Keeping patient data safe feels like an endless challenge when every new system, device, or connection multiplies your attack surface. For American healthcare leaders, security is a daily test of balancing care delivery with strict regulatory demands. Managed security in healthcare brings clarity and structure with adaptable controls that address complex risks, ensure HIPAA compliance, and support innovation without placing patient safety at risk.
Table of Contents
- Understanding Managed Security In Healthcare
- Core Components And Service Models Explained
- Essential Compliance And Regulatory Drivers
- Key Benefits For Healthcare Organizations
- Risks, Challenges, And Cost Implications
- Comparing Managed Security To In-House Solutions
Key Takeaways
| Point | Details |
|---|---|
| Healthcare Managed Security | Acts as a strategic framework to protect sensitive data while ensuring compliance and operational efficiency. |
| Three Key Components | Essential layers include organizational policies, risk management, and technology controls, all working together for effective security. |
| Service Model Options | Organizations can choose from full outsourcing, co-managed services, or on-premises management based on their needs and resources. |
| Compliance Importance | Adhering to regulations like HIPAA is critical, as non-compliance can lead to severe financial repercussions and reputational damage. |
Understanding Managed Security in Healthcare
Managed security in healthcare operates as a strategic framework designed to protect sensitive patient data while maintaining operational efficiency. Unlike generic IT security approaches, healthcare-specific managed security addresses the unique regulatory environment where patient safety and data protection are inseparable. Your organization faces a distinct challenge: you must safeguard electronic protected health information (ePHI) across complex clinical workflows without disrupting care delivery or slowing innovation. This is where managed security becomes not just a compliance checkbox but a operational necessity.
The foundation of healthcare managed security rests on HIPAA's administrative, physical, and technical safeguards that your organization must implement. Rather than a one-size-fits-all mandate, the Security Rule creates a flexible framework scaled to your facility's size, structure, and specific risks. A 50-bed critical access hospital faces different threat vectors than a large urban medical center or a specialized surgery center. Managed security providers understand this variability and tailor their approach accordingly. The core objective remains constant: protecting the integrity, availability, and confidentiality of ePHI while enabling adoption of technologies that improve patient care and operational efficiency. When security becomes restrictive enough that clinicians bypass controls or patient outcomes suffer, you have missed the mark entirely.
Implementing effective managed security requires three interconnected layers working in concert:
-
Organizational policies and workforce training: Staff members represent your strongest or weakest security control. A clinician who understands why they cannot email patient records to a personal account prevents data breaches more reliably than any firewall rule. Managed security includes ongoing education that connects security practices to patient safety and regulatory compliance.
-
Risk management and assessment: Rather than assuming standardized controls work for your environment, comprehensive approaches combining privacy and security efforts identify your actual vulnerabilities. This involves regular audits, vulnerability assessments, and threat modeling specific to your clinical workflows, surgical schedules, and connected medical devices.
-
Technology controls and monitoring: From access controls on electronic health records to detection systems monitoring unusual data access patterns, these tools enforce the policies and catch threats your staff cannot identify manually. This layer includes endpoint protection, network monitoring, incident detection capabilities, and identity management systems that work together seamlessly.
When you implement managed security effectively, something shifts within your organization. Rather than security existing as an obstacle to clinical work, it becomes woven into how your teams operate. A guide on healthcare managed services can help executive leaders understand how external partners integrate these capabilities into your existing infrastructure without requiring massive internal hiring or capital expenditure.
Pro tip: Start by conducting a risk assessment focused on your highest-value data flows and most critical systems, then prioritize managed security controls around those areas rather than attempting comprehensive coverage all at once.
Core Components and Service Models Explained
Managed security in healthcare operates through distinct technical and organizational components that work together to detect, prevent, and respond to threats. These components form the backbone of any managed security program, regardless of whether you deploy them internally, outsource them entirely, or use a hybrid approach. Understanding what these components are and how they function separately and together helps you evaluate managed security offerings and determine which service model aligns with your organization's capabilities, budget, and risk tolerance.

The technical foundation includes threat identification and detection systems that continuously monitor your network and endpoints for suspicious activity. This goes beyond traditional firewalls that simply block known bad traffic. Modern detection requires behavioral analysis that recognizes when a user accesses files they have never touched before, or when a workstation suddenly generates unusual network traffic patterns. Vulnerability management identifies weaknesses in your systems before attackers exploit them through regular scanning, assessment, and prioritization of remediation efforts. Data protection controls restrict who can access sensitive information and monitor how that data moves through your systems. Incident response capabilities provide structured processes to contain, investigate, and recover from security events when they occur. Finally, continuous monitoring operates 24/7 to maintain visibility across your infrastructure. According to practical, scalable cybersecurity guidelines, these core components must be tailored to your organization's specific size and structure rather than applied as generic security controls.
This table summarizes the business impact of core managed security components in healthcare:
| Component | Primary Function | Business Impact |
|---|---|---|
| Threat Detection Systems | Identify abnormal activity in real time | Reduce downtime, protect patients |
| Vulnerability Management | Find and fix system weaknesses | Prevent breaches, avoid fines |
| Data Protection Controls | Restrict and monitor data access | Safeguard patient confidentiality |
| Incident Response | Contain and recover from attacks | Minimize operational disruption |
| Continuous Monitoring | Provide 24/7 oversight | Ensure compliance, build trust |
Service models determine how these components are delivered and managed. You have three primary options:
Full outsourcing to managed security service providers (MSSPs) means an external team handles firewall management, intrusion detection, vulnerability scanning, and compliance audits. This model works well if your organization lacks internal security expertise or cannot justify hiring dedicated security staff. MSSPs bring economies of scale, access to specialized tools, and round-the-clock monitoring. The trade-off is reduced direct control over security decisions and dependency on vendor responsiveness. Your team shifts from managing security operations to managing the vendor relationship.
Co-managed services blend your internal security team with MSSP expertise. Your staff might handle day-to-day access management and routine updates while the MSSP provides threat hunting, advanced analytics, and strategic guidance. This model leverages your team's deep knowledge of your clinical workflows while filling gaps in specialized expertise. It requires clear delineation of responsibilities and strong communication channels between internal and external teams. Many healthcare organizations find this sweet spot because it balances cost with control and expertise.
On-premises security management keeps all security operations internal. This approach provides maximum control and customization but demands significant investment in hiring, training, and maintaining security talent. You also bear full responsibility for staying current with emerging threats and maintaining required certifications. For organizations with mature security programs and sufficient budget, this model ensures security decisions align perfectly with clinical operations.
Each service model maps to different organizational strengths. Managed security services involving continuous monitoring and threat detection require deep expertise in both healthcare operations and cybersecurity. The right choice depends on your current staffing, budget constraints, regulatory maturity, and strategic priorities. A health system with three facilities might start with co-managed services for core infrastructure while outsourcing specialized functions like vulnerability management. As your team grows and matures, you might shift toward more internal management of routine operations.
Here is a comparison of managed security service models for healthcare organizations:
| Service Model | Primary Advantage | Best Fit Organizations | Key Limitation |
|---|---|---|---|
| Full Outsourcing | Immediate expertise, 24/7 support | Lacking internal security staff | Less direct organizational control |
| Co-Managed | Balances control and expertise | Moderate internal security resources | Requires strong communication |
| On-Premises Management | Maximum customization and control | Large, mature security teams | High cost and staffing challenges |
Think about this practically: if your organization struggles to fill IT positions, full outsourcing provides immediate expertise and frees your small team from 24/7 monitoring responsibilities. If you have strong internal IT leadership but lack security depth, co-managed services allow you to learn from external experts while maintaining control. If you operate in a highly specialized clinical environment with unique data flows and regulatory requirements, on-premises management ensures security decisions account for those nuances.
Pro tip: Before selecting a service model, map your organization's current security maturity against the three options by listing available internal expertise, budget availability, and regulatory compliance gaps, then choose the model that addresses your largest weakness rather than attempting perfection across all areas.
Essential Compliance and Regulatory Drivers
Compliance is not optional in healthcare cybersecurity. It is the legal and operational foundation that forces your organization to build security programs worth maintaining. Unlike other industries where security might be considered a nice-to-have competitive advantage, healthcare regulations mandate specific security controls and create serious consequences for failures. Understanding which regulations apply to your organization and what they actually require shapes every managed security decision you make.
Federal regulations form the backbone of healthcare cybersecurity requirements. HIPAA (Health Insurance Portability and Accountability Act) establishes the primary framework for protecting electronic health information, requiring administrative, physical, and technical safeguards that we discussed earlier. HITECH (Health Information Technology for Economic and Clinical Health Act) strengthened HIPAA by increasing penalties for breaches and extending liability to business associates who handle patient data on your behalf. The 21st Century Cures Act added another layer by promoting interoperability while maintaining strict security requirements, forcing you to balance the desire to share data across systems with the need to prevent unauthorized access. These are not vague aspirations. Federal healthcare regulations mandate specific protections, require regular risk assessments, enforce breach notification within 60 days, and tie compliance directly to your organization's licensing and reimbursement. A single breach notification can cost your organization hundreds of thousands of dollars in direct expenses, legal fees, and reputational damage.
Beyond federal mandates, your organization likely faces additional regulatory pressure depending on your structure and patient population. State regulations often exceed federal minimums. If you handle Medicare or Medicaid patients, you must comply with Centers for Medicare and Medicaid Services (CMS) requirements. If you conduct research, the FDA oversees medical device cybersecurity. If you handle payment card information from patients paying out of pocket, PCI DSS compliance applies. Each regulation adds specific requirements to your managed security program. This is where many healthcare leaders get trapped: they focus exclusively on HIPAA compliance and discover too late that their program fails to meet state requirements or CMS expectations. The regulatory environment is not one checkbox. It is a stack of overlapping requirements that your managed security program must address comprehensively.
Managed security providers who work in healthcare understand this regulatory complexity because they live it daily. Top cyber threats and recommended practices specifically designed for healthcare provide practical guidance that aligns with regulatory expectations while remaining cost-effective. The Health Industry Cybersecurity Practices guide, for example, addresses the specific vulnerabilities in your environment: medical devices that run outdated software, clinical workflows that depend on speed and accessibility, and the constant tension between patient care delivery and security controls. When you select a managed security partner, verify they can demonstrate how their services map to your specific regulatory requirements. Ask them to show you exactly which controls satisfy HIPAA technical safeguards, how they document compliance evidence for audits, and what happens when a breach occurs. A provider who mumbles about "general security best practices" does not understand healthcare regulation.
Think about the real cost of non-compliance. A major health system in 2024 paid over 50 million dollars in settlements related to a data breach affecting 2.5 million patient records. That settlement included regulatory fines, litigation costs, and mandatory investment in enhanced security infrastructure. The organization's managed security program did not fail because they used the wrong technology. It failed because they did not fully understand their regulatory obligations or ensure their security controls actually addressed the specific vulnerabilities in their environment. Compliance-driven managed security is not about checking boxes on an audit form. It is about building defenses that actually prevent the breaches that regulators investigate and patients suffer from.
Pro tip: Conduct a compliance gap analysis mapping your current security controls against HIPAA Technical Safeguards, HITECH requirements, and any state-specific rules, then use that assessment to prioritize which managed security capabilities address your highest-risk gaps rather than trying to solve every regulatory requirement simultaneously.
Key Benefits for Healthcare Organizations
Managed security delivers tangible returns that go far beyond checking compliance boxes or satisfying auditors. When implemented effectively, managed security fundamentally changes how your organization operates by reducing operational disruption, protecting patient safety, and freeing your leadership team to focus on clinical innovation rather than firefighting security incidents. Understanding these benefits helps you justify the investment and align managed security with your organization's broader strategic priorities.
The most immediate benefit is operational resilience. A ransomware attack that encrypts your EHR system does not just create a security problem; it stops patient care. Surgeries get canceled. Emergency departments operate on paper charts. Medication dispensing slows. Patient outcomes suffer. Managed security prevents these scenarios by detecting threats before they disrupt systems and responding rapidly when incidents occur. Protecting electronic health records and clinical systems from cyberattacks that could disrupt care delivery directly protects patient safety. A health system that maintains continuous access to accurate patient information makes better clinical decisions. This is not theoretical; hospitals that experienced major cyber incidents report measurable increases in medication errors, adverse events, and patient mortality during the outage period. Managed security keeps your systems running, which keeps your patients safer.
The financial benefits extend far beyond avoided ransom payments. Consider the concrete costs of a breach: notification expenses, credit monitoring for affected patients, legal defense, regulatory fines, and the opportunity cost of staff time spent on incident response instead of productive work. A mid-sized health system breach can easily exceed 5 million dollars in direct costs. Beyond direct expenses, breaches damage patient trust. Healthcare organizations that suffer publicized data breaches see patient volume decline, employee recruitment becomes harder, and reputation recovery takes years. Managed security also reduces the overhead of maintaining security infrastructure internally. Your small IT team no longer needs to deploy and manage firewalls, intrusion detection systems, and security monitoring platforms. External experts handle these functions, allowing your internal staff to focus on supporting clinical workflows rather than patrolling networks for threats.
Managed security also optimizes resource allocation in ways many CISOs underestimate. Your organization likely employs talented IT professionals who were hired for infrastructure management, not cybersecurity. Managed security provides advanced threat intelligence and ensures rapid incident response while your internal team focuses on their core strengths. This complementary approach achieves better security outcomes with lower total cost than forcing your infrastructure team to become security experts or attempting to hire dedicated security staff in a market where cybersecurity talent is scarce and expensive. A co-managed approach, for instance, lets your team handle day-to-day access provisioning and routine updates while external specialists conduct threat hunting and strategic planning.
Regulatory compliance becomes less burdensome when managed security is part of your program. Auditors want evidence that you assess risks, monitor systems, respond to incidents, and maintain documentation. Managed security providers generate this evidence continuously. They conduct vulnerability scans, maintain audit logs, document security controls, and provide incident response records. Your compliance team no longer scrambles to compile evidence weeks before an audit; the evidence already exists in organized, auditor-ready formats. This reduces the time and stress your compliance team experiences during regulatory reviews.
The confidence you gain as a CISO or IT security leader matters more than many executives realize. When you know that threats are being monitored 24/7 by skilled professionals, that vulnerabilities are being identified and remediated systematically, and that your organization can respond rapidly to incidents, you stop waking up at 3 AM worrying about what you might have missed. That peace of mind allows you to lead strategically rather than react tactically.
Pro tip: When evaluating managed security benefits for your board or finance committee, quantify the avoided costs of a breach specific to your organization's size and patient population rather than using generic industry averages, then compare that to the managed security investment to demonstrate clear financial justification.
Risks, Challenges, and Cost Implications
The healthcare cybersecurity landscape has shifted dramatically in recent years. Threats that seemed unlikely five years ago now occur regularly. Attackers targeting healthcare are increasingly sophisticated, better funded, and more persistent than threats in other industries. These realities create substantial risks and challenges that your organization must address, and the financial implications of getting managed security wrong are severe enough to threaten organizational viability.
Ransomware attacks have become the dominant threat in healthcare. Unlike generic malware that steals data and disappears, ransomware encrypts your entire system and demands payment for decryption keys. When ransomware hits a health system, patient care stops immediately. Emergency departments cannot access medication lists. Surgery schedules disappear. Billing departments cannot process insurance claims. The ripple effects extend far beyond your organization: patients cannot schedule appointments at affiliated practices, pharmacy networks experience delays, and insurance companies struggle to verify coverage. Increasing sophistication of ransomware attacks, especially targeting critical third-party service providers causes widespread operational impact across entire healthcare ecosystems. A single attack on a major health information exchange or billing processor can paralyze hundreds of healthcare organizations simultaneously. The Change Healthcare ransomware attack in early 2024 demonstrated this reality perfectly. That single incident disrupted medical practices nationwide, delayed patient care, and created months of recovery work.
The financial consequences of these attacks are staggering. Direct ransom payments typically range from hundreds of thousands to tens of millions of dollars depending on the organization's size and operational criticality. But ransom is only the beginning. Recovery costs include hiring forensic investigators, rebuilding systems from clean backups, implementing new security controls, and investing in advanced detection technology. Lost revenue accumulates as billing systems remain offline and elective procedures get postponed. Insurance reimbursement delays create cash flow crises. A mid-sized health system might lose 100,000 dollars per day in revenue during an extended outage. Recovery timelines stretch from weeks to months depending on attack severity and backup availability. Some organizations never fully recover operationally or financially. Beyond immediate costs, cyberattacks such as the Change Healthcare ransomware incident demonstrate how an attack can paralyze billing processes and threaten the viability of medical practices nationwide.
Third-party risk compounds these challenges significantly. Your organization does not operate in isolation. You depend on electronic health information exchanges, billing processors, pharmacy networks, medical device manufacturers, and cloud service providers. Each connection creates a potential entry point for attackers. If your EHR vendor's system gets compromised, attackers potentially access your data without ever attacking you directly. Managing third-party risk requires visibility into their security practices, contractual requirements for security standards, and monitoring of their systems for unusual activity. Many healthcare organizations struggle with this because they have dozens or hundreds of third-party connections and limited resources to assess each vendor's security posture comprehensively.
Staffing shortages create another critical challenge. Qualified cybersecurity professionals are scarce and expensive. A skilled security engineer in a major healthcare market commands a salary of 150,000 to 200,000 dollars annually, and even at that price, recruitment takes months. Many healthcare organizations lack the budget or geographic appeal to attract this talent. This creates a vicious cycle: without adequate security staffing, your organization remains vulnerable. That vulnerability eventually leads to breaches, which damage reputation and make recruitment even harder. Some health systems have attempted to solve this through aggressive hiring, only to discover that their internal team cannot keep pace with the sophistication of modern threats without external expertise.
Balancing investment across prevention, detection, and remediation presents another strategic challenge. Prevention investments reduce breach probability but never eliminate it. Detection capabilities allow you to catch attacks quickly and limit damage. Remediation focuses on recovery after incidents occur. Each area demands resources, and budget constraints force difficult choices. Many organizations starve detection and remediation to fund prevention, only to discover that when a breach inevitably occurs, they lack the capabilities to respond effectively. This is where managed security provides clarity: an external provider brings economies of scale and specialized expertise across all three areas.
Pro tip: Quantify your organization's specific financial exposure by calculating daily revenue loss during a typical outage, multiplying by a realistic recovery timeframe based on your backup and recovery procedures, then add conservative estimates for incident response costs and regulatory fines to establish a realistic budget for preventive managed security investment.
Comparing Managed Security to In-House Solutions
The decision between building an internal security team and outsourcing to managed security providers is not a simple choice. Each approach has genuine strengths and real limitations. Understanding the trade-offs helps you make a decision aligned with your organization's capabilities, budget, and strategic direction. Many healthcare leaders discover that the choice is not binary; the best approach often combines elements of both.
In-house security teams offer meaningful advantages. Your internal team understands your clinical workflows, your legacy systems, your regulatory environment, and your organizational culture in ways external providers never will. They can make rapid decisions without waiting for vendor approval. They build relationships with clinical leadership that facilitate security policy adoption. They customize controls to fit your specific operational needs rather than implementing standard solutions. If you have the budget and talent pipeline to build a mature internal program, you gain direct control and deep contextual knowledge. However, building and maintaining this capability demands significant investment. A minimal in-house security team for a mid-sized health system includes a CISO, a security engineer, an analyst, and administrative support. That represents 400,000 to 600,000 dollars annually in salary and benefits before accounting for tools, training, and overhead. More comprehensive programs cost substantially more. Beyond cost, in-house security may offer more direct control but often faces challenges with staffing, higher operational costs, and difficulty maintaining up-to-date defense capabilities against rapidly evolving threats. Healthcare organizations struggle particularly with retention because talented security professionals can earn more in financial services or technology companies, and many prefer not to work in healthcare's highly regulated, high-stakes environment.
Managed security services address these constraints through specialization and scale. An MSSP brings expertise across hundreds of healthcare organizations, exposing them to threat patterns and attack techniques that no single organization's internal team will encounter. They invest in advanced detection tools, threat intelligence, and forensic capabilities that distribute costs across their entire customer base. They maintain 24/7 security operations centers staffed with analysts who specialize in threat detection and response. They hire and retain talent by offering career development paths, specialization opportunities, and compensation competitive with other technology industries. When a new vulnerability emerges, they update detection signatures for all customers simultaneously. When a new attack technique appears, they incorporate lessons learned across their entire customer portfolio. This distributed learning accelerates defensive capabilities. However, outsourced security requires careful vendor selection and governance. A poor MSSP relationship creates false confidence in security coverage while actual threats go undetected. You must establish clear service level agreements, define escalation procedures, and maintain oversight of their monitoring and response activities. The Change Healthcare ransomware attack demonstrated how dependent healthcare organizations are on third-party service providers. That attack occurred because an adversary exploited a vulnerability in a third-party software platform used across the healthcare industry. No internal team at any individual health system could have prevented an attack on a vendor's system that they did not directly control.
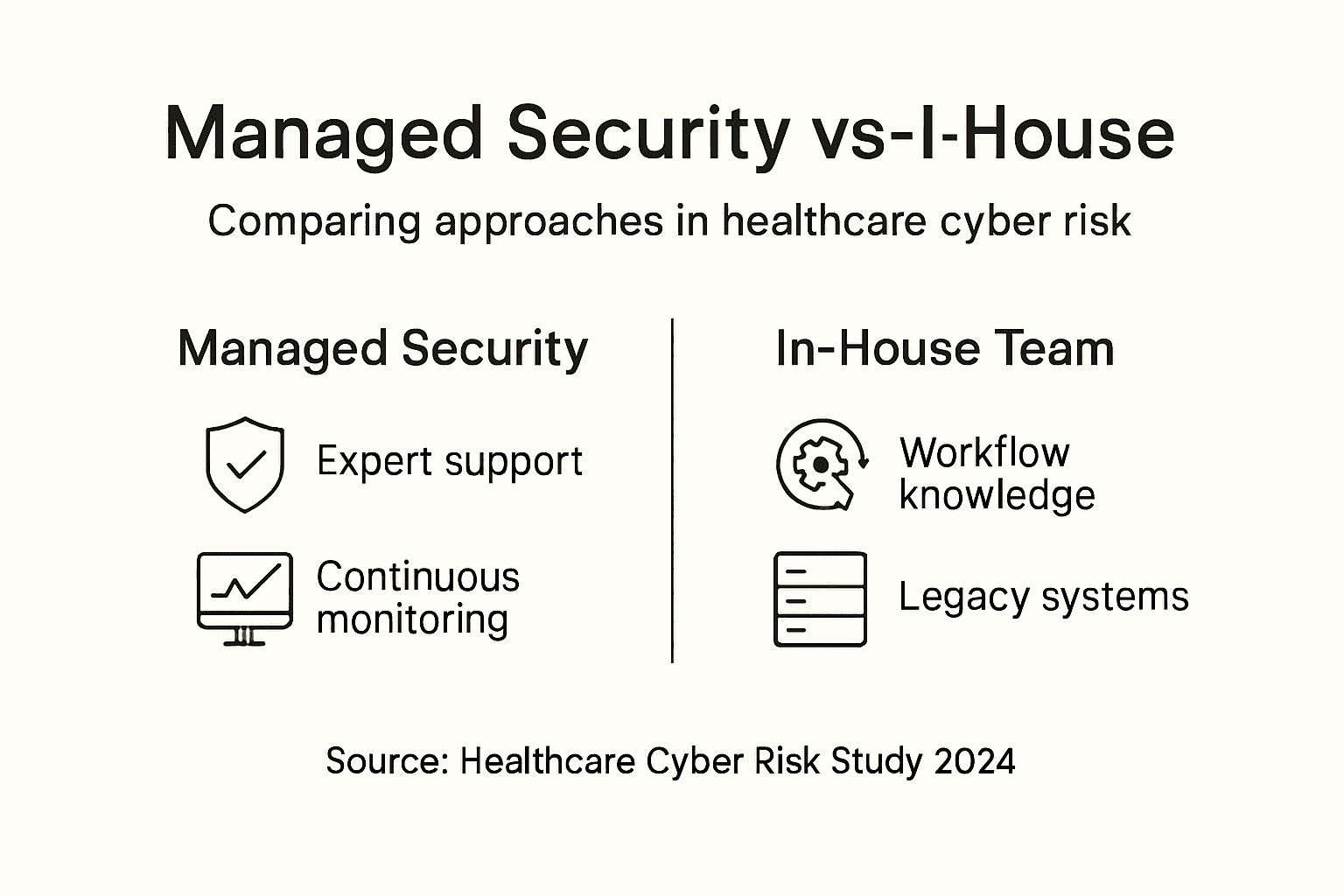
Co-managed security represents a pragmatic middle ground that many healthcare organizations are adopting. Your internal team focuses on day-to-day operations, access management, system administration, and clinical systems integration. External specialists provide threat hunting, advanced analytics, strategic planning, and specialized incident response. This approach leverages your team's contextual knowledge while supplementing their expertise with external specialization. You maintain control over decisions while benefiting from economies of scale. The success of co-managed arrangements depends entirely on clear role definition and strong communication. When responsibilities blur, critical tasks fall through cracks and security gaps emerge.
Think practically about your specific situation. If your organization currently has zero security personnel, building an in-house program from scratch while managing acute healthcare operations is unrealistic. Managed security provides immediate capability and expertise. If you have a small but capable internal team, co-managed services amplify their effectiveness without requiring massive hiring. If you have a mature internal program with multiple specialists, selective outsourcing of specialized functions allows your team to focus on strategic initiatives. The optimal choice depends on your current state, budget constraints, available talent, and organizational priorities.
Pro tip: Rather than making an all-or-nothing choice, assess your organization's maturity across threat detection, incident response, vulnerability management, and compliance monitoring, then select managed services for the areas where you have the largest capability gaps, allowing your internal team to focus on areas where they provide the most value.
Strengthen Your Healthcare Cybersecurity with Strategic Managed Security
Healthcare organizations face complex challenges protecting sensitive patient data while maintaining seamless clinical operations. This article highlights critical issues such as ransomware threats, evolving regulatory compliance like HIPAA and HITECH, and limited internal cybersecurity resources. Managed security solutions that combine 24/7 threat detection, vulnerability management, and incident response can transform cybersecurity from a reactive burden into a strategic advantage that safeguards patient safety and operational resilience.
Heights Consulting Group specializes in aligning advanced cybersecurity capabilities with healthcare business objectives and compliance mandates. Our managed cybersecurity services integrate industry best practices tailored specifically for healthcare environments challenged by staffing shortages and regulatory complexity. We empower your leadership with clear risk management strategies, continuous monitoring, and expert incident response designed to reduce breach risks and ensure audit readiness.

Take control of your healthcare cybersecurity today. Discover how to build a mature, effective managed security program that adapts to your unique clinical workflows and compliance demands by partnering with Heights Consulting Group. Visit our website now to learn more and schedule a consultation.
Frequently Asked Questions
What is managed security in healthcare?
Managed security in healthcare is a framework designed to protect sensitive patient data while ensuring compliance with regulations like HIPAA. It involves implementing tailored security measures specific to healthcare organizations to safeguard electronic protected health information (ePHI).
How does managed security differ from traditional IT security?
Managed security differs from traditional IT security by addressing the unique challenges and regulatory requirements of the healthcare industry. It focuses on protecting patient safety and data integrity without disrupting clinical workflows, while traditional IT security may not prioritize these factors.
What are the core components of a managed security program in healthcare?
The core components include threat identification and detection systems, vulnerability management, data protection controls, incident response capabilities, and continuous monitoring. These elements work together to prevent, detect, and respond to security threats effectively.
What are the benefits of implementing managed security for healthcare organizations?
Implementing managed security improves operational resilience, protects patient safety, reduces costs associated with breaches, and streamlines compliance with regulations. It allows healthcare organizations to focus on clinical innovation rather than navigating security incidents.