Nearly one in three American healthcare organizations now cite cybersecurity as their top operational risk. As the digital backbone of patient care becomes more complex, this challenge grows more urgent for every CISO and IT security manager. Establishing a modern Security Operations Center means going beyond basic defenses to align rapid threat detection, regulatory compliance, and clinical continuity within one cohesive strategy.
Table of Contents
- Defining A Security Operations Center In Healthcare
- Key SOC Types And Architectures Compared
- Core SOC Functions And Technology Stack
- SOC Staffing Models And Required Expertise
- Regulatory Compliance: HIPAA And Healthcare-Specific Standards
- Managing Risks, Costs, And Common Implementation Challenges
Key Takeaways
| Point | Details |
|---|---|
| Importance of SOC in Healthcare | A Security Operations Center is essential for protecting patient data and ensuring regulatory compliance amidst complex cybersecurity threats. |
| SOC Architectural Models | Organizations should carefully evaluate internal, external, and hybrid SOC models based on their specific needs, budget, and risk tolerance. |
| Core Functions and Technology | Modern SOCs utilize advanced technological stacks for real-time monitoring and incident response to safeguard sensitive medical information. |
| Compliance with HIPAA | Successfully integrating HIPAA standards into a SOC's operations is fundamental for maintaining patient privacy and security. |
Defining a Security Operations Center in Healthcare
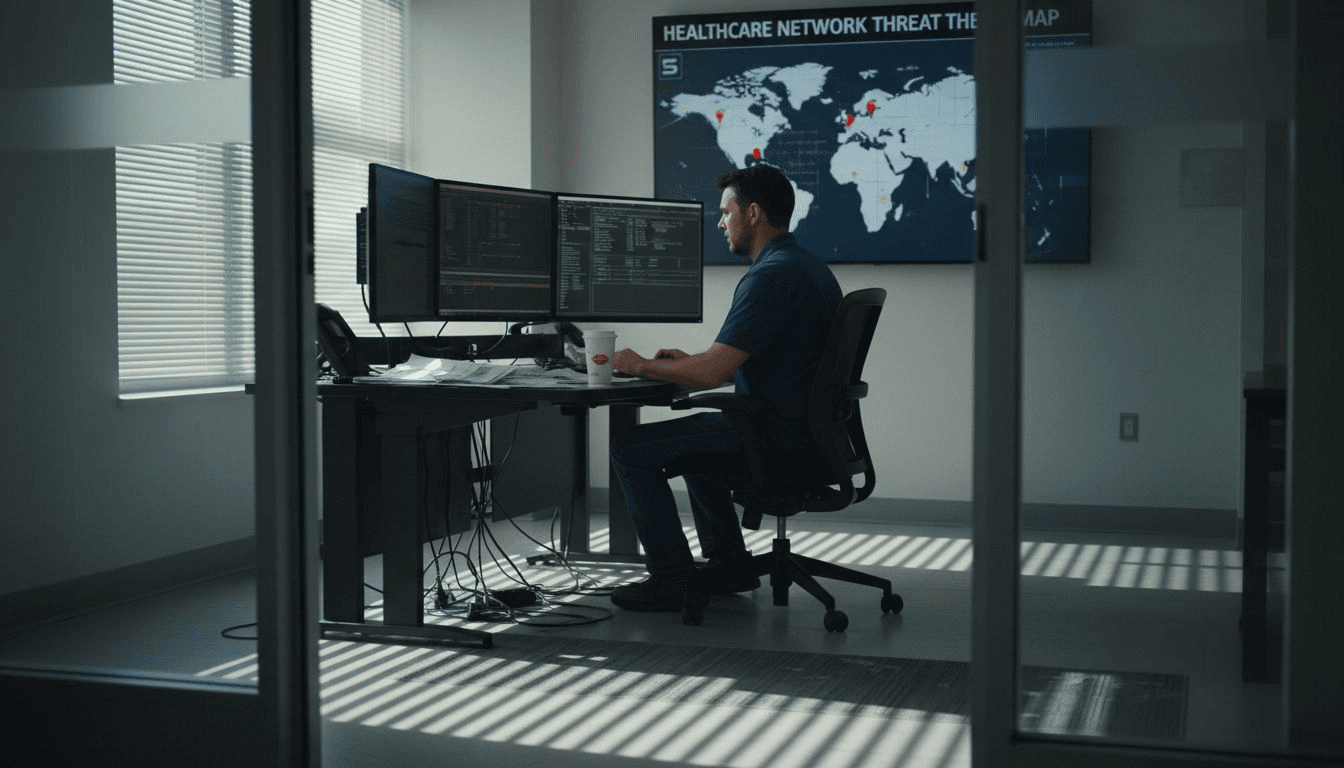
A Security Operations Center (SOC) represents the critical nerve center for protecting healthcare organizations from increasingly sophisticated cybersecurity threats. Modern healthcare SOCs address rising digital threats introduced by complex technological ecosystems like electronic health records, medical Internet of Things (IoT) devices, and interconnected remote care systems.
In healthcare settings, a SOC serves as a specialized cybersecurity unit charged with continuous monitoring, rapid threat detection, and strategic incident response. These centers integrate advanced technological capabilities with regulatory compliance requirements, ensuring patient data remains secure while maintaining operational integrity. Healthcare SOCs monitor, detect, and respond to cybersecurity threats against sensitive clinical information, protecting everything from patient records to critical medical infrastructure.
The fundamental components of a healthcare SOC typically include:
- Real-time system monitoring
- Advanced threat intelligence gathering
- Incident response and mitigation protocols
- Regulatory compliance tracking
- Staff cybersecurity awareness programs
Healthcare SOCs differ significantly from standard corporate security centers by maintaining an explicit connection to patient safety. Their mission transcends traditional IT security, directly linking technological defense mechanisms with clinical continuity and patient risk management.
Pro tip: Implement a comprehensive staff training program that integrates SOC awareness into routine clinical workflows to enhance overall organizational cybersecurity resilience.
Key SOC Types and Architectures Compared
Healthcare organizations have multiple Security Operations Center (SOC) architectural models to choose from, each with unique advantages and challenges. There are generally three main SOC types: internal, external, and hybrid, each designed to address different organizational cybersecurity needs and resource constraints.
Internal SOCs represent the most comprehensive model, where healthcare organizations maintain complete control and staffing of their security monitoring capabilities. These centers provide deep institutional knowledge, immediate incident response, and granular customization of security protocols. However, they require significant financial investment, specialized cybersecurity talent, and ongoing technological infrastructure maintenance.
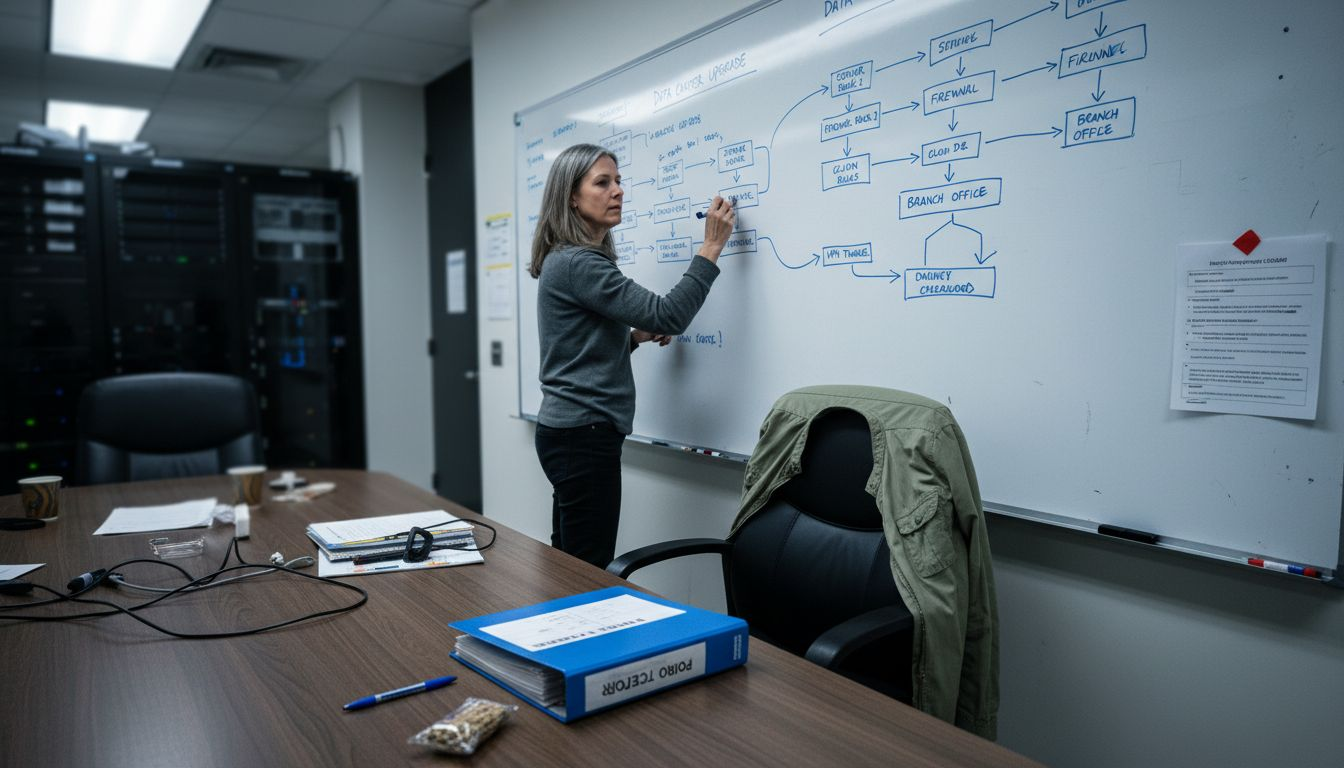
Managed Security Service Provider (MSSP) SOCs offer an alternative approach, providing external expertise and around-the-clock monitoring through third-party specialists. These service-based models compare distinctly with in-house SOCs in operational requirements and scalability. While they reduce internal resource burdens, they may introduce potential communication gaps and less precise understanding of an organization's unique technological ecosystem.
Hybrid SOC architectures represent a strategic middle ground, blending internal oversight with external monitoring capabilities. This model allows healthcare organizations to leverage specialized external expertise while maintaining direct control over critical security decision-making. Key characteristics include:
- Shared security responsibility
- Flexible resource allocation
- Balanced cost management
- Comprehensive threat coverage
- Scalable monitoring capabilities
The optimal SOC architecture depends on an organization's specific regulatory requirements, technological complexity, budget constraints, and risk tolerance. Healthcare providers must carefully evaluate their unique operational needs when selecting a SOC model.
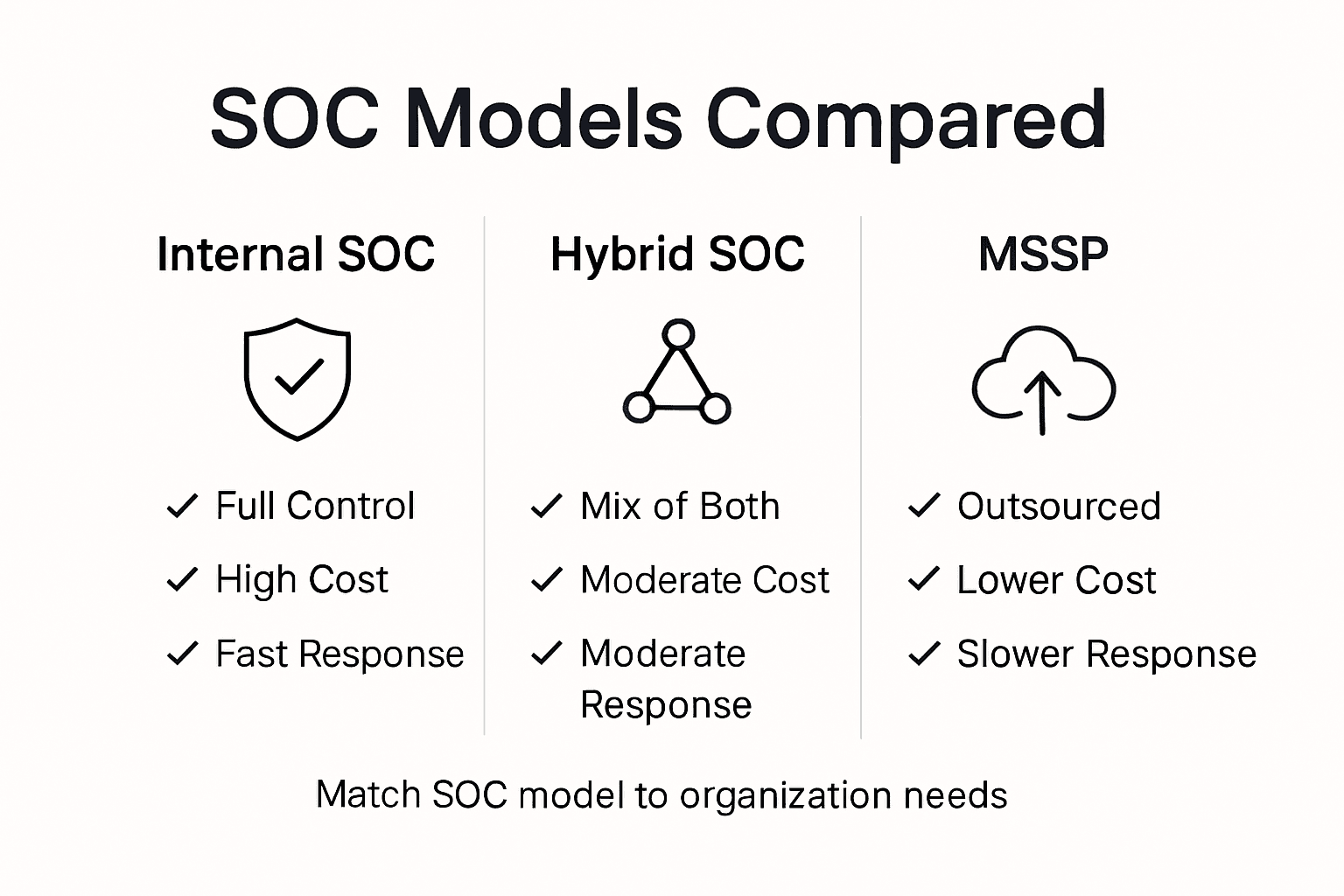
Here's a concise comparison of healthcare SOC architectural models and their organizational impact:
| SOC Model | Control Level | Cost Profile | Incident Response Speed | Customization Potential |
|---|---|---|---|---|
| Internal SOC | Full | High | Immediate | Extensive |
| External (MSSP) SOC | Limited | Variable | Moderate | Moderate |
| Hybrid SOC | Shared | Balanced | Rapid/Variable | Flexible |
Pro tip: Conduct a comprehensive risk assessment and resource inventory before selecting your SOC architecture to ensure alignment with your organization's specific cybersecurity objectives and operational capabilities.
Core SOC Functions and Technology Stack
A modern healthcare Security Operations Center (SOC) operates through a complex ecosystem of technological capabilities and strategic functions designed to protect sensitive medical infrastructure. Security Operations Centers perform essential functions such as real-time threat detection, security event analysis, and incident response coordination, creating a comprehensive cybersecurity defense mechanism.
The core technology stack of a healthcare SOC typically encompasses several critical platforms that work synergistically to identify, analyze, and mitigate potential security threats. Key technological components include:
- Security Information and Event Management (SIEM) platforms
- Endpoint Detection and Response (EDR) tools
- Intrusion Detection Systems (IDS)
- Threat intelligence feeds
- Case management tools
- Security Orchestration, Automation, and Response (SOAR) systems
A modern healthcare SOC technology stack integrates platforms for centralized security monitoring, dynamic incident response, and proactive threat hunting. These technologies enable security professionals to conduct comprehensive forensic analyses, monitor behavioral anomalies, and maintain continuous compliance with stringent healthcare regulations.
The functional capabilities of a healthcare SOC extend beyond mere technological implementation. Security teams must develop sophisticated processes for continuous threat identification, rapid incident triage, detailed investigation protocols, and strategic response mechanisms. This involves not just technological tools, but also highly trained personnel who can interpret complex security signals, understand healthcare-specific threat landscapes, and make critical decisions under time-sensitive conditions.
Pro tip: Regularly conduct tabletop exercises and simulated threat scenarios to validate your SOC's technological capabilities and team readiness in responding to potential cybersecurity incidents.
SOC Staffing Models and Required Expertise
Security Operations Centers require sophisticated staffing strategies that balance technical expertise, operational complexity, and strategic capabilities. SOC staffing models include 24x7 shift-based operations, tiered analyst structures, and hybrid teams with specialized skill sets, creating a multifaceted approach to cybersecurity workforce management.
Typical SOC staffing structures are organized into hierarchical tiers with distinct responsibilities:
- Entry-Level Analysts: Initial threat monitoring and basic incident triage
- Intermediate Analysts: Complex investigation and initial response coordination
- Advanced/Senior Analysts: Strategic threat hunting, forensic analysis, and advanced incident resolution
Critical SOC skills encompass a comprehensive range of technical and strategic competencies, including:
- Threat intelligence interpretation
- Security event correlation
- Vulnerability assessment techniques
- Malware analysis capabilities
- Regulatory compliance understanding
- Digital forensics expertise
Healthcare organizations must recognize that effective SOC staffing goes beyond technical skills. The most successful teams combine deep technological knowledge with strong communication abilities, adaptability, and a strategic understanding of organizational risk management. This requires continuous training programs, professional development opportunities, and a culture of collaborative problem-solving.
Pro tip: Implement a robust cross-training and mentorship program that allows junior analysts to learn from senior team members, creating a scalable and resilient cybersecurity workforce.
Regulatory Compliance: HIPAA and Healthcare-Specific Standards
Healthcare Security Operations Centers (SOCs) operate within an intricate regulatory landscape that demands rigorous compliance with Health Insurance Portability and Accountability Act (HIPAA) standards. Healthcare SOCs must ensure compliance by implementing administrative, physical, and technical safeguards that secure electronic protected health information (ePHI), creating a comprehensive approach to data protection and patient privacy.
The HIPAA Security Rule establishes three fundamental safeguard categories that SOCs must meticulously address:
- Administrative Safeguards: Policies and procedures governing information security management
- Physical Safeguards: Controls protecting physical access to electronic health information systems
- Technical Safeguards: Technological mechanisms controlling access and protecting data transmission
HIPAA requires formal risk analysis, security management, access restriction, and incident response policies for any system handling ePHI. This mandate compels healthcare organizations to develop sophisticated, adaptable compliance strategies that evolve with emerging technological and cybersecurity challenges. SOCs must demonstrate continuous vulnerability assessment, precise documentation of compliance measures, and robust incident response protocols.
Compliance is not a static achievement but a dynamic process requiring constant vigilance. Successful healthcare SOCs integrate regulatory requirements seamlessly into their operational frameworks, treating HIPAA compliance as a core component of their cybersecurity strategy rather than a separate, disconnected requirement.
The following table summarizes critical HIPAA safeguards and their implications for SOC operations:
| Safeguard Type | SOC Operational Focus | Impact on Patient Data Security |
|---|---|---|
| Administrative | Policy and procedure design | Ensures staff follow best practices |
| Physical | Facility and device controls | Protects system access points |
| Technical | Encryption and monitoring | Secures data in transit and at rest |
Pro tip: Conduct quarterly comprehensive risk assessments and maintain detailed documentation of all compliance activities to ensure ongoing HIPAA adherence and demonstrate proactive security management.
Managing Risks, Costs, and Common Implementation Challenges
Healthcare Security Operations Centers (SOCs) face increasingly complex cybersecurity landscapes that demand sophisticated risk management strategies. Common implementation challenges involve navigating the rising complexity of ransomware and supply chain attacks, scaling security for diverse clinical technologies, and ensuring cross-organization resilience, creating a multifaceted approach to organizational defense.
The primary risk management challenges in healthcare SOCs can be categorized into several critical domains:
- Technology Complexity
- Vendor and Third-Party Risk
- Financial Resource Constraints
- Regulatory Compliance Demands
- Evolving Threat Landscapes
Financial considerations play a pivotal role in SOC implementation, with organizations facing significant investments in technology, personnel training, and ongoing threat monitoring. The cost of a comprehensive SOC extends beyond immediate technological purchases, encompassing long-term strategic investments in human capital, continuous education, and adaptive security frameworks.
Successful SOC implementation requires a holistic approach that balances technological capabilities, financial constraints, and organizational risk tolerance. Healthcare providers must develop flexible, scalable security strategies that can rapidly adapt to emerging threats while maintaining operational efficiency and patient care continuity.
Pro tip: Develop a comprehensive risk assessment matrix that quantifies potential security threats, financial impacts, and mitigation strategies to create a data-driven approach to SOC resource allocation.
Elevate Your Healthcare Security Operations Center with Strategic Expertise
Healthcare organizations face unique challenges in building and operating an effective Security Operations Center (SOC). The article highlights critical pain points including managing complex SOC architectures, ensuring rapid incident response, meeting rigorous HIPAA compliance, and tackling rising cybersecurity risks like ransomware. These challenges demand not only advanced technology but also strategic staffing and continuous risk management to protect patient safety and sensitive data.
At Heights Consulting Group, we specialize in transforming your SOC into a strategic business asset. Our expert team delivers tailored cybersecurity consulting, managed security services, and compliance solutions designed for complex healthcare environments. From integrating cutting-edge threat hunting and endpoint detection to aligning your security program with healthcare-specific regulations and risk frameworks, we help you build resilience that goes beyond technology.
Unlock the full potential of your Security Operations Center today.

Discover how our hands-on approach to SOC staffing, incident response, and regulatory readiness can power your organization’s cybersecurity strategy. Contact Heights Consulting Group now for expert guidance and proven solutions that blend security with business value. Visit us at Heights Consulting Group to take the first step. Learn more about our managed cybersecurity services and strategic advisory tailored for healthcare leaders.
Frequently Asked Questions
What is a Security Operations Center (SOC) in healthcare?
A Security Operations Center (SOC) in healthcare is a specialized cybersecurity unit focused on continuous monitoring, rapid threat detection, and incident response to protect sensitive medical information and infrastructure from cyber threats.
What types of SOC architectures are available for healthcare organizations?
Healthcare organizations typically have three main SOC types: internal, external (managed security service provider), and hybrid SOCs. Each has distinct advantages and challenges regarding control, cost, and incident response capabilities.
What are the core functions of a healthcare SOC?
Core functions of a healthcare SOC include real-time threat detection, security event analysis, incident response coordination, compliance tracking, and promoting cybersecurity awareness among staff.
How does HIPAA compliance impact the operation of a healthcare SOC?
HIPAA compliance requires healthcare SOCs to implement strict administrative, physical, and technical safeguards to secure electronic protected health information (ePHI). This includes risk assessments, security management policies, access control, and incident response procedures.
Recommended
- What Is Security Risk Management Explained - Heights Consulting Group
- Cloud Security: Best Practices for Enterprise Protection
- Risk Management: Driving Business Resilience and Security
- Cybersecurity Insights &Leadership
- Supply Chain Risk Management: Safeguarding Global Trade - Worldwide Express, Inc.
- Complete Guide to Website Security for Businesses - ResponsiveWebsiteDesign
- Secure Removal Services Explained: Expert Guide for UK and North East Moves 2025 | Schott Removals