TL;DR:
- Organizations integrating cybersecurity with business goals are six times more likely to succeed in digital transformation.
- Embedding security from the start improves revenue growth, regulatory compliance, and customer trust.
- Strong cyber leadership, continuous risk management, and AI adoption are key to digital security resilience.
Organizations that treat cybersecurity as a compliance checkbox are leaving measurable business value on the table. Cyber-aligned firms are nearly six times more likely to achieve effective digital transformations, a figure that should reframe every boardroom conversation about security investment. For C-level executives and security leaders in regulated industries, this is not an abstract statistic. It is a strategic signal. This guide unpacks how embedding cybersecurity into your transformation strategy produces tangible gains in revenue, resilience, and market position, and what it takes to make that shift from reactive defense to proactive business enablement.
Table of Contents
- Cybersecurity as an enabler of digital transformation
- Aligning cybersecurity with business objectives
- Embedding cybersecurity into digital transformation strategy
- Evolving risks: AI, cloud, and the speed challenge
- Executive perspective: What most leaders get wrong about cybersecurity in transformation
- Partnering for cybersecurity-driven transformation
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Alignment fuels outcomes | Linking cybersecurity to business objectives makes digital transformation up to six times more effective. |
| Frameworks guide action | Using NIST CSF, CISA CPGs, and ENISA/NIS2 ensures compliance and security from the ground up. |
| AI shifts the risk equation | AI-driven threats require adaptive, behavior-led security strategies for regulated industries. |
| Executive leadership matters | Cyber-savvy boards and CISOs integrated in digital strategy yield higher business impact. |
Cybersecurity as an enabler of digital transformation
The traditional view of cybersecurity as a roadblock to innovation persists in many organizations, but the data tells a different story. High-cyber-maturity organizations consistently achieve greater business impact by integrating risk strategies directly into their technology and business initiatives. Security is not slowing transformation down. A weak security posture is.
Consider the contrast between two types of organizations. The first treats cybersecurity as a late-stage review, bolting on controls after systems are built. The second embeds security from the start, making it a design principle rather than an afterthought. The outcomes diverge sharply.
| Attribute | Low cybersecurity maturity | High cybersecurity maturity |
|---|---|---|
| Digital transformation success rate | Below average | Significantly above average |
| Revenue growth correlation | Weak | Strong |
| Regulatory compliance posture | Reactive | Proactive |
| Customer trust and retention | At risk | Reinforced |
| Incident recovery speed | Slow | Rapid |
"Cybersecurity maturity is no longer a technical benchmark. It is a business performance indicator that separates organizations capable of scaling digital initiatives from those that stall under the weight of unmanaged risk."
Several factors drive this gap. Organizations with mature security postures benefit from:
- Faster time-to-market for digital products, because security reviews are integrated rather than sequential
- Greater partner and customer confidence, enabling faster contract cycles in regulated sectors
- Reduced incident costs, freeing capital for innovation rather than remediation
- Stronger regulatory standing, reducing friction in market expansion
The role of leadership is equally decisive. When the C-suite is cyber-savvy and the CISO holds genuine influence over transformation decisions, security becomes a force multiplier. Executives who want to understand the cybersecurity strategic advantages available to their organizations will find that the most durable competitive positions are built on security foundations, not despite them.
Aligning cybersecurity with business objectives
Recognizing security as an enabler is the first step. Translating that recognition into operational alignment is where most organizations struggle. A structured approach makes the difference.
Here is a three-step framework for aligning cybersecurity with business priorities:
- Vision alignment: Start by mapping your cybersecurity strategy to specific business outcomes, such as entering new markets, accelerating product launches, or meeting regulatory requirements in target sectors. Security goals must speak the language of business value.
- Governance integration: Establish cross-functional governance that places security leadership at the same table as business unit leaders. This is not a reporting structure change alone. It is a cultural shift that gives security a voice in investment decisions.
- Execution with measurement: Define metrics that connect security performance to business outcomes. Reduction in breach-related downtime, customer data protection rates, and compliance audit pass rates all translate security work into business terms executives can act on.
The business case for this alignment is compelling. Organizations that align security with business objectives are 18% more likely to drive revenue growth, market share, and customer satisfaction. The same research identifies "cyber transformers" as nearly six times more likely to achieve effective digital transformations.
| Alignment level | Business outcome improvement | Transformation success likelihood |
|---|---|---|
| Low alignment | Marginal | Below average |
| Moderate alignment | Moderate | Average |
| High alignment | 18% above peers | Nearly 6X more likely |
To align cybersecurity with corporate goals effectively, organizations need regular maturity assessments that benchmark current capabilities against business requirements, not just technical standards. These assessments reveal gaps between where security investment is concentrated and where business risk is actually highest. Leaders who want a deeper strategic framework can explore how to align cybersecurity with business objectives at the executive level.

Pro Tip: Schedule a cybersecurity maturity assessment at least annually, and tie the findings directly to your business planning cycle. This ensures security investment decisions are driven by business risk, not technical preference.
Embedding cybersecurity into digital transformation strategy
With alignment established, embedding cybersecurity into every phase of transformation is the next critical step. This requires more than policy documents. It demands structural integration across planning, execution, and governance.
Actionable steps for embedding security throughout transformation include:
- Anchor strategy to business drivers: Cybersecurity strategy must articulate a clear vision tied to specific business drivers such as cloud adoption, digitalization, and regulatory change, then link that vision to a prioritized roadmap with measurable milestones.
- Engage the CISO from day one: Security leadership must participate in transformation planning from the earliest stages, not after architecture decisions are made. This prevents costly rework and security debt that accumulates when controls are retrofitted.
- Adopt proven frameworks: For regulated industries, CISA Cross-Sector Cybersecurity Performance Goals provide prioritized IT and OT practices aligned with NIST CSF 2.0, with a strong emphasis on governance. ENISA's technical guidance for regulated sectors under NIS2 covers 13 risk management measures including supply chain security and secure development.
- Embed governance and supply chain controls: Third-party risk is one of the most underestimated attack surfaces in digital transformation. Governance frameworks must extend to vendors, integrators, and cloud providers.
- Use agile risk management: Static annual risk assessments cannot keep pace with transformation velocity. Continuous risk monitoring, integrated into agile delivery cycles, keeps security posture current.
Building a cybersecurity roadmap for executives that reflects these principles gives leadership teams a clear line of sight from security investment to business outcome. A well-structured cybersecurity risk management framework provides the operational backbone for sustaining that roadmap over time.
Pro Tip: Involve your CISO in digital initiative planning from the first strategy session. Every week of delay in security engagement during transformation adds disproportionate cost and complexity to remediation later.
Evolving risks: AI, cloud, and the speed challenge
Embedding frameworks is essential, but transformation brings fast-evolving threats and new attack surfaces that frameworks alone cannot address. The pace of digital change is outrunning the capabilities of legacy security tools.
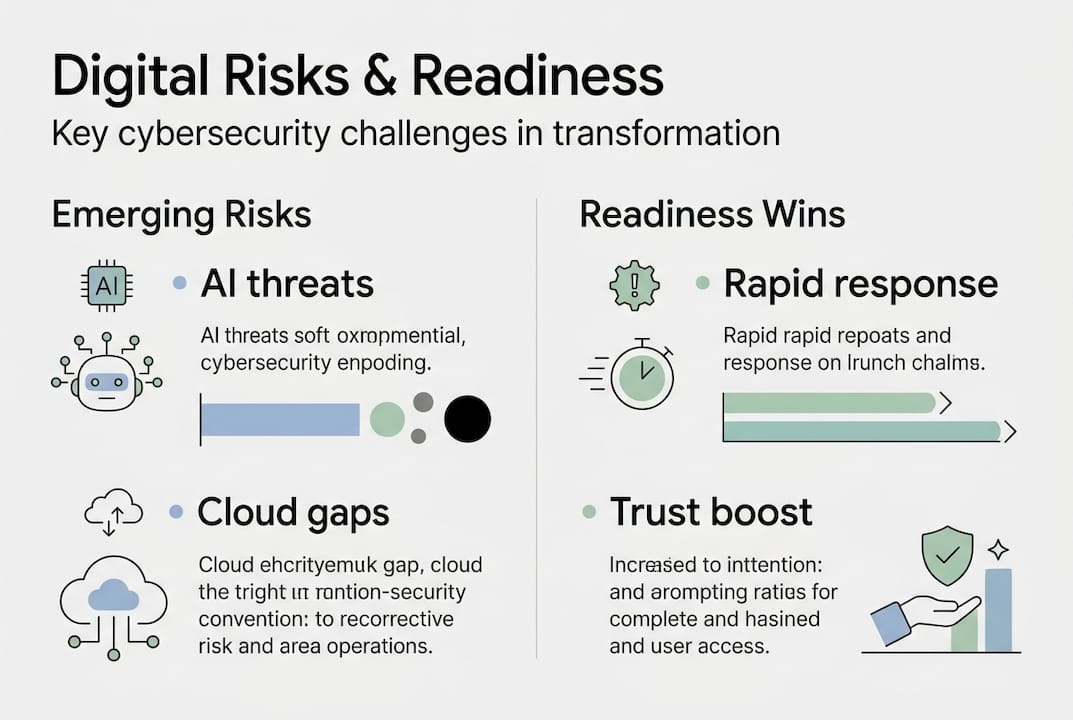
Legacy security struggles with the speed of digital growth. AI accelerates both threats and defenses simultaneously, making behavior-led detection and continuous operations a baseline requirement rather than an advanced capability. Cloud expansion and hyperconnectivity create blind spots that signature-based tools simply cannot see.
The readiness gap is stark. Only 4% of organizations globally have reached cybersecurity maturity, with AI Fortification the lowest-scoring domain at just 7% maturity. Nearly half of organizations surveyed experienced a cybersecurity attack in the past year. These numbers signal that most enterprises are scaling digital capabilities faster than they are securing them.
Executive actions that address this challenge include:
- Invest in AI-driven defenses: Understanding AI's real cybersecurity impact at the board level is now a governance responsibility, not just a technical one. AI-powered threat detection reduces mean time to detect and respond, which directly limits breach impact.
- Prioritize continuous improvement cycles: Point-in-time assessments are insufficient. Security posture must be measured and improved on a rolling basis, with executive dashboards tracking progress against business risk thresholds.
- Focus on network resilience: As organizations adopt AI-powered cybersecurity solutions, network architecture must be designed for resilience, assuming breach rather than relying solely on perimeter defense.
- Address cloud-specific risks: Multi-cloud environments require identity-centric security models, continuous posture management, and workload protection that legacy tools were never designed to provide.
The organizations that close this readiness gap fastest will carry a measurable advantage in market trust, regulatory standing, and operational continuity.
Executive perspective: What most leaders get wrong about cybersecurity in transformation
After working with C-level teams across regulated industries, a pattern emerges that statistics alone do not fully capture. Most executives understand that cybersecurity matters. Fewer understand that the way they position it internally determines whether it accelerates or constrains their transformation.
The most common mistake is treating cybersecurity as a compliance function rather than an enterprise risk and trust function. When security is owned by IT and reported to the CFO only during audits, it operates in isolation from the decisions that shape business outcomes. The result is a security program that checks boxes but does not move the needle on transformation.
The organizations that get this right do something counterintuitive. They measure security performance in business terms first, technical terms second. Breach probability, customer data exposure risk, and regulatory penalty exposure are business metrics. Patch rates and vulnerability counts are operational inputs. Executives who conflate the two end up optimizing the wrong things.
Cyber leadership in business strategy requires the CISO to function as a co-pilot in digital initiatives, not a last-minute advisor brought in to sign off on decisions already made. When security ownership is distributed across every business unit and measured in outcomes that matter to the board, transformation accelerates rather than stalls.
Pro Tip: Make the CISO a standing participant in your digital transformation steering committee. Their early involvement pays dividends that far exceed the cost of the seat at the table.
Partnering for cybersecurity-driven transformation
Ready to move from theory to action? The right partner can make security a genuine lever for digital progress, not just a risk management obligation.

Heights Consulting Group works with C-level teams and security leaders in regulated industries to embed cybersecurity into transformation strategies that deliver measurable business outcomes. From technical cybersecurity consulting to strategic advisory, our engagements are built around your business drivers, not generic frameworks. We help organizations transform cybersecurity challenges into competitive advantages by aligning security investment with growth objectives. If your organization is scaling digital capabilities and needs a security strategy that keeps pace, Heights Consulting Group is ready to build that roadmap with you.
Frequently asked questions
How does cybersecurity impact successful digital transformation?
Organizations integrating cybersecurity with business goals are six times more likely to achieve effective digital transformation, making security alignment a direct driver of transformation outcomes rather than a peripheral concern.
What frameworks should executives use for cybersecurity in transformation?
Leaders in regulated industries should prioritize NIST CSF 2.0, CISA Cross-Sector Cybersecurity Performance Goals, and ENISA NIS2 guidance covering 13 risk management measures including supply chain security and secure development practices.
Why is AI increasing cybersecurity risks during digital transformation?
AI accelerates both attack sophistication and defensive capabilities simultaneously, meaning organizations that do not adopt behavior-led detection and continuous operations will fall behind threat actors who are already using AI offensively.
What role should the CISO play in digital transformation?
The CISO should be a co-leader in transformation strategy from day one, embedding security into all business and technology initiatives rather than serving as a reviewer after architectural decisions have already been made.
