Every CISO knows the pressure of shaping a cybersecurity program that satisfies both stringent regulations and real business needs. The NIST Cybersecurity Framework stands out by offering a structured path for U.S. organizations to manage risks, protect critical assets, and document compliance efforts. By applying evidence-based risk assessment and continuous control mapping, security leaders in American healthcare and other regulated sectors can meet audit requirements while reducing exposure to threats.
Table of Contents
- Step 1: Assess Organizational Risks And Business Needs
- Step 2: Map Existing Controls To NIST Framework Functions
- Step 3: Develop And Document Your Customized NIST Roadmap
- Step 4: Execute Framework Controls And Monitor Implementation
- Step 5: Verify Compliance And Optimize Ongoing Performance
Quick Summary
| Essential Insight | Detailed Explanation |
|---|---|
| 1. Conduct a thorough risk assessment | Understanding your organization’s unique cybersecurity landscape helps in identifying critical assets and vulnerabilities effectively. |
| 2. Map controls to NIST framework | Aligning existing security measures with NIST functions enhances understanding of risk management and identifies improvement areas. |
| 3. Develop a customized NIST roadmap | A tailored roadmap guides organizations in improving cybersecurity processes and aligning them with strategic objectives. |
| 4. Execute and monitor control implementation | Proper execution and ongoing monitoring of security controls ensure that cybersecurity strategies remain effective and compliant. |
| 5. Verify compliance and optimize performance | Regular audits and assessments help in maintaining security effectiveness and adapting to emerging threats continually. |
Step 1: Assess organizational risks and business needs
Effective risk management begins with a comprehensive understanding of your organization's unique cybersecurity landscape. The NIST Cybersecurity Framework provides a structured approach to identifying organizational assets and risks.
To conduct a thorough organizational risk assessment, focus on these critical areas:
- Inventory critical assets: Catalog all hardware, software, data systems, and network infrastructure
- Identify potential vulnerabilities: Analyze existing security gaps across your technology ecosystem
- Evaluate business impact: Determine potential financial and operational consequences of cybersecurity incidents
- Understand regulatory requirements: Map compliance needs specific to your industry
The assessment process requires cross-functional collaboration, involving leadership from IT, security, legal, and business strategy teams. Your goal is developing a holistic view of organizational risk that aligns technical capabilities with strategic business objectives.
A comprehensive risk assessment is not a one-time event but a continuous, evolving process that adapts to changing technological landscapes.
Pro tip: Develop a standardized risk assessment template that can be regularly updated and provides consistent evaluation criteria across your organization.

Step 2: Map existing controls to NIST framework functions
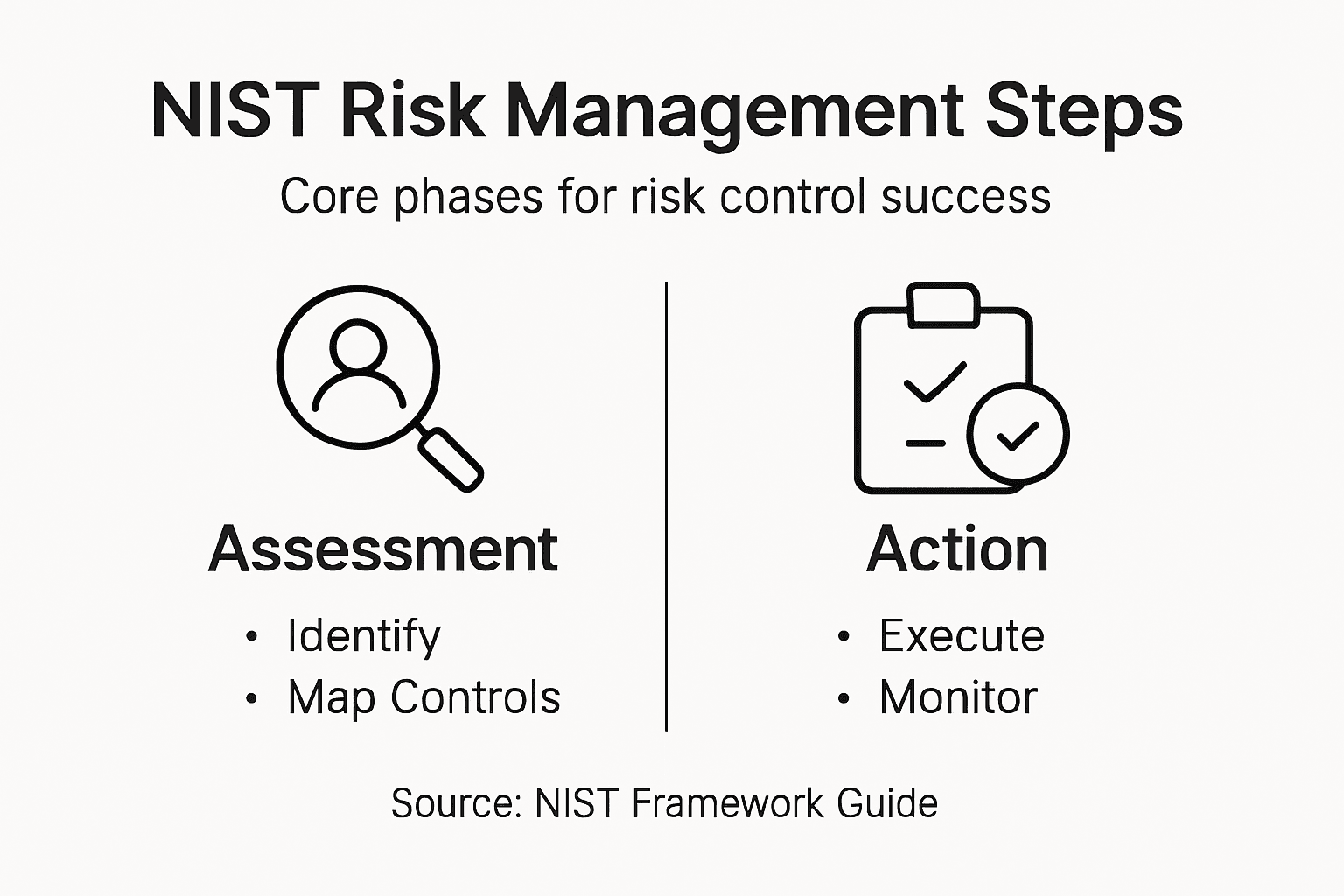
Navigating the complex landscape of cybersecurity controls requires a systematic approach to mapping organizational safeguards across the NIST Cybersecurity Framework's core functions: Govern, Identify, Protect, Detect, Respond, and Recover.
To effectively map your existing controls, follow these strategic steps:
- Document current controls: Create a comprehensive inventory of your existing security mechanisms
- Align with NIST functions: Match each control to the corresponding framework function
- Identify gaps: Highlight areas where current controls do not fully address framework requirements
- Prioritize improvements: Develop a roadmap for enhancing cybersecurity capabilities
Key areas to focus on during mapping include:
- Governance controls: Ensure leadership oversight and strategic alignment
- Asset management: Catalog and track all hardware, software, and data systems
- Access control: Review authentication and authorization mechanisms
- Incident response: Evaluate preparedness for detecting and responding to security events
Effective control mapping is not about perfect alignment, but continuous improvement and risk reduction.
Pro tip: Use automated mapping tools and conduct periodic reviews to maintain an up-to-date and comprehensive control landscape.
Here's a summary of how each NIST function influences business resilience:
| NIST Function | Primary Focus | Business Impact |
|---|---|---|
| Govern | Strategic oversight | Aligns security with business goals |
| Identify | Asset discovery | Reduces unknown risks |
| Protect | Preventive controls | Minimizes incident likelihood |
| Detect | Threat recognition | Enables rapid response |
| Respond | Incident management | Mitigates damage and downtime |
| Recover | Restoration planning | Accelerates business continuity |
Step 3: Develop and document your customized NIST roadmap
Creating a robust cybersecurity roadmap requires strategic planning and alignment with your organization's unique risk landscape. The NIST framework provides organizational profiles for targeted implementation that help translate broad guidelines into actionable strategies.
To develop a comprehensive roadmap, focus on these key components:
- Current state assessment: Document existing cybersecurity capabilities and maturity levels
- Target state definition: Establish clear cybersecurity objectives and desired outcomes
- Gap analysis: Identify specific areas requiring improvement or additional controls
- Resource allocation: Determine budget, personnel, and technological investments needed
Your roadmap should include detailed documentation that addresses:
- Governance structure: Define roles, responsibilities, and decision-making processes
- Risk prioritization: Rank potential threats based on potential business impact
- Implementation timeline: Create phased approach for control enhancement
- Performance metrics: Establish measurable indicators of cybersecurity effectiveness
A well-crafted roadmap transforms cybersecurity from a technical requirement into a strategic business enabler.
Pro tip: Regularly review and update your roadmap to ensure continuous alignment with evolving business objectives and emerging cybersecurity threats.
For clarity, here's a reference for cybersecurity maturity stages and their typical characteristics:
| Maturity Stage | Key Characteristics | Organizational Advantages |
|---|---|---|
| Initial | Ad-hoc controls | Vulnerable to threats |
| Defined | Formal policies | Improved compliance and consistency |
| Managed | Measured effectiveness | Predictable performance and reliability |
| Optimized | Continuous improvement | Agile response to new risks |
Step 4: Execute framework controls and monitor implementation
Successful cybersecurity implementation demands meticulous execution and continuous oversight. Organizations can leverage systematic control monitoring approaches to ensure ongoing effectiveness and compliance with established security protocols.
Key strategies for executing and monitoring framework controls include:
- Systematic deployment: Implement controls consistently across all organizational systems
- Documentation: Maintain detailed records of control implementation and configuration
- Performance tracking: Establish metrics to measure control effectiveness
- Incident response preparation: Develop mechanisms for rapid detection and mitigation
Critical implementation activities involve:
- Configuration management: Standardize control settings across technology infrastructure
- Access control verification: Validate user permissions and authentication mechanisms
- Security testing: Conduct regular vulnerability assessments and penetration testing
- Compliance validation: Ensure alignment with industry regulations and framework requirements
Effective control execution transforms theoretical security frameworks into practical, actionable defense strategies.
Pro tip: Implement automated monitoring tools that provide real-time insights into control performance and potential security vulnerabilities.
Step 5: Verify compliance and optimize ongoing performance
Ensuring long-term cybersecurity effectiveness requires rigorous and continuous validation of your framework's implementation. Organizations can achieve this by implementing comprehensive assessment strategies that provide actionable insights into their security posture.
Key strategies for verification and optimization include:
- Performance metrics: Develop quantitative measurements of control effectiveness
- Regular audits: Conduct periodic comprehensive security assessments
- Gap analysis: Identify and address emerging vulnerabilities
- Continuous improvement: Create mechanisms for adaptive security enhancement
Critical verification activities involve:
- Quantitative reporting: Generate detailed performance dashboards
- Executive briefings: Communicate cybersecurity status to leadership
- Benchmarking: Compare performance against industry standards
- Risk reassessment: Dynamically update risk management strategies
Compliance verification is not a destination but a continuous journey of security refinement and organizational resilience.
Pro tip: Implement automated compliance monitoring tools that provide real-time insights and generate comprehensive reports with minimal manual intervention.
Strengthen Your Risk Management with Expert NIST Framework Implementation
Navigating the complexities of the NIST Cybersecurity Framework is a critical challenge for organizations seeking to align security with business goals, manage risks effectively, and ensure regulatory compliance. If you struggle with identifying gaps in your current controls, developing a clear cybersecurity roadmap, or maintaining continuous oversight, you are not alone. Many security leaders face difficulty in transforming the NIST framework from a theoretical guide into an actionable strategy that protects critical assets and supports business resilience.
Heights Consulting Group specializes in turning these challenges into opportunities. Our seasoned experts provide strategic guidance and technical services tailored to your organization's unique risk profile. We help you assess risks, map controls to the NIST framework, execute security measures, and monitor compliance — all while embedding cybersecurity within your core business strategies. Discover how our comprehensive solutions like managed cybersecurity, incident response, and compliance frameworks can elevate your security posture today by visiting Heights Consulting Group.
Elevate your cybersecurity from a requirement to a competitive advantage. Get started now with professional consultation at Heights Consulting Group and explore our full range of services to ensure your NIST roadmap drives real business value.

Ready to overcome risk management challenges and safeguard your organization? Contact Heights Consulting Group today for a customized strategy that ensures effective implementation and optimization of the NIST Cybersecurity Framework.
Frequently Asked Questions
How do I start assessing my organization's cybersecurity risks using the NIST Framework?
To begin assessing your organization's cybersecurity risks, inventory all critical assets, identify potential vulnerabilities, and evaluate the business impact of cybersecurity incidents. Take action by creating a detailed list of your hardware, software, and data systems within the next 30 days to gain clarity on your risk landscape.
What are the core functions of the NIST Cybersecurity Framework I need to map my existing controls to?
The core functions of the NIST Cybersecurity Framework are Govern, Identify, Protect, Detect, Respond, and Recover. Start by documenting your current security controls and aligning them with these functions to identify gaps and prioritize improvements over the next quarter.
How can I develop a custom cybersecurity roadmap using the NIST Framework?
To develop a custom cybersecurity roadmap, begin with a current state assessment, define your target state, and conduct a gap analysis. Formulate an initial roadmap draft within 60 days that outlines key objectives, necessary controls, and a resource allocation plan.
What steps should I follow to verify compliance with the NIST Framework once implemented?
To verify compliance, establish performance metrics, conduct regular audits, and perform continuous assessments of your security measures. Take action by planning your first comprehensive audit within the next 90 days to ensure that your security practices align with the NIST Framework's requirements.
How often should I update my risk management assessment according to the NIST Framework?
You should update your risk management assessment continuously as your organizational landscape and cybersecurity threats evolve. Implement a schedule for regular assessments, ideally every six months, to ensure your cybersecurity measures remain effective and relevant.
Recommended
- Your Guide to Cybersecurity Risk Assessment Frameworks - Heights Consulting Group
- Your Guide to a Modern Risk Governance Framework - Heights Consulting Group
- A Guide to Cybersecurity Risk Management Frameworks - Heights Consulting Group
- Your Guide to a Cyber Risk Assessment Framework - Heights Consulting Group
- Confidential Waste Risk Management: Essential Guide for UK Businesses 2025 - Venture Waste