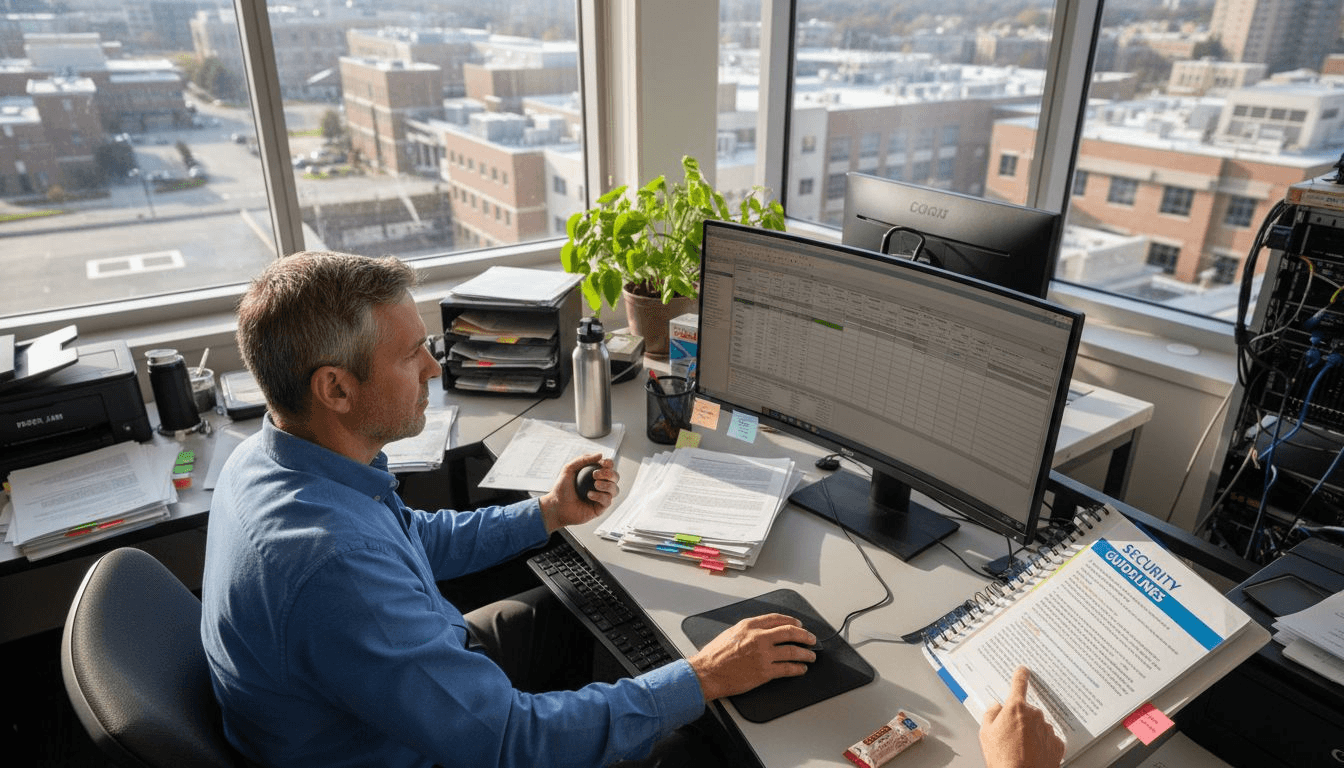
Facing relentless phishing campaigns and mounting HIPAA requirements, CISOs in American healthcare organizations know the stakes are high. Without well-defined risk assessment objectives and scope, security teams risk wasted effort and missed vulnerabilities. This guide highlights actionable steps for enhancing risk assessment workflows, combining practical advice with compliance-driven strategies vetted by Federal guidance, HHS, and CISA resources to help you sharpen your defenses and strengthen regulatory readiness against emerging cyber threats.
Table of Contents
- Step 1: Establish Risk Assessment Objectives And Scope
- Step 2: Gather Relevant Data And Identify Critical Assets
- Step 3: Analyze Threats And Vulnerabilities Impacting Compliance
- Step 4: Prioritize Remediation Actions For Risk Mitigation
- Step 5: Validate Workflow Effectiveness Through Testing
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Define clear risk assessment objectives | Establishing specific goals aligns with your organization's mission and helps focus the assessment on critical vulnerabilities and compliance needs. |
| 2. Create a comprehensive asset inventory | Catalog all systems handling e-PHI to identify critical assets, ensuring no vulnerabilities are overlooked during the risk assessment process. |
| 3. Analyze threats against compliance standards | Understand specific vulnerabilities linked to compliance failures, allowing for targeted remediation that protects patient data and minimizes regulatory risks. |
| 4. Prioritize remediation based on risk | Rank vulnerabilities by potential impact and likelihood to optimize resource allocation and address the most pressing security issues first. |
| 5. Regularly validate testing of security controls | Conduct ongoing assessments to ensure that remediation efforts are effective and to identify any emerging threats before they lead to breaches. |
Step 1: Establish risk assessment objectives and scope
Before you dive into identifying vulnerabilities or measuring security gaps, you need a clear picture of what you're actually trying to accomplish. Defining your risk assessment objectives and scope sets the foundation for everything that follows, preventing wasted effort and ensuring your team focuses on what matters most to your organization.
Start by aligning your risk assessment objectives with your healthcare organization's mission and compliance requirements. Your objectives should answer specific questions: Are you assessing risks to meet HIPAA requirements? Do you need to evaluate emerging threats in your clinical environment? Are you preparing for an audit or accreditation review? Write these down explicitly.
Clear objectives prevent scope creep and ensure your risk assessment directly supports your organization's security posture and compliance standing.
Define your assessment scope next. This means determining which systems, departments, and processes you'll evaluate. In healthcare, you might scope risk assessments around:
- Electronic health record (EHR) systems and database infrastructure
- Clinical devices connected to your network
- Third-party vendor integrations handling patient data
- Physical security controls at your facilities
- Staff access and authentication mechanisms
Consult relevant frameworks to ground your approach. The CISO Handbook provides foundational guidance on establishing risk assessment objectives aligned with organizational mission and compliance requirements. Document your scope boundaries clearly so stakeholders understand what's included and what isn't.
Involve your compliance team early. They'll help you connect your risk assessment objectives to regulatory requirements like HIPAA Security Rule standards and any state-specific health data protection laws. When compliance priorities shape your objectives, you're building efficiency into the process rather than retrofitting it later.
Consider using established healthcare-focused resources. A HIPAA security risk assessment guide can help you structure your objectives around specific security requirements your organization must address.
Document everything in writing. Your objectives and scope statement becomes a reference document that keeps your team aligned and provides accountability for what the assessment covers. This written clarity also helps when communicating results to your board or executive leadership later.
Pro tip: Set a specific timeline and resource budget alongside your objectives—define how long the assessment will take and which team members will participate, so your scope remains realistic rather than becoming an open-ended security audit that delays critical findings.
Step 2: Gather relevant data and identify critical assets
Now that you've defined what you're assessing and why, it's time to get serious about understanding what you actually have running in your healthcare environment. This step transforms vague security concerns into concrete, inventory-based information that will guide your entire risk assessment process.
Start by cataloging all systems and assets that handle electronic protected health information (e-PHI). This includes obvious targets like your EHR platform, but also includes less obvious ones like backup systems, email servers, patient portals, and medical devices connected to your network. HHS guidance on risk analysis methodologies emphasizes gathering comprehensive data on information systems and assets handling e-PHI.
Create a complete asset inventory by documenting:
- System names, versions, and operating systems
- Data classification (what type of PHI does it process or store)
- Physical and network locations
- System owners and departments
- Interfaces with external systems or vendors
- Current security controls already in place
Use vulnerability scanning and all-hazards risk assessment tools to systematically gather data. CISA's healthcare cybersecurity resources provide toolkits and practices for identifying critical assets and collecting comprehensive cybersecurity data across your environment.
Your asset inventory becomes the foundation for everything else—without it, you're assessing risks in the dark.
Prioritize your critical assets based on their impact to patient care and regulatory significance. An EHR system down for four hours creates more disruption than a departmental printer offline. Document this prioritization explicitly so your team understands which assets demand the most scrutiny during risk evaluation.
Interview system owners and department heads directly. They'll tell you about undocumented integrations, legacy systems running unsupported software, and workarounds that bypass official processes. These conversations often surface the biggest security gaps.
Document data flows between systems. How does patient information move from your imaging system to the EHR? Where does it get backed up? Who has access at each step? Mapping these flows reveals potential vulnerabilities and helps you understand your actual security perimeter.

Pro tip: Create a visual network diagram showing all systems and data flows—it's invaluable for communicating your asset landscape to executives and makes it much easier to spot missing connections when you review it with department leaders.
Step 3: Analyze threats and vulnerabilities impacting compliance
You've inventoried your assets and understand your environment. Now comes the critical analysis phase where you connect specific vulnerabilities to compliance failures. This step separates a theoretical risk assessment from one that actually protects patient data and your organization's reputation.
Start by identifying the threat actors and attack vectors most relevant to healthcare. Ransomware operators targeting hospitals, disgruntled insiders with system access, and opportunistic external attackers using phishing all represent real threats. CISA's analysis of healthcare threat vectors and vulnerabilities demonstrates how common attacks like phishing, credential misuse, and misconfigurations directly impact regulatory compliance.
Map vulnerabilities against specific compliance requirements. For example, if HIPAA requires encryption of data in transit and you discover unencrypted patient records being transmitted over your network, that's a direct compliance violation. Document which control failures create compliance gaps:
- Missing or weak access controls violating minimum necessary standards
- Unencrypted e-PHI in storage or transmission
- Inadequate audit logging preventing breach detection
- Unsupported or unpatched systems creating exploitation pathways
- Third-party vendor access without proper contractual safeguards
Prioritize vulnerabilities by their impact on patient safety and compliance standing. A vulnerability affecting your EHR's audit trail is more critical than a misconfigured printer. A compromised physician credential could expose thousands of patient records.
Vulnerabilities matter only when they create compliance exposure. Connect every finding back to the specific control it undermines.
Conduct scenario analysis for your highest-risk vulnerabilities. If an attacker exploits credential misuse in your clinical system, what e-PHI becomes accessible? How long before detection? What's your containment capability? These scenarios reveal the real compliance consequences of inaction.
Involve your legal and compliance teams in this analysis. They understand which violations create regulatory penalties, notification requirements, and reputational damage. Their perspective shapes which vulnerabilities demand immediate remediation versus staged improvements.
Document your findings comprehensively. Your threat and vulnerability analysis becomes the evidence base for risk mitigation decisions and executive reporting. Clear documentation also demonstrates due diligence to regulators.
Pro tip: Use a risk matrix plotting likelihood versus impact to visually communicate which vulnerabilities pose the greatest compliance threat—executives grasp this format immediately and understand why certain remediation efforts take priority.
Step 4: Prioritize remediation actions for risk mitigation
You've identified vulnerabilities and understand their compliance impact. Now you face the reality of every CISO's world: limited budgets, competing priorities, and a long list of security improvements. Prioritization separates smart risk management from reactive firefighting.
Start by ranking vulnerabilities by risk level. This means considering both the likelihood an attacker will exploit each weakness and the impact if they succeed. A critical vulnerability affecting your EHR with active exploitation in the wild demands immediate attention. A minor issue in a non-critical system can wait. HHS guidance on risk assessment and remediation prioritization emphasizes selecting appropriate safeguards and prioritizing efforts according to risk severity to allocate resources effectively.
Structure your remediation roadmap using these criteria:
- Compliance mandates (what HIPAA, state law, or accreditation requires immediately)
- Active exploitation risk (vulnerabilities being actively attacked in healthcare)
- Patient data exposure (how many records could be compromised)
- Operational impact (how severely patient care would be affected if exploited)
- Remediation feasibility (cost and effort to fix)
Align your priorities with organizational risk tolerance and strategic goals. CMS's Risk Management Framework approach advises organizations to connect remediation priorities with compliance mandates and cybersecurity objectives to maximize resource utilization.
Not all risks are created equal. A HIPAA violation affecting one patient's data demands different treatment than a theoretical attack that requires insider knowledge to execute.
Engage your executive leadership in prioritization decisions. They understand budget constraints, business impact, and strategic direction in ways your technical team may not. A vulnerability affecting patient safety systems takes different priority than one affecting administrative functions.
Create a phased remediation plan with realistic timelines. Quick wins in the first 30 days build momentum. Medium-term improvements over 90 days show progress. Strategic long-term projects over six to twelve months address foundational security improvements that require significant change.
Communicate your prioritization logic to stakeholders. When department heads understand why their system remediation is scheduled for quarter three rather than immediately, they become partners rather than obstacles.
Here's a quick comparison of risk priority criteria to guide effective remediation planning:
| Priority Factor | Description | Example Application |
|---|---|---|
| Compliance Mandates | Legal or regulatory requirements driving urgency | HIPAA Security Rule encryption deadline |
| Active Exploitation | Current threats targeting known vulnerabilities | Ongoing ransomware attacks in healthcare |
| Patient Data Exposure | Number of records or systems impacted | EHR breach affecting thousands of records |
| Operational Impact | Disruption to delivery of care if exploited | Downtime in prescription system halts treatments |
| Remediation Feasibility | Cost, resources, and time to address | Quick patch deployable in 48 hours |
Pro tip: Create a visual remediation roadmap showing high, medium, and low priority items with target completion dates—executives and board members grasp this timeline immediately and can defend your security budget during resource allocation meetings.
Step 5: Validate workflow effectiveness through testing
You've built your risk assessment process and begun remediation. But here's the uncomfortable truth: workflows that look good on paper often fail in practice. Testing reveals gaps, false assumptions, and areas where your process breaks down before regulators find them.
Start by conducting regular security assessments to validate that your risk identification and remediation efforts actually work. This means testing whether vulnerabilities you claimed to fix are actually remediated, and whether your risk assessment process catches new threats that emerge. CMS guidance on risk assessment validation and testing emphasizes continuous testing and monitoring to ensure workflows remain effective in identifying and mitigating cybersecurity risks.
Design your testing program around these activities:
- Penetration testing targeting your highest-risk systems to validate control effectiveness
- Vulnerability rescans after remediation to confirm vulnerabilities were actually eliminated
- Control testing to verify that security controls operate as designed
- Tabletop exercises simulating breach scenarios to test your incident response readiness
- Compliance assessments confirming your controls meet HIPAA Security Rule requirements
Involve your technical teams in testing execution. They understand your systems intimately and can identify when test results don't align with expected behavior. Their skepticism often uncovers workflow weaknesses that management overlooks.
A risk assessment workflow that hasn't been tested is just an exercise in documentation. Testing transforms it into validated security assurance.
Schedule testing on a consistent cadence. Annual penetration tests catch major issues but miss emerging vulnerabilities. Quarterly vulnerability scans keep you ahead of new threats. Monthly control spot-checks ensure your remediation efforts stay on track.
Document test results meticulously. When testing reveals control gaps, you've discovered them proactively rather than having regulators or breach investigators find them. This documentation demonstrates due diligence to your board and compliance teams.
Adjust your workflow based on what testing reveals. If your risk assessment process missed a significant vulnerability, how will you improve detection going forward? If remediation took longer than planned, what resource constraints need addressing?
The following table summarizes recommended validation methods and their primary focus in healthcare security workflows:
| Testing Activity | Primary Focus | Typical Frequency |
|---|---|---|
| Penetration Testing | Control effectiveness | Annually or after major changes |
| Vulnerability Rescans | Verification of remediation | Quarterly or after fixes |
| Control Testing | Ongoing operational assurance | Monthly spot checks |
| Tabletop Exercises | Incident response readiness | Twice per year |
| Compliance Assessments | Regulatory control verification | Annually or before audits |
Pro tip: Schedule testing results review meetings with your remediation teams immediately after completion—while findings are fresh, your team can identify root causes and implement workflow improvements before the next assessment cycle.
Accelerate Your Healthcare Risk Assessment with Expert Cybersecurity Partnership
Healthcare CISOs face the constant challenge of optimizing risk assessment workflows while balancing limited resources and complex compliance mandates such as HIPAA. This article highlights key pain points like defining clear objectives, identifying critical assets, analyzing compliance-impacting vulnerabilities, and prioritizing remediation under strict operational constraints. Protecting patient data while ensuring business continuity demands strategic clarity and proven execution.
At Heights Consulting Group, we translate these critical concepts into actionable solutions. Our comprehensive cybersecurity services integrate seamlessly with healthcare organizations’ mission and compliance goals. Whether you need expert guidance on risk management frameworks, advanced endpoint detection, or tailored compliance strategies aligned with HIPAA and other regulatory standards, our team helps you move beyond documentation to validated security assurance. Discover how our strategic approach converts your risk assessment into a competitive advantage.
Ready to transform your risk assessment process into a resilient, compliance-driven foundation for healthcare security?
Managed Cybersecurity Solutions

Take the next step with Heights Consulting Group today. Visit our website to learn how our expert advisory and technical services empower healthcare CISOs to navigate risk and compliance confidently. Don't wait until vulnerabilities threaten patient trust and regulatory standing. Connect now to secure your healthcare organization's future.
Frequently Asked Questions
What are the key steps to optimize a risk assessment workflow for Healthcare CISOs?
To optimize a risk assessment workflow, start by establishing clear objectives and scope, gathering relevant data on critical assets, analyzing threats and vulnerabilities, prioritizing remediation actions, and validating your processes through regular testing. Implement these steps systematically to enhance your organization's cybersecurity posture and ensure compliance.
How can I determine the scope of my risk assessment in a healthcare environment?
Define the scope by identifying which systems, departments, and processes you will evaluate. Focus on critical areas like Electronic Health Record (EHR) systems and third-party vendor interactions to set boundaries that ensure comprehensive risk management.
What should I include when documenting my risk assessment objectives?
Document objectives that align with your healthcare organization’s mission and compliance requirements. Include specific goals such as meeting HIPAA standards or preparing for an upcoming audit to provide clarity and accountability for your assessment team.
How do I prioritize vulnerabilities discovered during a risk assessment?
Prioritize vulnerabilities based on their risk level, considering factors like compliance mandates, potential for active exploitation, and impact on patient data. Create a tiered remediation plan, addressing the most critical vulnerabilities first, ideally within the next 30 days.
What methods can I use to validate the effectiveness of my risk assessment process?
Conduct regular security assessments, including penetration testing and control testing, to validate that your processes are effective. Schedule these assessments quarterly to ensure ongoing improvement and to address any newly identified vulnerabilities promptly.
How can I engage my executive leadership in the risk assessment process?
Involve executive leadership by clearly communicating the prioritization logic behind your remediation actions. Present a visual roadmap of vulnerabilities and remediation timelines, so they can understand the implications for budgeting and strategic direction.