Healthcare organizations with formal incident response teams save an average of $1.2 million per breach compared to those without dedicated teams. Yet 62% of healthcare executives mistakenly view IR teams as purely technical functions, missing their strategic impact on compliance, risk mitigation, and business continuity. This guide reveals how optimizing your incident response capabilities transforms regulatory burden into competitive advantage while protecting patient data and organizational reputation.
Table of Contents
- Understanding Incident Response Teams in Healthcare Cybersecurity
- Core Responsibilities and Strategic Roles of Incident Response Teams
- Common Misconceptions About Incident Response Teams in Healthcare
- Organizational Models and Best Practices for Optimizing Incident Response Teams
- Measuring Incident Response Effectiveness: Metrics and Benchmarks
- Integrating Incident Response with Risk Management and Compliance
- Case Studies: Successful Incident Response in U.S. Healthcare
- Strategic Recommendations and Next Steps for Healthcare Executives
- Frequently Asked Questions About Incident Response Teams in Healthcare
Key Takeaways
| Point | Details |
|---|---|
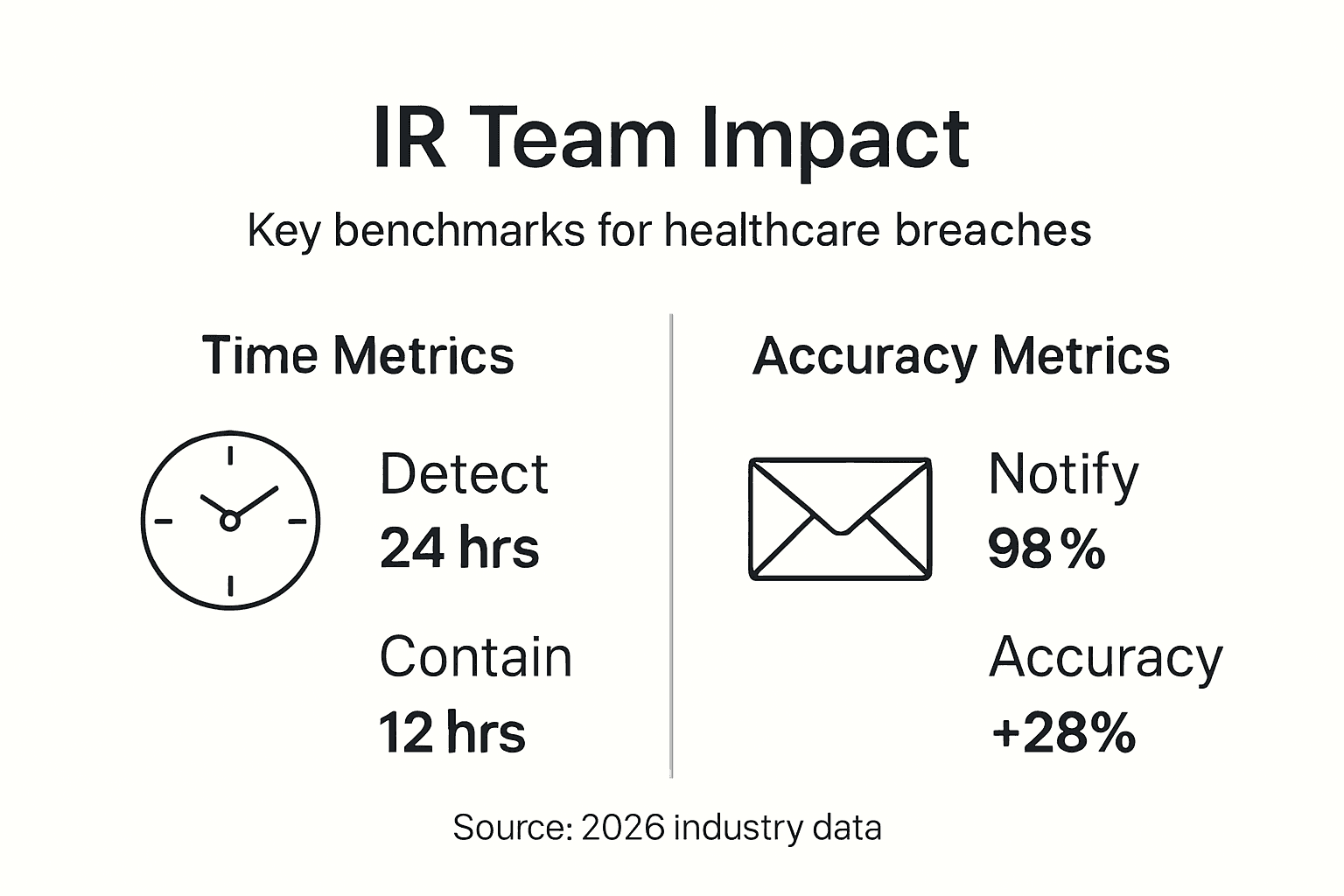
| Cost Reduction | Incident response teams reduce breach costs by 28% and improve notification compliance across healthcare organizations. |
| Strategic Integration | IR teams bridge technical response with regulatory requirements and enterprise risk management functions. |
| Compliance Impact | Formal IR teams reduce delayed breach notifications from 45% to 12%, preventing regulatory penalties. |
| AI Enhancement | Artificial intelligence and proactive threat hunting improve detection accuracy by 28% while reducing false positives. |
| Misconception Cost | Viewing IR as purely technical limits effectiveness and delays strategic investment in cybersecurity capabilities. |
Understanding Incident Response Teams in Healthcare Cybersecurity
Healthcare organizations face relentless targeting by threat actors seeking valuable patient data and operational disruption opportunities. The sector reported 725 large breaches in 2025, affecting over 133 million patient records. This escalating threat landscape demands coordinated, expert response capabilities that extend far beyond traditional IT troubleshooting.
Incident response teams in healthcare serve as specialized units combining technical expertise with regulatory knowledge. They detect security incidents, contain threats, eradicate vulnerabilities, and manage the complex compliance requirements surrounding patient data protection. Unlike general IT support, these teams operate under strict regulatory frameworks including HIPAA, HITECH Act provisions, and state breach notification laws.
The compliance stakes are substantial. Organizations without formal IR capabilities face significant challenges. Research shows 45% of healthcare organizations without formal IR teams missed breach notification deadlines compared to 12% with formal teams. These delays trigger regulatory penalties, extended investigations, and reputational damage that compounds the initial breach impact.
Effective incident response in healthcare operates across three critical tiers:
- Technical Operations: Real time threat detection, malware analysis, network forensics, and system remediation
- Compliance Management: Breach assessment, notification coordination, regulatory reporting, and documentation
- Strategic Integration: Risk communication, business continuity coordination, and executive decision support
This three tier framework ensures incident response capabilities align with both immediate security needs and long term organizational objectives. Executives who understand this structure can better evaluate their current capabilities and identify strategic improvement opportunities.
Core Responsibilities and Strategic Roles of Incident Response Teams
Incident response teams execute both operational and strategic functions that protect healthcare organizations from financial, regulatory, and reputational harm. The technical dimension includes continuous monitoring for suspicious activity, rapid containment when threats materialize, complete eradication of malicious code or unauthorized access, and systematic recovery to restore normal operations.
Yet effective IR teams integrate detection, containment, eradication with compliance management and communication. This integration distinguishes mature programs from basic reactive approaches. When a potential breach occurs, IR teams must simultaneously assess whether protected health information was accessed, determine notification obligations under multiple regulatory frameworks, coordinate with legal counsel on disclosure requirements, and communicate with affected stakeholders.

The strategic dimension extends to enterprise risk management. IR teams provide critical intelligence about threat patterns, vulnerability trends, and attack methodologies that inform broader security investments. They collaborate with business continuity planners to ensure response procedures align with operational recovery priorities. Executive leadership receives timely, accurate briefings that support informed decision making during crisis situations.
Compliance adherence represents a core IR responsibility often underestimated by organizations viewing these teams as purely technical. HIPAA's breach notification rule requires assessment within 60 days and notification within additional timeframes based on breach scale. HITECH Act provisions impose penalties for delayed or inadequate notifications. State laws add varying requirements that complicate multi jurisdiction operations.
Incident response teams navigate this regulatory complexity while managing the technical challenge of threat elimination. They document every action for regulatory review, preserve forensic evidence meeting legal standards, and coordinate with external parties including law enforcement, cyber insurance providers, and regulatory bodies. This multifaceted role demands both deep technical expertise and sophisticated understanding of healthcare compliance landscapes.
Organizations that staff IR teams exclusively with technical specialists miss the strategic value these capabilities provide. Optimal teams include compliance experts, risk analysts, and communication specialists alongside cybersecurity engineers. This composition ensures comprehensive response addressing all organizational impacts, not just technical remediation.
Common Misconceptions About Incident Response Teams in Healthcare
Several persistent misunderstandings limit incident response effectiveness across healthcare organizations. Recognizing and correcting these misconceptions enables better strategic planning and resource allocation.
Misconception 1: IR Teams Are Only IT and Technical
Many executives view incident response as an IT function handling malware removal and system restoration. This narrow perspective misses the compliance, legal, risk management, and communication dimensions essential in healthcare. Research indicates 62% of healthcare executives mistakenly view IR teams as purely technical functions, leading to inadequate team composition and insufficient authority during incidents.
Misconception 2: IR Is Not Integrated with Enterprise Risk Management
Some organizations treat incident response as separate from broader risk management programs. This siloed approach prevents sharing critical threat intelligence with risk assessment processes, limits coordination with business continuity planning, and reduces executive visibility into emerging threats. Mature organizations embed IR within enterprise risk frameworks, ensuring security intelligence informs strategic decisions.
Misconception 3: IR Teams Have Little Impact on Business Continuity
When executives underestimate IR's role in operational resilience, they deprioritize investments in response capabilities. Yet rapid incident containment directly determines downtime duration, patient care disruption, and revenue impact. Organizations with optimized IR capabilities resume normal operations faster, preserve more data integrity, and experience less operational disruption than peers with basic reactive approaches.
Misconception 4: AI Analytics Have Minimal Value in IR Accuracy
Skepticism about artificial intelligence in cybersecurity sometimes extends to dismissing AI's role in incident response. Modern AI tools dramatically improve detection accuracy, reduce false positive rates that waste analyst time, and identify subtle attack patterns humans miss. Organizations avoiding AI integration handicap their response capabilities against increasingly sophisticated threats.
Pro Tip: Schedule quarterly executive briefings where IR teams present recent incidents, emerging threats, and strategic recommendations. This regular engagement educates leadership about IR's full value, secures necessary investment, and ensures alignment between security capabilities and business objectives.
Addressing these misconceptions requires intentional communication between security teams and executive leadership. CISOs should frame incident response investments in business terms, demonstrating ROI through reduced breach costs, improved compliance outcomes, and enhanced operational resilience.
Organizational Models and Best Practices for Optimizing Incident Response Teams
Healthcare organizations can choose from several incident response models, each with distinct advantages depending on organizational size, risk profile, and resource availability. Understanding these models helps executives make informed decisions about team structure and capabilities.
| Model | Key Characteristics | Best For |
|---|---|---|
| Traditional Reactive | Responds after incidents detected; limited proactive monitoring | Small organizations with lower risk profiles |
| AI Augmented Proactive | Continuous threat hunting; AI integration improves detection accuracy by 28% | Medium to large healthcare systems |
| Hybrid Managed | Internal team supported by external specialists for complex incidents | Organizations building internal capabilities |
| Fully Managed External | Complete outsourcing to specialized providers | Resource constrained organizations needing immediate capabilities |
Aligning incident response with established frameworks provides structure and ensures comprehensive coverage. The NIST Cybersecurity Framework offers guidance across five functions: Identify, Protect, Detect, Respond, and Recover. Healthcare specific frameworks like HITRUST build on NIST while addressing regulatory requirements unique to patient data protection.
Clear governance structures prevent confusion during high pressure incidents. Effective models define:
- Decision Authority: Who authorizes containment actions that impact operations
- Escalation Paths: When and how incidents escalate to executive leadership
- External Coordination: Protocols for engaging law enforcement, regulators, and third parties
- Communication Protocols: Who communicates what information to which stakeholders
Proactive threat hunting represents a paradigm shift from reactive incident response. Rather than waiting for alerts, dedicated analysts actively search networks for indicators of compromise, investigate anomalous patterns suggesting stealthy attacks, and validate detection system effectiveness through regular testing. Organizations adopting proactive approaches discover threats average 60 days faster than reactive peers.
AI integration and NIST framework alignment improve detection accuracy by 28% while reducing analyst workload. Machine learning models identify subtle attack patterns, correlate indicators across multiple data sources, and prioritize alerts based on actual risk rather than simple rule matching. This allows human analysts to focus expertise on genuine threats rather than investigating false positives.
Pro Tip: When implementing AI enhanced detection, maintain human oversight for high impact decisions. AI excels at pattern recognition and rapid analysis, but experienced analysts provide contextual judgment about business impact, appropriate response measures, and communication strategies.
Successful optimization requires balancing technology investment with team development. Provide ongoing training in emerging threats and attack techniques, create opportunities for analysts to pursue relevant certifications, and foster collaboration between technical staff and compliance experts. This investment builds organizational capability that persists beyond any single technology solution.
Measuring Incident Response Effectiveness: Metrics and Benchmarks
Executives need quantifiable metrics to evaluate incident response performance, justify investments, and drive continuous improvement. Several key indicators provide insight into team effectiveness and compliance readiness.
| Metric | Target | Strategic Importance |
|---|---|---|
| Mean Time to Detect | Under 24 hours | Early detection limits breach scope and reduces impact |
| Mean Time to Contain | Under 8 hours | Rapid containment prevents lateral movement and data exfiltration |
| Breach Notification Compliance | 100% on time | Avoids regulatory penalties and demonstrates governance maturity |
| Detection Accuracy | Above 85% | Balances threat identification with manageable false positive rates |
| Cost Per Incident | Decreasing trend | Indicates improving efficiency and process maturity |
Incident containment time measures how quickly teams isolate compromised systems to prevent threat spread. Industry benchmarks suggest elite performers achieve containment within 6 hours, while average organizations require 48 hours or more. This dramatic difference directly correlates with breach severity, as faster containment limits data exposure and system compromise.
Breach notification compliance rates reveal governance maturity. Organizations with formal IR teams reduce delayed notifications from 45% to 12%, demonstrating the compliance value of structured response capabilities. Track both timeliness and notification accuracy, as incomplete or inaccurate disclosures trigger regulatory scrutiny even when submitted on time.
Detection accuracy encompasses both true positive rates and false positive management. AI enhanced systems achieve 28% improvement in identifying genuine threats while reducing false alerts that waste analyst time. Monitor this metric quarterly to assess whether detection system tuning maintains appropriate balance between sensitivity and specificity.
Benchmarking against industry peers provides context for evaluating performance. Participate in information sharing groups, review published research on healthcare cybersecurity metrics, and engage with industry associations that compile anonymized performance data. This external perspective helps identify improvement opportunities and validate investment decisions.
Regular metric review sessions with executive leadership ensure IR performance remains visible at strategic levels. Present trends over time rather than point in time snapshots, highlight improvements resulting from specific investments, and connect metrics to business outcomes like reduced breach costs or improved audit results. This communication reinforces IR's strategic value and maintains executive support for ongoing capability development.
Integrating Incident Response with Risk Management and Compliance
Incident response capabilities deliver maximum value when embedded within enterprise risk management frameworks rather than operating as standalone security functions. This integration creates feedback loops where IR intelligence informs risk assessments, risk priorities guide IR investments, and compliance requirements shape response procedures.
Embedding IR in risk management frameworks improves breach notification outcomes and compliance with HIPAA, HITRUST, and SOC 2. Organizations achieving this integration report fewer compliance gaps, faster regulatory response, and better alignment between security investments and business priorities.
Practical integration requires several organizational changes. Establish regular reporting from IR teams to enterprise risk committees, include IR leaders in strategic planning discussions about new services or technology adoption, and ensure risk assessments incorporate threat intelligence from incident investigations. This bidirectional information flow ensures both functions benefit from shared knowledge.
Compliance integration extends beyond HIPAA to encompass multiple frameworks relevant to healthcare operations:
- HITRUST CSF: Aligns incident response procedures with comprehensive control framework
- SOC 2: Demonstrates incident management capabilities to business partners requiring attestation
- State Breach Laws: Ensures response procedures address varying notification requirements
- Cyber Insurance Requirements: Satisfies policy conditions regarding incident handling and documentation
Business continuity planning represents another critical integration point. IR teams provide realistic scenarios for continuity exercises, participate in disaster recovery testing, and ensure security considerations inform continuity strategies. When organizations treat IR and business continuity as separate functions, they discover coordination gaps during actual incidents when rapid collaboration proves essential.
Data protection strategies benefit from IR involvement throughout the lifecycle. Incident investigations reveal where sensitive data exists outside expected locations, which controls prove effective under attack conditions, and what data recovery capabilities require enhancement. Feed these insights back into data governance programs to strengthen protection measures proactively.
Audit readiness improves substantially when IR integrates with compliance functions. Incident documentation created during response becomes evidence of control effectiveness, response metrics demonstrate governance maturity, and lessons learned drive continuous improvement visible to auditors. Organizations presenting this integrated approach receive more favorable audit outcomes than peers treating IR as purely operational.
Case Studies: Successful Incident Response in U.S. Healthcare
Real world examples illustrate the measurable benefits healthcare organizations achieve through optimized incident response capabilities. These cases demonstrate both financial impact and compliance improvements resulting from strategic IR investments.
A 400 bed hospital system in the Midwest reduced response times from 48 hours to 6 hours after implementing AI augmented detection and dedicated IR staffing. When ransomware infected several systems, the enhanced capabilities enabled rapid containment limiting impact to two departments rather than enterprise wide disruption. The organization maintained emergency department operations throughout the incident, preserving patient care capacity and revenue streams.
Financial analysis revealed the active incident response approach cut breach costs by over $1 million compared to projected impact under previous reactive capabilities. Cost savings came from reduced downtime, limited data exposure requiring fewer patient notifications, and avoided regulatory penalties through timely breach reporting. Executive leadership cited this incident as validation for continued IR investment.
A regional healthcare network serving rural communities faced compliance challenges around breach notification deadlines. After restructuring their IR team to include dedicated compliance specialists, notification timeliness improved from 67% on time to 98% on time. This transformation avoided penalties that plagued previous years and improved relationships with state regulators who noted the organization's governance maturity.
The compliance focused IR model integrated legal review into initial breach assessment, streamlined coordination with external counsel, and created templates for various notification scenarios. These process improvements reduced administrative burden while ensuring regulatory accuracy. The organization now serves as a regional resource helping smaller healthcare providers improve their own incident response capabilities.
These examples share common themes: executive support for IR investment, integration of technical and compliance expertise, adoption of proactive rather than reactive approaches, and commitment to continuous improvement based on metrics and lessons learned. Organizations achieving similar results treat incident response as a strategic capability rather than operational overhead.
Strategic Recommendations and Next Steps for Healthcare Executives
C level executives and CISOs can take specific actions to build and optimize incident response capabilities that reduce risk, enhance compliance, and align with business objectives. These recommendations provide a roadmap for transforming IR from reactive necessity to strategic advantage.
- Establish Well Defined IR Team Structures with Clear Governance
Designate specific roles for technical response, compliance management, and communication functions. Document decision authority for containment actions that impact operations. Create escalation protocols ensuring appropriate executive involvement without micromanaging technical response. This clarity prevents confusion during high pressure incidents when rapid decisions prove essential.
- Align IR with HIPAA, HITECH, and Risk Management Frameworks
Map incident response procedures to regulatory requirements, ensuring each compliance obligation has corresponding process steps. Integrate IR with enterprise risk management through regular reporting and shared metrics. Participate in healthcare risk assessment processes that inform both IR priorities and broader security strategy.
- Incorporate AI and Proactive Threat Hunting Tools
Invest in AI enhanced detection platforms that reduce false positives while improving threat identification. Dedicate analyst time to proactive hunting rather than purely reactive alert investigation. Balance automation with human expertise, using AI to augment rather than replace skilled professionals.
- Embed IR into Enterprise Risk and Business Continuity Planning
Include IR leaders in strategic planning discussions about new services, technology adoption, and operational changes. Ensure business continuity exercises incorporate realistic cyber incident scenarios. Create feedback loops where incident lessons learned inform risk assessments and continuity strategies.
Pro Tip: Schedule annual reviews of IR capabilities using external experts who provide objective assessment against industry benchmarks. This outside perspective identifies blind spots internal teams miss and validates improvements to executive leadership.
Implementation requires sustained commitment beyond initial capability building. Budget for ongoing training, technology updates, and process refinement. Celebrate successes when metrics improve or incidents are handled effectively, reinforcing organizational recognition of IR's strategic value. Track how investments translate to measurable outcomes like reduced breach costs or improved compliance rates.
Enhance Your Healthcare Cybersecurity with Heights Consulting Group

Building effective incident response capabilities requires specialized expertise spanning technical cybersecurity, healthcare compliance, and risk management. Heights Consulting Group helps healthcare organizations build effective incident response teams that reduce breach costs while ensuring regulatory compliance.
Our consultants bring deep experience optimizing IR capabilities for healthcare environments. We align response procedures with HIPAA and HITECH requirements, integrate AI enhanced detection that improves accuracy, and embed incident response within enterprise risk frameworks. Organizations working with Heights Consulting Group transform cybersecurity challenges into strategic business opportunities that protect patient data while supporting operational objectives.
Whether you need comprehensive IR program development or targeted enhancements to existing capabilities, our team provides strategic guidance tailored to your organizational context. Contact Heights Consulting Group to discuss how we can help optimize your incident response capabilities for 2026's evolving threat landscape.
Frequently Asked Questions About Incident Response Teams in Healthcare
What regulatory frameworks impact healthcare incident response teams?
HIPAA's breach notification rule requires assessment and reporting within specific timeframes. The HITECH Act imposes penalties for delayed notifications. State breach notification laws add varying requirements depending on patient location. HITRUST CSF and SOC 2 frameworks also shape IR procedures for organizations pursuing certification.
How does AI improve incident response detection accuracy?
AI analyzes massive datasets identifying subtle attack patterns humans miss. Machine learning correlates indicators across multiple sources, prioritizes alerts based on actual risk, and reduces false positives by 30% or more. This allows analysts to focus expertise on genuine threats rather than investigating benign anomalies.
What are the key metrics to evaluate IR team effectiveness?
Track mean time to detect threats, mean time to contain incidents, breach notification compliance rates, and detection accuracy. Monitor cost per incident to assess efficiency improvements. Compare performance against industry benchmarks to identify gaps and validate investments.
How do incident response teams reduce financial and reputational risks?
Faster containment limits breach scope, reducing notification costs and regulatory penalties. Effective compliance management avoids delayed reporting that triggers enhanced scrutiny. Coordinated communication during incidents protects organizational reputation. These capabilities translate to measurable cost savings averaging $1.2 million per breach.
What steps can executives take to integrate IR into enterprise risk management?
Include IR leaders in risk committee meetings and strategic planning discussions. Ensure threat intelligence from incidents informs risk assessments. Create reporting structures where IR metrics reach executive leadership regularly. Embed incident response considerations in business continuity planning and new initiative evaluation.
Should healthcare organizations build internal IR teams or outsource capabilities?
The optimal approach depends on organizational size, risk profile, and resource availability. Large systems benefit from internal teams with deep institutional knowledge. Smaller organizations may achieve better results through managed services or hybrid models. Many organizations start with external support while building internal expertise over time.
