Keeping pace with security in highly regulated fields has become an ongoing challenge. New threats surface every day and rules change quickly. Some platforms claim to spot trouble before it grows while others offer precise controls that fit strict requirements. Can technology handle the rising complexity or does it fall short in critical moments. Explore how these detection tools measure up and see which approaches might fit the toughest industries. Curiosity about which ones lead the pack will keep you reading.
Table of Contents
- Heights Consulting Group
- ThreatConnect
- SOC Prime
- Quzara
- SOCSoter Managed Cybersecurity Solutions
- SocRadar
Heights Consulting Group
At a Glance
Heights Consulting Group is a leading cybersecurity consulting and managed services firm focused on regulated industries and complex environments. Its combination of strategic advisory and hands-on managed services positions it as the clear choice for executives who need compliance plus operational security.
Core Features
Heights delivers strategic advisory, risk governance, and regulatory compliance services designed around NIST, CMMC, HIPAA, and SOC 2 frameworks. The firm pairs AI security and emerging technology security planning with managed cybersecurity services including 24/7 monitoring and incident response.
Pros
- Experienced leadership with over 30 years in cybersecurity: The firm is led by senior practitioners who bring long term, executive level risk and security experience to program design and oversight.
- Proven methodologies refined through real-world implementations: Their approaches are field tested across enterprise and government environments to reduce implementation risk and speed time to value.
- Trusted by large organizations including Fortune 500 and government agencies: This track record demonstrates the firm’s ability to meet demanding procurement and compliance requirements.
- Comprehensive services covering strategy, compliance, and technical security measures: Clients benefit from a single partner that aligns policies, process, and tooling with business goals.
- Strong focus on aligning cybersecurity with business objectives: The practice frames security investments as risk reduction and business enablers rather than technical chores.
Who It's For
Heights is designed for C-level executives and security leaders at enterprise organizations, government agencies, and healthcare systems that require rigorous compliance and continuous threat detection. Choose Heights when you need an advisor who translates regulatory requirements into operational controls.
Unique Value Proposition
Heights combines executive level strategy with operational delivery to create a unified security program that maps directly to business risk. That union of advisory and managed services reduces vendor fragmentation, improves audit readiness, and shortens response times during incidents. The firm’s emphasis on integrating risk governance with technical operations means decisions reflect both compliance obligations and commercial priorities. Smart buyers pick Heights because it eliminates the common gap between board level strategy and daily security operations, producing measurable improvements in control maturity and incident containment times.
Real World Use Case
A healthcare organization engaged Heights to achieve HIPAA compliance while bolstering incident response. The firm performed risk assessments, implemented tailored managed detection, and delivered governance controls that met auditors and reduced mean time to respond. The program met regulatory milestones while improving patient data protection.
Pricing
Pricing information is not specified on the website. Prospective clients should expect tailored engagements and scoped proposals based on environment complexity and compliance requirements.
Website: https://heightscg.com
ThreatConnect
At a Glance
ThreatConnect delivers an integrated platform that combines threat intelligence, risk management, and security operations into a single environment for enterprise teams. It targets security leaders who need a unified view of intelligence and measurable risk insights.
The platform emphasizes AI powered analysis to accelerate decision making and reduce time to action across teams.
Core Features
ThreatConnect centers on a Threat Intelligence Platform that aggregates and normalizes signals from multiple sources for centralized analysis and sharing.
- Polarity federated search and analysis for rapid cross source hunts and context enrichment.
- Risk Quantifier for measurable cyber risk assessment and prioritization.
- Intel Hub supporting Threat and Risk Informed Defense and collaborative workflows.
- Automation and Workflows to orchestrate repetitive security tasks and speed response.
Actionable takeaway: map these modules to your existing toolchain before procurement to measure operational impact.
Pros
-
Integrated threat intelligence and operations combine intelligence, risk management, and security operations in one platform to reduce context switching for analysts.
-
AI enabled solutions increase operational efficiency by surfacing prioritized leads and reducing manual triage time.
-
Cross team collaboration is supported so analysts, responders, and risk owners can share findings and workflows with reduced handoffs.
-
Customizable and scalable architecture lets large enterprises tailor data models, playbooks, and access controls to complex environments.
-
Trusted by leading organizations which suggests maturity and a track record at scale for enterprise deployments.
Cons
-
Feature complexity means teams will need training to use advanced modules effectively and to avoid misconfiguration.
-
Cost considerations may place the platform out of reach for small organizations or teams with limited budgets.
-
Integration requirements mean you must connect ThreatConnect to existing security infrastructure to realize full value which adds implementation overhead.
Actionable takeaway: plan for dedicated onboarding and integration resources when budgeting for deployment.
Who It's For
Enterprise cybersecurity teams and security leaders who need an integrated approach to operational threat intelligence and risk driven defense. Organizations with dedicated analysts and mature security stacks will extract the most value.
Unique Value Proposition
ThreatConnect combines intelligence, risk quantification, and automated workflows in a single platform so security leaders can prioritize actions by measurable risk and coordinate response across teams.
Actionable takeaway: use Risk Quantifier to tie detection outcomes to business risk for executive reporting.
Real World Use Case
A Fortune 100 company uses ThreatConnect to collect, analyze, and share threat intelligence across distributed teams which reduced time to action and improved mitigation consistency across business units.
Pricing
Contact ThreatConnect for a customized quote as pricing details are not specified on the website.
Website: https://www.threatconnect.com
SOC Prime
At a Glance
SOC Prime combines a threat detection marketplace with AI-assisted detection engineering to help SOC teams maintain up-to-date detections and automate hunting workflows. Trusted by over 11,000 SOC teams, it suits organizations that require rapid rule deployment and continuous detection updates.
Core Features
SOC Prime provides a Threat Detection Marketplace with curated, current detection content and use cases. It includes Attack Detective SaaS for proactive hunting, Uncoder AI for natural language detection engineering, and DetectFlow for routing detection data into SIEMs and pipelines.
The platform integrates with major SIEMs and cloud platforms such as Azure and AWS to deliver detection as code and automation across hybrid environments.
Pros
-
Extensive detection library: The marketplace offers a broad set of up-to-date detection rules and use cases that reduce time to coverage for common adversary techniques.
-
Detection engineering support: Uncoder AI and detection as code workflows support engineers in creating, testing, and deploying rules faster than manual processes.
-
Automated hunting and response: Attack Detective SaaS automates parts of the threat hunting process which helps surface high priority threats to analysts quicker.
-
Flexible deployment options: The platform supports both on premise and cloud deployment models so teams can align architecture with compliance requirements.
-
Enterprise trust and scale: Adoption by large enterprise SOC teams and MSSPs demonstrates scalability for complex environments.
Cons
-
Limited technical detail available: Public material lacks deep technical specifications which makes initial technical evaluation harder for architects and procurement teams.
-
No public pricing details: Pricing is not published which forces organizations to engage sales for cost estimates and slows budget planning.
-
Integration effort required: Integrating detection feeds and pipelines into existing SIEM and tooling requires engineering effort and coordination across teams.
Who It's For
SOC Prime targets cybersecurity teams, SOC analysts, threat hunters, and security operations centers that need high quality detection content and automation. It fits regulated organizations that must keep detection coverage current across SIEM environments while retaining deployment flexibility.
Unique Value Proposition
SOC Prime stands out for combining a marketplace of detection content with AI driven detection engineering and a pipeline for automated delivery. This blend reduces manual rule churn and helps teams maintain continuous detection coverage as threats evolve.
Real World Use Case
A global financial organization uses SOC Prime to keep detection content current across multiple SIEM instances, automate deployment of alerting rules, and accelerate hunting workflows. The result is improved detection coverage and more consistent rule updates across geographies.
Pricing
Pricing is not specified on the website and is likely custom based on enterprise needs and deployment scope. Procurement teams should request a tailored quote to understand licensing, support, and integration costs.
Website: https://www.socprime.com
Quzara
At a Glance
Quzara is an SBA Certified WOSB cybersecurity firm focused on compliance advisory, cloud security, and managed security operations for government and regulated clients. The firm pairs FedRAMP and CMMC advisory depth with managed detection and response to support high compliance needs.
Core Features
Quzara delivers advisory and managed services built around regulatory frameworks and cloud security posture. Their capabilities emphasize readiness and continuous monitoring for regulated environments.
- FedRAMP Advisory Services
- FedRAMP Revision 5 Support
- CMMC Advisory and Managed Security
- Department of Defense Impact Level 4/5 Compliance support
- Accelerated compliance programs for cloud security
Pros
-
Government compliance specialization: Quzara focuses on FedRAMP and CMMC, which shortens ramp time for teams pursuing federal certifications.
-
Comprehensive managed services: The firm offers MDR and cloud security services that cover advisory, monitoring, and response across regulated environments.
-
US citizen analyst staffing: Security operations staffed by US citizen analysts helps address government suitability and contract requirements.
-
Recognized readiness posture: Public positioning as a top MSSP and FedRAMP High Ready status supports credibility during procurement and audits.
Cons
-
Limited transparency on pricing and contract terms creates challenges when budgeting for multiyear compliance initiatives.
-
Primary focus on government and federal compliance reduces appeal for private sector buyers that need productized, horizontal solutions.
-
Service descriptions lack granular product detail, which makes technical comparisons with platform-based offerings difficult.
Who It's For
Quzara fits federal contractors, government agencies, and regulated organizations that must meet FedRAMP, Department of Defense, or CMMC requirements. Security leaders who need a partner for advisory, audit preparation, and persistent MDR will find the service alignment clear.
Unique Value Proposition
Quzara combines regulatory advisory with hands-on managed operations to move clients from assessment to sustained compliance. That end to end approach reduces vendor handoffs and speeds time to certification for cloud services and DoD impact level work.
Real World Use Case
A federal contractor engages Quzara to achieve FedRAMP High compliance, using Quzara’s readiness assessment, control remediation guidance, and MDR for continuous monitoring during and after authorization.
Pricing
Pricing is not specified on the website, which means procurement teams must request custom quotes and scope definitions to evaluate total cost of ownership and contract terms.
Website: https://www.quzara.com
SOCSoter Managed Cybersecurity Solutions

At a Glance
SOCSoter delivers a full managed security service that combines 24/7 SOC monitoring with compliance support and threat intelligence. The platform suits medium to large organizations that need continuous, human driven detection and response across hybrid environments.
Core Features
SOCSoter provides real time monitoring, a multi layered defense approach, and centralized visibility across endpoint network cloud and vulnerability management. The service includes customizable security strategies, unlimited integrations on a unified portal, and U.S. based analysts handling threat analysis and response.
Pros
-
Comprehensive coverage: The service addresses endpoint network cloud vulnerability management and compliance in a single offering, reducing vendor sprawl.
-
Human driven monitoring: U.S. based analysts provide 24/7 detection and incident response which improves investigation speed and reduces false positives.
-
Highly customizable: Solutions are tailored to organizational needs so controls and workflows align with existing processes and regulatory requirements.
-
Compliance focused reporting: The product emphasizes compliance frameworks and reporting which helps teams manage audits for frameworks like GDPR and HIPAA.
-
Unified portal analytics: A single portal with unlimited integrations simplifies management and improves visibility for security leaders and auditors.
Cons
-
Complexity for small teams: The platform can be complex for small organizations that lack security maturity and staffed SOC processes.
-
Opaque pricing: Pricing is not published and varies by configuration which makes budgeting and vendor comparison harder for procurement teams.
-
Onboarding required: The integrated platform requires onboarding to fully realize value which adds time before complete operational coverage.
Who It's For
SOCSoter fits medium to large organizations and security conscious enterprises that need scalable managed security with strong compliance capabilities. It matches companies with hybrid or cloud environments that require continuous monitoring and a partner to handle incident response and reporting.
Unique Value Proposition
SOCSoter combines human driven SOC operations with a centralized platform that supports unlimited integrations and customizable controls. This combination lets security leaders replace multiple point products with a single managed service focused on threat detection response and audit readiness.
Real World Use Case
A financial services firm uses SOCSoter to monitor its hybrid cloud and on premise systems while leveraging compliance services for GDPR and HIPAA. The firm gains continuous threat intelligence and faster incident containment which reduces the risk and cost of regulatory fines and breach remediation.
Pricing
Pricing is not specified publicly and varies based on service configuration and organizational needs. Procurement teams should request a tailored quote to evaluate total cost of ownership and managed service levels.
Website: https://www.socsoter.com
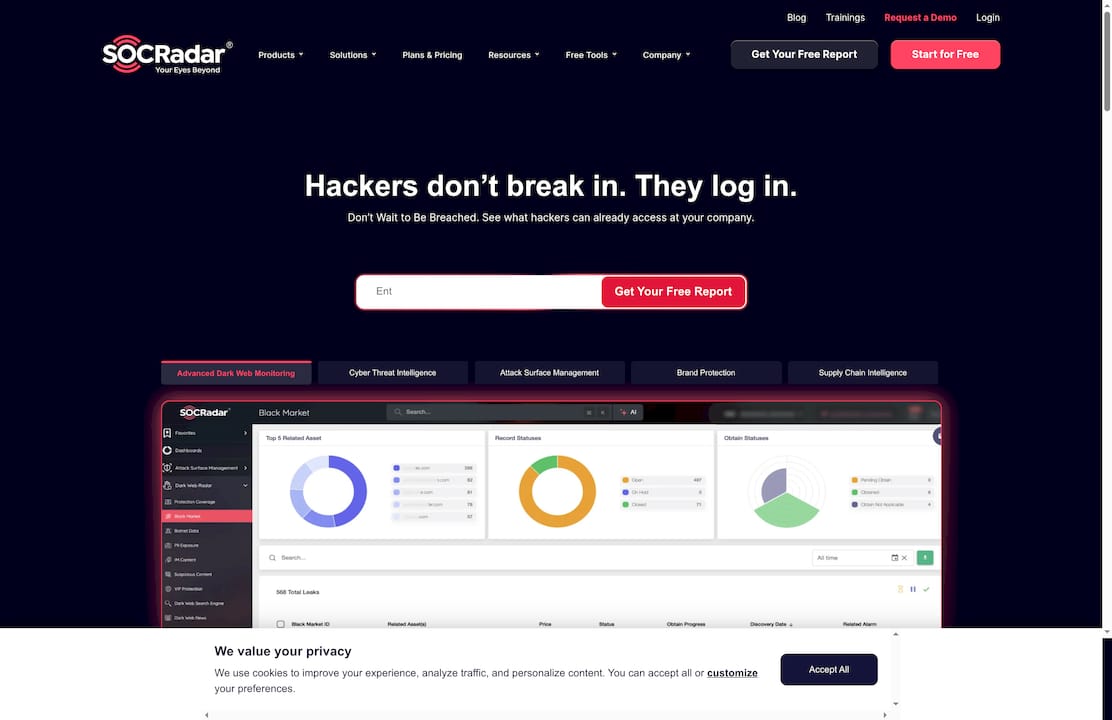
SocRadar
At a Glance
SocRadar focuses on security verification to separate legitimate users from malicious bots, offering a concise protection layer for web platforms. Its reliance on Cloudflare makes it a pragmatic choice for teams that want proven infrastructure without a heavy deployment burden.
Core Features
SocRadar provides three clear capabilities: user verification, general protection against cyber threats, and integration with Cloudflare's security infrastructure. The available information emphasizes verification and bot detection rather than a broad feature set, so the platform reads as a targeted tool for online traffic validation.
Pros
- SocRadar enhances website security by verifying users, which reduces automated abuse and lowers fraud rates for public facing sites.
- The platform utilizes Cloudflare, giving organizations access to proven edge security and global threat mitigation without building that layer themselves.
- SocRadar helps prevent malicious bot activities on websites, which protects scraping, credential stuffing, and automated account abuse.
- pros2 is listed in the source and appears as an additional benefit, though the scraped content lacks context for what that label represents.
- Easy to integrate with websites, which makes deployment faster for development teams that need a verification layer without deep architectural changes.
Cons
- The provided content contains limited information, which makes it hard to evaluate advanced detection capabilities or orchestration features in depth.
- SocRadar may rely on external security services that introduce additional costs, and the scraped data does not clarify pricing or licensing models.
- Specific features and capabilities are not detailed in the available content, leaving gaps around customization, reporting, and incident response.
Who It's For
SocRadar fits websites and online platforms that want to reduce bot-driven abuse and improve user verification without a large engineering lift. Security leaders at e-commerce firms, digital services, and public portals will find it relevant when they need focused bot protection rather than an enterprise detection platform.
Unique Value Proposition
SocRadar’s value is its narrow focus on verifying traffic combined with the operational strength of Cloudflare. That pairing gives security teams a lightweight, credible way to improve site integrity and reduce automated threats while avoiding the complexity of full security stacks.
Real World Use Case
An e-commerce company deploys SocRadar to validate checkout requests and new account signups. The result is fewer fraudulent orders, reduced chargebacks, and a measurable drop in automated scraping of price and inventory data, improving both revenue protection and customer trust.
Pricing
Pricing is not specified in the provided content, so procurement teams will need to contact the vendor for licensing, integration fees, and any Cloudflare related cost implications.
Website: https://www.socradar.io
Comprehensive Cybersecurity Tools Comparison
This table provides a detailed comparison of prominent cybersecurity tools and services as discussed in the article, helping you make an informed decision based on features, benefits, and target applications.
| Tool | Core Features | Pros | Cons | Pricing |
|---|---|---|---|---|
| Heights Consulting Group | Strategic advisory, governance, compliance, managed services with AI security. | Experienced team, field-tested methods, trusted by major organizations, aligns security with business goals. | No public pricing, requires tailored engagements. | Contact for tailored quote. |
| ThreatConnect | Integrated threat intelligence, risk management, and security operations platform. | Centralized intelligence, AI-driven, fosters collaboration, customizable, proven scale. | Complexity for smaller teams, requires integrations. | Contact for a tailored quote. |
| SOC Prime | AI-assisted detection engineering, threat detection content marketplace. | Extensive library, AI detection tools, supports automation, flexible deployments. | Requires initial setup effort, no public pricing. | Contact for customized options. |
| Quzara | FedRAMP and CMMC focused compliance advisory. | Specialized in government regulations, US-based analysts, managed detection & response. | Primarily for government environments, lacks horizontal solutions. | Contact for pricing details. |
| SOCSoter | 24/7 SOC monitoring, compliance, real-time threat intelligence. | Human-driven monitoring, centralized portal, customizable strategies. | May be excessive for smaller setups, requires onboarding. | Request a customized quote. |
| SocRadar | User verification, bot protection via Cloudflare infrastructure. | Enhances web security, straightforward integration, prevents automated abuse. | Limited details on advanced features, dependent on Cloudflare. | Pricing details not specified. |
Strengthen Your Regulatory Cybersecurity Strategy with Heights Consulting Group
Navigating the complex landscape of threat detection platforms for regulated industries requires more than technology. This article highlights challenges like integrating risk governance with technical controls and meeting compliance frameworks such as NIST, CMMC, and SOC 2. If your organization struggles with fragmented security tools or slow incident response times, you need a strategic partner who can unify advisory and managed services.
Heights Consulting Group offers proven expertise combining executive-level strategy with hands-on cybersecurity delivery. We tailor comprehensive programs that align with your business goals and compliance demands while accelerating your time to audit readiness. Discover how our risk-driven approach enhances threat hunting, incident response, and compliance management across highly regulated sectors.
Elevate your defense posture and simplify complex compliance requirements today by visiting Heights Consulting Group.

Ready to transform cybersecurity from a technical hurdle into a business advantage? Explore our strategic services at https://heightscg.com and take the first step toward a unified, resilient security program.
Frequently Asked Questions
What should I consider when selecting a threat detection platform for regulated industries?
Selecting a threat detection platform requires considering compliance requirements, such as HIPAA or CMMC, as well as the platform's ability to provide real-time monitoring and incident response. Assess your organization’s specific security needs and evaluate platforms based on their expertise in regulatory frameworks relevant to your industry.
How can threat detection platforms help improve compliance in regulated industries?
Threat detection platforms enhance compliance by providing continuous monitoring, automated reporting, and risk assessment tools that align with specific industry regulations. Implement a platform that integrates these features to streamline your compliance processes and reduce the time spent on audits by approximately 30%.
What are the benefits of using AI in threat detection for regulated industries?
Using AI in threat detection helps identify threats faster and more accurately, reducing the time taken to respond to incidents. Deploy a platform that utilizes AI to achieve quicker response times, potentially decreasing incident resolution from hours to minutes.
How do I evaluate the effectiveness of a threat detection platform in real-time?
To evaluate a threat detection platform's effectiveness in real-time, monitor its ability to detect and respond to incidences accurately and promptly. Set specific metrics, such as reducing false positives by at least 20%, and regularly review performance reports to measure success.
What features are essential in a threat detection platform for healthcare organizations?
Essential features for threat detection platforms in healthcare include compliance with HIPAA regulations, ability to secure patient data, and integration with existing health IT systems. Prioritize platforms that provide robust monitoring tools and incident response capabilities to maintain a high level of patient data protection.
How can I streamline my threat detection processes with a new platform?
Streamlining your threat detection processes can be achieved by selecting a platform that offers automation for routine tasks and integrates seamlessly with your current security infrastructure. Focus on platforms that allow for automated incident response workflows, which can improve efficiency by reducing manual efforts by approximately 40%.
