TL;DR:
- Security automation speeds response, reduces breach costs, and enhances regulatory compliance.
- Effective automation balances machine processes with human oversight for high-impact decisions.
- Successful programs require cultural change, clear governance, and executive leadership support.
The average data breach now costs organizations $3.92 million, yet many regulated enterprises still rely on manual security workflows that cannot scale to meet today's threat volume. For C-level executives, this is not a technical problem. It is a business risk with direct financial, reputational, and regulatory consequences. Security automation has emerged as the strategic lever that separates organizations that absorb these costs from those that prevent them. This article examines what automation means at the executive level, where it delivers measurable value in regulated industries, and how to implement it without sacrificing the human judgment that compliance frameworks demand.
Table of Contents
- What is security automation and how does it work?
- Strategic benefits of security automation for regulated industries
- Balancing automation with human oversight: best practices and pitfalls
- Implementing security automation: executive action plan
- Our perspective: The hidden upside (and challenge) few executives see
- Get expert guidance to accelerate your automation strategy
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Reduces risk and cost | Security automation cuts breach risk and associated costs for regulated organizations. |
| Enhances compliance | Automating key security tasks accelerates compliance and audit-readiness. |
| Strategic focus | Automation frees expert staff for high-impact strategy rather than repetitive tasks. |
| Maintain human oversight | Full automation is not suitable for all scenarios; executive oversight is critical for sensitive actions. |
| Plan for change | A phased, strategic approach ensures successful automation adoption and business alignment. |
What is security automation and how does it work?
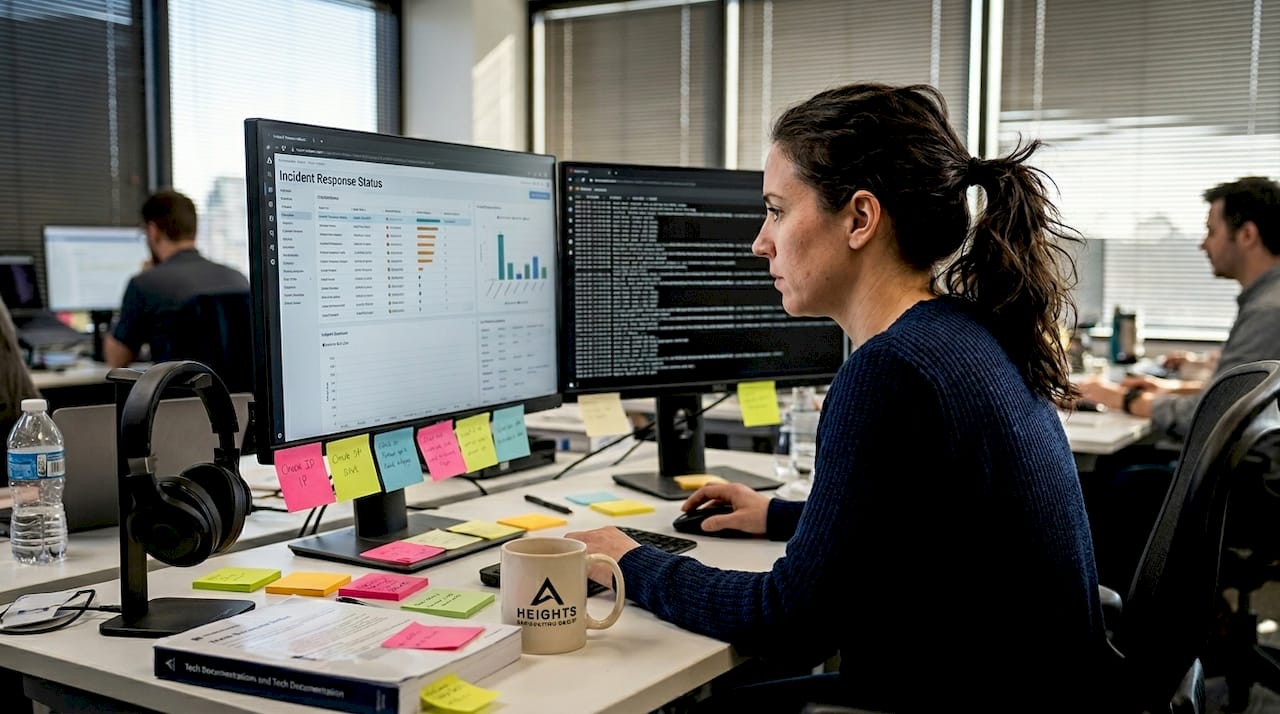
Security automation refers to the use of technology, software, and predefined playbooks to execute security tasks with minimal or no human intervention. Rather than relying on analysts to manually review every alert, investigate every anomaly, or coordinate every response action, automated systems perform these functions at machine speed and scale. The result is a security operation that responds faster, misses less, and frees skilled personnel for higher-order work.
At its core, automation operates by integrating data from multiple security tools, applying logic and rules to classify events, and triggering predefined responses. Platforms such as SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) are the primary engines. SIEM aggregates log data across the environment; SOAR adds workflow automation on top, enabling coordinated response actions across tools and teams.
Common use cases include:
- Alert triage: Automatically classifying and prioritizing thousands of daily alerts so analysts focus only on confirmed threats
- Phishing response: Isolating suspicious emails, extracting indicators of compromise, and notifying affected users without manual steps
- Vulnerability scanning: Scheduling and running scans, correlating results with asset criticality, and generating remediation tickets automatically
- User behavior analytics: Flagging anomalous access patterns in real time and triggering conditional access controls
Security automation reduces SecOps workload by handling routine tasks like alert triage and incident response, which allows analysts to concentrate on complex investigations. This is a critical distinction for executives: automation augments your security team, it does not replace it. The misconception that automation eliminates the need for skilled professionals is one of the most damaging beliefs in the industry. Organizations that operate under this assumption tend to underinvest in talent precisely when automation demands more strategic human oversight.
For organizations evaluating their security posture, virtual CISO services can provide the executive-level guidance needed to assess automation readiness and build a program aligned with business objectives. Similarly, understanding how automation supports navigating evolving regulations is essential for regulated organizations facing shifting compliance landscapes.
Strategic benefits of security automation for regulated industries
For organizations operating in banking, healthcare, defense contracting, or other regulated verticals, security automation is not simply an efficiency tool. It is a competitive and compliance advantage. The strategic benefits extend well beyond faster incident response.
Businesses with automated security are 1.5x more likely to meet their organizational goals — a finding that reflects automation's broader impact on operational performance, not just security outcomes.
The following table illustrates key strategic benefits across regulated industry verticals:
| Benefit | Healthcare | Financial Services | Defense/Government |
|---|---|---|---|
| Faster breach containment | Reduces HIPAA exposure window | Limits financial fraud impact | Shortens CMMC incident reporting time |
| Automated compliance reporting | Streamlines audit documentation | Accelerates SOX and PCI-DSS cycles | Supports continuous ATO processes |
| Reduced analyst burnout | Improves staff retention | Lowers operational risk from turnover | Maintains clearance-level continuity |
| Real-time threat detection | Protects patient data at scale | Monitors transaction anomalies 24/7 | Detects insider threats proactively |
Beyond the table, several strategic dimensions deserve direct attention:
- Reduced breach costs: Automated detection and containment shortens the breach lifecycle, which directly reduces remediation and regulatory penalty costs
- Compliance acceleration: Automation generates the audit trails, evidence packages, and reporting outputs that compliance frameworks require, reducing the labor burden on security and legal teams
- Analyst focus: When routine work is automated, your most experienced security professionals concentrate on threat hunting, architecture decisions, and strategic risk management
- Business resilience: Automated response capabilities mean that security operations continue functioning even during off-hours, holidays, or staffing gaps
Engaging technical cybersecurity consulting expertise helps organizations map these benefits to their specific regulatory environment and risk profile. Establishing a leadership workflow for compliance ensures that automation investments align with governance structures rather than operating in isolation from executive decision-making.
Balancing automation with human oversight: best practices and pitfalls
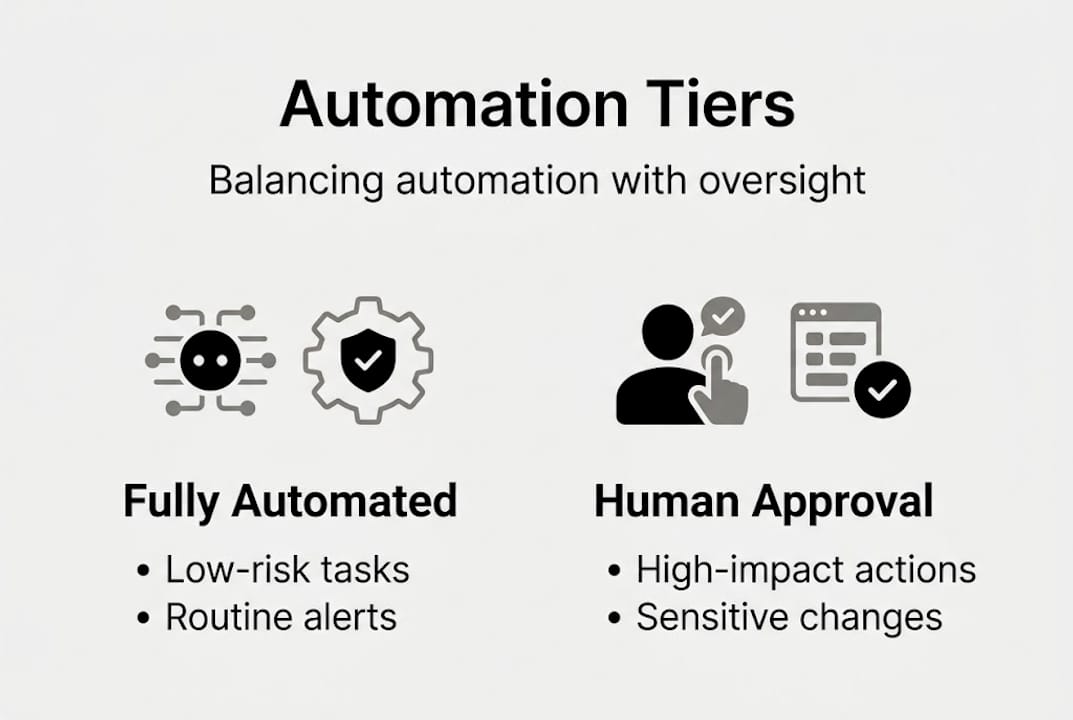
The most consequential mistake organizations make with security automation is treating it as a binary choice: either automate everything or automate nothing. Effective programs use a tiered model that matches the level of automation to the risk profile of each action.
Tiered automation means fully automating low-risk tasks, requiring human approval for high-impact decisions, and never fully automating irreversible actions. This principle is not just operationally sound. It is increasingly a regulatory expectation.
Comparison: automation tiers by action type
| Automation tier | Action type | Example |
|---|---|---|
| Full automation | Low-risk, high-volume, reversible | Alert triage, log correlation, scan scheduling |
| Human-in-the-loop | Medium-risk, significant impact | Account suspension, firewall rule changes |
| Human decision only | High-risk, irreversible | OT/ICS shutdowns, legal holds, breach notifications |
Best practices for compliance-conscious automation rollout:
- Document every automated action in an immutable audit log that satisfies regulatory evidence requirements
- Define escalation thresholds so that anomalies outside expected parameters automatically route to human analysts
- Test playbooks in a staging environment before deploying to production, particularly for actions that touch critical infrastructure
- Review and update playbooks quarterly to account for new threat patterns and regulatory changes
- Assign ownership to each automated workflow so accountability is clear during audits or incident reviews
Pro Tip: Map each automated action to a specific compliance control before deployment. This practice not only strengthens your audit posture but also helps justify automation investments to boards and regulators by demonstrating intentional, governance-aligned design.
For executives building proactive responses to emerging threats, establishing these boundaries early prevents costly rework later. Pairing automation with proactive cybersecurity monitoring ensures that human analysts remain engaged with the threat landscape rather than becoming passive observers of automated systems.
Implementing security automation: executive action plan
Moving from automation strategy to operational reality requires a structured approach. The following steps provide a practical framework for executives initiating or scaling automation programs.
-
Assess current state: Inventory existing security tools, workflows, and manual processes. Identify where analyst time is consumed by repetitive, low-judgment tasks. This baseline informs where automation will deliver the fastest return.
-
Define automation objectives: Align automation goals with specific business and compliance outcomes. Reducing mean time to respond (MTTR), achieving continuous compliance monitoring, or eliminating a specific category of manual reporting are all measurable targets.
-
Select a platform: Evaluate SOAR platforms based on integration capabilities with your existing stack, playbook flexibility, and vendor support for your compliance frameworks. SOAR playbooks include detection, enrichment, investigation, containment, and remediation steps with branching logic and human approval gates built in.
-
Pilot with low-risk use cases: Begin automation with high-volume, low-risk tasks such as alert triage or routine vulnerability scan scheduling. Measure outcomes against baseline KPIs before expanding scope.
-
Establish KPIs: Track metrics including reduction in manual analyst hours, MTTR improvement, false positive rate, and compliance reporting cycle time. These numbers tell the executive story of automation's value.
-
Scale and iterate: Once pilots demonstrate measurable improvement, extend automation to adjacent workflows. Revisit playbooks regularly and incorporate lessons from real incidents.
Pro Tip: Engage your virtual CISO services partner early in the platform selection process. A vCISO brings cross-industry experience that accelerates vendor evaluation and reduces the risk of selecting a platform that cannot scale with your compliance requirements.
For executives focused on aligning cybersecurity with business goals, this action plan provides the connective tissue between security investment and measurable organizational outcomes.
Our perspective: The hidden upside (and challenge) few executives see
After working with organizations across regulated industries, one pattern stands out clearly: most security automation failures are not technical failures. They are cultural ones. Organizations invest in capable platforms, build technically sound playbooks, and then watch adoption stall because analysts distrust the system, leadership lacks visibility into what is being automated, or no one owns the program's ongoing evolution.
The real upside of automation is not the hours saved on alert triage. It is what those hours become. When experienced analysts stop triaging noise, they start doing genuine threat hunting, architecture review, and adversarial thinking. That shift in cognitive focus is where regulated organizations build a durable security advantage.
Best-in-class organizations treat automation as a strategic enabler, not a headcount reduction strategy. The ones that succeed invest equally in the technology and in the cultural change management required to make it stick. Executives who frame automation as freeing their team to do more meaningful work will see far better outcomes than those who frame it as doing more with less. Addressing executive responses to security challenges with this mindset transforms automation from a cost center justification into a genuine capability investment.
Get expert guidance to accelerate your automation strategy
Security automation offers regulated organizations a measurable path to lower breach costs, faster compliance, and stronger operational resilience. But the gap between strategy and execution is where most programs lose momentum.

Heights Consulting Group helps C-level executives bridge that gap. Our technical cybersecurity consulting team works directly with security leaders to assess automation readiness, design governance-aligned playbooks, and build scalable programs that reduce adoption risk while accelerating ROI. Whether you are starting from scratch or optimizing an existing program, we bring the cross-industry experience needed to transform cybersecurity challenges into measurable business outcomes. Contact Heights CG to begin building your tailored automation roadmap today.
Frequently asked questions
What types of security tasks should always require human review?
High-impact, potentially irreversible actions such as operational shutdowns or investigation of ambiguous novel threats should always require human judgment. Irreversible actions like OT shutdowns carry adversarial risk and regulatory human oversight requirements that no automated system should bypass.
How does security automation help with compliance requirements?
Automation streamlines data collection, audit workflows, and incident response, helping regulated organizations achieve timely and accurate compliance reporting. Automating routine tasks like alert triage and incident response directly reduces the SecOps workload associated with evidence gathering and audit preparation.
What is a SOAR playbook and why is it important?
A SOAR playbook is an automated set of actions for common incident types, ensuring consistent and efficient response by merging detection, investigation, and remediation. SOAR playbooks include branching logic and human approval gates, making them adaptable to both routine and complex security scenarios.
Is security automation expensive to implement?
Upfront costs vary based on platform selection and integration complexity, but automation consistently lowers long-term spending by reducing breach costs and improving team efficiency. Organizations with automated security programs are 1.5x more likely to meet their organizational goals, reflecting a return that extends well beyond the security function.
Recommended
- Unlocking the Strategic Managed Security Services Benefits - Heights Consulting Group
- Unlocking Executive Advantage: Cybersecurity Simplified - Heights Consulting Group
- Key advantages of AI in cybersecurity for executives - Heights Consulting Group
- Managed Cybersecurity Services: Strengthen Your Strategy - Heights Consulting Group
- How to secure corporate banking: a step-by-step guide
