunting capabilities
- Inadequate data management and analysis infrastructure
- Overreliance on traditional indicator-based detection methods
- Insufficient skills and knowledge among security teams
- Lack of continuous methodology improvement
- Undefined metrics for measuring threat hunting effectiveness
The financial implications of threat hunting extend beyond direct monetary investments. Organizations must consider the potential costs of undetected security breaches, which can far outweigh the initial investment in sophisticated threat hunting capabilities. Many companies mistakenly view threat hunting as an expensive luxury, when in reality, it represents a critical proactive defense mechanism that can potentially save millions in potential damage and recovery costs.
Successful threat hunting programs require a holistic approach that balances technological investment, human expertise, and continuous learning. Security leaders must develop robust frameworks that not only detect potential threats but also provide actionable insights for ongoing risk mitigation. This involves creating adaptive strategies that can evolve alongside emerging cyber threats and organizational technological landscapes.
Pro tip: Start with a lean, focused threat hunting approach using existing resources, prioritizing continuous improvement and strategic skill development over massive initial investments.
Empower Your Cyber Defense with Strategic Threat Hunting
The article highlights how proactive threat hunting transforms cybersecurity from a reactive task to an intelligence-driven discipline. If you are a CISO struggling with identifying hidden threats and building resilience against sophisticated cyber attacks then understanding and implementing advanced threat hunting methodologies is critical. Key challenges include aligning skilled analysts, leveraging advanced tools like SIEM and XDR, and integrating continuous learning to outpace evolving attacker strategies. At Heights Consulting Group we recognize these pain points and specialize in helping organizations integrate threat hunting with business objectives, risk management, and regulatory compliance to turn cybersecurity into a competitive advantage.

Take the next step to strengthen your organization’s cyber resilience. Explore how our strategic guidance and technical services—covering managed cybersecurity, incident response, and tailored threat hunting solutions—can empower your team to detect and neutralize threats before they escalate. Visit Heights Consulting Group now to start building a more adaptive and comprehensive security strategy. Discover more about how we integrate compliance frameworks and deliver expert cybersecurity consulting designed for industry leaders like you.
Frequently Asked Questions
What is threat hunting in cybersecurity?
Threat hunting is a proactive cybersecurity approach where security professionals actively search for hidden threats and vulnerabilities within an organization's network, as opposed to waiting for alerts from traditional security systems.
Why is threat hunting important for organizations?
Threat hunting is crucial because it helps organizations identify sophisticated threats that automated defenses may miss, ultimately preventing potential breaches and enhancing overall security resilience.
What methodologies are commonly used in threat hunting?
Common methodologies in threat hunting include attack-centric, defense-centric, asset-centric, and hybrid models, each offering unique perspectives on cybersecurity risk assessment and threat detection strategies.
What skills are essential for effective threat hunting?
Essential skills for effective threat hunting include advanced network forensics, proficiency in scripting languages, deep knowledge of system architectures, and critical thinking for hypothesis development, alongside familiarity with advanced analytical technologies.