Cyberattacks in the financial sector rarely arrive with warning, yet the fallout can be swift and severe. For American CISOs, the difference between a contained breach and a costly crisis hinges on a robust, well-practiced incident response program. When regulatory bodies like the Federal Reserve and OCC scrutinize every move, a structured incident response process does more than manage threats—it demonstrates compliance, preserves trust, and supports business resilience.
Table of Contents
- Defining Incident Response In Cybersecurity
- Types And Phases Of Incident Response Programs
- Regulatory Drivers And Compliance Requirements
- Ciso Responsibilities In Incident Response Success
- Risk Mitigation And Business Continuity Impacts
- Common Pitfalls And Best Practice Solutions
Key Takeaways
| Point | Details |
|---|---|
| Structured Incident Response | A well-defined incident response framework reduces recovery time from weeks to hours, ensuring better containment and damage management. |
| Regulatory Compliance | Financial institutions must maintain documented incident response plans to meet regulatory expectations and protect against fines and reputational damage. |
| CISO Leadership | Strong leadership from the CISO is critical for setting incident response strategy, resource allocation, and ensuring clear communication across departments. |
| Continuous Improvement | Conducting regular post-incident reviews and training exercises helps organizations learn from breaches and refine their response plans for future incidents. |
Defining Incident Response in Cybersecurity
Incident response is the structured, coordinated approach your organization uses to identify, contain, and recover from security breaches or cyberattacks. Unlike reactive firefighting, it's a deliberate process built on frameworks, communication protocols, and documented procedures. For financial services firms facing regulatory pressure and constant threat activity, incident response transforms chaos into controlled action.
At its core, incident response serves three critical functions: detecting when a breach occurs, managing the damage in real-time, and preventing similar attacks in the future. Your security team doesn't just react to alerts. They follow playbooks, notify the right stakeholders, preserve evidence, and execute recovery steps in a predetermined sequence. This structured approach reduces recovery time from weeks to hours and prevents attackers from expanding their foothold.
Financial institutions face unique pressures that make incident response non-negotiable. A data breach costs banks an average of 4.82 million dollars according to recent industry data, but that number climbs when you factor in regulatory fines, customer notifications, and reputational damage. Beyond dollars, regulators like the OCC and Federal Reserve expect documented incident response capabilities as part of your compliance posture. Your incident response plan isn't optional—it's audited.
The difference between organizations with mature incident response and those without shows up when attacks happen. Teams with clear playbooks contain breaches faster, lose less data, and maintain operational continuity. Teams without them spend weeks investigating, often discovering more damage after initial response concludes. The structured process prevents key information from falling through cracks and ensures nothing gets overlooked in the chaos.
Incident response also bridges the gap between cybersecurity and business leadership. It gives your CISO a language to communicate risk to the board, a framework to request resources, and measurable ways to demonstrate progress. When your incident response plan works, you have data to show faster detection times, reduced dwell time, and better containment outcomes. That's what drives executive buy-in and budget allocation.
Pro tip: Start documenting your incident response plan today, even if it's basic—having a rough playbook is infinitely better than improvising during an actual breach when stress and confusion reign.
Types and Phases of Incident Response Programs
Incident response programs follow a structured lifecycle that ensures your organization responds consistently and effectively to security breaches. Rather than treating each incident as a unique problem requiring improvisation, your team works through defined phases that build on each other. This framework, developed by leading security organizations, helps financial firms move from chaos to coordinated action.
The five phases of incident response are Preparation, Detection and Analysis, Containment, Eradication and Recovery, and Post-Incident Activity. Each phase serves a distinct purpose and requires different skills, tools, and decision-making processes. Your CISO doesn't manage all phases the same way—what works in preparation doesn't work during containment.

Preparation starts before any breach occurs. Your team builds incident response playbooks, trains staff on their roles, establishes communication channels, and deploys detection tools. Think of this as building muscle memory before the game starts. Banks that skip this phase spend weeks fumbling when attacks happen. Those with solid preparation contain breaches in hours instead of days.
Detection and Analysis happens when alerts fire and your security team investigates whether a real threat exists or a false alarm. Speed matters here. The faster you confirm a breach, the faster you move to containment. This phase requires trained analysts who know how to interpret logs, hunt suspicious activity, and escalate appropriately.
Containment, Eradication, and Recovery form the crisis response portion. Containment stops the bleeding—isolating affected systems so attackers cannot spread further. Eradication removes the attacker from your environment completely. Recovery restores systems to normal operations. This phase demands clear decision-making authority, because delays cost money and expose more data.
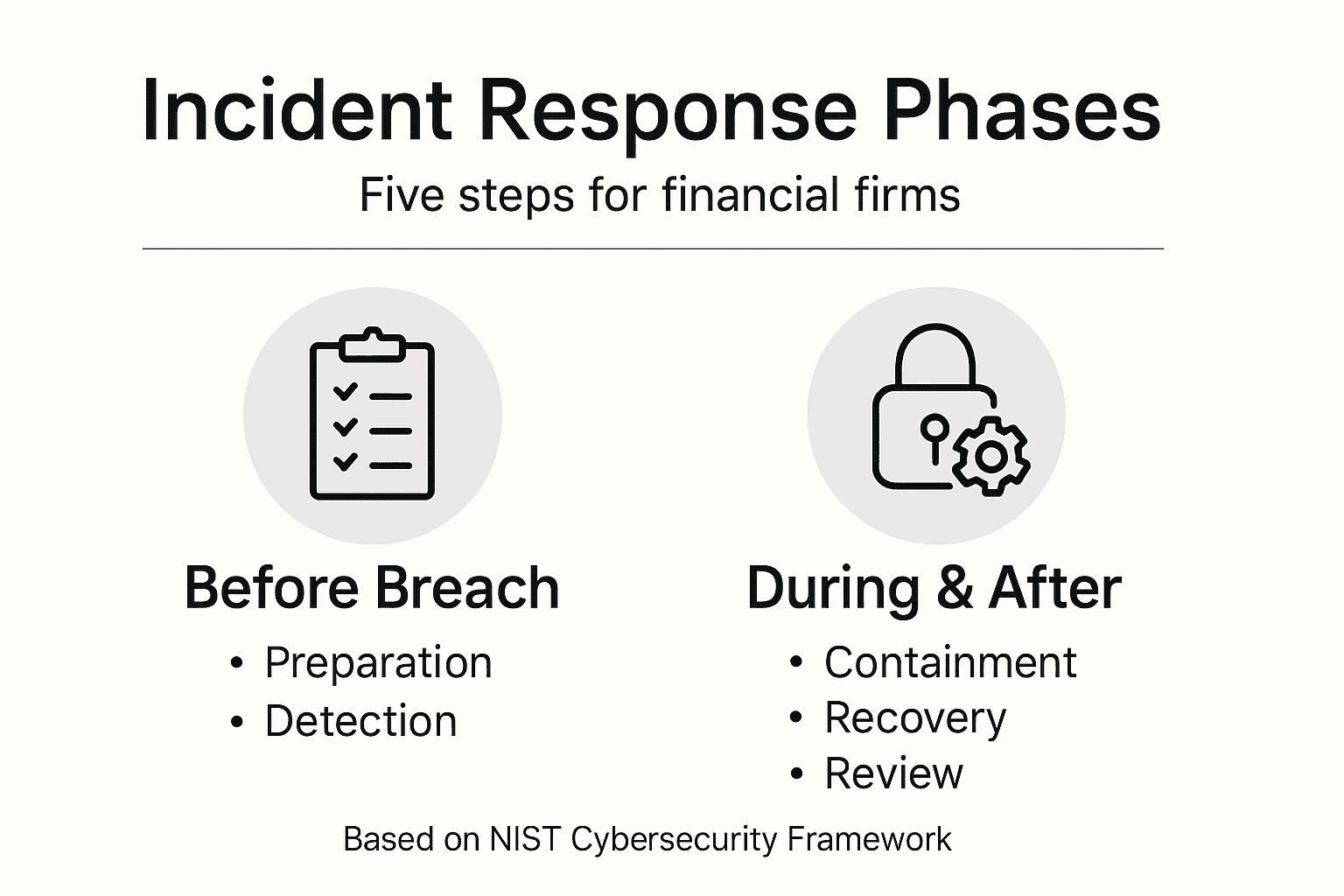
Post-Incident Activity happens after you've recovered. Your team documents what happened, identifies what went wrong, and updates playbooks so the next incident goes smoother. Organizations that skip this phase repeat the same mistakes repeatedly. Those that invest in learning improve their response capability significantly.
Financial firms often need tailored incident response types based on their environment. Insider threats require different responses than ransomware. Payment processing breaches trigger different regulatory notifications than customer data leaks. Your program should account for these variations with specific playbooks.
Here is a structured summary of the five core phases of an incident response program:
| Phase | Main Objective | Key Activities | Business Benefit |
|---|---|---|---|
| Preparation | Readiness before attacks | Build playbooks, train staff | Faster response times |
| Detection & Analysis | Identify and validate threats | Investigate alerts, analyze evidence | Early breach identification |
| Containment | Limit attacker impact | Isolate systems, restrict spread | Minimize data loss |
| Eradication & Recovery | Remove threats and restore functions | Clean up, restore systems | Restore operations quickly |
| Post-Incident Activity | Learn and improve | Review actions, update procedures | Continuous improvement |
Pro tip: Map your current incident response phases to NIST frameworks right now—identify which phases are strong and which ones lack documentation or training, then prioritize closing the biggest gaps.
Regulatory Drivers and Compliance Requirements
Regulators view incident response as non-negotiable. Your financial institution operates under constant scrutiny from the Office of the Comptroller of the Currency, the Federal Reserve, the Securities and Exchange Commission, and state banking authorities. Each of these bodies expects documented incident response capabilities as a baseline requirement, not a nice-to-have feature.
The regulatory landscape doesn't mandate one specific incident response tool or process. Instead, regulators expect your organization to demonstrate that you have a coherent plan, trained personnel, and the ability to execute under pressure. Regulatory incident reporting standards require financial institutions to notify regulators within specific timeframes when breaches occur. Depending on the type of data compromised and the number of customers affected, you may need to notify customers as well.
Different regulations apply depending on your institution's structure and what data you handle. Banks handling cardholder data must comply with Payment Card Industry standards. Those managing health information must meet HIPAA requirements. Firms trading securities face SEC cybersecurity rules that went into effect in 2023. Each framework demands specific incident response capabilities, documentation, and timely reporting.
What regulators really care about is your ability to contain breaches quickly and limit customer harm. An incident that spreads across your entire network for 180 days looks far worse to examiners than one you detected and contained in 24 hours. Your incident response program demonstrates to regulators that you take cybersecurity seriously and have invested in defensive capabilities.
Beyond regulatory compliance, incident response protects your institution's reputation and operational continuity. A breach notification process that takes weeks erodes customer trust. A containment process that fails allows attackers to steal more data. Regulators understand this connection, which is why they increasingly scrutinize your incident response capabilities during examinations.
Your CISO should treat regulatory requirements as a floor, not a ceiling. Meeting minimum standards leaves you vulnerable. Leading financial firms build incident response capabilities that exceed regulatory expectations, allowing them to respond faster and more effectively than competitors.
Pro tip: Schedule a regulatory gap assessment immediately to identify which specific regulatory requirements apply to your institution, then map your current incident response capabilities against those requirements to pinpoint compliance gaps.
CISO Responsibilities in Incident Response Success
Your CISO owns incident response success at the organizational level. This doesn't mean they execute the technical response themselves, but they set the strategy, allocate resources, establish accountability, and ensure the organization can execute under pressure. When a breach occurs at 2 AM, your CISO is the person who decides whether to take systems offline, how to communicate with the board, and when to notify regulators.
A critical CISO responsibility is building and maintaining the incident response program itself. This means creating playbooks, training teams, securing budget for detection tools, and establishing clear decision-making authority before incidents occur. CISOs balance technology with business needs while managing compliance obligations. Without this foundational work, your organization responds chaotically when attacks happen.
CISOs must establish clear roles and responsibilities during incidents. Who has authority to shut down a production system? Who communicates with customers? Who briefs the CEO and board? Who decides when to involve law enforcement? Ambiguity during a breach costs hours you cannot afford to lose. Your CISO creates clarity through documented procedures and regular tabletop exercises.
Communication across departments falls squarely on the CISO's shoulders. IT operations needs to understand incident response isn't just a security team problem. Finance needs to understand the budget impact of downtime. Legal needs to know notification obligations. Human Resources needs to understand insider threat protocols. Without clear cross-departmental alignment, incident response fails even if the technical team executes perfectly.
Your CISO also bears responsibility for post-incident learning. After each breach, your organization should be stronger and more prepared than before. This means conducting blameless post-incident reviews, updating playbooks, retraining staff, and closing security gaps that made the incident possible. CISOs who skip this step watch the same attack succeed twice.
CISO success requires executive sponsorship. If your CISO lacks access to the CEO and board, incident response capabilities remain underfunded and underprioritized. Leading CISOs cultivate relationships with the CFO, COO, and Chief Legal Officer before incidents occur, making it easier to mobilize resources when breaches happen.
Compare how CISO leadership impacts incident response outcomes versus a lack of clear ownership:
| Attribute | Strong CISO Leadership | Weak or No Leadership |
|---|---|---|
| Decision Authority | Clearly defined | Ambiguous, slow reactions |
| Team Coordination | Cross-department alignment | Delayed or fractured action |
| Budget and Resources | Proactive allocation | Undersupported program |
| Post-Incident Learning | Continuous improvements | Repeat mistakes, missed gaps |
| Board Communication | Timely, accurate | Reactive, incomplete |
Pro tip: Define your CISO's incident response authority in writing today and share it with the executive team, specifying which decisions they can make independently and which require escalation to the board.
Risk Mitigation and Business Continuity Impacts
Incident response directly reduces your financial institution's risk exposure and protects operational continuity. When your team detects and contains a breach within hours instead of days, you prevent attackers from stealing additional data, accessing customer accounts, or disrupting payment processing. That containment difference translates into millions of dollars saved in potential liability and regulatory fines.
Business continuity planning and incident response work together. A strong incident response program identifies which systems are critical to operations and prioritizes their protection. Effective business continuity planning ensures your institution can restore critical functions quickly when breaches occur. Without this coordination, you might contain a breach but still lose customer trust because your recovery takes weeks.
Your institution's reputation is a business asset. A breach notification that reaches customers weeks after the incident damages trust more severely than one sent immediately after detection. Banks that respond quickly demonstrate control and transparency. Those that delay create perception of incompetence or cover-up attempts. Incident response capability directly impacts whether customers stay or flee to competitors.
Downtime costs are brutal in financial services. Every hour your trading platform is offline costs thousands in missed transactions and trades. Every hour your payment processing system is down affects your institution and every customer trying to move money. A well-executed incident response minimizes downtime by containing damage, preserving system availability, and enabling faster recovery.
Operational continuity during disruptions requires resilience built into your infrastructure, backup systems, and recovery procedures. Your incident response program must identify single points of failure, test recovery procedures regularly, and maintain data backups in geographically dispersed locations. Organizations that skip this preparation discover critical gaps during actual breaches.
Risk mitigation also includes third-party risk management. Your incident response program should account for threats introduced by vendors, payment processors, and technology partners. A breach affecting your service provider could cascade into your systems. Leading financial firms extend incident response coordination to critical third parties.
Pro tip: Test your incident response plan quarterly with tabletop exercises that simulate realistic breach scenarios, measuring how quickly your team detects, contains, and recovers from simulated incidents.
Common Pitfalls and Best Practice Solutions
Financial firms repeatedly make the same incident response mistakes, often learning only after a breach exposes the gaps. The most damaging pitfall is treating incident response planning as a checkbox exercise rather than a strategic capability. Your organization creates a plan, files it away, and never tests or updates it. When a real breach occurs, the plan is outdated, irrelevant, or nobody remembers what it says.
Another critical mistake is unclear roles and responsibilities. During a breach, your team wastes precious time debating who decides to notify customers, who communicates with regulators, and who has authority to shut down systems. This ambiguity during a crisis costs hours you cannot recover. Clear communication channels and defined policies must be established before incidents occur, not improvised during them.
Insufficient training represents a major blind spot. Your incident response plan means nothing if team members have never practiced executing it. Banks that conduct annual tabletop exercises catch gaps in their playbooks, discover communication failures, and identify missing tools. Those that skip exercises deploy untested procedures during real incidents.
Many firms isolate incident response within the security team, creating coordination failures. When IT operations, legal, finance, and communications don't understand incident response responsibilities, response becomes fractured. Best practice requires cross-functional alignment where every department knows how incidents affect their function and what they need to do.
Failure to update response plans after incidents is a pattern that repeats failures. Organizations that conduct post-incident reviews, identify root causes, and update playbooks improve continuously. Those that skip post-incident analysis encounter the same attack twice.
Best practices emphasize ongoing training and secure system design combined with continuous monitoring and rapid software updates. These foundational practices reduce your attack surface and enable faster detection when threats do penetrate. Layering detection capabilities with well-practiced response procedures multiplies your effectiveness.
Leading financial firms treat incident response as a competitive advantage, investing in talent, tools, and continuous improvement. They test response capabilities quarterly, update playbooks based on emerging threats, and measure response times relentlessly.
Pro tip: Schedule your next tabletop exercise for this quarter, invite representatives from IT, legal, finance, and communications, and measure how quickly your team executes each phase of incident response.
Strengthen Your Incident Response with Strategic Cybersecurity Support
Financial firms face enormous challenges in building and maintaining effective incident response programs that meet strict regulatory requirements while minimizing operational disruption. The article highlights critical pain points such as unclear decision-making authority, gaps in preparation and training, and the costly consequences of slow breach containment. If you are striving to transform your incident response from a reactive headache into a controlled, strategic advantage you need expert guidance that aligns cybersecurity with your business objectives.
At Heights Consulting Group we specialize in helping financial institutions develop mature incident response programs tailored to their unique environments. Our services include technical implementation of endpoint detection and threat hunting, advisory on compliance frameworks like NIST and SOC 2, and ongoing support for crisis communication and post-incident improvement. We empower CISOs to establish clear authority, build playbooks, and ensure rapid containment and recovery.
Take control of your cybersecurity future today Heights Consulting Group offers integrated cybersecurity solutions that convert incident response from a costly risk into a competitive edge.

Ready to reduce breach impact and meet regulatory demands with confidence Contact Heights Consulting Group now to schedule your personalized incident response readiness assessment and start turning chaos into coordinated action.
Frequently Asked Questions
What is the main purpose of an incident response plan in financial firms?
The main purpose of an incident response plan in financial firms is to provide a structured approach to identifying, containing, and recovering from security breaches or cyberattacks, ensuring quick recovery and minimizing damage.
What are the key phases of an incident response program?
The key phases of an incident response program include Preparation, Detection and Analysis, Containment, Eradication and Recovery, and Post-Incident Activity, each serving a distinct function in the response process.
How does incident response support compliance with regulatory requirements?
Incident response supports compliance with regulatory requirements by demonstrating that a financial institution has a coherent plan, trained personnel, and the ability to respond quickly to breaches, which regulators expect as a baseline standard.
Why is it important for the CISO to establish clear roles during an incident?
It is crucial for the CISO to establish clear roles during an incident to ensure prompt decision-making, avoid confusion, and minimize delays when responding to a breach, ultimately protecting the organization from further damage.
Recommended
- Incident Response: Build Effective Cybersecurity Teams
- Cyber Risk in Financial Services: Managing Modern Threats
- Incident Response Readiness Assessment for Security - Heights Consulting Group
- Data Security in Financial Services A Strategic Guide - Heights Consulting Group
- Cybersecurity for Insurers, tools and best practices - Digital Insurance Platform | IBSuite Insurance Software | Modern Insurance System
- Understanding Online Payment Security: Essential Insights|CS
- What Does Incident Response Mean in A Legal Context?