Most American healthcare organizations face rising cyber threats and intense scrutiny from regulators. A single data breach can cost millions, and the healthcare sector consistently reports the highest average breach costs of any industry. For CISOs and IT security managers, building strong security governance is not just about checklists but about protecting sensitive patient data, supporting business goals, and staying confidently compliant. This guide lays out practical steps to make security an integrated advantage for your American healthcare organization.
Table of Contents
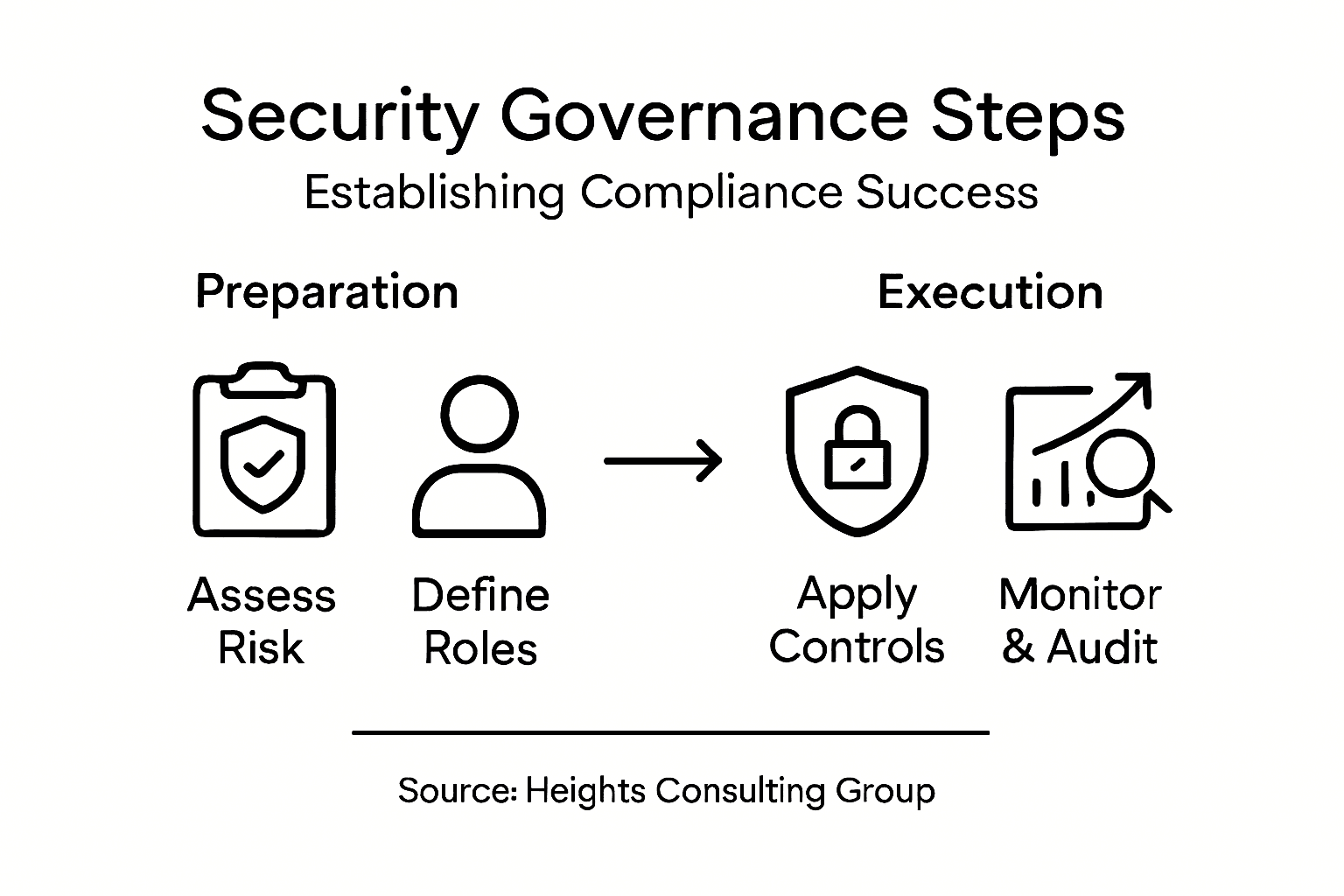
- Step 1: Assess Organizational Risk And Compliance Requirements
- Step 2: Define Governance Structure And Stakeholder Roles
- Step 3: Implement Security Policies And Technical Controls
- Step 4: Integrate Governance Into Business Operations
- Step 5: Verify Effectiveness Through Monitoring And Audits
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Conduct a comprehensive risk assessment | Evaluate your organization's security and compliance needs to identify vulnerabilities. |
| 2. Establish a clear governance structure | Define roles and responsibilities for stakeholders to enhance security oversight. |
| 3. Develop tailored security policies | Create policies that align with regulatory requirements and protect sensitive data. |
| 4. Integrate compliance into daily operations | Make risk management a fundamental part of all business processes. |
| 5. Implement effective monitoring and audits | Use varied assessment methods to maintain and improve security governance. |
Step 1: Assess organizational risk and compliance requirements
Establishing robust security governance requires a systematic approach to understanding your organization's unique risk landscape and compliance obligations. Your initial goal is to comprehensively map out potential cybersecurity vulnerabilities and regulatory requirements specific to your healthcare environment.
Begin by conducting a detailed comprehensive risk assessment that evaluates your current security infrastructure, data handling practices, and potential threat vectors. This process involves gathering input from multiple departments including IT, legal, human resources, and executive leadership to create a holistic view of organizational risks. Healthcare organizations must pay special attention to protected health information (PHI) regulations, mapping out potential scenarios where sensitive patient data could be compromised.
Your risk assessment should categorize potential threats based on likelihood and potential impact, creating a prioritized risk registry that enables targeted mitigation strategies. Consider factors like data sensitivity, system interconnectivity, third party vendor relationships, and historical breach patterns. Utilize frameworks like NIST and HIPAA as foundational guidelines, but customize your approach to your specific organizational context.
Pro Tip: Conduct your risk assessment as an iterative process, scheduling regular reviews every six months to ensure your compliance strategy remains adaptive to emerging cybersecurity threats and regulatory changes.
Step 2: Define governance structure and stakeholder roles
Establishing a clear governance structure is critical for transforming security compliance from a technical requirement into a strategic organizational capability. Your objective is to create a well-defined framework that precisely outlines responsibilities, accountability, and decision making authority across different levels of your healthcare organization.
Begin by implementing a comprehensive risk governance framework that identifies key stakeholders and their specific roles in managing cybersecurity risks. This typically involves creating a multilayered structure that includes board level oversight, executive leadership, operational management, and technical implementation teams. In a healthcare context, this means engaging your Chief Information Security Officer (CISO), compliance officers, IT directors, department heads, and clinical leaders to ensure a holistic approach to security governance.
Document each stakeholders responsibilities with clear performance metrics and reporting requirements. Your governance model should include mechanisms for regular communication, escalation protocols for identified risks, and a structured approach to decision making. Ensure that roles are not just defined on paper but actively maintained through ongoing training, periodic reviews, and accountability measures.
Pro Tip: Create a governance responsibility matrix that visually maps each stakeholders specific duties, authority levels, and communication channels to eliminate ambiguity and promote organizational alignment.
Here is a summary of common stakeholder roles in healthcare security governance:
| Stakeholder | Primary Responsibility | Typical Impact |
|---|---|---|
| Board of Directors | Oversight and strategic direction | Ensures enterprise alignment |
| Executive Leadership | Policy approval, resource allocation | Drives adoption and culture |
| Chief Information Security Officer (CISO) | Security program leadership | Implements security vision |
| IT Department | Technical safeguards, daily support | Maintains system integrity |
| Compliance Officer | Regulatory interpretation, audits | Maintains legal compliance |
| Department Heads | Department-level implementation | Applies controls effectively |
| Clinical Leaders | Data stewardship, process input | Bridges care and security |
Step 3: Implement security policies and technical controls
Transforming your security governance strategy into actionable policies and technical controls requires a systematic and comprehensive approach tailored to your healthcare organizations unique risk profile. Your goal is to develop a robust framework that protects sensitive patient information while maintaining operational efficiency.
Start by developing comprehensive risk management practices that align technical controls with organizational objectives and regulatory requirements. This involves creating detailed security policies that address critical areas such as data protection, access management, network security, incident response, and employee training. For healthcare organizations, these policies must specifically address Protected Health Information (PHI) regulations, ensuring compliance with HIPAA and other industry specific standards.
Implement technical controls that provide multiple layers of protection across your digital infrastructure. This includes deploying advanced endpoint protection, implementing multifactor authentication, establishing encryption protocols for data at rest and in transit, and creating segmented network architectures that limit potential breach impacts. Regularly test and validate these controls through penetration testing, vulnerability assessments, and continuous monitoring systems that can detect and respond to potential security incidents in real time.
Pro Tip: Develop a living document approach to your security policies, scheduling quarterly reviews and updates to ensure they remain adaptive to emerging technological threats and evolving regulatory landscapes.
The following table compares key compliance and security frameworks relevant to healthcare organizations:
| Framework | Focus Area | Applicability |
|---|---|---|
| NIST | Cybersecurity best practices | General industry, adaptable |
| HIPAA | Patient data privacy | U.S. healthcare specific |
| ISO 27001 | Information security controls | International standard |
| COSO ERM | Enterprise risk management | Broad business risk frameworks |
Step 4: Integrate governance into business operations
Transforming security governance from an isolated technical function to a strategic business capability requires deliberate and systematic integration across your entire healthcare organization. Your mission is to embed compliance and risk management principles deeply into everyday operational processes and decision making frameworks.

Start by embedding risk management practices into core business processes, ensuring that compliance considerations are not an afterthought but a fundamental component of strategic planning. This means creating mechanisms where security governance becomes intrinsic to departmental workflows, from clinical operations to administrative functions. Develop cross functional committees that include representatives from IT, clinical leadership, legal departments, and executive management to promote a unified approach to risk and compliance.
Create training programs and communication channels that consistently reinforce the importance of security governance across all organizational levels. Implement performance metrics and accountability mechanisms that incentivize proactive risk management and compliance adherence. Your goal is to cultivate a culture where every employee understands their role in maintaining organizational security, transforming compliance from a regulatory requirement into a shared organizational value.
Pro Tip: Develop a quarterly governance review process that maps security initiatives directly to business objectives, demonstrating the strategic value of your compliance efforts to senior leadership.
Step 5: Verify effectiveness through monitoring and audits
Verifying the effectiveness of your security governance framework requires a systematic and rigorous approach to monitoring, assessment, and continuous improvement. Your objective is to transform compliance from a static checkpoint into a dynamic, adaptive process that proactively identifies and addresses potential vulnerabilities.
Begin by implementing comprehensive audit approaches that go beyond traditional checklist methodologies. This means developing a multifaceted monitoring strategy that combines automated technical assessments, periodic manual audits, and real time performance tracking. For healthcare organizations, this involves creating specialized audit protocols that examine security controls across clinical systems, administrative networks, and patient data management platforms.
Establish key performance indicators (KPIs) and metrics that provide meaningful insights into your governance effectiveness. These should include quantitative measures like compliance rates, incident response times, and control effectiveness, as well as qualitative assessments of organizational security culture. Develop a reporting mechanism that provides transparent, actionable intelligence to executive leadership, enabling data driven decision making and continuous improvement of your security governance framework.
Pro Tip: Create a quarterly risk assessment dashboard that translates complex technical metrics into clear, business focused insights that demonstrate the strategic value of your security governance efforts.
Strengthen Your Security Governance With Expert Cybersecurity Partners
Establishing effective security governance is vital for your organization to succeed in today’s complex compliance landscape. The challenge lies in managing risk, defining clear stakeholder roles, and integrating security policies seamlessly into daily operations while staying ahead of evolving threats. If you aim to transform your security governance into a strategic business advantage, you need tailored solutions that align cybersecurity with your organizational goals.
Heights Consulting Group offers comprehensive cybersecurity advisory and technical services designed to help organizations like yours build resilient compliance frameworks based on industry standards such as NIST and HIPAA. Our expertise in risk management, incident response, and endpoint protection empowers C-level executives and security leaders to embed security deeply into business processes, ensuring continuous monitoring and effective governance.
Discover how our compliance solutions can enhance your security governance strategy and protect your critical data with practical, adaptive controls.

Ready to move beyond basic compliance and turn security governance into your competitive edge? Connect with us today at Heights Consulting Group to start building a robust, risk-aware cybersecurity posture that supports your organization’s long-term success.
Frequently Asked Questions
How can I assess my organization's risk and compliance requirements for security governance?
To assess your organization's risk and compliance requirements, conduct a detailed risk assessment that maps potential cybersecurity vulnerabilities and regulatory obligations. Gather input from departments like IT, legal, and human resources to create a comprehensive view of your risks within 30 days.
What roles should be included in a security governance structure for compliance success?
Include key stakeholders such as the Chief Information Security Officer (CISO), compliance officers, IT directors, and department heads in your security governance structure. Document their specific responsibilities and establish clear communication channels to promote accountability and effectiveness.
How do I implement security policies and technical controls in my organization?
Begin by developing comprehensive security policies that align with organizational objectives and compliance regulations. Focus on areas like data protection, access management, and employee training, and ensure these policies are regularly updated every quarter.
What steps should I take to integrate security governance into business operations?
Integrate security governance by embedding risk management practices into everyday workflows and strategic planning processes. Create cross-functional committees that include representatives from various departments to foster a unified approach to compliance and risk management.
How can I verify the effectiveness of my security governance framework?
To verify the effectiveness of your security governance framework, implement a multifaceted monitoring strategy that includes automated assessments and periodic audits. Establish key performance indicators (KPIs) that provide insights into compliance rates and incident response times, and review these metrics quarterly to drive continuous improvement.
Recommended
- Boardroom Cybersecurity: Heights CG's Strategic Governance
- Your Guide to a Modern Risk Governance Framework - Heights Consulting Group
- Unlocking the Hidden Value of Compliance in Business Growth - Heights Consulting Group
- Mastering Regulatory Compliance: Confidence and Clarity for Executive Leaders - Heights Consulting Group
