TL;DR:
- Regulatory compliance is an ongoing strategic priority driven by enterprise reputation and executive accountability.
- Successful organizations layer multiple frameworks like COBIT, NIST, and ITIL based on their risk and regulatory needs.
- Managing sector-specific mandates, third-party risks, and AI regulations is critical to maintaining audit readiness and avoiding violations.
Regulatory compliance is not a single project with a finish line. Many IT leaders still operate under the assumption that selecting one governance framework and completing an annual audit constitutes a mature compliance program. That assumption is costly. In regulated industries, compliance now functions as a core driver of enterprise trust, market access, and executive accountability. The frameworks are multiplying, the mandates are overlapping, and the penalties for falling short are steeper than ever. This guide cuts through the noise by showing how to strategically layer frameworks, manage sector-specific mandates, and build a compliance posture that holds up in 2026 and beyond.
Table of Contents
- Why regulatory compliance is mission-critical for IT leaders
- Comparing top compliance frameworks: COBIT, ITIL, NIST, and ISO/IEC 38500
- Navigating sector-specific compliance: HIPAA, DORA, GLBA, and the rise of AI regulation
- Edge cases, pitfalls, and future threats: What most compliance guides miss
- Beyond the checklist: Why compliance maturity depends on executive mindset
- Advance your compliance strategy with expert support
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Layer frameworks | Stack multiple compliance frameworks for comprehensive governance and sector coverage. |
| Anticipate new risks | Third-party risks, human error, and regulatory conflict are major compliance threats in 2026. |
| Compliance is cultural | Sustained compliance arises from executive mindset and organization-wide accountability. |
| Leverage expert support | Partnering with compliance experts accelerates readiness and reduces risk exposure. |
Why regulatory compliance is mission-critical for IT leaders
The stakes around regulatory compliance have shifted dramatically over the past decade. What was once a back-office function managed by legal and audit teams is now a board-level priority with direct implications for revenue, reputation, and executive liability. C-level leaders who treat compliance as a periodic checkbox exercise are exposing their organizations to risks that go well beyond fines.
Consider the financial exposure alone. Regulatory penalties in healthcare, finance, and critical infrastructure can reach tens of millions of dollars per violation cycle. Beyond the financial hit, noncompliance can trigger loss of operating licenses, disqualification from government contracts, and erosion of customer trust that takes years to rebuild. In some jurisdictions, executives now face personal accountability, including criminal liability, for compliance failures that occur on their watch.
The industries most affected share a common characteristic: they operate under multiplying regulatory requirements and increasingly frequent audits. A financial institution might face simultaneous reviews under GLBA, DORA, and state-level cybersecurity rules. A healthcare system may navigate HIPAA, GDPR for international patients, and new AI governance requirements, all at once. The volume and complexity of these requirements demand a fundamentally different approach.
"Compliance is no longer a one-off project but an ongoing strategic mandate, especially in regulated industries."
What separates high-performing organizations from those that struggle is culture. Executives who champion continuous compliance, rather than reactive remediation, build organizations that are more resilient, more audit-ready, and more trusted by partners and regulators alike. This means embedding security governance for compliance into business planning cycles, not just IT project timelines.
Key drivers making compliance mission-critical today include:
- Regulatory velocity: New rules and updates are being issued faster than most organizations can absorb them.
- Executive accountability: Personal liability for CISOs and CIOs is now codified in several regulatory frameworks.
- Third-party exposure: Your compliance posture is only as strong as your weakest vendor relationship.
- Audit frequency: Regulators are moving toward continuous monitoring rather than annual point-in-time reviews.
- Competitive differentiation: Organizations with demonstrable compliance maturity win contracts and partnerships that others cannot access.
With the stage set, it is crucial to understand the frameworks underpinning modern compliance strategies.
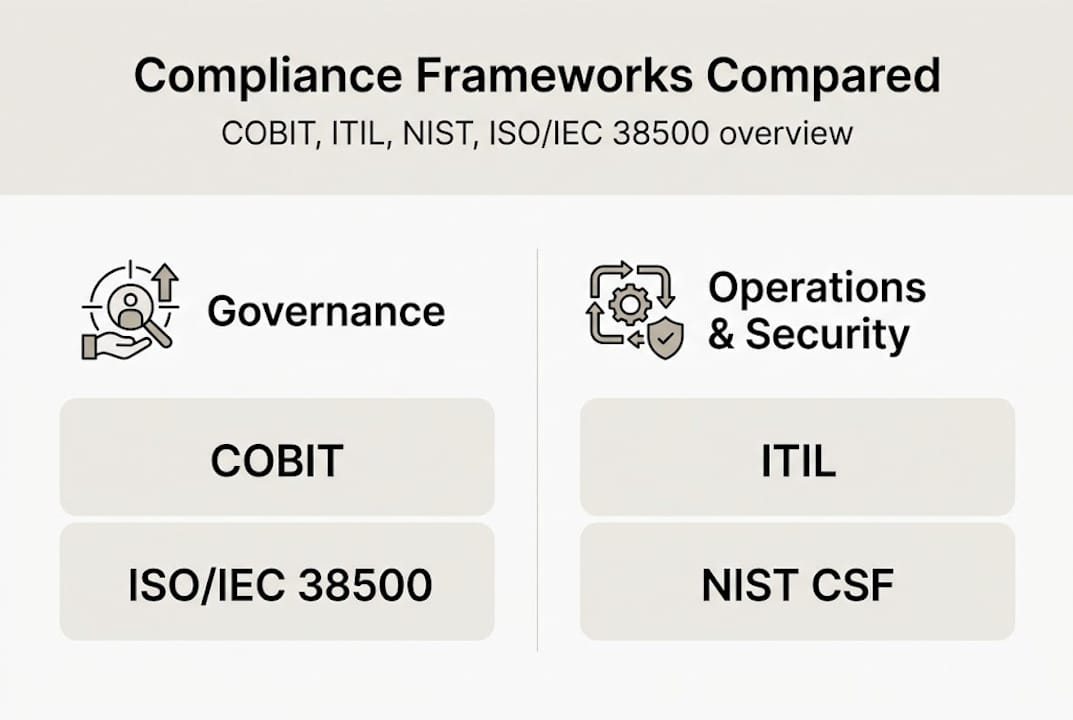
Comparing top compliance frameworks: COBIT, ITIL, NIST, and ISO/IEC 38500
No single framework addresses every dimension of IT governance, risk management, and cybersecurity. Key IT governance frameworks for regulatory compliance include COBIT, ITIL, NIST CSF, and ISO/IEC 38500, and in regulated industries, these are routinely stacked together rather than used in isolation. Understanding what each delivers is the first step toward building a coherent compliance architecture.
| Framework | Primary focus | Best suited for | Governance level |
|---|---|---|---|
| COBIT | IT governance and risk management | Board and executive oversight | Strategic |
| ITIL | IT service management and operations | Service delivery and continuity | Operational |
| NIST CSF | Cybersecurity risk and controls | Security maturity and incident response | Technical/Strategic |
| ISO/IEC 38500 | Board-level IT accountability | Corporate governance of IT | Strategic |
COBIT is particularly valuable for organizations that need to demonstrate governance rigor to boards and regulators. It provides a structured model for aligning IT decisions with business objectives and managing risk at scale. ITIL, by contrast, focuses on service delivery. It gives operations teams the process discipline to maintain uptime, manage change, and meet service-level commitments that underpin compliance.

NIST CSF has become the de facto cybersecurity backbone for organizations in the United States, particularly those in defense, healthcare, and critical infrastructure. Its five core functions, Identify, Protect, Detect, Respond, and Recover, map cleanly onto audit requirements and provide a measurable maturity model. ISO/IEC 38500 rounds out the picture by establishing board-level accountability for IT decisions, ensuring that governance does not stop at the CIO level.
Pro Tip: Do not attempt to implement all four frameworks simultaneously from scratch. Start with framework implementation steps that map your current gaps, then layer frameworks in priority order based on your regulatory obligations and risk profile.
The most effective approach is a unified compliance strategy that uses COBIT and ISO/IEC 38500 for board-facing governance, NIST CSF for cybersecurity controls, and ITIL for operational discipline. For a detailed breakdown of how COBIT and ITIL interact, the COBIT vs ITIL guide from Intellectsoft is a useful reference. Understanding what each framework delivers, IT leaders can now see how precise mapping improves compliance posture.
Navigating sector-specific compliance: HIPAA, DORA, GLBA, and the rise of AI regulation
Generic framework knowledge only takes you so far. In practice, IT leaders in regulated industries must manage sector-specific mandates that layer on top of foundational governance frameworks, creating complex compliance stacks that require deliberate coordination.
AI compliance is sector-specific with framework stacking as the norm. Healthcare organizations typically operate under HIPAA plus GDPR for any international data handling. Financial institutions face DORA plus GLBA plus NYDFS cybersecurity requirements, and often additional state-level rules. Each of these combinations introduces overlapping controls, sometimes with conflicting requirements around data retention, breach notification timelines, and access management.
The 2026 regulatory landscape raises the bar further. HIPAA Security Rule updates include mandatory multi-factor authentication, advanced encryption standards, annual technical audits, and a 72-hour incident reporting window. These are not optional enhancements. They represent a fundamental shift in the minimum acceptable standard for healthcare data protection. For a deeper look at what these changes mean operationally, the HIPAA safeguards 2026 breakdown is worth reviewing.
AI systems introduce an entirely new layer of compliance variables. Organizations deploying AI in clinical decision support, credit scoring, or fraud detection must now account for authenticated identity management, FIPS-validated encryption, and detailed audit logging of model inputs and outputs. Regulators are increasingly treating AI systems as regulated entities in their own right, not just tools.
A practical approach to managing overlapping mandates involves the following steps:
- Map all applicable regulations to your industry, geography, and data types before selecting controls.
- Identify overlapping requirements where a single control satisfies multiple mandates, reducing duplication.
- Flag conflicting requirements early, particularly around data residency and retention, and escalate to legal counsel.
- Build a unified control library that tags each control to the specific regulations it satisfies.
- Assign ownership for each control to a named individual, ensuring accountability across the compliance stack.
Organizations that invest in multi-regulatory compliance planning early avoid the costly rework that comes from discovering conflicts during an audit. With the landscape mapped, IT leaders must also address emerging edge cases and real-world pitfalls.
Edge cases, pitfalls, and future threats: What most compliance guides miss
Most compliance guidance focuses on the primary frameworks and their core requirements. What gets less attention are the edge cases and structural vulnerabilities that consistently cause organizations to fail audits, suffer breaches, or face regulatory action despite having formal compliance programs in place.
Third-party risk is the most persistent blind spot. Third-party risks cause 35% of breaches, and human error accounts for 82% of cloud misconfigurations. These are not abstract statistics. They represent real gaps in vendor contracts, inadequate security assessments, and misconfigured cloud storage buckets that expose sensitive data. Your compliance posture is only as strong as your least-scrutinized vendor.
AI classification ambiguities affect 40% of systems, creating significant uncertainty for organizations trying to determine which regulatory requirements apply to a given AI deployment. Is a recommendation engine a high-risk AI system under the EU AI Act? Does an automated underwriting model trigger ECOA obligations? These questions do not have simple answers, and getting them wrong carries real regulatory exposure.
Regulatory conflicts add another layer of complexity. GDPR's data minimization and residency requirements can directly conflict with the CLOUD Act's provisions allowing US law enforcement access to data held by American companies, regardless of where that data is stored. Organizations operating across jurisdictions need nuanced strategies, not generic policies.
Key pitfalls to actively monitor and mitigate:
- Vendor due diligence gaps: Conduct annual security assessments of all third parties with access to sensitive data, not just at onboarding.
- Cloud misconfiguration drift: Implement continuous configuration monitoring rather than point-in-time reviews.
- Regulatory conflict mapping: Maintain a living document that tracks where your applicable regulations conflict and how each conflict is resolved.
- AI system inventory: Classify every AI system by risk level and applicable regulation before deployment, not after.
- Cross-functional ownership: Compliance failures often occur at the seams between IT, legal, and operations. Assign explicit accountability across teams.
Pro Tip: Use the NIST compliance checklist as a baseline for continuous control validation, not just pre-audit preparation. It provides a structured way to catch configuration drift and control gaps before regulators do.
To make proactive compliance a differentiator, IT leaders need to shift from reactive to strategic oversight.
Beyond the checklist: Why compliance maturity depends on executive mindset
Here is the uncomfortable truth that most compliance guides avoid: frameworks do not create compliance maturity. Executives do. We have seen organizations with meticulously documented NIST implementations fail audits because no one in leadership actually understood what the controls were protecting or why. The documentation was pristine. The culture was hollow.
Real compliance maturity comes from executives who regularly interrogate their own assumptions. Who ask not just "are we compliant?" but "does our compliance program reflect our actual risk environment?" That distinction matters. A virtual CISO perspective can be invaluable here, providing the independent challenge function that internal teams often cannot.
The organizations that consistently outperform on compliance embed it in business objectives and tie risk-aware decision making to performance incentives. They treat compliance not as a cost center but as a signal of operational discipline that creates competitive advantage. That mindset shift, from obligation to differentiator, is what separates audit-ready organizations from those that scramble every time a regulator calls.
Advance your compliance strategy with expert support
Building a compliance program that holds up across multiple frameworks, sector-specific mandates, and evolving threats is not a task that most internal teams can manage alone. The regulatory environment is simply too dynamic, and the cost of getting it wrong is too high.

Heights Consulting Group works with C-level leaders and security teams to map, integrate, and optimize compliance frameworks tailored to their specific regulatory obligations and risk profiles. From technical cybersecurity consulting to understanding the role of compliance frameworks in healthcare, our advisors bring the strategic depth and operational experience that regulated industries demand. If you are ready to move from reactive compliance to a purpose-driven, audit-ready program, connect with Heights CG to schedule a readiness assessment or framework strategy consultation.
Frequently asked questions
What frameworks should IT leaders prioritize for regulatory compliance?
IT leaders should prioritize COBIT for governance, ITIL for operations, and NIST CSF for cybersecurity, then layer sector-specific frameworks based on their industry and regulatory obligations.
What are the biggest compliance risks for regulated industries in 2026?
Third-party risk and human error are leading causes of compliance failures, while regulatory conflicts and AI ambiguities represent fast-growing threats that most organizations are underprepared to address.
How does 'framework stacking' work for compliance?
Framework stacking means combining multiple frameworks, such as HIPAA plus GDPR or DORA plus GLBA, to satisfy overlapping compliance mandates across different regulatory domains simultaneously.
What are the new HIPAA compliance requirements for 2026?
Proposed 2026 HIPAA updates include mandatory multi-factor authentication, advanced encryption, annual technical audits, and a 72-hour incident reporting requirement for covered entities.
How can IT leaders address regulatory conflicts like GDPR vs CLOUD Act?
They should adopt nuanced data residency and contractual controls, maintain a living conflict-resolution document, and seek ongoing legal counsel as the cross-jurisdictional landscape continues to evolve.
Recommended
- Regulatory Compliance Checklist 2026: Essential Steps for Executives | Heights Consulting Group
- CISOs and regulatory compliance success: 5 key roles
- Navigating Regulatory Compliance in 2026: Insights for Executives - Heights Consulting Group
- Cybersecurity Compliance: Strategies & Insights for 2026 - Heights Consulting Group.