Managing security risks in a large American healthcare organization means more than ticking off compliance items. The stakes go beyond data privacy—patient safety, operational resilience, and financial stability are all interconnected. Enterprise Risk Management in healthcare requires tailored assessments that address unique clinical systems, evolving cyber threats, and complex regulatory obligations like HIPAA. This article clarifies how risk assessments create actionable priorities, protect patient information, and help you turn vulnerability insights into meaningful improvements for your entire organization.
Table of Contents
- Defining Risk Assessments In Healthcare Security
- Types Of Risk Assessments And Key Differences
- HIPAA Requirements And Legal Obligations Explained
- Integrating Assessments With Cyber Risk Management
- Common Pitfalls And How To Avoid Them
Key Takeaways
| Point | Details |
|---|---|
| Unique Aspects of Healthcare Risk Assessments | Risk assessments must address clinical, operational, and financial risks that directly impact patient care, not just compliance. |
| HIPAA Compliance Essentials | Periodic risk assessments are legally required and must encompass administrative, physical, and technical safeguards. |
| Assessment Methodologies | Utilizing both qualitative and quantitative assessments enhances understanding and prioritization of risks, with each method serving distinct purposes. |
| Common Pitfalls to Avoid | Ensure assessments are ongoing and involve multiple stakeholders to prevent incomplete inventories and missed threats. |
Defining Risk Assessments in Healthcare Security
Risk assessments in healthcare aren't generic security checklists. They're structured processes that identify vulnerabilities specific to your organization's electronic protected health information (ePHI), clinical operations, and infrastructure. For CISOs managing large healthcare systems, this distinction matters because healthcare risk differs fundamentally from other industries.
Healthcare organizations face interconnected risks across clinical, operational, and financial domains. A breach of patient records isn't just a data security issue—it disrupts patient care, triggers regulatory penalties, and damages reputation. That's why risk assessments must account for how cybersecurity threats intersect with clinical workflows and patient safety.
What makes healthcare risk assessments different:
- Clinical systems require 24/7 uptime; downtime directly harms patients
- ePHI involves sensitive data covering medical history, billing, and identifiable information
- Compliance frameworks (HIPAA, state privacy laws) impose legal liability for inadequate risk management
- Legacy systems in hospitals often can't be quickly patched without disrupting operations
- Third-party vendors and business associates create extended attack surfaces
Formally, risk assessment is the process of identifying threats, analyzing vulnerabilities, and evaluating the potential impact if those vulnerabilities are exploited. Risk assessment in complex systems goes beyond predicting what might happen—it requires understanding the psychological, organizational, and systemic factors that influence how threats materialize in your environment.
Your risk assessment isn't complete until it reflects how your specific workflows, staffing constraints, and vendor relationships create actual attack paths.
With an Enterprise Risk Management framework, healthcare leaders establish strategic priorities by analyzing which risks threaten operations, clinical outcomes, finances, and workforce stability. For your role as CISO, this means translating security vulnerabilities into business impact language your board understands.
Risk assessments form the foundation for HIPAA compliance. The Security Rule explicitly requires covered entities to conduct periodic assessments identifying risks to ePHI and implement controls proportional to those risks. Without documented assessments, you can't demonstrate compliance during audits or regulatory investigations.
The assessment process typically follows these stages:
- Inventory your assets (systems, data, infrastructure)
- Identify threats relevant to healthcare (ransomware, insider threats, supply chain compromises)
- Determine vulnerabilities that threats could exploit
- Analyze business impact if vulnerabilities are exploited
- Rate risk based on likelihood and severity
- Prioritize remediation based on risk levels
Your risk assessment output should guide your security investment roadmap. High-risk findings drive resource allocation. Medium-risk findings inform your monitoring strategy. Low-risk findings get documented but deprioritized. This translates abstract vulnerability data into actionable priorities.
Pro tip: Document your assessment methodology and scoring criteria before you start; this consistency makes year-over-year comparisons meaningful and demonstrates due diligence to regulators.
Types of Risk Assessments and Key Differences
Not all risk assessments work the same way. Your choice between assessment types depends on your data availability, timeline, budget, and organizational maturity. For CISOs, understanding these differences directly impacts how effectively you communicate risk to leadership and allocate remediation resources.
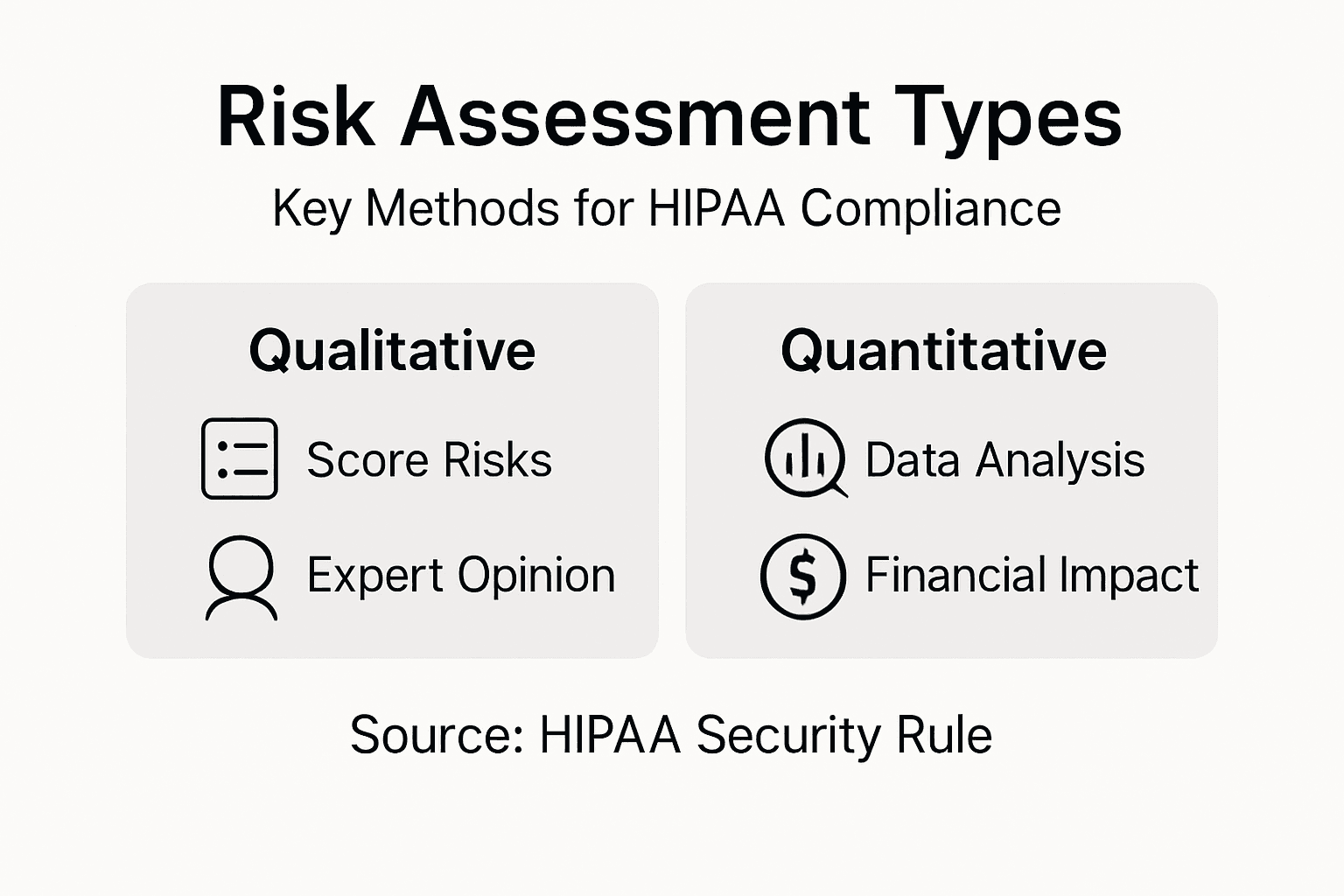
Healthcare risk assessments fall into two primary categories: qualitative and quantitative. Risk assessment methodologies vary in how they measure likelihood and impact, with qualitative approaches using descriptive language while quantitative approaches assign numerical values to create objective priority rankings.
Qualitative assessments rely on expert judgment and descriptive measures. You identify risks, describe them using terms like "high," "medium," or "low," and prioritize based on collective experience. This approach works quickly and requires less historical data, making it ideal when you need rapid baseline assessments.
When qualitative assessments work best:
- Initial risk scoping before detailed analysis
- Limited historical breach or incident data available
- Resource constraints prevent extensive data collection
- Stakeholder alignment needed on risk language
- Rapid compliance documentation required
Quantitative assessments assign numerical values to likelihood and impact, then calculate risk scores mathematically. You estimate probability percentages, assign dollar values to potential losses, and derive metrics like annualized loss expectancy (ALE). This produces defensible, objective data your board can understand.
When quantitative assessments work best:
- Mature security programs with historical incident data
- Budget justification requires financial impact projections
- Regulatory scrutiny demands objective evidence
- Year-over-year trend analysis shows improvement or decline
- Complex interdependencies need mathematical modeling
Beyond those two primary types, HIPAA specifically requires assessments covering three distinct safeguard domains. Administrative, physical, and technical safeguards address different vulnerability categories but must work together cohesively. Administrative safeguards cover workforce policies and training. Physical safeguards protect facility access and hardware. Technical safeguards control data access through encryption, authentication, and monitoring.
Most breaches result from gaps across multiple safeguard types, not failures in just one category—your assessment must evaluate all three layers.
Hybrid approaches combine both methods. You might use qualitative rankings to categorize risks initially, then apply quantitative analysis to high-risk findings requiring budget justification. This pragmatic approach balances speed with analytical rigor.
Your assessment scope also matters. A full-scope assessment examines all systems, locations, and data flows across your organization. A focused assessment targets specific systems, departments, or risk areas. Periodic reassessments track changes in threat landscape, technology, or compliance requirements.
The assessment type you select must align with your governance requirements, available expertise, and regulatory expectations. Most large healthcare organizations benefit from blending qualitative and quantitative methods—speed for initial scoping, precision for high-impact decisions.
Pro tip: Use qualitative assessments to establish baseline risk profiles, then apply quantitative analysis only to findings that would drive meaningful budget or remediation decisions—this optimizes your team's time while building credible business cases.
Here's a concise comparison of qualitative and quantitative healthcare risk assessment methods:
| Approach | Key Characteristics | Ideal Use Cases | Limitations |
|---|---|---|---|
| Qualitative | Relies on expert judgment, uses descriptive risk terms | Rapid baseline assessments, limited data environments | Less measurable, subjective outcomes |
| Quantitative | Uses numerical scoring, calculates financial impact | Budget justification, advanced security programs | Requires historical data, more resource-intensive |
| Hybrid (combined) | Starts qualitative, adds quantitative for high-priority risks | Balanced decision-making and resource allocation | May require multiple assessment cycles |
HIPAA Requirements and Legal Obligations Explained
HIPAA isn't a single rule—it's a comprehensive federal framework with three core components, each creating distinct legal obligations for your organization. As a CISO, understanding these obligations matters because they directly determine what your risk assessment must cover and what your board is legally liable for if compliance fails.
The Privacy Rule sets national standards protecting individuals' health information. The HIPAA Privacy Rule governs how covered entities use and disclose Protected Health Information (PHI), defines individual rights to access their records, and establishes administrative requirements for handling patient data. Violations trigger civil penalties ranging from $100 to $50,000 per violation, with annual maximums reaching millions.
The Security Rule extends privacy protections specifically to electronic PHI (ePHI). This rule requires three categories of safeguards: administrative (policies and access controls), physical (facility and hardware security), and technical (encryption and monitoring). Your risk assessment must address all three layers comprehensively.
The Breach Notification Rule mandates that you notify affected individuals if unsecured ePHI is compromised. Notification must occur within 60 days, with specific content requirements. Large breaches trigger media notification and reporting to the Department of Health and Human Services (HHS).
Your legal obligations include:
- Conducting periodic risk assessments identifying ePHI vulnerabilities
- Documenting all administrative, physical, and technical safeguards
- Implementing safeguards proportional to identified risks
- Training workforce members on privacy and security policies
- Executing Business Associate Agreements with third-party vendors
- Maintaining audit logs and monitoring for unauthorized access
- Reporting breaches to HHS and affected individuals within required timeframes
HIPAA compliance requires implementing safeguards tailored to your organization's size and complexity. You can't use a generic template—your controls must address your specific environment, systems, and threat landscape. This is exactly why individualized risk assessments form the foundation of HIPAA defense.
Covered entities include healthcare providers, health plans, and healthcare clearinghouses. Business associates—vendors processing ePHI on your behalf—share legal liability for compliance. If your cloud provider breaches patient data, you're both accountable.
Documented risk assessments are your primary legal protection; they prove you acted with due diligence even if a breach occurs.
The Office for Civil Rights (OCR) enforces HIPAA through investigations triggered by complaints or breaches. OCR looks first at your risk assessment documentation. If it's absent, outdated, or incomplete, OCR assumes you didn't identify foreseeable risks, which constitutes negligence and eliminates defenses against penalties.
Penalties vary by violation category. Unintentional violations incur $100-$50,000 per incident. Violations resulting from willful neglect increase to $10,000-$50,000 per incident. Systematic failures across your organization can accumulate to millions in liability.
Your risk assessment must be documented, specific to your environment, and updated periodically. It should identify threats, vulnerabilities, and current safeguards, then recommend improvements. This documentation demonstrates compliance intent and provides evidence of your governance process.
Pro tip: Document your risk assessment methodology, scoring criteria, and board approval explicitly—this creates an audit trail proving informed decision-making and reasonable risk management, which regulators recognize as due diligence even when breaches occur.
This summary table outlines HIPAA rules and their relevance to healthcare security:
| HIPAA Rule | Main Focus | Impact on Healthcare Security | Enforcement Details |
|---|---|---|---|
| Privacy Rule | Protects patient data and access rights | Sets standards for patient information handling | Civil penalties per violation |
| Security Rule | Safeguards electronic PHI (ePHI) | Requires multi-layer risk assessments and controls | Must document risk assessments |
| Breach Notification | Mandates notice after data compromise | Obligates timely reporting and transparency | Annual maximums for penalties |
Integrating Assessments with Cyber Risk Management
Risk assessments exist within a larger cybersecurity strategy—they're not standalone compliance exercises. For CISOs at large healthcare organizations, the real power comes from integrating HIPAA risk assessments into your broader cyber risk management program. This integration transforms compliance documentation into actionable intelligence guiding your security investment roadmap.

Traditional HIPAA risk assessments focus on protecting ePHI through administrative, physical, and technical safeguards. Cyber risk management takes a broader view, prioritizing threats that could disrupt operations, compromise patient data, or undermine clinical systems. When integrated properly, these two approaches reinforce each other rather than compete for resources.
Healthcare's threat environment has shifted dramatically. Cyber threats endangering patient safety now include ransomware targeting billing systems, medical device vulnerabilities affecting treatment delivery, and supply chain compromises affecting interconnected infrastructure. Your HIPAA assessment must account for these evolving cyber threats, not just traditional data protection gaps.
Integration means aligning your assessment scope with cyber risk priorities:
- Threat modeling identifies which cyber attacks create greatest business impact
- Vulnerability scanning surfaces exploitable weaknesses in clinical and administrative systems
- Risk prioritization reflects both compliance requirements and operational resilience needs
- Remediation roadmaps address high-risk findings first, regardless of whether they're technically a HIPAA requirement
- Monitoring strategies detect active cyber threats and unauthorized access attempts
Legacy medical devices and interconnected IT systems create cascading risk. A vulnerability in your EHR system could expose patient records while simultaneously enabling ransomware deployment across your network. Your assessment must trace these interdependencies rather than evaluating systems in isolation.
Standalone HIPAA assessments miss cyber threats that don't directly target ePHI but create conditions enabling breaches.
Your enterprise risk management framework should position cybersecurity as foundational to HIPAA compliance, not separate from it. This means your CISO reports to leadership on both regulatory compliance and cyber resilience simultaneously. Budget discussions become clearer: you're not just meeting compliance checkboxes—you're protecting patient safety and operational continuity.
Integration also improves governance. When your risk assessment informs your security roadmap, and your security roadmap drives resource allocation, stakeholders see clear logic connecting compliance requirements to cybersecurity investments. This eliminates the perception that security is overhead and repositions it as strategic business protection.
Practically, this means conducting risk assessments that identify threats, vulnerabilities, and business impacts using consistent scoring criteria across both HIPAA and cyber domains. A ransomware vulnerability gets rated high because it threatens operations and data confidentiality. An access control gap gets prioritized based on actual compromise likelihood given your threat environment.
Your assessment findings should drive decisions about which systems need enhanced monitoring, which third-party vendors require additional security reviews, and which infrastructure upgrades justify budget requests. This direct line from assessment to action makes the assessment valuable beyond compliance.
Pro tip: Present your integrated risk assessment results to leadership using threat-impact language rather than compliance language—phrase findings as "ransomware vulnerability affecting billing and clinical operations" rather than "technical safeguard gap"—this shifts perception from checkbox compliance to strategic protection.
Common Pitfalls and How to Avoid Them
Most healthcare organizations conduct risk assessments because HIPAA requires them. Few conduct them effectively. The difference lies in recognizing common mistakes early and building processes to prevent them. For CISOs, understanding these pitfalls keeps your assessment from becoming a compliance checkbox that misses actual threats.
The first major mistake is treating the assessment as a one-time event. Organizations complete their assessment, document it, file it away, and ignore it for three years. Meanwhile, your threat landscape changed, systems were added, vendors were brought on, and vulnerabilities evolved. A stale assessment provides false confidence while masking emerging risks.
Second, many assessments fail because the organization doesn't actually own its own asset inventory. You can't assess risk to systems you haven't cataloged. Incomplete asset inventories prevent you from identifying all devices handling ePHI, all third-party integrations, and all potential attack surfaces. Without knowing what you have, your assessment covers only what you remember.
Third, organizations often document findings and then stop. They complete the assessment, identify high-risk gaps, and never implement corrections. The assessment becomes evidence of negligence rather than due diligence—regulators will ask why you identified risks but failed to address them.
Common assessment mistakes:
- Treating risk assessment as compliance documentation rather than operational intelligence
- Failing to involve clinical staff, IT operations, and security together in the process
- Underestimating people-related risks while over-focusing on technology vulnerabilities
- Ignoring threat-and-vulnerability combinations that create realistic attack paths
- Applying generic assessment templates without customizing for your environment
- Neglecting third-party and supply chain risks from vendors and business associates
- Rating risks without considering actual likelihood given your specific threat environment
Comprehensive assessments require evaluating all components, including administrative practices, physical security, technical safeguards, workforce training, and vendor management. Organizations often focus narrowly on technical vulnerabilities while missing administrative gaps like inadequate access controls or insufficient security awareness training.
The deadliest gap isn't always technical—it's the gap between what your policy requires and what employees actually do daily.
To avoid these pitfalls, establish a repeating assessment schedule tied to your security roadmap. Conduct full assessments annually and focused assessments after major changes like new system implementations or vendor additions. Document everything—methodology, scoring criteria, findings, and remediation decisions.
Involve stakeholders beyond security. Clinical leadership, IT operations, compliance, and procurement all bring essential perspective. Their input identifies risks you'd miss alone, and their buy-in accelerates remediation. A siloed security team produces siloed assessments that leadership ignores.
Most importantly, close the loop. Remediate findings proportional to risk. Track completion dates. Provide leadership updates on progress. When your next assessment shows improvement, it validates the entire process and justifies continued investment.
Pro tip: Document your corrective action tracking in a format leadership reviews quarterly—showing Risk Rating, Remediation Status, and Completion Timeline—this creates accountability while demonstrating continuous improvement to regulators.
Strengthen Your HIPAA Risk Assessments with Strategic Cybersecurity Expertise
Navigating the complexities of healthcare risk assessments and HIPAA compliance requires more than just checklist fulfillment. CISOs face the challenge of translating vulnerability data into actionable business impact insights while ensuring comprehensive coverage of administrative, physical, and technical safeguards. Key pain points include managing evolving cyber threats, coordinating cross-functional teams, and maintaining up-to-date, documented risk methodologies that satisfy regulatory scrutiny.
Heights Consulting Group specializes in transforming these challenges into strategic advantages. Our cybersecurity consulting services integrate risk management frameworks with real-world protection strategies tailored for healthcare and other highly regulated industries. By partnering with us, you gain expert guidance to develop rigorous, repeatable risk assessments that align with HIPAA mandates and empower confident decision-making across your enterprise.

Take control of your compliance and cybersecurity landscape today. Visit Heights Consulting Group to discover how our combined advisory and technical services can help you create resilient risk assessments that protect patient safety, support regulatory objectives, and optimize your security investment roadmap. Do not let outdated or incomplete assessments leave you vulnerable—reach out now and secure your organization’s future.
Frequently Asked Questions
What is the purpose of risk assessments in healthcare?
Risk assessments in healthcare aim to identify vulnerabilities related to electronic protected health information (ePHI), clinical operations, and infrastructure, ensuring that patient data is protected and regulatory requirements are met.
How do risk assessments impact HIPAA compliance for healthcare organizations?
Risk assessments are a critical component of HIPAA compliance, as they help identify risks to ePHI and ensure that appropriate safeguards are in place, protecting healthcare organizations from potential penalties and breaches.
What are the key differences between qualitative and quantitative risk assessments?
Qualitative assessments rely on expert judgment and descriptive terms to categorize risks, while quantitative assessments use numerical values to assess risk probability and impact, providing more objective data for decision-making.
How often should healthcare organizations conduct risk assessments?
Healthcare organizations should conduct comprehensive risk assessments at least annually and perform focused assessments whenever there are significant changes, such as new systems or vendors, to ensure continuous compliance and risk management.