Regulated organizations face mounting pressure to implement risk management workflows that satisfy both compliance mandates and evolving cybersecurity threats. C-level executives must navigate complex frameworks like NIST CSF 2.0 and GSA RMS Revision 6 while maintaining operational efficiency and business continuity. This guide delivers a strategic, stepwise approach to building effective risk management workflows aligned with 2026 standards, helping cybersecurity leaders transform risk management from a compliance burden into a competitive advantage that protects enterprise value and supports business objectives.
Table of Contents
- Understanding Risk Management Workflows In Cybersecurity
- Preparing For A Risk Management Workflow: Assessing Your Organization's Landscape
- Executing And Maintaining Your Risk Management Workflow For Regulatory Compliance And Security
- Common Pitfalls And Pro Tips For Successful Risk Management Workflows
- Enhance Your Risk Management With Heights Consulting Group
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Framework alignment | Updated standards like GSA RMS Rev 6 and NIST CSF 2.0 provide modern guidance for integrated enterprise risk management in 2026. |
| Five core workflow steps | Effective risk management follows a structured cycle: identify, assess, mitigate, monitor, and review risks continuously. |
| Framework integration benefits | Combining ISO 27001 governance with NIST flexibility creates comprehensive security postures that satisfy multiple compliance requirements. |
| Risk register elevation | Translating technical risks into enterprise-level data enables executive decision-making and strategic resource allocation. |
| Continuous adaptation | Regular workflow updates aligned with evolving threats and regulations maintain effectiveness and compliance over time. |
Understanding risk management workflows in cybersecurity
Risk management workflows integrate multiple critical steps: identification, assessment, mitigation, monitoring, and reporting. These interconnected processes create a systematic approach that transforms scattered security activities into cohesive enterprise protection strategies. The Risk Management Strategy guide Revision 6 aligns with CSF 2.0 and updated procedural guides, reflecting modern enterprise risk management requirements for 2026.
Frameworks like NIST CSF and ISO 31000 provide standardized approaches that guide organizations through risk identification, assessment, and mitigation with proven methodologies. These frameworks ensure consistency across departments and enable benchmarking against industry standards. When you implement the NIST framework alongside complementary standards, you create layered defenses that address both technical vulnerabilities and governance gaps.
Workflow clarity directly supports regulatory compliance by establishing documented procedures that auditors can verify and stakeholders can understand. Organizations that maintain transparent risk workflows reduce enterprise exposure by identifying threats earlier and responding faster to incidents. A strategic approach enables executable plans tailored to your organizational objectives, resource constraints, and risk appetite.
Pro Tip: Map your existing security activities against a cybersecurity risk management framework to identify gaps and redundancies before building new workflows.
Consider these essential workflow components:
- Risk identification processes that capture threats from internal and external sources
- Assessment methodologies that quantify likelihood and impact using consistent metrics
- Mitigation strategies that balance cost, feasibility, and risk reduction effectiveness
- Monitoring systems that track control performance and detect emerging threats
- Review cycles that incorporate lessons learned and adapt to changing conditions
The 2025 update to the GSA RMS guide reflects significant shifts in how federal agencies and regulated industries approach cybersecurity risk. This revision emphasizes integration between cybersecurity and enterprise risk management, recognizing that cyber threats impact business operations, financial performance, and strategic objectives. Organizations that align their workflows with these updated standards position themselves for smoother audits and stronger security postures.
Effective workflows also support executive communication by translating technical risks into business impact terms. When you present risks as potential revenue loss, operational disruption, or regulatory penalties, leadership can make informed decisions about security investments. This translation capability becomes crucial during budget cycles and strategic planning sessions where cybersecurity competes with other business priorities.
Preparing for a risk management workflow: Assessing your organization's landscape
Successful workflow implementation begins with comprehensive preparation. Start by mapping critical assets including data repositories, production systems, intellectual property, and customer information. This inventory establishes what you need to protect and helps prioritize security efforts based on asset value and criticality. Risk identification includes recognizing critical assets, potential threats, and vulnerabilities to establish a baseline for all subsequent activities.
Understanding your threat landscape requires analyzing both generic and targeted threats relevant to your industry and geographic location. State-sponsored actors target intellectual property and critical infrastructure, while cybercrime organizations focus on financial gain through ransomware and data theft. Insider threats, whether malicious or accidental, represent another significant risk category that workflows must address. Your guide to risk assessment cybersecurity should account for threat actor capabilities, motivations, and historical targeting patterns.
Framework selection depends on your industry, regulatory requirements, and organizational maturity. Financial services organizations often combine NIST CSF with sector-specific guidance, while healthcare entities integrate HIPAA requirements. Defense contractors must address CMMC alongside NIST 800-171. Accurate cybersecurity risk assessments include system architecture understanding and realistic impact evaluations for decision-making, which requires selecting frameworks that match your technical environment and compliance obligations.
Pro Tip: Document cybersecurity requirements with clear rationales linking each control to specific threats, vulnerabilities, or compliance mandates to streamline future audits and justify security investments.
Follow these preparation steps in sequence:
- Conduct comprehensive asset inventory across all business units and IT environments
- Analyze threat intelligence specific to your industry, size, and geographic footprint
- Review applicable regulations and compliance frameworks that govern your operations
- Assess current security controls and identify gaps against selected frameworks
- Document baseline risk posture including known vulnerabilities and control deficiencies
- Establish risk appetite and tolerance levels aligned with business strategy
Your preparation phase should also include stakeholder engagement across departments. Finance teams provide input on acceptable risk levels and budget constraints. Legal counsel advises on regulatory interpretation and liability concerns. Operations leaders identify business-critical processes that cannot tolerate disruption. This cross-functional input ensures your workflow addresses real business needs rather than purely technical considerations.
System architecture documentation proves essential for accurate risk assessment. You need detailed network diagrams, data flow maps, and dependency charts that show how systems interconnect. This documentation reveals single points of failure, trust boundaries, and attack paths that adversaries might exploit. Organizations with poor architecture documentation consistently underestimate their risk exposure and struggle to implement effective controls.
Consider engaging strategic cybersecurity governance expertise during preparation to avoid common pitfalls and accelerate workflow development. External advisors bring industry benchmarking data, lessons learned from similar implementations, and objective perspectives on your security posture. They also help navigate complex regulatory requirements and translate technical findings into executive-friendly business impact assessments.
Executing and maintaining your risk management workflow for regulatory compliance and security
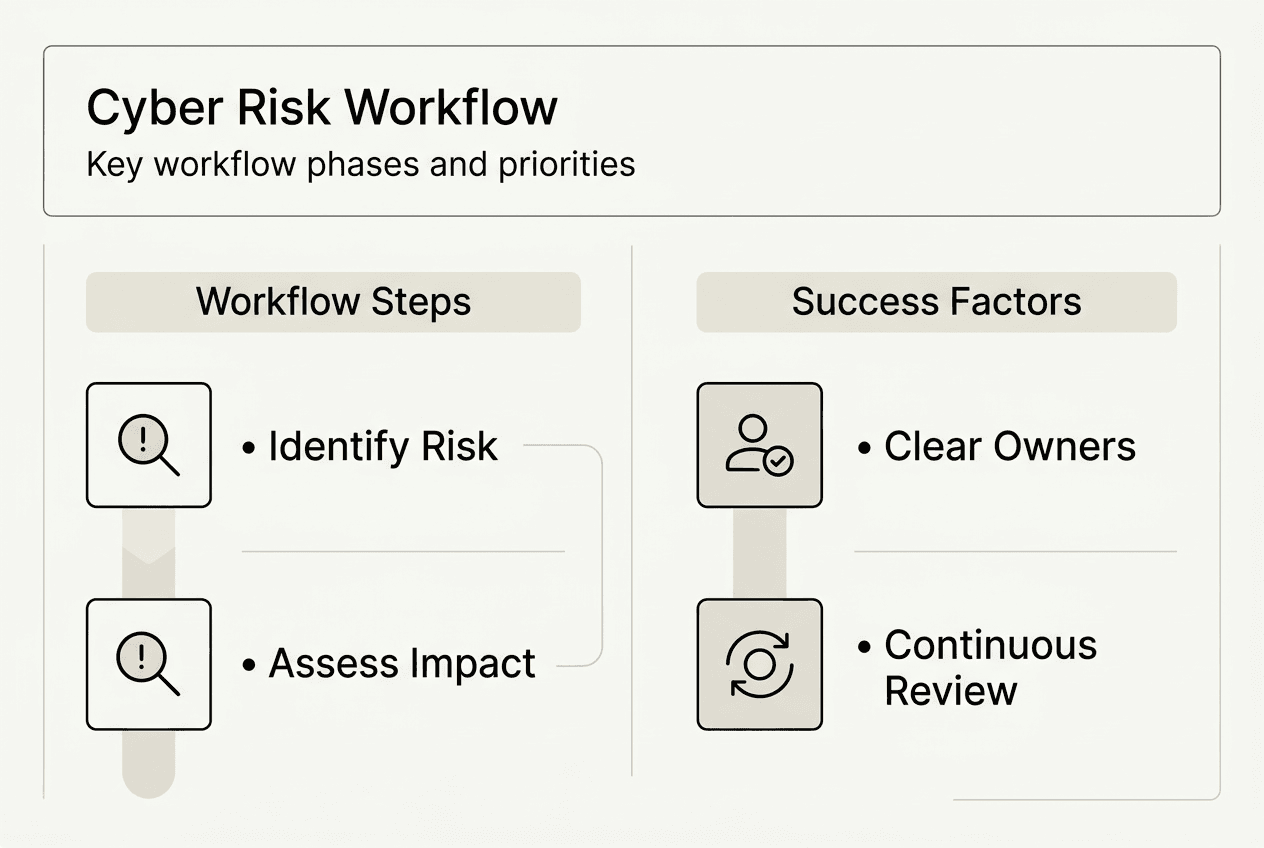
Workflow execution follows five core steps that create a continuous improvement cycle. First, identify risks through threat modeling, vulnerability scanning, penetration testing, and security assessments. Second, assess each risk by evaluating likelihood and potential impact using quantitative or qualitative methods. Third, mitigate risks through control implementation, risk transfer, acceptance, or avoidance strategies. Fourth, monitor controls continuously to verify effectiveness and detect degradation. Fifth, review outcomes regularly to capture lessons learned and adapt to changing conditions.
Risk registers serve as central repositories that translate detailed cybersecurity risks into aggregated enterprise data for governance and decision-making. These registers document risk descriptions, likelihood scores, impact assessments, mitigation strategies, control owners, and status updates. Executive dashboards pull from risk registers to provide leadership with current risk postures without overwhelming them with technical details. Effective registers use consistent scoring methodologies and clear definitions that enable comparison across different risk categories.
Framework integration amplifies workflow effectiveness. The NIST framework identifies, protects, detects, responds, and recovers from cyber incidents in a flexible manner that adapts to organizational needs. When combined with ISO 27001's governance structure and control requirements, you create comprehensive coverage that satisfies multiple compliance obligations simultaneously. This integration reduces duplication, streamlines audits, and strengthens overall security posture.
Follow these execution steps for sustained effectiveness:
- Deploy automated tools for continuous vulnerability identification and threat detection
- Conduct quarterly risk assessments that incorporate new threats and organizational changes
- Implement controls based on risk priority, balancing effectiveness with resource constraints
- Establish monitoring dashboards that track control performance and security metrics
- Schedule regular reviews with executive stakeholders to communicate risk posture and resource needs
- Update workflows based on incident lessons learned and emerging threat intelligence
Pro Tip: Assign clear accountability for each risk and control to specific individuals with authority and resources to take corrective action when issues arise.
Your risk management business security approach should incorporate metrics that demonstrate workflow effectiveness. Track mean time to detect threats, mean time to respond to incidents, percentage of systems with current patches, and compliance audit findings. These metrics provide objective evidence of improvement and help justify continued security investments. They also enable benchmarking against industry peers and identification of areas requiring additional focus.
| Workflow Phase | Key Activities | Success Metrics | Review Frequency |
|---|---|---|---|
| Identification | Threat modeling, vulnerability scanning, asset discovery | Coverage percentage, new risks identified | Monthly |
| Assessment | Likelihood scoring, impact analysis, risk prioritization | Assessment completion rate, score consistency | Quarterly |
| Mitigation | Control implementation, risk acceptance, transfer decisions | Controls deployed, risk reduction achieved | Quarterly |
| Monitoring | Performance tracking, anomaly detection, compliance checks | Control effectiveness, incident detection rate | Continuous |
| Review | Lessons learned, workflow optimization, stakeholder updates | Action items completed, stakeholder satisfaction | Semi-annually |
Continuous improvement requires incorporating threat intelligence feeds that alert you to emerging attack techniques and vulnerabilities. Subscribe to industry-specific information sharing organizations, government advisories, and vendor security bulletins. When new threats emerge, assess their relevance to your environment and update risk registers accordingly. This proactive approach prevents surprises and demonstrates due diligence to regulators and auditors.
Your cybersecurity leadership workflow should also address organizational change management. New systems, business processes, and partnerships introduce new risks that workflows must capture. Establish procedures that trigger risk assessments during project planning phases, ensuring security considerations inform decisions before implementation. This shift-left approach reduces costly remediation and prevents security becoming a project bottleneck.
Integration with your cybersecurity risk management guide ensures consistency between strategic risk management principles and tactical workflow execution. Alignment between high-level strategy and day-to-day operations creates coherent security programs that deliver measurable business value.
Common pitfalls and pro tips for successful risk management workflows
Organizations frequently overcomplicate risk documentation, creating assessment templates so detailed that security teams spend more time on paperwork than actual security improvement. Simplify documentation to capture essential information: risk description, likelihood, impact, mitigation strategy, and owner. Detailed technical analysis belongs in supporting documents, not executive risk registers. Changing documentation perspective improves risk assessment clarity, transforming complex workflows into elegant decision tools.
Framework integration failures create duplication and gaps. Some organizations implement NIST, ISO 27001, and industry frameworks as separate parallel programs with different assessment cycles, control mappings, and reporting structures. This approach wastes resources and confuses stakeholders. Instead, create unified control libraries that map requirements across frameworks, conduct integrated assessments, and produce consolidated reports. Aligning frameworks reduces redundancy and strengthens cross-departmental accountability, supporting compliance across jurisdictions.
| Common Mistake | Consequence | Best Practice Alternative |
|---|---|---|
| Overly complex documentation | Assessment paralysis, outdated risk data | Streamlined templates focused on decision-making needs |
| Siloed framework implementation | Duplicated effort, coverage gaps | Integrated control libraries and unified assessment cycles |
| Static risk assessments | Missed emerging threats, compliance failures | Continuous monitoring with quarterly formal reviews |
| Unclear accountability | Delayed remediation, finger-pointing | Named control owners with authority and resources |
| Ignoring threat evolution | Outdated risk priorities, ineffective controls | Regular threat intelligence integration and scenario updates |
Pro Tip: Schedule annual workflow reviews from fresh perspectives by rotating assessment team members or engaging external reviewers who challenge assumptions and identify blind spots.
Avoid these critical mistakes:
- Treating risk management as a compliance checkbox rather than strategic business function
- Failing to update risk assessments when organizational changes occur
- Accepting risks without executive approval and documented rationale
- Implementing controls without verifying effectiveness through testing
- Neglecting to communicate risk posture changes to leadership promptly
Threat landscape neglect represents another common failure. Organizations conduct annual risk assessments but ignore mid-year threat developments like zero-day vulnerabilities, new attack techniques, or geopolitical events that shift threat actor focus. Establish processes that trigger rapid risk reassessments when significant threat changes occur. This agility prevents your workflow from becoming obsolete between formal review cycles.
Accountability gaps undermine even well-designed workflows. When risks lack clear owners or owners lack authority to implement controls, mitigation efforts stall. Assign risk ownership to individuals with budget authority, technical resources, and executive support. Document ownership in risk registers and hold owners accountable through performance reviews and security metrics.
Your approach to cyber risk management best practices should emphasize practical implementation over theoretical perfection. Start with core workflow elements, demonstrate value through early wins, then expand scope and sophistication over time. Organizations that pursue comprehensive workflows from day one often become overwhelmed and abandon efforts before achieving meaningful results.
Consider how unified compliance by design principles can streamline your workflow by building compliance into processes rather than treating it as separate validation activity. When controls serve both security and compliance purposes, you reduce overhead and improve stakeholder buy-in.
Enhance your risk management with Heights Consulting Group
Implementing effective risk management workflows requires expertise, experience, and strategic vision that balances security effectiveness with business practicality. Heights Consulting Group delivers tailored cybersecurity leadership workflow compliance success services designed specifically for regulated industries facing complex compliance requirements and evolving threat landscapes.

Our consultants bring deep experience with NIST CSF 2.0, ISO 27001, CMMC, and industry-specific frameworks, helping you build integrated workflows that satisfy multiple compliance obligations without duplicating effort. We provide hands-on support for risk assessment, framework selection, workflow design, and executive communication that transforms cybersecurity from technical burden into strategic business advantage. Our risk management business security approach ensures your workflows align with 2026 compliance requirements while supporting your unique business objectives. Contact Heights Consulting Group to discuss how we can accelerate your risk management success.
Frequently asked questions
What are the essential steps in a risk management workflow?
Identify risks through assessments and threat modeling, assess likelihood and impact using consistent scoring, mitigate threats with appropriate controls, monitor control effectiveness continuously, and review outcomes regularly to capture lessons learned. This five-step cycle creates continuous improvement that adapts to evolving threats and organizational changes.
How do updated frameworks like NIST CSF 2.0 impact risk workflows in 2026?
They provide modern, flexible guidance for integrated cybersecurity and enterprise risk management aligned with current threats and regulations. NIST CSF 2.0 emphasizes governance, supply chain security, and outcome-based metrics that help organizations demonstrate security effectiveness to stakeholders and regulators.
Why integrate ISO 27001 with NIST frameworks?
Integration fosters comprehensive governance through ISO 27001's structured requirements while maintaining NIST's flexible, risk-based approach to incident management. This combination improves security posture by addressing both systematic control implementation and adaptive threat response, satisfying multiple compliance requirements simultaneously.
How can risk registers improve executive decision-making?
They aggregate detailed technical risks into enterprise-level views that translate cyber threats into business impact terms like revenue loss, operational disruption, and regulatory penalties. This translation enables informed prioritization and resource allocation by presenting risks in language executives understand and can act upon.
What common mistakes should be avoided in risk management workflows?
Avoid overcomplex documentation that delays assessments, failure to update risks when threats or organizations change, siloed accountability that prevents effective remediation, and neglecting evolving threat landscapes between formal review cycles. These mistakes undermine workflow effectiveness and leave organizations vulnerable to emerging threats.