Over 60 percent of American organizations say keeping up with compliance standards puts major pressure on their IT and security teams. Meeting SOC 2 requirements can feel daunting, especially when each step demands detailed documentation and coordination across multiple departments. By understanding how to assess your controls, define your scope, and gather watertight evidence, you will be better prepared for a successful audit and lasting trust with your clients.
Table of Contents
- Step 1: Assess Current Controls And Identify Gaps
- Step 2: Define SOC 2 Trust Service Criteria And Scope
- Step 3: Implement Required Security And Compliance Processes
- Step 4: Document Evidence And Prepare For Audit
- Step 5: Conduct Internal Review And Address Deficiencies
- Step 6: Engage A SOC 2 Auditor For Final Certification
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Conduct a thorough gap analysis | Assess your current security controls against SOC 2 criteria to identify vulnerabilities and strengths. |
| 2. Define relevant Trust Services Criteria | Select specific criteria that align with your organization’s risk landscape for targeted compliance efforts. |
| 3. Develop actionable security processes | Create detailed, practical security policies that all employees can implement and follow effectively. |
| 4. Systematically document for audit | Maintain comprehensive logs and evidence of control implementation to facilitate the audit process. |
| 5. Perform an internal review before audit | Conduct a mock audit to identify and address deficiencies proactively, ensuring stronger compliance readiness. |
Step 1: Assess current controls and identify gaps
Achieving SOC 2 compliance requires a strategic and comprehensive evaluation of your organization's existing security controls. Your goal in this critical initial phase is to perform a thorough gap analysis that pinpoints exactly where your current cybersecurity infrastructure meets or falls short of the Trust Services Criteria.
Start by assembling a cross functional team including representatives from IT, security, compliance, and executive leadership. Systematically review your current security policies, technical controls, and operational procedures against the five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. Document each control's current state, identifying specific strengths and potential vulnerabilities. This detailed mapping will help you understand the precise gaps between your existing infrastructure and SOC 2 requirements.
Pay special attention to access management, data protection mechanisms, incident response protocols, and third party vendor risk management. Create a comprehensive gap assessment report that not only highlights deficiencies but also recommends specific remediation strategies. Prioritize these recommendations based on potential risk impact and resource requirements.
Pro tip: Create a color coded tracking spreadsheet that visually maps your control maturity across each Trust Services Criteria, allowing quick identification of high priority improvement areas and enabling more strategic resource allocation.
Step 2: Define SOC 2 trust service criteria and scope
Defining SOC 2 trust service criteria and scope is a critical foundation for your compliance journey. Your objective is to understand and strategically select the most relevant Trust Services Criteria framework that align with your organization's specific operational requirements and risk landscape.

The SOC 2 framework encompasses five primary Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. Your task is to carefully evaluate which criteria are most pertinent to your business context. This evaluation requires a nuanced understanding of your data handling practices, system architecture, and regulatory environment. Not every organization will need to address all five criteria equally some may focus on one or two core areas that represent their most significant risk exposure.
Begin by conducting a comprehensive internal assessment of your current systems and data management processes. Engage key stakeholders from IT, security, compliance, and executive leadership to collaboratively determine the most appropriate scope. Document your rationale for selecting specific criteria, ensuring that your approach reflects a strategic and risk informed decision making process. Your goal is to create a tailored compliance strategy that provides meaningful assurance to stakeholders while efficiently addressing your most critical security and operational requirements.
Pro tip: Create a decision matrix that maps each Trust Services Criteria against your specific business objectives, enabling a clear visualization of which criteria offer the most strategic value for your organization.
Here's a comparison of the five Trust Services Criteria and their business relevance:
| Criteria | Core Focus Area | Typical Business Impact |
|---|---|---|
| Security | Protecting system access | Prevents data breaches and disruptions |
| Availability | System uptime | Ensures reliability for users |
| Processing Integrity | Data accuracy | Maintains trustworthy operations |
| Confidentiality | Data secrecy | Reduces risk of information leaks |
| Privacy | Personal data protection | Builds customer and regulatory trust |
Step 3: Implement required security and compliance processes
Implementing SOC 2 security and compliance processes is a critical transformation of your organizational framework. Your primary objective is to develop comprehensive security controls that systematically address the Trust Services Criteria you previously identified.
Start by drafting detailed security policies and procedural documentation that explicitly outline your organization's approach to data protection, access management, system monitoring, and incident response. These documents must be more than theoretical statements they need to be actionable blueprints that every team member can understand and implement. Focus on creating clear protocols for authentication, data encryption, network security, vendor management, and employee training. Each policy should include specific implementation guidelines, responsibility assignments, and mechanisms for ongoing monitoring and enforcement.
Work closely with stakeholders from IT, security, legal, and operations to ensure these processes are not only compliant but also practical and integrated into your existing workflows. Develop robust change management procedures that allow for periodic review and updates of your security controls. Implement technical controls such as multi factor authentication, encryption protocols, access logging, and continuous vulnerability scanning. Document every process meticulously, as this documentation will be crucial during your eventual SOC 2 audit.
Pro tip: Create a living compliance playbook that serves as a single source of truth for your security processes, making it easy to train new employees and demonstrate your commitment to rigorous security standards.
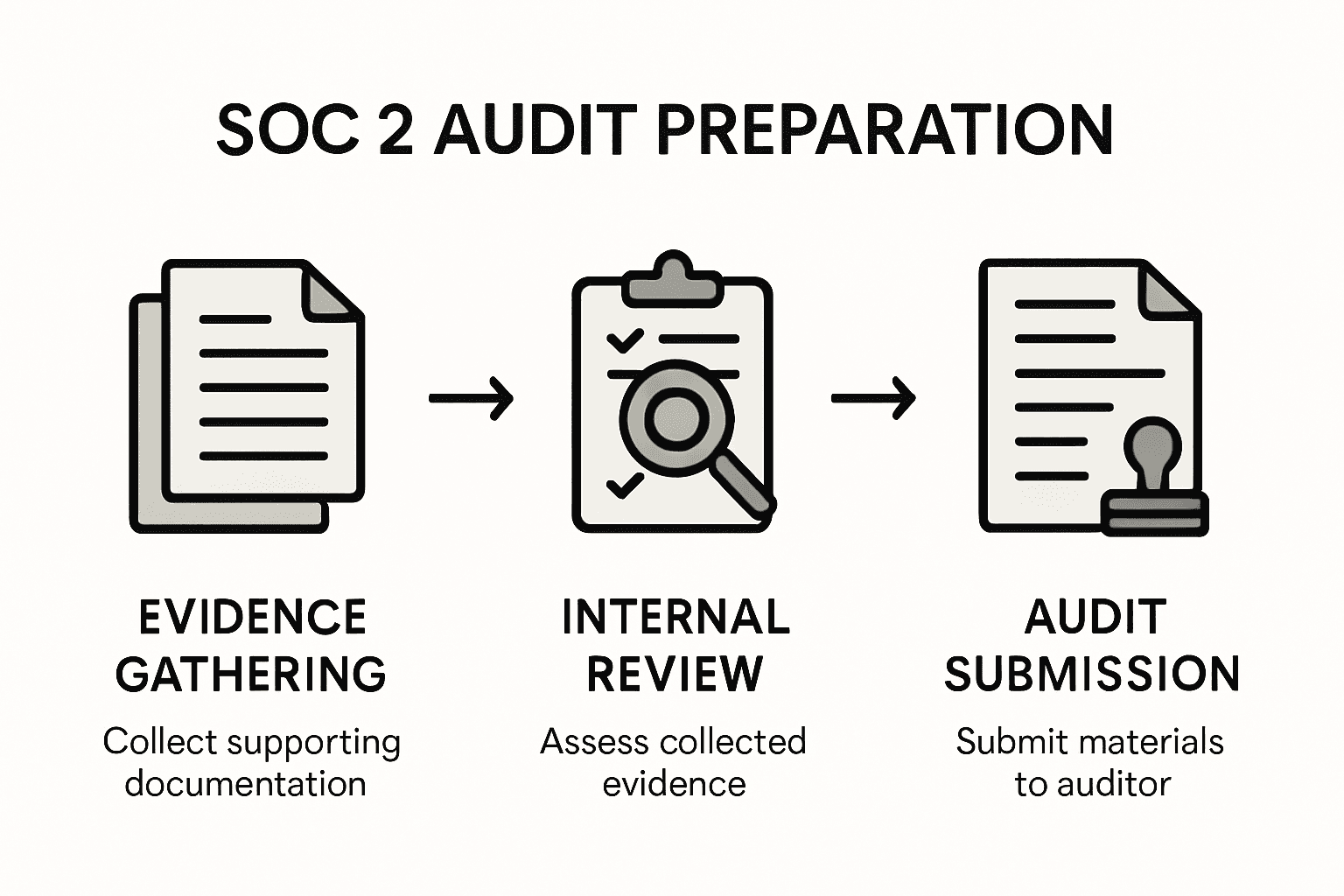
Step 4: Document evidence and prepare for audit
Preparing for your SOC 2 audit requires a meticulous approach to documenting control implementation and effectiveness. Your goal is to create a comprehensive evidence portfolio that demonstrates your organization's robust security and compliance practices.
Begin by establishing a systematic documentation strategy that captures every aspect of your implemented controls. This involves creating detailed logs, screenshots, policy documents, and performance records that prove your security measures are not just theoretical but consistently applied. Focus on collecting evidence that directly maps to each Trust Services Criteria you identified earlier. Include change management logs, access control records, incident response documentation, risk assessment reports, and detailed system configuration snapshots. Organize these documents in a clear, chronological manner that allows auditors to easily trace the implementation and ongoing maintenance of your security controls.
Engage your cross functional team to conduct a comprehensive internal review before the actual audit. This preemptive mock audit should critically examine your evidence collection, looking for potential gaps or areas of weakness. Ensure that your documentation tells a cohesive story of your security posture demonstrating not just compliance but a proactive approach to managing organizational risks. Prepare a master index that cross references your evidence with specific SOC 2 requirements, making it easier for auditors to navigate and validate your compliance efforts.
Pro tip: Create a digital evidence vault with version controlled documents and a clear audit trail, enabling quick and transparent access to compliance documentation while maintaining strict access controls.
Step 5: Conduct internal review and address deficiencies
Conducting a rigorous internal review is a critical step in ensuring your organization is fully prepared for the SOC 2 audit. Your primary objective is to perform a comprehensive assessment of control effectiveness before external auditors evaluate your security practices.
Begin by assembling a cross functional team of internal experts from IT, security, compliance, and operations. Develop a systematic approach to evaluate each implemented control against the Trust Services Criteria. This involves conducting detailed tests and simulations that challenge your existing security mechanisms. Look for potential vulnerabilities, inconsistent implementations, or gaps in your current processes. Pay special attention to areas such as access management, data protection, incident response, and vendor risk management. Document every finding meticulously, creating a comprehensive report that not only identifies deficiencies but also provides clear recommendations for remediation.
Prioritize the identified issues based on their potential risk and impact on your overall security posture. Create a structured remediation plan with specific timelines, assigned responsibilities, and measurable outcomes. Implement corrective actions systematically, ensuring that each improvement is thoroughly tested and documented. Conduct follow up reviews to verify that the implemented changes effectively address the initial deficiencies. This proactive approach demonstrates your organization is committed to continuous improvement and maintains a robust security framework.
Pro tip: Establish a continuous improvement cycle that treats the internal review as an ongoing process rather than a one time audit preparation activity, embedding a culture of persistent security enhancement.
Step 6: Engage a SOC 2 auditor for final certification
Selecting the right SOC 2 auditor is a critical step in your compliance journey. Your goal is to choose a qualified independent auditor who will provide an objective assessment of your security controls and practices.
Begin by researching and identifying Certified Public Accounting firms with specific expertise in SOC 2 audits. Look for auditors who have deep experience in your industry and understand the unique security challenges of your business sector. During the selection process, request detailed information about their audit methodology, experience with similar organizations, and approach to evaluating Trust Services Criteria. Prepare a comprehensive information package that includes your internal documentation, gap analysis results, and implemented security controls to facilitate a smooth audit process.
Schedule initial scoping meetings with potential auditors to discuss the specific requirements of your SOC 2 examination. Be transparent about your organizational structure, technology infrastructure, and previous compliance efforts. Work collaboratively to define the audit's scope, timeline, and specific areas of focus. Expect the auditor to conduct an in depth review of your documentation, perform interviews with key personnel, and test the effectiveness of your implemented controls. Maintain open communication throughout the audit process, providing prompt and comprehensive responses to any questions or requests for additional information.
Pro tip: Create an audit support team within your organization that can quickly respond to auditor inquiries and provide context for your security controls, ensuring a smooth and efficient certification process.
The following table summarizes key roles and responsibilities throughout the SOC 2 preparation process:
| Role | Main Responsibility | Area of Ownership |
|---|---|---|
| IT | Implement technical controls, monitor systems | Security, monitoring |
| Security | Design policies, run risk assessments | Controls, compliance |
| Compliance | Document controls, coordinate audit process | Reporting, evidence |
| Operations | Integrate practices, train staff | Procedures, training |
| Leadership | Approve strategy, allocate resources | Oversight, priorities |
Strengthen Your SOC 2 Compliance Journey With Expert Guidance
Navigating the complexities of SOC 2 compliance involves thorough gap analysis, tailored risk assessments, and detailed control implementations. Many regulated organizations face challenges such as incomplete documentation, inconsistent control effectiveness, and the need to balance security with operational efficiency. At Heights Consulting Group, we understand these critical pain points and offer strategic cybersecurity consulting designed to transform compliance from a technical hurdle into a business advantage. Our expertise in the Trust Services Criteria and comprehensive frameworks equips your leadership and security teams with the tools to confidently implement controls, prepare for audits, and maintain continuous security improvements.

Partner with Heights Consulting Group today to accelerate your path to SOC 2 certification. Our services cover everything from the initial gap assessment to audit readiness and beyond — aligning cybersecurity with your business objectives and regulatory requirements. Don’t leave your compliance success to chance when you can leverage proven expertise and a collaborative approach. Visit Heights Consulting Group now to learn how our advisory and technical solutions can help you overcome compliance challenges with confidence and precision.
Frequently Asked Questions
What are the first steps to achieve SOC 2 compliance for regulated organizations?
Achieving SOC 2 compliance begins with assessing your current security controls and identifying gaps. Assemble a cross-functional team and perform a gap analysis to document your existing cybersecurity infrastructure against the Trust Services Criteria.
How do I define the scope of my SOC 2 compliance efforts?
To define the scope, carefully evaluate which Trust Services Criteria are most relevant to your organization. Engage stakeholders from various departments to collaboratively determine the specific criteria that align with your operational needs and potential risks.
What processes should be in place for SOC 2 compliance?
Implementing comprehensive security and compliance processes is essential for SOC 2 readiness. Draft detailed security policies that cover data protection, access management, incident response, and vendor management, ensuring they are practical and integrated into daily operations.
What documentation is required to prepare for the SOC 2 audit?
Prepare a comprehensive evidence portfolio that includes detailed logs, policy documents, and performance records to support your compliance claims. Organize these documents systematically and conduct a mock audit to identify any gaps prior to the actual audit.
How can I effectively engage a SOC 2 auditor for certification?
Select a qualified independent auditor by researching firms experienced in SOC 2 assessments within your industry. Schedule scoping meetings to align on specific requirements, and maintain open communication throughout the audit process to facilitate a smooth experience.
Recommended
- SOC 2 compliance checklist: 10 essential controls - Heights Consulting Group
- A Practical Guide to Your SOC 2 Readiness Assessment - Heights Consulting Group
- The Ultimate 2025 SOX IT Controls Checklist Overview - Heights Consulting Group
- Compliance for Financial Services: Ensuring Integrity - Heights Consulting Group
- Cannabis Financial Reporting Guide for Full Compliance Success - Cannabis Business Minds
