TL;DR:
- Healthcare cybersecurity incidents cost over 11 million dollars and often disrupt patient care.
- Leadership must integrate cybersecurity into strategic planning, risk management, and organizational culture.
- Combining frameworks like HIPAA and NIST with a focus on human behavior enhances digital health security.
Healthcare cybersecurity has never carried higher stakes. Breach costs average $10.93M to $11.3M per incident in today's threat environment, and 93% of organizations reported at least one cyberattack in the past year, with nearly three-quarters of those incidents directly disrupting patient care. For C-level executives and senior IT leaders, these numbers represent more than financial exposure. They signal a structural vulnerability in how digital health programs are planned, governed, and defended. This article provides a practical, strategic framework for aligning cybersecurity with compliance obligations and enterprise risk management, so your organization can move from reactive posture to durable resilience.
Table of Contents
- Why cybersecurity is foundational to digital health success
- Essential frameworks: HIPAA, NIST, and the regulatory-technical connection
- Mitigating risk: Core cybersecurity methodologies for digital health
- The real threat: Human factors, policies, and the sociotechnical approach
- From risk to opportunity: The C-suite agenda for digital health cybersecurity
- Why the human-technology balance is the hidden lever in digital health cybersecurity
- Partner with experts to fortify your digital health organization
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cybersecurity is foundational | Protecting digital health data is essential for patient safety, compliance, and reliable operations. |
| Framework alignment required | HIPAA and NIST are critical blueprints for setting legal, technical, and process controls in healthcare. |
| People drive risk outcomes | Human error contributes to major breaches, highlighting the need for training and culture alongside technology. |
| Risk methodologies transform outcomes | Effective risk assessments, encryption, and incident response are practical steps towards resilience. |
| C-suite must lead strategy | Executive engagement ensures cybersecurity becomes a strategic advantage rather than just a compliance box-tick. |
Why cybersecurity is foundational to digital health success
With the crisis starkly framed, it is essential to unpack why cybersecurity underpins every aspect of digital health progress. The integration of electronic health records, telehealth platforms, connected medical devices, and AI-assisted diagnostics has created extraordinary clinical potential. It has also dramatically expanded the attack surface facing every healthcare organization.
Cybersecurity in digital health is not simply a technical requirement. It protects patient data, ensures operational continuity, and prevents patient harm through regulatory compliance, risk management, encryption, training, and incident response working in concert. When any one of those elements fails, the consequences ripple outward far beyond the IT department.
Consider the operational dimension alone. When ransomware disables a hospital's electronic health record system, clinicians revert to paper processes, medication errors increase, and elective procedures are canceled. These are not hypothetical scenarios. 72% of cyberattacks against healthcare organizations in the past year disrupted patient care in measurable ways.
Understanding the healthcare risk management importance at the executive level means recognizing that cybersecurity failures carry both direct and indirect costs:
- Direct financial costs: Breach notification, regulatory fines, legal fees, system restoration, and ransom payments
- Operational disruption: Downtime measured in days or weeks, diversion of emergency patients, and delayed procedures
- Reputational damage: Patient trust erosion that drives volume losses over subsequent quarters
- Regulatory consequences: HIPAA enforcement actions, corrective action plans, and potential loss of participation in federal programs
- Long-term liability: Class action lawsuits from affected patients that can persist for years after the incident
"Cybersecurity in digital health must be understood at the board level as a patient safety imperative, not merely a compliance checkbox. The organizations that treat it as infrastructure investment consistently outperform peers on both resilience and regulatory outcomes."
For executives, this framing requires a shift in ownership. Conducting a thorough risk assessment in healthcare is not a task that belongs exclusively to the CISO. It belongs to the C-suite as a governance responsibility. The organizations that consistently weather cyber threats do so because leadership has embedded security into strategic planning, capital allocation, and organizational culture, rather than treating it as a back-office technical function.
Essential frameworks: HIPAA, NIST, and the regulatory-technical connection
Once the foundation is clear, C-level leaders need to know which frameworks set the agenda for action and how to align compliance efforts efficiently. Two frameworks dominate the digital health compliance landscape: HIPAA and the NIST Cybersecurity Framework. Understanding how they interact is essential for building a security strategy that satisfies regulators while delivering genuine risk reduction.
HIPAA security requirements mandate three categories of safeguards for the protection of electronic protected health information, or ePHI:
| Safeguard category | Key requirements | Examples |
|---|---|---|
| Administrative | Risk analysis, workforce training, access management policies | Security officer designation, sanction policies |
| Physical | Facility access controls, workstation use policies, device controls | Badge access systems, screen locks, media disposal |
| Technical | Access controls, audit controls, integrity controls, encryption | Unique user IDs, automatic logoff, data encryption |
The NIST Cybersecurity Framework, structured around five functions, Identify, Protect, Detect, Respond, and Recover, maps directly onto HIPAA's safeguard categories while providing more granular implementation guidance. NIST gives organizations a repeatable, measurable methodology for building controls that satisfy HIPAA's requirements and go beyond them.

Using the NIST framework in healthcare means your security program is anchored in a structured lifecycle rather than a static compliance checklist. Organizations that implement both frameworks in alignment benefit from reduced redundancy in their compliance programs, clearer audit trails, and faster identification of control gaps.
Understanding the compliance frameworks in healthcare is also critical for capital allocation. Executives who understand how NIST and HIPAA overlap can direct security investments toward controls that satisfy multiple requirements simultaneously, maximizing return on security spending.
Pro Tip: Design your security program to exceed minimum HIPAA requirements using NIST as the implementation guide. Organizations that treat HIPAA as a ceiling rather than a floor consistently face larger remediation costs when new threat vectors emerge, because their controls were calibrated to yesterday's minimum, not tomorrow's reality.
Mitigating risk: Core cybersecurity methodologies for digital health
With frameworks setting requirements, organizations need to be able to deliver. Here is what effective implementation looks like at the ground level, covering the technical and organizational methodologies that translate policy into protection.
Key methodologies for digital health cybersecurity include risk assessments, encryption standards such as AES-256 and TLS 1.3, access controls, employee training, incident response plans, and network segmentation. Each methodology addresses a distinct risk vector, and together they create overlapping layers of defense.
The following prioritized sequence reflects how executive teams should operationalize these tactics:
- Conduct formal risk assessments. A structured step-by-step risk assessment identifies assets, maps threats, quantifies vulnerabilities, and prioritizes remediation based on impact and likelihood. This is the essential first step because it determines where every subsequent dollar of security investment goes.
- Implement strong encryption. All ePHI at rest should be protected with AES-256. All ePHI in transit must be secured with TLS 1.3. These are not aspirational standards but operational baselines for any digital health organization.
- Deploy granular access controls. Role-based access control, multi-factor authentication, and the principle of least privilege ensure that only authorized personnel access sensitive data, and only to the extent their role requires.
- Segment your network. Medical devices, clinical systems, and administrative networks should operate on separate segments. Segmentation limits lateral movement by attackers who breach one part of the environment, preventing a device compromise from becoming an enterprise-wide incident.
- Build and test an incident response plan. A documented, practiced incident response plan reduces mean time to containment and mean time to recovery, two metrics with direct financial and clinical impact.
- Establish continuous employee training. Training is not an annual compliance event. It is an ongoing program tied to current threat intelligence, with simulated phishing, tabletop exercises, and role-specific modules.
| Methodology | Primary risk addressed | Compliance alignment |
|---|---|---|
| Risk assessments | Asset exposure, undetected vulnerabilities | HIPAA Security Rule §164.308(a)(1) |
| AES-256 / TLS 1.3 encryption | Data interception, unauthorized disclosure | HIPAA Technical Safeguards |
| Role-based access controls | Insider threat, unauthorized access | NIST Protect function |
| Network segmentation | Lateral movement, ransomware spread | NIST Protect / Recover functions |
| Incident response planning | Breach escalation, prolonged downtime | HIPAA §164.308(a)(6) |
Leveraging managed security for digital health can accelerate implementation of these methodologies, particularly for organizations without mature in-house security teams. Managed security partners provide continuous monitoring, threat intelligence, and rapid response capabilities that are difficult to sustain internally at equivalent cost and coverage.
Pro Tip: Treat your incident response plan as a living document. Test it with tabletop exercises at least twice per year, and update it after every significant threat intelligence development or regulatory change. Plans that have never been tested are not plans; they are paper artifacts.
The real threat: Human factors, policies, and the sociotechnical approach
Strategic defense is never just technology. It demands cultural and process excellence to close the most persistent gaps in any healthcare security program.
Research on human factors in cybersecurity consistently demonstrates that people remain both the greatest vulnerability and the largest opportunity in digital health security. 35% of data loss in healthcare organizations stems directly from policy non-compliance, making workforce behavior a primary risk driver that no technical control can fully substitute for.
The sociotechnical approach, which integrates people, technology, and organizational processes as a unified system, represents the most effective model for sustained security improvement. It recognizes that technical controls fail when workflows are cumbersome, when policies are unclear, or when staff lack the context to understand why compliance matters. Consider a few concrete examples of where the human factor creates outsized risk:
- Clinicians sharing login credentials to expedite access to urgent patient data, inadvertently disabling audit trail integrity
- Staff clicking phishing links in emails crafted to mimic internal IT communications, opening the door to credential theft
- Administrative personnel using personal devices on unsecured networks to access ePHI, creating unmonitored data pathways
- Third-party vendors with overly broad access permissions that are never reviewed after onboarding
Improving your security risk assessment impact requires explicitly including human behavior and workflow analysis in the assessment process. Security audits that evaluate only technical controls miss approximately a third of the actual risk environment.
"The sociotechnical model demands that executives see every policy, workflow, and training program as a security control. Culture is infrastructure. Behavior is your defense posture."
Executive leaders play a critical and irreplaceable role in change management. When the CEO treats a phishing simulation breach as a learning opportunity rather than a disciplinary event, when the CFO champions security training budget as a patient safety investment, and when the board receives regular security briefings with clinical outcome metrics alongside technical indicators, the organizational culture shifts. That shift reduces the behavioral attack surface in ways no firewall can replicate.
Optimizing your CISO risk assessment workflow to include behavioral risk indicators and policy compliance rates provides a more complete picture of your actual risk posture, not just your technical control coverage.
From risk to opportunity: The C-suite agenda for digital health cybersecurity
Armed with a thorough understanding of frameworks, risks, and the human element, it is time for the C-suite to drive real business value from strategic cybersecurity investment.
> Organizations that experienced a breach in the past year faced average costs of $10.93M to $11.3M per incident, with 93% reporting attacks and 72% experiencing care disruption. The cost of proactive investment is a fraction of the cost of reactive remediation.
The C-suite agenda for digital health cybersecurity should center on four strategic priorities:
- Risk prioritization with executive discipline. Use quantitative risk analysis, specifically, financial impact modeling tied to specific threat scenarios, to prioritize which vulnerabilities receive investment and which controls to implement first. Implement cyber risk management strategies that connect security metrics to business outcomes the board already tracks.
- Cross-functional oversight and board reporting. Create a cybersecurity steering committee with representation from clinical operations, legal, finance, IT, and compliance. Establish a regular cadence of board-level reporting that translates technical security posture into business risk language, using metrics such as mean time to detect, mean time to respond, and percentage of systems with current patch compliance.
- Continuous improvement through incident learning. Build formal processes for after-action review following every security incident, including near-misses. Organizations that institutionalize learning from incidents improve their mean time to detect by an average of 40% within 24 months of implementing structured review programs.
- Balance protection, compliance, and innovation. Security cannot become a barrier to digital health progress. Structured governance frameworks, including security-by-design principles embedded into new technology procurement, allow organizations to adopt telehealth platforms, AI tools, and connected devices without exposing new attack surfaces unnecessarily.
Understanding the managed cybersecurity benefits for organizations at the enterprise level reveals that strategic security investments consistently deliver positive ROI through avoided breach costs, reduced insurance premiums, faster regulatory audits, and increased patient and partner trust.
Why the human-technology balance is the hidden lever in digital health cybersecurity
After working through the frameworks, technical controls, and executive agenda, a harder truth deserves direct attention: the organizations that fail most spectacularly at cybersecurity do not typically fail because of insufficient technology. They fail because their culture treats security as someone else's problem.
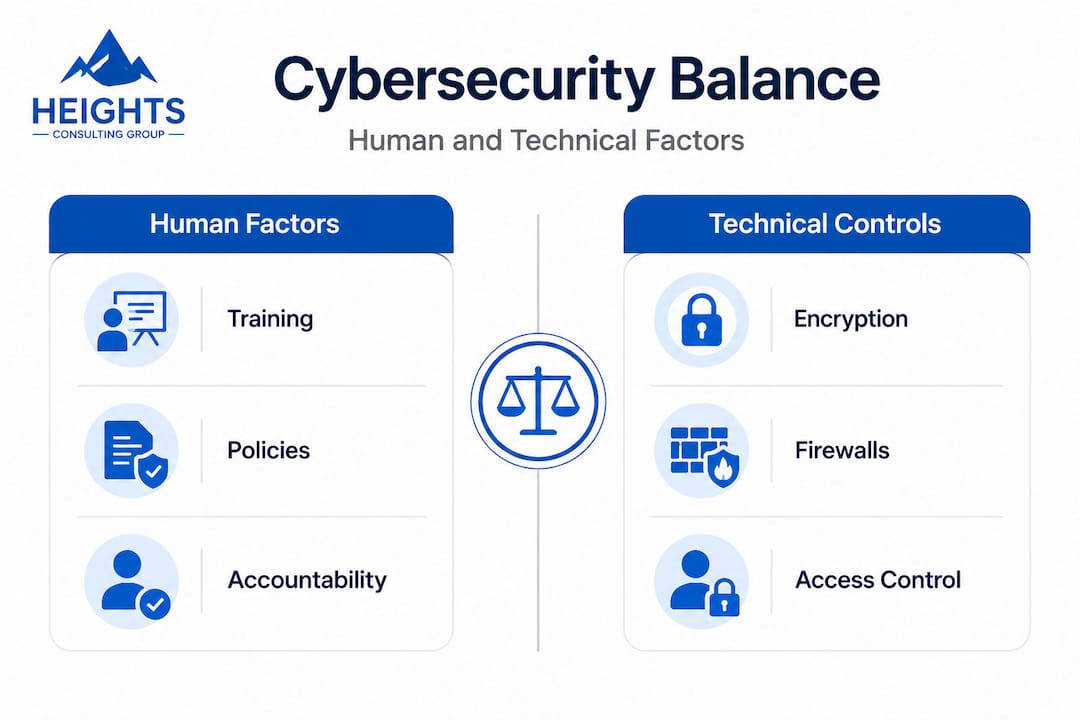
Most security breakdowns begin with policy, not code. A misconfigured access permission, an untested backup system, a training module that clinical staff skipped without consequence, these are the preconditions that turn a minor intrusion into a catastrophic breach. The technology was present. The governance was absent.
There is a meaningful difference between checkbox compliance and lived, resilient security practices. A healthcare organization can pass a HIPAA audit on Friday and suffer a devastating ransomware attack on Monday because the audit measured documentation, not behavior. Auditors check policies. Attackers exploit habits.
The contrarian view worth embracing is this: the most effective cybersecurity investment for the next phase of digital health is not a new detection tool or a more sophisticated SIEM platform. It is sustained, executive-led investment in culture, process clarity, and behavioral accountability. Technology amplifies a strong security culture. It cannot substitute for the absence of one.
Executive integration best practices consistently show that organizations where security is a board-level priority, where the CISO reports to the CEO rather than the CIO, and where security metrics appear alongside clinical quality metrics in leadership reviews, outperform peers on every meaningful security outcome. The return on that organizational investment exceeds the return on almost any point technology solution available.
The recommendation is straightforward. Invest as much in continuous education, policy clarity, and accountability structures as you invest in technical controls. Build a security culture where every employee from the front desk to the operating room understands their role in protecting patient data. That is the hidden lever most organizations have not pulled, and it may be the most powerful one available.
Partner with experts to fortify your digital health organization
Translating frameworks, methodologies, and cultural priorities into a functional, sustainable security program is a significant organizational undertaking. Most healthcare leaders recognize the destination clearly. The challenge is navigating the path without exhausting internal resources or creating compliance gaps along the way.

Heights Consulting Group brings specialized expertise in healthcare cybersecurity strategy, technical cybersecurity consulting, and compliance alignment to organizations at every stage of digital health maturity. From structured risk assessments and HIPAA-aligned security programs to managed cybersecurity services that deliver continuous protection without the overhead of building an in-house SOC, our team works alongside executive leadership to convert complex requirements into clear business value. If your organization is ready to move from reactive to resilient, contact our team to begin a strategic conversation tailored to your specific risk environment and compliance obligations.
Frequently asked questions
How do cybersecurity frameworks help with digital health compliance?
Frameworks like NIST and HIPAA provide structured controls and implementation guidance that satisfy legal, technical, and organizational compliance requirements, reducing audit risk and strengthening security posture simultaneously.
What is the typical financial impact of a healthcare cyber breach?
Healthcare breaches cost organizations an average of $10.93M to $11.3M per incident, making healthcare consistently the most expensive industry for breach-related losses, surpassing financial services and manufacturing.
Why are human factors so important in digital health cybersecurity?
Policy non-compliance drives 35% of healthcare data loss, meaning workforce behavior and training programs are as critical to security outcomes as any technical control deployed in the environment.
What are the must-have technical safeguards for digital health?
Core safeguards include formal risk assessments, AES-256 and TLS 1.3 encryption, role-based access controls, network segmentation, documented incident response plans, and continuous employee security training updated with current threat intelligence.