Holding a stack of certifications does not guarantee security. Many organizations that have passed rigorous audits still suffer costly data breaches, exposing a dangerous gap between documented compliance and actual resilience. Checkbox compliance creates a false sense of security, leaving organizations vulnerable despite certifications. For CISOs and compliance officers in regulated industries, this reality demands a fundamental shift: compliance must evolve from a periodic exercise into a continuous, risk-driven discipline that directly supports business objectives. This article examines how the CISO's role now bridges security, compliance, and business strategy in ways that go far beyond any checklist.
Table of Contents
- Why compliance is more complex than ever
- What does a CISO actually do in compliance?
- Beyond checkbox compliance: Why risk-driven strategy wins
- Best practices for CISOs leading compliance
- Future-proofing: Adapting compliance for AI, third-party risk, and the road ahead
- Partnering for next-level compliance and resilience
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Strategic leadership | CISOs must align compliance and security with business objectives using risk-based frameworks. |
| Continuous monitoring | Ongoing monitoring and automation are vital for managing audit fatigue and real threats. |
| Beyond checklists | Moving past checkbox compliance reduces gaps and improves true cyber resilience. |
| Future-readiness | AI and third-party risks require adaptive privacy programs and evolving controls. |
| Measurable value | Focusing on outcomes, not just controls, demonstrates compliance effectiveness to stakeholders. |
Why compliance is more complex than ever
The regulatory landscape facing CISOs today is not simply growing. It is fragmenting, overlapping, and accelerating simultaneously. Frameworks like GDPR, HIPAA, PCI DSS, and NIS2 each carry distinct requirements, yet organizations in regulated industries must satisfy several of them at once. Building a coherent cybersecurity strategy for compliance means reconciling these overlapping obligations without duplicating effort or creating blind spots.
CISOs lead compliance efforts by mapping regulations like GDPR, HIPAA, PCI DSS, and NIS2 to security controls using frameworks such as NIST CSF, CIS Controls, and ISO 27001. This mapping work is not a one-time project. Cross-border challenges and compliance creep increase complexity year over year, as new sector-specific rules layer on top of existing obligations.
The numbers reflect this pressure clearly:
| Compliance pressure indicator | Current reality |
|---|---|
| Organizations running 2 or more audits per year | 97% |
| Organizations pursuing multiple certifications | 92% |
| CISOs now reporting directly to the CEO | Majority |
| Average frameworks a regulated org must satisfy | 3 to 5 |
The risks of falling short are severe. Financial penalties under GDPR alone can reach 4% of global annual revenue. Reputational damage and legal scrutiny compound those costs in ways that are difficult to quantify but impossible to ignore. For deeper context on how these pressures are evolving, the regulatory compliance insights available from our team provide a useful executive-level overview.
"Compliance is no longer a back-office function. It is a board-level conversation, and the CISO is increasingly the person leading it."
Organizations that treat compliance as a series of isolated audits will consistently find themselves reactive. Those that build it into their operating model, guided by a strategic compliance guide, position themselves to absorb regulatory change without disruption.
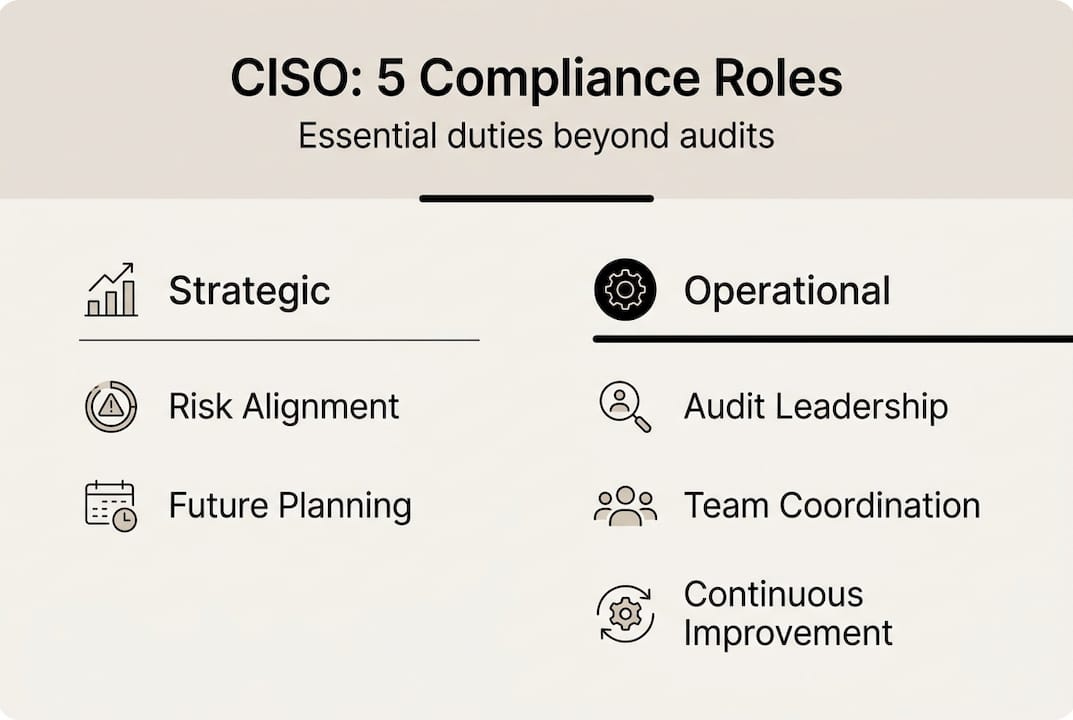
What does a CISO actually do in compliance?
Now that we know why compliance is so complex, let's examine what a CISO tangibly does to steer organizations through these requirements. The role spans technical, organizational, and executive dimensions simultaneously.
CISOs integrate compliance mapping, GRC, and collaboration with legal, IT, and business stakeholders as core functions, not side responsibilities. In practice, this means:
- Mapping regulatory requirements to technical controls using frameworks like NIST CSF, ISO 27001, and CIS Controls to translate legal language into actionable security measures.
- Driving governance, risk, and compliance (GRC) initiatives that create a structured, auditable record of how the organization manages risk.
- Orchestrating cross-functional collaboration between business units, IT teams, legal counsel, and external auditors to ensure no requirement falls through the cracks.
- Ensuring continuous monitoring and reporting so that compliance posture is visible in real time, not just at audit time.
- Communicating risk in business terms to the board and executive leadership, translating technical findings into financial and operational impact.
The distinction between a tactical and a strategic CISO is significant:
| Dimension | Tactical (checkbox) CISO | Strategic (risk-aware) CISO |
|---|---|---|
| Primary focus | Passing audits | Reducing business risk |
| Compliance trigger | Upcoming audit deadline | Continuous risk posture |
| Stakeholder engagement | IT and compliance team only | Board, legal, business units |
| Metrics reported | Control counts | MTTD, MTTR, incident impact |
| Framework use | Checklist completion | Outcome-driven mapping |
Pro Tip: If you are building or refining your cybersecurity roadmap, start by identifying which regulatory requirements directly affect your highest-value business processes. That alignment will make every subsequent compliance decision faster and more defensible.
The compliance leadership strategies that distinguish high-performing CISOs share one trait: they treat compliance as a business enabler, not a cost center.

Beyond checkbox compliance: Why risk-driven strategy wins
With tactical roles outlined, it is critical to clarify why not all compliance strategies are created equal. The compliance paradox is real: organizations can be certified yet still vulnerable, because certifications validate controls at a point in time, not the ongoing effectiveness of those controls.
The compliance security illusion is particularly dangerous in fast-moving threat environments. Attackers do not wait for your next audit cycle. A risk-driven approach addresses this by focusing on outcomes rather than control counts.
Characteristics of a risk-driven compliance program include:
- Continuous risk assessment rather than annual snapshots
- Threat-informed prioritization of controls based on actual attack patterns
- Business context integration so that risk decisions reflect operational impact
- Adaptive governance that updates policies as regulations and threats evolve
- Cross-functional accountability where compliance ownership extends beyond the security team
"92% of CISOs now report directly to the CEO, a structural shift that reflects how central risk-driven compliance has become to business strategy."
Risk-driven methodologies align security with business outcomes in ways that checklist approaches cannot. The cybersecurity compliance challenges facing regulated industries today require this level of strategic integration. Organizations that make this shift find that compliance becomes a business advantage, not just a cost of doing business.
Best practices for CISOs leading compliance
Having contrasted risk-based and checklist approaches, we move to actionable strategies for CISOs to lead compliance transformation. The following practices reflect what high-performing security leaders actually implement.
- Build a dedicated compliance function. Assign clear ownership across business units, not just within the security team. Cross-functional accountability prevents gaps and accelerates audit response times.
- Shift from periodic audits to continuous assurance. Continuous monitoring and automation using tools like SIEM platforms and automated vulnerability scanning increase program maturity and reduce the cost of each audit cycle.
- Measure outcomes, not just controls. Track metrics like mean time to detect (MTTD), mean time to respond (MTTR), and incident frequency reduction. These numbers tell a more compelling story to the board than a list of completed controls.
- Automate evidence collection. Manual evidence gathering is a significant drain on compliance team capacity. Automation frees analysts to focus on risk analysis rather than documentation.
- Integrate compliance into project delivery. Compliance by design means embedding regulatory requirements into new systems and processes from the start, not retrofitting them after deployment.
Pro Tip: Start your metrics reporting with three to five outcome-oriented KPIs rather than a sprawling dashboard. Fewer, sharper metrics drive better executive conversations and clearer accountability. Review compliance frameworks relevant to your sector to identify which outcome metrics regulators and auditors find most credible.
Key benefits of dedicated compliance teams and continuous assurance include faster audit cycles, reduced remediation costs, and stronger board-level confidence in the organization's risk posture.
Future-proofing: Adapting compliance for AI, third-party risk, and the road ahead
Equipped with best practices, it is essential to anticipate how emerging challenges are reshaping the compliance mandate. Three forces are driving the next wave of complexity: artificial intelligence governance, third-party vendor risk, and the accelerating pace of regulatory change.
AI governance is now a compliance responsibility. 90% of CISOs have expanded privacy programs due to AI, reflecting how quickly regulators are moving to address algorithmic accountability, data provenance, and automated decision-making. CISOs must now assess AI systems with the same rigor applied to traditional IT infrastructure.
Third-party risk has become a primary attack vector. 35.5% of breaches now involve suppliers or partners, making vendor risk management a core compliance function rather than a procurement afterthought. Effective programs include:
- Pre-contract security screening with standardized questionnaires and evidence requirements
- Contractual security obligations that specify breach notification timelines and audit rights
- Ongoing monitoring of vendor security posture through continuous assessment tools
- Tiered risk classification so that critical vendors receive proportionally greater scrutiny
The pace of regulatory change is not slowing. The Brussels effect, where GDPR's global influence has prompted similar legislation across dozens of jurisdictions, illustrates how a single major regulation can reshape compliance obligations worldwide. Cybersecurity trends indicate that AI-specific regulations, supply chain security mandates, and expanded breach notification requirements will continue to emerge through 2026 and beyond.
For organizations that lack the internal capacity to track and respond to these changes, virtual CISO advantages include access to specialized expertise across multiple regulatory domains without the cost of a full-time executive hire.
Partnering for next-level compliance and resilience
The strategies outlined in this article represent a significant operational and cultural shift for most organizations. Executing them well requires not only technical expertise but also the organizational influence to drive cross-functional change.

Heights Consulting Group works directly with CISOs and compliance officers to accelerate this transformation. Our team brings specialized GRC, audit, and technical expertise to organizations navigating overlapping regulatory obligations, third-party risk exposure, and AI governance requirements. Whether you need structured compliance implementation steps or a unified compliance strategy that spans multiple frameworks, we provide the advisory depth to move from reactive auditing to continuous, risk-driven assurance. Contact our cybersecurity experts to discuss a compliance program tailored to your organization's risk profile and regulatory obligations.
Frequently asked questions
What are the first steps a CISO should take when new regulations are announced?
CISOs should assess business impact, map requirements to current controls, and coordinate with legal and IT for timely integration. Compliance mapping and cross-functional integration are the foundational activities that determine how efficiently a new regulation is absorbed.
How can CISOs balance ongoing audits with daily cyber threats?
Implementing continuous monitoring and automation helps CISOs align audit demands with active threat defense, reducing the operational tension between compliance cycles and real-time incident response.
Why is 'checkbox compliance' risky in cybersecurity?
Checkbox approaches foster the compliance paradox, where organizations hold valid certifications while critical vulnerabilities remain unaddressed between audit cycles.
What metrics should CISOs use to demonstrate compliance value?
Focus on risk reduction, MTTD, MTTR, and incident impact rather than control counts. Best practices emphasize outcome metrics because they communicate business value in terms that boards and executives can act on.
How is AI changing the compliance role for CISOs?
AI expands privacy and compliance responsibilities significantly. 90% of CISOs expanded privacy programs due to AI, requiring new policy frameworks, vendor assessments, and control mappings specific to algorithmic systems.
Recommended
- Unlocking Regulatory Success with a Virtual CISO Today - Heights Consulting Group
- Build a Cybersecurity Strategy for Compliance in 2026: Heights Consulting Group.
- Compliance Frameworks – How They Drive Cybersecurity Success
- CISO's Strategic Role: Protecting Your Business in 2026
- How fire alarm systems work: safety and compliance guide
