Protecting endpoints often feels like playing catch-up with attackers who constantly shift tactics and probe for weaknesses. For CISOs and IT security managers in regulated U.S. industries, the stakes rise with every compliance mandate and headline-making breach. By focusing on a defense-in-depth strategy and enforcing robust access controls, you gain actionable tools to strengthen endpoint defenses, address regulatory demands, and reduce the risk of a costly incident.
Table of Contents
- Step 2: Implement Layered Protection And Controls
- Step 3: Enforce Access And Compliance Policies
- Step 4: Monitor And Respond To Endpoint Threats
- Step 5: Test And Validate Endpoint Security Measures
Quick Summary
| Key Insight | Explanation |
|---|---|
| 1. Implement Layered Security | Use multiple defense tools to ensure if one fails, others will protect against threats. |
| 2. Enforce Access and Compliance Policies | Document and enforce policies that restrict user access and ensure security compliance within your organization. |
| 3. Continuously Monitor Endpoint Threats | Set up real-time monitoring for suspicious activity to quickly respond to detected threats, minimizing potential damage. |
| 4. Regularly Test Security Measures | Conduct vulnerability scans and penetration testing to validate that your security measures effectively stop real-world attacks. |
| 5. Integrate Security Tools Effectively | Ensure that security tools work together seamlessly to avoid performance issues and enhance overall protection. |
...
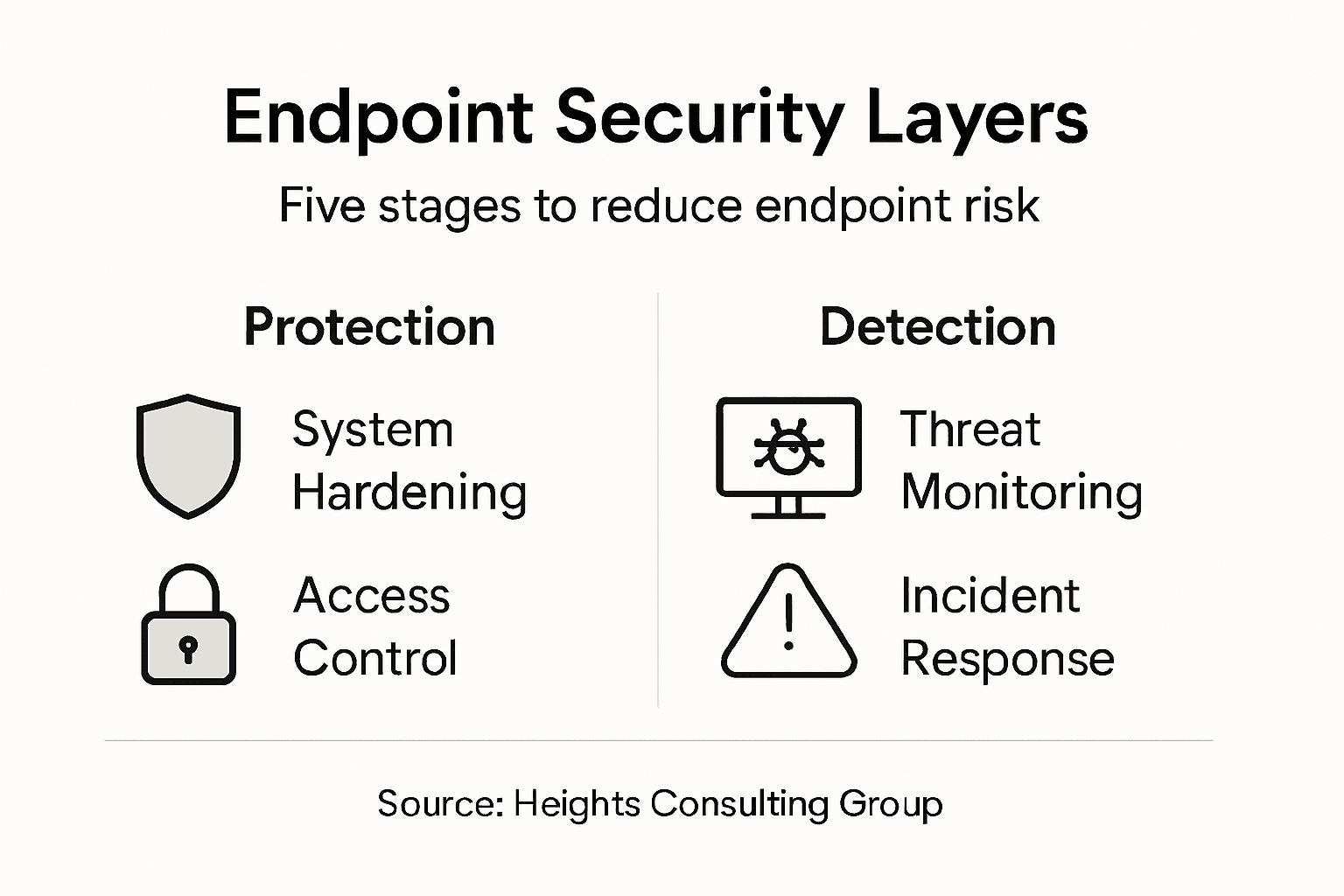
Step 2: Implement layered protection and controls
Layered security means stacking multiple defensive tools so that if one fails, others catch the threat. This approach, known as defense-in-depth, significantly reduces the likelihood that any single vulnerability becomes a critical breach. You'll combine different technologies and policies to address various attack vectors at the endpoint level.
Start by identifying the core control layers your organization needs. Most effective strategies include:
- Endpoint Detection and Response (EDR) for real-time threat visibility
- Traditional antivirus as a baseline layer
- Application control to restrict unauthorized software execution
- Multi-factor authentication (MFA) to secure access points
- Network segmentation to limit lateral movement if compromise occurs
Defense-in-depth works because attackers rarely exploit just one vector—your layered approach forces them to overcome multiple obstacles simultaneously.
Implement system hardening first by removing unnecessary services, disabling unused ports, and restricting administrative privileges. This reduces your attack surface before adding detection tools. Then add defense-in-depth security controls that address different attacker tactics at each endpoint.
Don't overload endpoints with redundant tools—this creates performance issues and management complexity. Instead, select complementary solutions that work together. For example, EDR should integrate with your antivirus rather than replace it, and MFA should work seamlessly with your identity platform.
Continuously monitor which controls are actually blocking threats. Review logs quarterly to confirm your layered approach is preventing incidents, then adjust based on what you observe in your threat data.
Below is a summary of common endpoint security controls and the risks they address:
| Security Control | Primary Purpose | Example Risks Mitigated |
|---|---|---|
| Endpoint Detection & Response | Detect and respond to threats | Malware, ransomware attacks |
| Multi-factor Authentication | Strengthen identity verification | Credential theft, unauthorized logins |
| Application Control | Restrict program execution | Unauthorized software, zero-days |
| Network Segmentation | Limit internal attack spread | Lateral movement, data leaks |
| System Hardening | Reduce attack surface | Unpatched vulnerabilities, misconfigurations |
Pro tip: Start with CIS Critical Security Controls as your implementation roadmap—these prioritized controls are proven to stop most common breaches and provide a structured path for layering defenses effectively.
Step 3: Enforce access and compliance policies
Access and compliance policies form the guardrails that prevent unauthorized users from reaching sensitive data and ensure your organization meets regulatory requirements. Strong policy enforcement means only authorized personnel can access specific endpoints and resources, reducing your exposure to insider threats and data breaches. This step translates your security strategy into actionable rules that everyone follows.
Begin by documenting your access control requirements. Define who needs access to which systems and what actions they can perform. Your policy framework should address:
- Multi-factor authentication (MFA) for all user logins
- Least privilege principles restricting permissions to minimum necessary levels
- Account management procedures for creating, modifying, and removing access
- Privileged access controls limiting administrative credentials
- User access reviews conducted quarterly to catch unauthorized permissions
Policies without enforcement are just suggestions. Your technology must actively block unauthorized access attempts, not simply warn about them.
Implement access control and compliance standards that govern how users authenticate and what they can do on endpoints. Configure your identity management system to enforce these rules automatically. When someone tries to access a resource outside their permitted scope, the system denies access immediately.
Monitor compliance continuously rather than waiting for annual audits. Set up automated logging to track who accessed what, when, and why. Review these logs monthly for anomalies. If someone suddenly starts accessing files they never touched before, that's a red flag worth investigating immediately.
Communicate your policies clearly to employees. Many compliance failures happen because people don't understand the rules, not because they're trying to bypass them. Provide training on MFA setup, password requirements, and what to do if they need access they don't currently have.
Pro tip: Implement continuous user access reviews using least privilege principles rather than static annual reviews—this catches permission creep early before it becomes a compliance problem.
Step 4: Monitor and respond to endpoint threats
Monitoring endpoints means actively watching for suspicious behavior while your defenses are in place. Detection alone is not enough—you need a coordinated response plan that kicks in when threats are identified. This step bridges the gap between prevention and recovery, dramatically reducing the time attackers spend inside your environment.

Set up continuous monitoring across all endpoints using your EDR solution and security information and event management (SIEM) tools. These systems collect logs and behavioral data that reveal what's happening on each device. Your team needs visibility into failed login attempts, unusual file access patterns, unauthorized software installations, and network connections to known malicious sites.
Establish clear detection priorities. Focus your monitoring efforts on:
- High-risk user accounts like administrators and finance staff
- Critical systems storing sensitive data or running essential services
- External-facing devices more likely to be targeted
- Recently patched systems where attackers might exploit zero-days
- Anomalous network traffic indicating data exfiltration attempts
A threat detected in 5 minutes versus 5 days makes the difference between a minor incident and a catastrophic breach.
When your monitoring systems detect suspicious activity, follow a structured incident response and threat detection process. Don't wait for perfect certainty before investigating—false alarms are far better than missed threats. Your incident response plan should document who to contact, what information to gather, and how to contain compromised endpoints immediately.
Containment is critical. When you identify a compromised endpoint, isolate it from the network within minutes. This prevents attackers from spreading laterally to other systems. Then investigate what happened, remove the threat, and validate the system is clean before reconnecting it.
Document every incident and use those lessons to improve your monitoring. If an attack slipped past your controls, adjust your detection rules so similar attacks don't bypass you again.
The following table compares key endpoint monitoring and response activities and their business impact:
| Activity | Key Benefit | Business Impact |
|---|---|---|
| Continuous Monitoring | Detect threats in real-time | Prevents prolonged breaches |
| Incident Response Planning | Enables rapid threat containment | Minimizes damage and downtime |
| Regular Log Reviews | Identifies anomalous activities early | Reduces risk of unnoticed attacks |
| Automated Alerting | Notifies team of critical events | Improves response speed |
Pro tip: Implement continuous vulnerability management and threat intelligence into your monitoring workflow so your detection systems automatically adapt to emerging threat patterns rather than relying solely on static rules.
Step 5: Test and validate endpoint security measures
Testing your endpoint security controls reveals whether they actually work in real-world conditions. Theory and practice often diverge—a policy that looks solid on paper might fail when faced with actual threats. This step converts your security investments into measurable confidence that your defenses can stop real attacks.
Begin with vulnerability scanning on representative endpoints across your organization. These automated scans check for known weaknesses in operating systems, applications, and configurations. Schedule scans monthly and after major changes like software updates or policy modifications. When vulnerabilities appear, prioritize fixes based on severity and exploitability rather than trying to fix everything at once.
Conduct penetration testing to simulate actual attacker behavior. Unlike passive vulnerability scanning, pen testing actively attempts to compromise systems using techniques attackers would employ. Your team should perform host-based and network-based security assessments at least annually, and more frequently in high-risk environments.
Structure your testing to cover critical scenarios:
- Access control validation confirming MFA actually blocks unauthorized logins
- Malware detection testing whether EDR catches known and unknown threats
- Data exfiltration attempts verifying network monitoring catches suspicious outbound traffic
- Lateral movement simulating how attackers would move between systems
- Privilege escalation testing whether unprivileged users can gain admin access
A security control that hasn't been tested is just an assumption waiting to be proven wrong.
Document your testing results and create a remediation plan for failures. If EDR missed a specific malware variant, investigate why and update detection signatures. If an attacker could escalate privileges through a misconfiguration, fix that configuration and retest.
Validate improvements by retesting the same scenarios after fixes are applied. This closes the feedback loop and demonstrates that your changes actually worked rather than just assuming they did.
Pro tip: Maintain a continuous assessment program that tests endpoint controls quarterly rather than waiting for annual penetration tests—this catches new misconfigurations before attackers find them.
Strengthen Your Endpoint Security with Expert Guidance from Heights Consulting Group
The article highlights critical challenges in endpoint security such as implementing defense-in-depth, enforcing access controls, and continuous threat monitoring. Organizations often struggle with complex layers of protection, real-time detection, and strict policy enforcement to minimize cyber risks. If you are seeking to reduce vulnerability exposure, ensure compliance with frameworks like NIST or SOC 2, and respond swiftly to incidents, aligning your strategy with expert support is essential.
Elevate your security posture by partnering with a firm that understands how to integrate technical solutions into business objectives. Heights Consulting Group offers comprehensive services including managed cybersecurity, endpoint detection, incident response, and compliance advisory to help you build a resilient defense tailored to your unique risks.

Don’t wait for a breach to disrupt your operations. Visit Heights Consulting Group now to learn more about our managed cybersecurity services and how our proven frameworks protect endpoints across highly regulated industries. Take control of your cybersecurity success today with trusted strategic guidance.
Frequently Asked Questions
What are the essential components of an endpoint security strategy?
To build a strong endpoint security strategy, incorporate multiple layers of protection, including Endpoint Detection and Response (EDR), antivirus solutions, application control, and multi-factor authentication (MFA). Start by assessing your organization's specific needs and implement controls that address different attack vectors.
How can I assess the effectiveness of my current endpoint security measures?
You can assess your endpoint security by conducting regular vulnerability scans and penetration tests to identify weaknesses. Schedule these assessments monthly or after significant changes, and prioritize remediation based on the severity of the findings.
What steps should I take to implement system hardening?
Begin system hardening by removing unnecessary services, disabling unused ports, and restricting administrative privileges. This reduces your attack surface and should be a primary step before adding additional security tools.
How often should I monitor and review access controls for my endpoints?
Monitor and review access controls for your endpoints continuously, conducting thorough user access reviews at least quarterly. This practice will help you identify and rectify any unauthorized permissions promptly, reducing the risk of breaches.
What should I do if a threat is detected on an endpoint?
If a threat is detected, immediately isolate the compromised endpoint from the network to prevent lateral movement. Follow your incident response plan to investigate the threat and validate that the system is clean before reconnecting it.
How can I ensure continual improvement of my endpoint security measures?
Regularly test and validate your endpoint security measures through continuous assessments, making adjustments based on what you learn. Adopt a feedback loop where you retest and confirm that any implemented changes effectively address previously identified vulnerabilities.