Nearly 60 percent of American healthcare organizations report experiencing a security incident in the past year. With sensitive patient data and strict regulatory demands at stake, risk assessment is not just a technical necessity—it is a business imperative for Chief Information Security Officers and compliance officers. This overview explains how structured risk assessment protects electronic health information and supports organizations in meeting both HIPAA and NIST standards while strengthening overall security posture.
Table of Contents
- Defining Risk Assessment In Healthcare Security
- Key Types And Methodologies Used
- How Risk Assessment Supports HIPAA And NIST
- Integrating Risk Assessment With Business Goals
- Common Pitfalls And Overlooked Risks
Key Takeaways
| Point | Details |
|---|---|
| Importance of Risk Assessment | A systematic risk assessment is essential for identifying and mitigating threats to healthcare security. Regular assessments ensure comprehensive cybersecurity strategy updates. |
| Methodologies Used | Employ both qualitative and quantitative methodologies to evaluate cybersecurity risks effectively. This balanced approach enhances understanding and prioritization of vulnerabilities. |
| Compliance with Regulations | Align risk assessment practices with HIPAA and NIST requirements to ensure robust compliance and protection of sensitive health information. Annual assessments are critical for maintaining this alignment. |
| Addressing Overlooked Risks | Focus on emerging cybersecurity challenges, insider threats, and legacy systems to prevent significant vulnerabilities. Regular training and assessments can mitigate these risks effectively. |
Defining Risk Assessment in Healthcare Security
Risk assessment in healthcare security represents a systematic process for identifying, evaluating, and mitigating potential threats to electronic health information systems. Healthcare organizations can systematically assess security vulnerabilities by comprehensively analyzing their technological infrastructure, data management practices, and potential cybersecurity risks.
The core objective of risk assessment involves creating a structured approach to understanding potential security challenges. Healthcare organizations must develop a methodical framework that examines potential vulnerabilities across multiple dimensions - including technological systems, human factors, administrative protocols, and potential external threat vectors. This comprehensive evaluation enables security professionals to prioritize risks based on their potential impact and likelihood of occurrence, ultimately creating targeted mitigation strategies.
A robust healthcare security risk assessment typically involves several critical components: identifying potential security vulnerabilities, analyzing existing protection mechanisms, evaluating potential consequences of potential breaches, and developing strategic response plans. Risk assessment helps organizations systematically evaluate potential hazards and determine appropriate actions to reduce potential harm by creating a proactive and dynamic approach to cybersecurity management.
Pro Tip: Conduct risk assessments annually and after any significant technological infrastructure changes to maintain a current and comprehensive understanding of your organization's cybersecurity landscape.
Key Types and Methodologies Used
Healthcare cybersecurity risk assessment encompasses multiple sophisticated methodological approaches designed to comprehensively evaluate technological vulnerabilities. Cybersecurity risk management techniques integrate both qualitative and quantitative methodological frameworks to systematically identify, analyze, and prioritize potential security threats across healthcare technology infrastructures.
The primary risk assessment methodologies can be categorized into two fundamental approaches: qualitative and quantitative techniques. Qualitative methodologies rely on expert judgment, scenario analysis, and structured interviews to assess potential risks based on professional experience and contextual understanding. These approaches typically involve creating risk matrices, developing threat scenarios, and evaluating potential impacts through collaborative expert assessments. Quantitative methodologies, conversely, utilize statistical models, numerical data, and probabilistic calculations to assign precise risk values and potential financial impacts associated with specific cybersecurity vulnerabilities.
Here is a comparison of qualitative and quantitative risk assessment methodologies in healthcare cybersecurity:
| Aspect | Qualitative Approach | Quantitative Approach |
|---|---|---|
| Decision Basis | Expert opinion and scenarios | Statistical models and data |
| Assessment Output | Relative risk ratings | Numeric risk values |
| Typical Tools Used | Risk matrices, interviews | Probability analysis, financial metrics |
| Key Advantage | Fast, good for unknown threats | Precise, enables financial forecasting |
| Main Limitation | May lack objectivity | Requires substantial data and modeling |
Healthcare organizations implement risk assessment processes through strategic stages that include comprehensive risk identification, detailed impact analysis, targeted mitigation strategy development, and ongoing control review. These stages enable healthcare technology leaders to create dynamic, adaptive security frameworks that can rapidly respond to emerging technological threats and changing regulatory requirements. The methodological approach involves systematically mapping potential vulnerabilities, assessing their likelihood and potential consequences, and developing targeted interventions that protect sensitive patient information and critical healthcare technology infrastructure.

Pro Tip: Develop a standardized risk assessment template that incorporates both qualitative and quantitative evaluation methods to ensure a comprehensive and nuanced understanding of your organization's cybersecurity landscape.
How Risk Assessment Supports HIPAA and NIST
Risk assessment plays a critical role in ensuring healthcare organizations maintain robust cybersecurity compliance with both HIPAA regulations and NIST framework requirements. The NIST Cybersecurity Framework provides comprehensive guidance for identifying, assessing, and prioritizing cybersecurity risks that directly align with healthcare organizations' operational needs and regulatory mandates.
HIPAA's Security Rule mandates specific risk assessment protocols that require healthcare organizations to systematically evaluate and protect electronic protected health information (ePHI). These requirements compel organizations to implement comprehensive security controls across technical, physical, and administrative domains. The assessment process involves identifying potential vulnerabilities, analyzing their potential impact, and developing targeted mitigation strategies that address specific risks to patient data confidentiality, integrity, and availability.
Healthcare compliance demands a structured approach to risk assessment that integrates both HIPAA requirements and NIST framework recommendations to create a holistic cybersecurity strategy. This integrated approach enables healthcare organizations to develop dynamic security frameworks that can adapt to emerging technological threats while maintaining strict regulatory compliance. By systematically mapping potential vulnerabilities, assessing their likelihood and potential consequences, and implementing targeted interventions, healthcare technology leaders can create robust protection mechanisms that safeguard sensitive patient information.
Pro Tip: Conduct annual comprehensive risk assessments that explicitly map your security controls to both HIPAA requirements and NIST Cybersecurity Framework recommendations to ensure comprehensive compliance and protection.
Integrating Risk Assessment With Business Goals
Strategic risk assessment transforms cybersecurity from a technical requirement into a critical business enabler for healthcare organizations. Cybersecurity must be deeply embedded into organizational business strategies to safeguard digital assets and maintain critical operational trust by aligning security initiatives with core organizational objectives and performance metrics.
Effective integration requires a holistic approach that transcends traditional security boundaries. Healthcare leaders must develop risk assessment frameworks that not only protect technological infrastructure but also support broader business continuity and strategic goals. This means understanding how potential cybersecurity vulnerabilities can impact financial performance, operational efficiency, patient trust, and regulatory compliance. By translating technical risks into business language, organizations can create more compelling risk narratives that resonate with executive leadership and drive strategic investment in cybersecurity capabilities.
Successful risk assessment integration demands aligning security policies with precise organizational objectives while maintaining operational flexibility. The process involves creating dynamic risk models that can rapidly adapt to changing technological landscapes, emerging threats, and evolving business strategies. Healthcare technology leaders must develop comprehensive risk assessment approaches that provide granular insights into potential vulnerabilities while simultaneously demonstrating clear connections between cybersecurity investments and tangible business outcomes.
Pro Tip: Develop a cross-functional risk assessment team that includes representatives from IT, compliance, operations, and executive leadership to ensure a comprehensive and strategically aligned approach to cybersecurity risk management.
Common Pitfalls and Overlooked Risks
Healthcare cybersecurity risk assessment requires vigilant identification of potential vulnerabilities that can often escape traditional security frameworks. Organizations frequently underestimate insider threats and fail to comprehensively address emerging cybersecurity challenges such as sophisticated ransomware attacks and complex human-factor security risks.
One of the most significant overlooked risks involves legacy technological infrastructure and inadequate employee cybersecurity training. Healthcare organizations frequently maintain outdated systems with inherent security vulnerabilities, creating potential entry points for malicious actors. These technological gaps are compounded by insufficient personnel training, which leaves organizations exposed to social engineering tactics, phishing attempts, and inadvertent data disclosure risks that can compromise entire technological ecosystems.
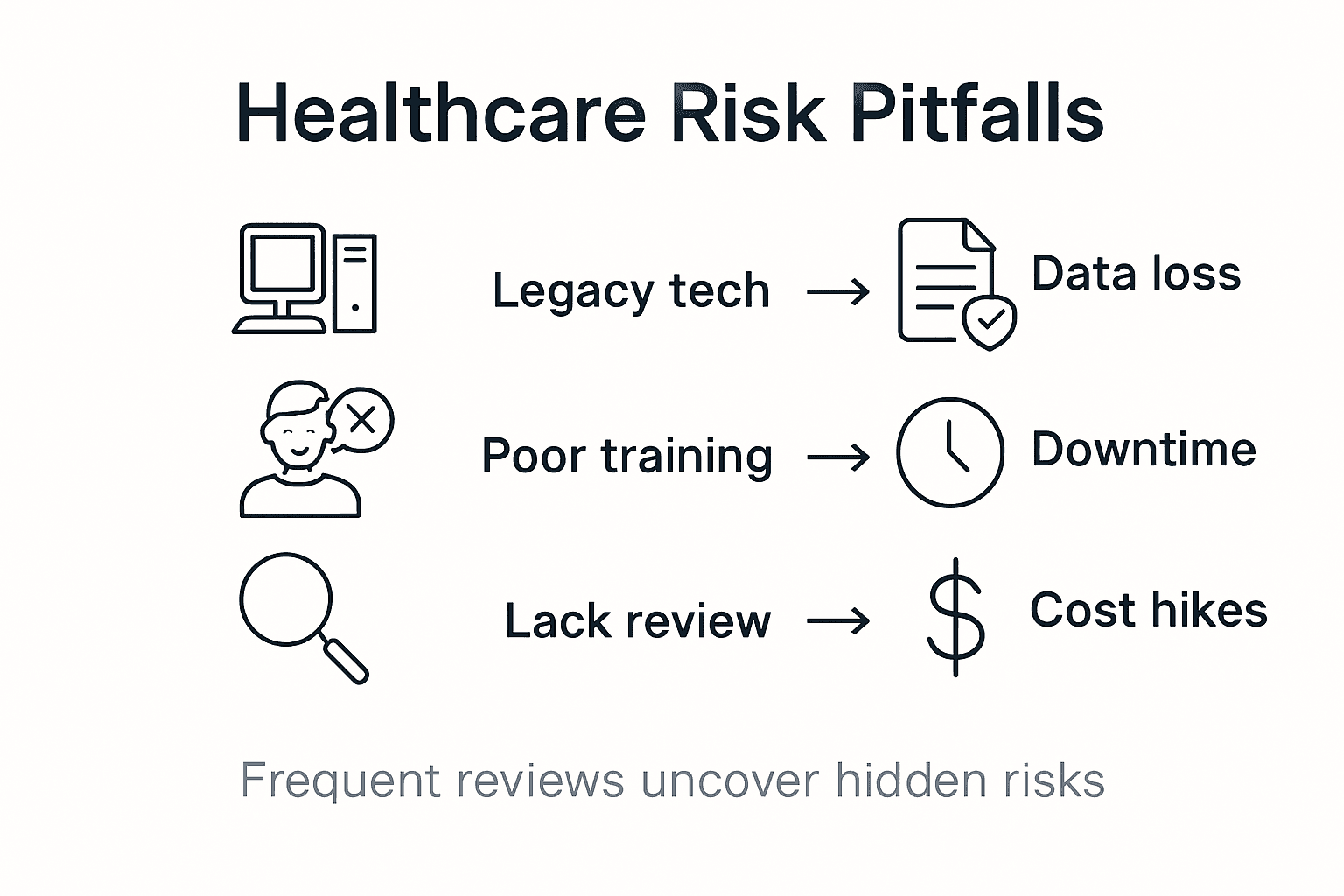
Healthcare cybersecurity faces complex challenges including systemic vulnerabilities in IT infrastructure and persistent gaps in skilled cybersecurity personnel that create substantial organizational risk. The most critical overlooked risks include third-party vendor security gaps, inadequate patient privacy protection mechanisms, and failure to develop dynamic, adaptive risk assessment strategies that can quickly respond to evolving technological threats. Organizations must recognize that cybersecurity is not a static condition but a continuous process requiring constant vigilance, reassessment, and proactive strategic planning.
This table summarizes common overlooked risks versus established vulnerabilities in healthcare security:
| Risk Type | Description | Potential Business Impact |
|---|---|---|
| Legacy Systems | Outdated tech with known flaws | Increased breach likelihood |
| Insider Threats | Internal staff misusing access | Data leaks, compliance loss |
| Third-Party Vendor Gaps | Weaknesses in partners’ security practices | Supply chain disruptions |
| Insufficient Training | Employees unprepared for cyber threats | Higher phishing success rates |
| Static Risk Assessments | Failing to update practices regularly | Missed new vulnerabilities |
Pro Tip: Implement a quarterly comprehensive risk assessment review that explicitly examines both technological vulnerabilities and human factor risks to create a holistic and dynamic cybersecurity strategy.
Strengthen Your Healthcare Cybersecurity With Expert Risk Assessment
Healthcare organizations face daunting challenges identifying and effectively managing cybersecurity risks that threaten sensitive patient data and operational integrity. This article highlights the critical role of comprehensive risk assessment methodologies aligned with frameworks like HIPAA and NIST to prioritize vulnerabilities and protect against evolving threats such as insider risks and legacy system flaws. If you are seeking to transform cybersecurity risk assessment from a static technical task into a dynamic business advantage that supports compliance and strategic goals, expert guidance is essential.

Heights Consulting Group specializes in partnering with healthcare leaders to develop integrated cybersecurity strategies that align risk management with organizational objectives. Our consulting services include risk assessment frameworks, compliance solutions, and technical implementations designed to proactively identify vulnerabilities and adapt to emerging threats. Don’t wait for your next breach or compliance challenge. Visit Heights Consulting Group to explore how our team can support your cybersecurity transformation today. Learn more about our strategic advisory services and start turning cybersecurity risks into competitive strengths now.
Frequently Asked Questions
What is the purpose of conducting a risk assessment in healthcare cybersecurity?
The purpose of conducting a risk assessment in healthcare cybersecurity is to systematically identify, evaluate, and mitigate potential threats to electronic health information systems, ensuring the confidentiality, integrity, and availability of patient data.
What methodologies are used in healthcare cybersecurity risk assessments?
Healthcare cybersecurity risk assessments typically use two primary methodologies: qualitative and quantitative approaches. Qualitative methodologies rely on expert judgment and scenario analysis, while quantitative approaches use statistical models and numerical data to assess risks.
How does risk assessment support compliance with HIPAA and NIST frameworks?
Risk assessment supports compliance with HIPAA and NIST frameworks by requiring healthcare organizations to evaluate and protect electronic protected health information (ePHI), identifying vulnerabilities and developing mitigation strategies that align with regulatory requirements.
What are some common overlooked risks in healthcare cybersecurity?
Common overlooked risks in healthcare cybersecurity include legacy systems with vulnerabilities, insider threats, third-party vendor security gaps, and insufficient employee training, which can all expose organizations to potential cyberattacks.