TL;DR:
- Effective cyber incident response depends on strong governance and board-level accountability.
- Regular, realistic exercises reveal leadership and communication gaps critical for readiness.
- Regulatory compliance requires integrating multi-jurisdictional reporting, documentation, and third-party procedures.
When a cyber incident strikes a regulated organization, the difference between a controlled response and a catastrophic failure often comes down to governance, not technology. Boards that lack accountability structures, executives who have never rehearsed their roles, and compliance teams operating in silos are routinely exposed when real pressure arrives. NIST SP 800-61r3 establishes the foundational methodology for incident response, integrating directly with CSF 2.0's Govern, Identify, Protect, Detect, Respond, and Recover functions. This guide delivers the advanced strategies, practical frameworks, and actionable steps that executive and security leaders in regulated industries need to build response programs that actually hold under fire.
Table of Contents
- The strategic foundation: governance and accountability
- Building the advanced incident response program
- Simulation, practice, and real-world readiness
- Regulatory integration and global compliance demands
- Why traditional plans fail: an executive perspective
- Connect with experts to elevate your incident response
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Board accountability | Embed incident response into executive oversight for lasting resilience. |
| Simulate, don't just document | Exercise plans regularly across business functions to uncover and address weaknesses. |
| Align with regulations | Meet and harmonize all major regulatory demands to avoid fines and reputational damage. |
| Continuous improvement | Iteratively refine your IR program with lessons from testing and external assessments. |
The strategic foundation: governance and accountability
Effective incident response begins at the board level, not in the security operations center. Organizations operating in regulated industries such as financial services, healthcare, and critical infrastructure must treat incident response as a governance imperative rather than a technical procedure. The consequences of misaligned governance are concrete and measurable: regulatory fines, elevated insurance premiums, loss of operating licenses, and lasting reputational damage that erodes customer trust.
NIST SP 800-61r3 makes the accountability case clearly. It emphasizes embedding IR within organizational governance for regulated industries, with explicit board-level accountability assigned to named executives. This is not optional language for auditors. It is a structural requirement that determines whether an organization can respond decisively when a ransomware attack or data breach escalates beyond the security team's authority.
The NIST CSF 2.0 "Govern" function, elevated to a primary framework component, reinforces this mandate. Rather than treating cybersecurity as a technical domain managed by IT, CSF 2.0 requires that executives define risk tolerance, set priorities, and establish oversight processes that span the entire IR lifecycle. Organizations that still treat the Govern function as a compliance checkbox will find themselves unprepared when cross-functional decisions must be made in real time.
The CISA Cybersecurity Performance Goals update adds further pressure by incorporating supply chain risks, zero-trust mandates, and IR communication requirements for critical infrastructure operators. These additions signal that regulators expect a maturity level that goes well beyond perimeter defense and basic recovery planning.
To move from passive governance to active accountability, executive teams should implement the following structural controls:
- Assign a named executive sponsor for every incident response plan, with a designated backup
- Include IR metrics in every board packet, covering detection rates, mean time to respond, and exercise completion rates
- Map IR obligations to specific regulatory frameworks applicable to your sector, including sector-specific requirements layered on top of NIST baselines
- Integrate supply chain IR procedures into third-party risk management programs, ensuring vendors are contractually bound to incident notification timelines
- Document decision authority thresholds so that executives know exactly when they must engage versus delegate during an active incident
Pro Tip: The most common governance gap is not the absence of an IR plan but the absence of clear escalation authority. Before your next board review, confirm that every executive understands which decisions require their direct approval during an active incident and that their backup has equivalent authority.
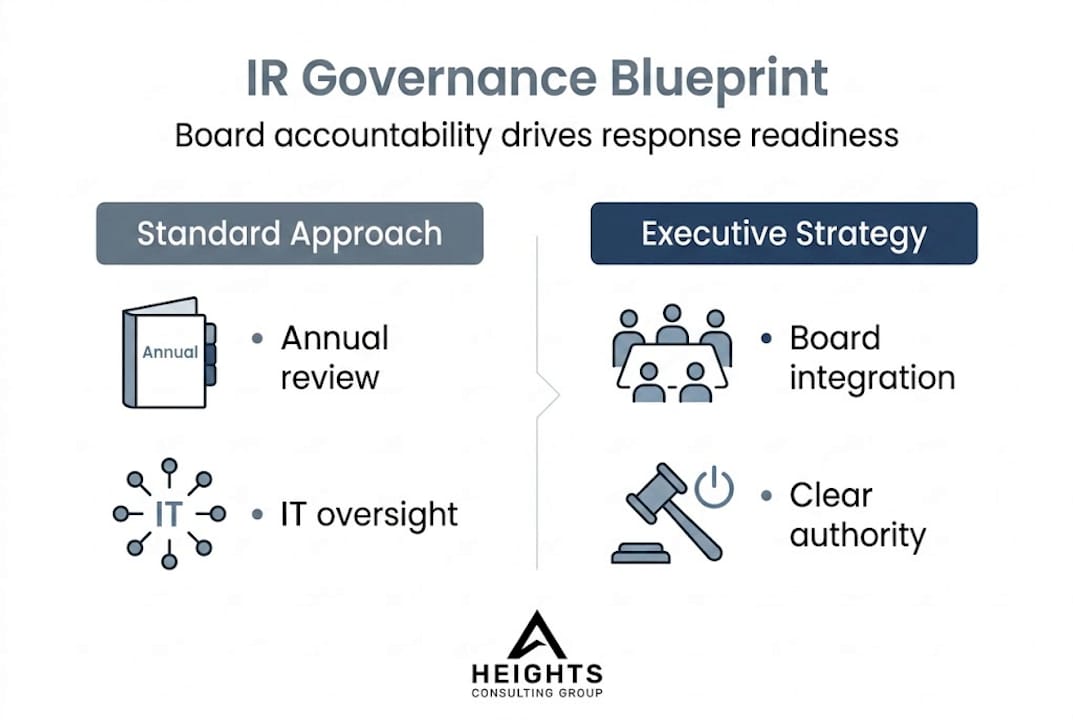
| Standard governance approach | Advanced executive governance |
|---|---|
| IR plan reviewed annually by IT | IR plan owned by named executive sponsor |
| Cybersecurity updates in tech committee only | IR metrics included in every board packet |
| Vendor contracts mention security generally | Vendors contractually bound to notification timelines |
| Risk tolerance defined broadly | Risk tolerance mapped to specific IR scenarios |
Using a structured NIST compliance checklist aligned to CSF 2.0 functions can help security leaders systematically verify governance controls before regulatory scrutiny arrives. Aligning your IR governance with enterprise-wide risk management services also ensures that cyber risk does not remain isolated from broader organizational risk frameworks.
Building the advanced incident response program
With strategic foundations established, the next priority is constructing an IR program that reflects the complexity of modern regulated environments. Standard IR plans typically cover detection, containment, eradication, and recovery at a surface level. Advanced programs go further, integrating third-party procedures, continuous improvement cycles, and technical controls that regulators increasingly expect to see demonstrated rather than documented.
CISA's cybersecurity advisory guidance identifies several specific practices that separate mature IR programs from baseline compliance efforts. Prompt vulnerability patching with defined SLAs, regular testing and exercising of IR plans that include third-party access scenarios, continuous review of endpoint detection and response (EDR) alerts, and out-of-band logging as a resilience mechanism are among the most frequently cited differentiators. Out-of-band logging, in particular, deserves executive attention because it preserves forensic integrity even when primary systems are compromised, making regulatory investigations significantly more straightforward.
The CISA CPG 2.0 update also emphasizes that supply chain integration within IR programs is no longer an advanced consideration. It is a baseline expectation for critical infrastructure organizations and increasingly for any enterprise with complex vendor ecosystems.
An effective advanced IR program for regulated industries should include the following components, implemented in order of dependency:
- A formally documented IR plan that assigns roles, escalation paths, and decision authority at every phase of response
- Third-party IR procedures that define how vendors, managed service providers, and cloud partners are notified, contained, and monitored during an incident
- Supply chain integration protocols that identify high-risk vendors and establish pre-negotiated response commitments
- A continuous vulnerability management program with defined patching windows and exception processes requiring executive approval
- EDR alert review cadences that ensure security analysts are not overwhelmed and that critical alerts receive prioritized investigation
- Out-of-band logging architecture that preserves audit trails on systems isolated from primary network infrastructure
- Regular IR exercises conducted at least annually, with tabletop simulations and functional drills covering different threat scenarios
"Failure to rehearse is failure to lead. An IR plan that has never been tested under pressure is a liability, not an asset."
The maturity gap between organizations that exercise their plans and those that merely document them is significant. Resources for building effective IR teams and reviewing incident response tips for C-level executives can accelerate this maturity journey by providing structured starting points and practical benchmarks.
| Standard IR action | Advanced IR program action |
|---|---|
| Annual plan review | Quarterly plan updates with exercise integration |
| Generic vendor notification clause | Pre-negotiated vendor IR commitments with timelines |
| Reactive vulnerability patching | Continuous patching with executive-approved SLAs |
| Basic logging on primary systems | Out-of-band logging for forensic integrity |
| Tabletop exercise with internal staff only | Cross-functional exercises with third-party facilitators |
Simulation, practice, and real-world readiness
With core program elements in place, the critical differentiator becomes how often and how rigorously organizations test their plans. Documentation creates the illusion of readiness. Simulation creates actual readiness. This distinction is not semantic. It determines whether your leadership team can execute effectively when an incident unfolds on a Friday evening with incomplete information and competing organizational pressures.

Cross-functional exercises improve executive alignment for 80% of organizations that implement them regularly, and yet 57% of organizations report that their last significant incident involved plans that had never been rehearsed. These numbers reveal a preparation gap that regulatory frameworks increasingly penalize through post-incident scrutiny of IR documentation and exercise records.
Executive sponsorship of simulations is not just symbolic. When senior leaders participate directly in tabletop exercises, cross-functional teams treat the process with the seriousness it deserves. Legal, communications, finance, operations, and human resources all have roles in incident response. Their alignment cannot be assumed. It must be built through repeated practice under realistic conditions.
Common weaknesses that surface during well-designed IR exercises include:
- Unclear decision authority when the designated IR leader is unavailable or overwhelmed
- Communication breakdowns between technical teams and executive leadership, often because different teams use different terminology
- Incomplete regulatory notification procedures, particularly when incidents span multiple jurisdictions
- Third-party notification delays caused by undefined escalation contacts within vendor organizations
- Recovery prioritization conflicts between IT teams focused on restoration and business units focused on continuity
- Documentation gaps that prevent forensic investigators from reconstructing the incident timeline accurately
Understanding the role of incident response in financial sector organizations provides additional context for why cross-functional alignment matters so much in highly regulated environments. Financial institutions face simultaneous obligations to multiple regulators, and a simulation that does not include the regulatory notification workflow is incomplete by definition.
Pro Tip: Engage a third-party facilitator for at least one major IR exercise annually. Internal facilitators, however experienced, cannot fully replicate the objectivity required to surface the leadership and communication gaps that only appear when participants feel genuinely tested. A good facilitator will create scenarios that expose your weakest links without creating organizational defensiveness.
For organizations that want a structured framework to guide their exercise programs, a step-by-step IR plan for executives provides a starting point that can be adapted to sector-specific requirements and organizational complexity.
Regulatory integration and global compliance demands
Testing brings actionable insight, but integrating compliance requirements ensures that your response survives regulatory review after the incident is resolved. For organizations operating across multiple jurisdictions or under the oversight of several regulators simultaneously, this integration is among the most operationally demanding elements of a mature IR program.
The regulatory landscape is not uniform. Reporting timelines, log retention requirements, and notification obligations differ significantly across jurisdictions and sectors. India's BFSI sector requirements illustrate the specificity regulators now demand: CERT-In mandates incident reporting within six hours of detection, with log retention obligations extending to 180 days. Organizations operating across borders must harmonize these obligations without letting secondary regulatory requirements undermine compliance with the primary regulator.
This challenge is not unique to the BFSI sector. Healthcare organizations navigating HIPAA alongside state-level breach notification laws, defense contractors managing CMMC requirements alongside federal contract obligations, and financial institutions balancing SEC disclosure rules with prudential regulator requirements all face analogous multi-regulator complexity.
"Prioritize your primary regulator, but never assume secondary obligations are optional. Enforcement actions rarely originate from the regulator you were watching most carefully."
A structured approach to regulatory integration within your IR program should follow these steps:
- Identify every regulatory framework that applies to your organization, including sector-specific rules, jurisdiction-specific breach notification laws, and contractual obligations to customers or partners
- Map reporting timelines for each framework, noting where requirements conflict or overlap, and build your fastest obligation into your default notification workflow
- Harmonize documentation requirements by designing incident records that satisfy the most demanding framework, reducing duplication while ensuring completeness
- Test your regulatory notification workflow explicitly during IR exercises, including the specific contacts, templates, and approval processes required for each regulator
- Document your compliance decisions during an incident in real time, creating an audit trail that demonstrates good-faith efforts to comply even when timelines are compressed
Detailed guidance on regulatory compliance cybersecurity strategies can help security leaders structure this multi-framework integration systematically, particularly when new regulatory requirements create gaps in existing IR plans.
Why traditional plans fail: an executive perspective
Most IR plans fail not because they lack technical detail but because they lack leadership resilience. Organizations invest in documentation, hire qualified security professionals, and then quietly assume that preparedness will follow. It rarely does without deliberate, executive-driven simulation.
The uncomfortable reality from working with regulated organizations across sectors is that the most dangerous IR gap is almost never technical. It is human. Specifically, it is the assumption that the designated IR leader will be available, functional, and effective at the moment of maximum pressure. The hard question that most leadership teams avoid is this: what happens if your primary IR decision-maker is unreachable during a major incident? If that answer is not written down and practiced, your plan has a critical vulnerability that no security tool can address.
The true return on investment from simulation is not the technical findings it produces. It is the leadership gaps it surfaces. Organizations that approach exercises primarily as technical drills miss the most valuable output. They learn whether their systems work. They do not learn whether their leaders can function under pressure, communicate across functions, and make defensible decisions with incomplete information.
Reviewing executive IR lessons reinforces a consistent pattern: organizations that overrate documentation and underrate experiential drills are the ones that struggle most when real incidents occur. The shift from a compliance mindset to a resilience mindset is the defining characteristic of executive teams that lead effectively through crises.
Connect with experts to elevate your incident response
Turning executive insight into operational readiness requires more than frameworks and checklists. It requires experienced partners who can assess your current posture objectively, design exercises that surface real gaps, and implement the technical and procedural improvements your organization needs to meet evolving regulatory expectations.

Heights Consulting Group provides technical cybersecurity consulting that bridges strategic intent and operational execution, helping regulated organizations build IR programs that satisfy regulators and actually work under pressure. Our incident response services include readiness assessments, exercise facilitation, and managed response capabilities designed for organizations with complex environments and stringent compliance demands. If your IR posture has not been independently assessed in the past twelve months, now is the right time to act.
Frequently asked questions
What should an executive focus on first in incident response?
Begin by ensuring board-level accountability and integrating incident response within the broader governance framework. NIST SP 800-61r3 establishes that embedding IR within executive governance is the foundational requirement for regulated industries before any technical program elements can be effective.
Why are cross-functional IR exercises important?
They reveal alignment gaps and help executives ensure that plans are effective under real pressure, not just on paper. 80% of executives report that cross-functional exercises improve organizational alignment, making them one of the highest-return investments in IR preparedness.
How fast do we need to report incidents to regulators?
Many sectors require rapid reporting, with timelines far shorter than most organizations expect. India BFSI regulations mandate reporting within six hours and 180-day log retention, and similar urgency applies across multiple global regulatory frameworks.
What is CSF 2.0 and why does it matter?
CSF 2.0 is the latest NIST cybersecurity framework, elevating governance as a primary function and integrating IR into executive-level oversight. NIST SP 800-61r3 aligns directly with CSF 2.0, providing the methodology that makes the Govern function actionable for regulated organizations.
How often should IR plans be tested?
Best practice is to test at least annually and after any major organizational or technological change. CISA advisory guidance specifically calls for regular IRP exercises that include third-party access scenarios and use third-party facilitators to ensure objectivity and completeness.
